- Cisco Community
- Technology and Support
- Security
- Network Security
- Cannot Ping or Telnet through ASA
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Cannot Ping or Telnet through ASA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-06-2012 02:59 PM - edited 03-11-2019 04:02 PM
Hi Experts,
I built the network like attached diagram, and hoping it to work like this:
the traffic coming from outside, which is VLAN 1, will pass through ASA and go to VLAN 100 and 254.Routing protocol between R0, ASA and R1 is OSPF.
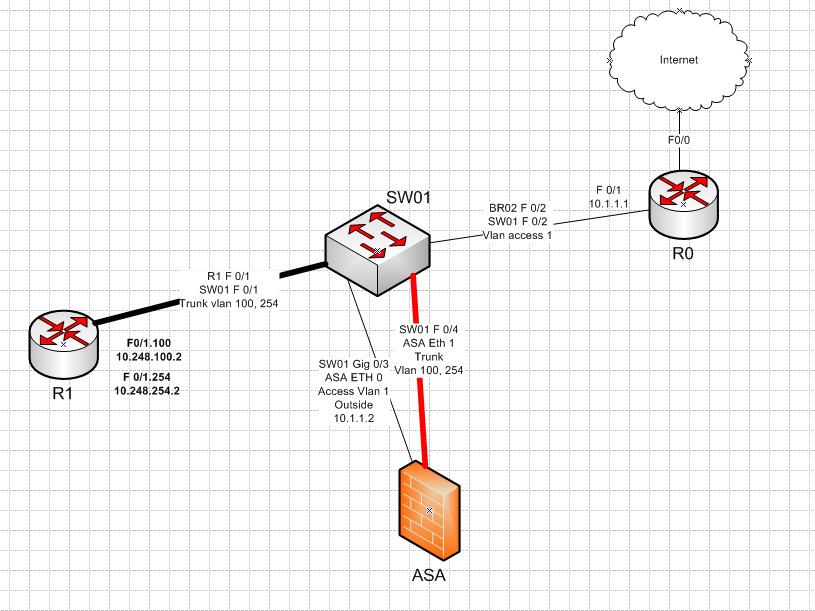
The problem now is that, router R1 can already see all the route information but cannot ping/telnet to R0 or internet. I tried with acl but it doesn't work. Kindly please have a look with the configs below:
R0:
R0#sh run
Building configuration...
Current configuration : 2752 bytes
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname R0
!
boot-start-marker
boot-end-marker
!
logging message-counter syslog
enable secret 5
!
no aaa new-model
!
dot11 syslog
ip source-route
!
!
ip cef
ip dhcp excluded-address 10.1.1.1 10.1.1.100
!
ip dhcp pool frankfurt
network 10.1.1.0 255.255.255.0
default-router 10.1.1.1
!
!
no ip domain lookup
multilink bundle-name authenticated
!
vpdn enable
!
vpdn-group 1
!
!
archive
log config
hidekeys
!
!
interface FastEthernet0/0
ip address x.x.x.x 255.255.255.252
ip nat outside
!
interface FastEthernet0/1
ip address 10.1.1.1 255.255.255.0
ip nat inside
ip virtual-reassembly
!
router ospf 1
log-adjacency-changes
network 10.1.1.0 0.0.0.255 area 0
default-information originate
!
ip forward-protocol nd
ip route 0.0.0.0 0.0.0.0 x.x.x.x
!
no ip http server
no ip http secure-server
!
ip nat inside source list 1 interface FastEthernet0/0 overload
!
access-list 1 permit 10.1.1.0 0.0.0.255
snmp-server community public RO
!
control-plane
!
!
scheduler allocate 20000 1000
no process cpu extended
no process cpu autoprofile hog
end
R1:
R1#sh run
Building configuration...
Current configuration : 1161 bytes
!
version 12.4
no service pad
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname R1
!
boot-start-marker
boot-end-marker
!
logging message-counter syslog
!
no aaa new-model
!
ip source-route
!
!
ip cef
!
no ipv6 cef
!
multilink bundle-name authenticated
!
!
archive
log config
hidekeys
!
!
interface FastEthernet0/1.100
encapsulation dot1Q 100
ip address 10.248.100.2 255.255.255.0
!
interface FastEthernet0/1.254
encapsulation dot1Q 254
ip address 10.248.254.2 255.255.255.0
!
router ospf 1
log-adjacency-changes
network 10.248.100.0 0.0.0.255 area 0
network 10.248.254.0 0.0.0.255 area 0
!
ip forward-protocol nd
no ip http server
no ip http secure-server
R1#sh ip route
Codes: C - connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area, * - candidate default, U - per-user static route
o - ODR, P - periodic downloaded static route
Gateway of last resort is 10.248.254.1 to network 0.0.0.0
10.0.0.0/24 is subnetted, 4 subnets
O 10.1.1.0 [110/11] via 10.248.254.1, 00:25:35, FastEthernet0/1.254
[110/11] via 10.248.100.1, 00:25:35, FastEthernet0/1.100
C 10.248.254.0 is directly connected, FastEthernet0/1.254
C 10.248.100.0 is directly connected, FastEthernet0/1.100
O*E2 0.0.0.0/0 [110/1] via 10.248.254.1, 00:25:35, FastEthernet0/1.254
[110/1] via 10.248.100.1, 00:25:35, FastEthernet0/1.100
ASA:
ASA# sh run
: Saved
:
ASA Version 8.4(2)
!
hostname ASA
!
interface GigabitEthernet0/0
nameif outside
security-level 100
ip address 10.1.1.2 255.255.255.0
!
interface GigabitEthernet0/1
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/1.100
vlan 100
nameif inside
security-level 100
ip address 10.248.100.1 255.255.255.0
!
!
interface GigabitEthernet0/1.254
vlan 254
nameif inside_Tra
security-level 100
ip address 10.248.254.1 255.255.255.0
!
interface GigabitEthernet0/2
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/3
shutdown
no nameif
no security-level
no ip address
!
interface Management0/0
shutdown
no nameif
no security-level
no ip address
!
ftp mode passive
access-list acl_out extended permit icmp any any
access-list acl_out extended permit tcp any any
access-list acl_out extended permit icmp any any echo-reply
access-list acl_out extended permit icmp any any time-exceeded
access-list acl_out extended permit icmp any any echo
access-list acl_out extended permit icmp any any unreachable
access-list acl_out extended permit ospf any any
access-list acl_out extended permit ip any any
access-list acl_out extended permit icmp any host 10.1.1.1
access-list acl_out extended permit udp any any
pager lines 24
mtu outside 1500
mtu inside 1500
mtu inside_Tra 1500
no failover
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
access-group acl_out in interface outside
access-group acl_out in interface inside
access-group acl_out global
!
router ospf 1
network 10.1.1.0 255.255.255.0 area 0
network 10.248.100.0 255.255.255.0 area 0
network 10.248.254.0 255.255.255.0 area 0
log-adj-changes
!
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
user-identity default-domain LOCAL
no snmp-server location
no snmp-server contact
telnet 0.0.0.0 0.0.0.0 outside
telnet 0.0.0.0 0.0.0.0 inside
telnet timeout 5
ssh timeout 5
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
username cisco password 3USUcOPFUiMCO4Jk encrypted
!
class-map inspection_default
match default-inspection-traffic
class-map default
!
!
policy-map type inspect dns migrated_dns_map_1
parameters
message-length maximum client auto
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns migrated_dns_map_1
inspect ftp
inspect h323 h225
inspect h323 ras
inspect ip-options
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
!
service-policy global_policy global
prompt hostname context
no call-home reporting anonymous
Cryptochecksum:a480e144892c65ff1e853becaffc26e9
: end
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-06-2012 07:14 PM
Angran,
I guess the problem is that R0 does not know where Vlan254 is located. Can you try on Router 0
Ip route 10.248.254.0 255.255.255.0 10.1.1.2
Let me know.
Mike
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
