- Cisco Community
- Technology and Support
- Security
- Network Security
- Exchange 2010 and Pix515
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-13-2012 07:43 AM - edited 03-11-2019 04:06 PM
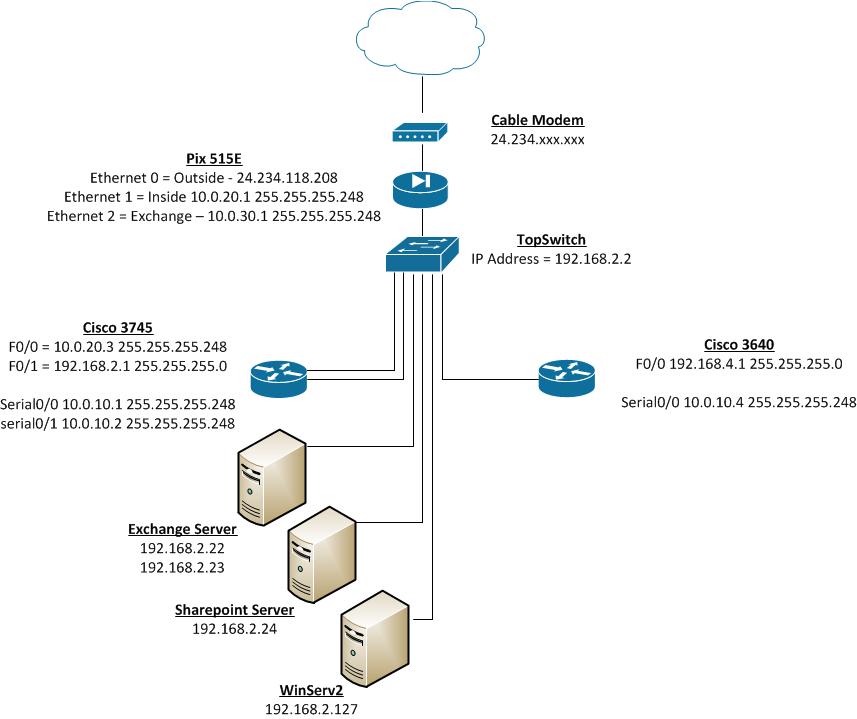
I need some help getting my Exchange Server to be able to send out emails. Can someone review my Pix config and verify that the setting are correct so I can elminate the Pix from the problem?
User Access Verification
Password:
Type help or '?' for a list of available commands.
pixfirewall> enable
Password: ********
pixfirewall# show run
: Saved
:
PIX Version 8.0(4)32
!
hostname pixfirewall
domain-name home.jkkcc.com
enable password DQucN59Njn0OjpJL encrypted
passwd DQucN59Njn0OjpJL encrypted
names
!
interface Ethernet0
nameif outside
security-level 0
ip address dhcp setroute
!
interface Ethernet1
nameif inside
security-level 100
ip address 10.0.20.1 255.255.255.248
!
interface Ethernet2
nameif exchange
security-level 100
ip address 10.0.30.1 255.255.255.248
!
ftp mode passive
dns domain-lookup inside
dns server-group DefaultDNS
name-server 192.168.2.127
name-server 192.168.2.22
domain-name home.jkkcc.com
access-list inbound extended permit tcp any host 24.234.xxx.xxx eq www
access-list inbound extended permit tcp any host 24.234.xxx.xxx eq smtp
pager lines 24
mtu outside 1500
mtu inside 1500
mtu exchange 1500
icmp unreachable rate-limit 1 burst-size 1
icmp deny any outside
asdm image flash:/asdm-61551.bin
no asdm history enable
arp timeout 14400
global (outside) 1 interface
nat (inside) 1 0.0.0.0 0.0.0.0
nat (exchange) 1 0.0.0.0 0.0.0.0
static (inside,outside) tcp interface smtp 192.168.2.23 smtp netmask 255.255.255.255
!
router eigrp 1
network 10.0.0.0 255.0.0.0
network 192.168.0.0 255.255.255.0
network 192.168.2.0 255.255.255.0
network 192.168.4.0 255.255.255.0
!
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
dynamic-access-policy-record DfltAccessPolicy
aaa-server TACACS+ protocol tacacs+
aaa-server RADIUS protocol radius
http server enable
http 0.0.0.0 0.0.0.0 inside
no snmp-server location
no snmp-server contact
snmp-server community *****
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 4608000
telnet 0.0.0.0 0.0.0.0 inside
telnet timeout 5
ssh timeout 5
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
inspect http
inspect ils
!
service-policy global_policy global
prompt hostname context
Cryptochecksum:5af55d8ca2ba2cda2cbcbdd4b50138ae
: end
pixfirewall#
Solved! Go to Solution.
- Labels:
-
NGFW Firewalls
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2012 06:50 PM
Here you go:
static (inside,outside) tcp interface smtp 192.168.2.22 smtp netmask 255.255.255.255
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-13-2012 07:42 PM
You should be able to send email out base on the configuration of the PIX.
