- Cisco Community
- Technology and Support
- Security
- Network Security
- ASA Rest API not working since upgrade
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ASA Rest API not working since upgrade
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-14-2020 04:41 PM - edited 02-21-2020 09:55 AM
I upgraded all my firewalls from 9.4 to 9.8(4)12. They are running in single context routed mode. I disabled the rest-api agent, as per the upgrade instructions, while doing the upgrade. After upgrading the OS, I upgraded the Rest API package to asa-restapi-7131-lfbff-k8.SPA. the file passes the verification check. Cisco Don't seem to have bothered to update any of the guide docs for this version
I have enabled the api again with no errors, but it does not work properly. I have two primary problems:
It no longer works with TACACS, where as it previously did. The TACACS server has the enable_1 user, as required. If I disable TACACS and only do local auth for http I can authenticate, but the API does not work properly. It doesn't seem to pass the username and password through correctly from the Rest API agent web server to the aaa process. The tacacs logs just show password incorrect. it definitely is not, as I log in to ssh with the same password.
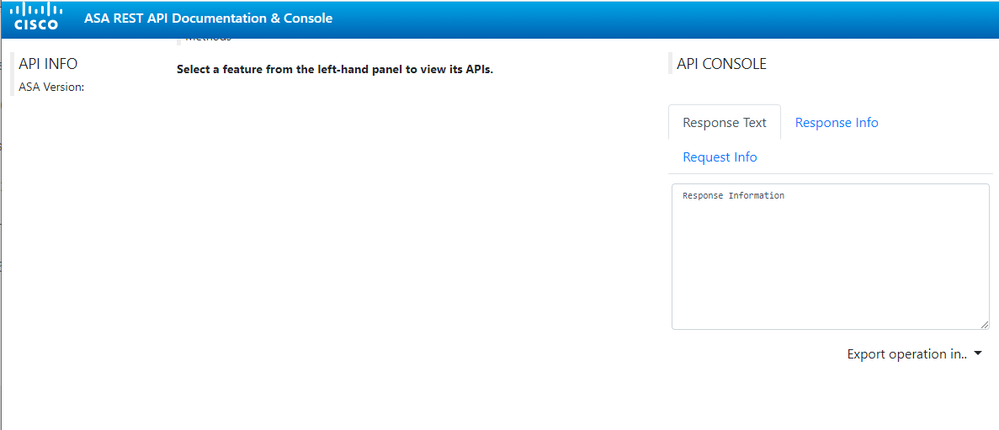
Another example of weirdness: If I go to the https://firewall/doc/ I get a skeleton page with no information populated.
If I try and use the RESTClient addon for Firefox to get a page, even with the basic auth authentication set, I just get a response page asking for my credentials.
<FORM METHOD=POST autocomplete=new-password style="max-width:300px;margin:auto"><HEAD><TITLE>Authorization Required</TITLE></HEAD><H2>Authorization Required!</H2><label for=user>Username</label><br><input id=user name=username type=text><br><label for=pass>Password</label><br><input id=pass name=password type=password><br><INPUT TYPE=HIDDEN NAME=csrf_token VALUE="b54313a25468d6854351a3218b3613512f321321"> <INPUT TYPE=submit VALUE=submit> </FORM>
If I go to the same api url in a normal browser window, I get prompted with the authentication credentials page, which then gives me Invalid request content-type:application/x-www-form-urlencoded
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-03-2021 07:29 AM
I know i'm necro-ing an old post, but as i just installed a new vm with asa and asdm working just fine i also noticed this problem with the doc page not letting me login with the privilege 15 user/passwd that work fine elsewhere but not on the doc page. The doc page for me stays empty, but of course my version numbers may be different (7.16.1.75 for the agent).
I'm wondering if you ever found a solution in the mean time.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-03-2021 08:05 AM
Bug CSCvu48285 was registered for this issue. I think it was fixed in 9.8.4.26.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-03-2021 09:02 AM
Thanks, i must be having another issue then, even though it looks similar. I'm running ASAv 9.14.2.15.
Basically it seems to me that the API Agent is somehow not connected to the local database. I have nothing else there its just a new empty vm to test with.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide