Hello,
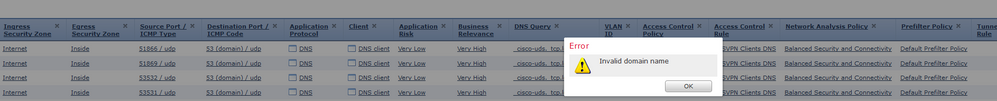
I am trying to filter DNS request from VPN Clients calling for "_cisco-uds._tcp.*" but when I did the obvious from the Connection Events Tab and trying to add the domain to the global blacklist it says that it is an invalid domain.
Priviously on the old ASA there was a an extra policy-map with regex matching on "_cisco-uds._tcp.*" tied to the global policy-map dns inspection that took care of it.
Since I ran into trouble by adding the domaoin to the global DNS blacklist I also tried it with an custom DNS list and DNS policy without luck.
What would be the best solution to drop/filter the DNS requests from the VPN Clients ?
Best regards,
Thomas