I also assume that the following is configured but not used and all traffic is being routed via PIX inside interface:
interface Ethernet2
nameif exchange
security-level 100
ip address 10.0.30.1 255.255.255.248
I assume that routing is correct on the PIX, ie: for 192.168.2.0/24 network on the PIX is being routed towards 10.0.20.3 (you can check on the PIX using "show route"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2012 12:59 PM
Ok, it kinda works, but I can't rehecieve emails from outside the internet. Can you review the config and verify the problem is not with the Pix? Do I need to configure a route on the 3745 router too?
ISP IP Address: 24.234.xxx.xxx
PIX IP: 10.0.20.1 (inside)
3745 Router: 10.0.20.3 F0/0 192.168.2.1 F0/1
Show Run:
pixfirewall# show run
: Saved
:
PIX Version 8.0(4)32
!
hostname pixfirewall
domain-name jkkcc.com
enable password DQucN59Njn0OjpJL encrypted
passwd DQucN59Njn0OjpJL encrypted
names
!
interface Ethernet0
nameif outside
security-level 0
ip address 24.234.xxx.xxx 255.255.255.224
!
interface Ethernet1
nameif inside
security-level 100
ip address 10.0.20.1 255.255.255.248
!
interface Ethernet2
shutdown
nameif exchange
security-level 100
ip address 10.0.30.1 255.255.255.248
!
ftp mode passive
dns domain-lookup inside
dns server-group DefaultDNS
name-server 68.105.28.16
name-server 68.105.29.16
domain-name home.jkkcc.com
access-list inbound extended permit tcp any host 24.234.xxx.xxx eq smtp
access-list inbound extended permit tcp any host 24.234.xxx.xxx eq www
access-list inbound extended permit tcp any host 24.234.xxx.xxx eq 587
pager lines 24
mtu outside 1500
mtu inside 1500
mtu exchange 1500
icmp unreachable rate-limit 1 burst-size 1
icmp deny any outside
asdm image flash:/asdm-61551.bin
no asdm history enable
arp timeout 14400
global (outside) 1 interface
nat (inside) 1 0.0.0.0 0.0.0.0
static (outside,inside) tcp 24.234.xxx.xxx smtp 192.168.2.22 smtp netmask 255.255.255.255
static (inside,outside) tcp 192.168.2.22 smtp 24.234.xxx.xxx smtp netmask 255.255.255.255
!
router eigrp 1
network 10.0.0.0 255.0.0.0
network 192.168.0.0 255.255.255.0
network 192.168.2.0 255.255.255.0
network 192.168.4.0 255.255.255.0
!
route outside 0.0.0.0 0.0.0.0 24.234.118.193 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
dynamic-access-policy-record DfltAccessPolicy
aaa-server TACACS+ protocol tacacs+
aaa-server RADIUS protocol radius
http server enable
http 0.0.0.0 0.0.0.0 inside
no snmp-server location
no snmp-server contact
snmp-server community *****
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 4608000
telnet 0.0.0.0 0.0.0.0 inside
telnet timeout 5
ssh timeout 5
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum 512
policy-map global_policy
class inspection_default
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect netbios
inspect rsh
inspect rtsp
inspect skinny
inspect esmtp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
inspect http
inspect ils
!
service-policy global_policy global
prompt hostname context
Cryptochecksum:db493c9a2975a6a622644c000983b0db
: end
pixfirewall#
Show Route
pixfirewall# show route
Codes: C - connected, S - static, I - IGRP, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, E - EGP
i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area
* - candidate default, U - per-user static route, o - ODR
P - periodic downloaded static route
Gateway of last resort is 24.234.xxx.xxx to network 0.0.0.0
D 192.168.4.0 255.255.255.0 [90/2174976] via 10.0.20.3, 24:21:56, inside
C 24.234.118.192 255.255.255.224 is directly connected, outside
D 10.0.10.0 255.255.255.248 [90/2172416] via 10.0.20.3, 24:21:56, inside
C 10.0.20.0 255.255.255.248 is directly connected, inside
D 192.168.2.0 255.255.255.0 [90/30720] via 10.0.20.3, 24:21:56, inside
S* 0.0.0.0 0.0.0.0 [1/0] via 24.234.118.193, outside
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2012 05:54 PM
To receive mail from the outside, please remove and configure the following:
no static (outside,inside) tcp 24.234.xxx.xxx smtp 192.168.2.22 smtp netmask 255.255.255.255
no static (inside,outside) tcp 192.168.2.22 smtp 24.234.xxx.xxx smtp netmask 255.255.255.255
static (inside,outside) tcp 24.234.xxx.xxx smtp 192.168.2.22 smtp netmask 255.255.255.255
access-list outside-acl permit tcp any host 24.234.xxx.xxx eq 25
access-group outside-acl in interface outside
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2012 06:49 PM
While trying to input the new confige i get this:
ERROR: Static PAT using the interface requires the use of the 'interface' keyword instead of the interface IP address
any ideas
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2012 06:50 PM
Here you go:
static (inside,outside) tcp interface smtp 192.168.2.22 smtp netmask 255.255.255.255
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2012 06:56 PM
thank you so so so so so so so so so much....three days of pulling my hair out and it works finally....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-15-2012 07:52 PM
Great to hear it's working now, thanks for the update
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide


