- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: FTD failed simulation : Drop-reason: (no-adjacency) No valid adjacency
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2018 02:45 AM - edited 02-21-2020 07:32 AM
Hi team,
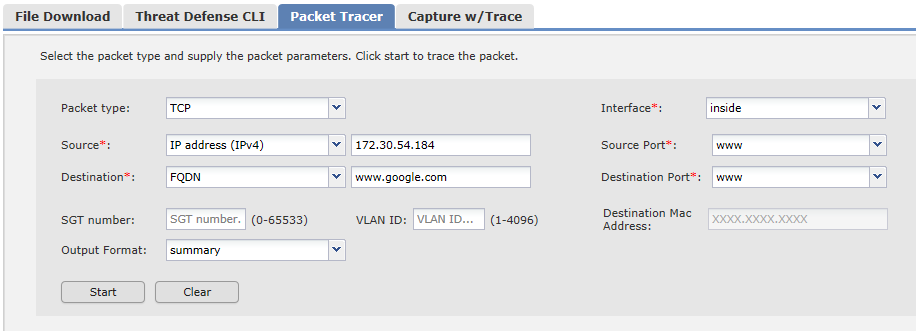
I'm simulating packet tracer before putting my FTD on production:
But when sending a packet from a Lan machine to google :
I get always this result :
Result:
input-interface: inside
input-status: up
input-line-status: up
output-interface: outside
output-status: up
output-line-status: up
Action: drop
Drop-reason: (no-adjacency) No valid adjacency
Does any one knows if this message (Drop-reason: (no-adjacency) No valid adjacency) means a NAT problem or routing problem ?
Regards,
Solved! Go to Solution.
- Labels:
-
NGFW Firewalls
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2018 03:18 AM
Generally that would be a routing issue. Although since your target is a FQDN it could also be DNS lookup. Substitute a target public IP to rule that out.
Have you configured a default route on the device?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2018 03:18 AM
Generally that would be a routing issue. Although since your target is a FQDN it could also be DNS lookup. Substitute a target public IP to rule that out.
Have you configured a default route on the device?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-22-2018 03:33 AM
Thank you Marvin ,
In fact I found the issue :
seen that I'm testing this outside the production , the FTD did not find the mac adress of next hop.
So i think when i will put it in production , it will resolve the mac adress and packet will be allowed.
regards,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-01-2020 09:16 PM
◄ I have same issue ►
packet-tracer input inside icmp 70.1.2.2 8 0 172.16.111.100
Phase: 13
Type: ROUTE-LOOKUP
Subtype: Resolve Egress Interface
Result: ALLOW
Config:
Additional Information:
found next-hop 172.16.111.100 using egress ifc outside
Result:
input-interface: inside
input-status: up
input-line-status: up
output-interface: outside
output-status: up
output-line-status: up
Action: drop
Drop-reason: (no-adjacency) No valid adjacency
==========[ fix ] ==========
no xlate per-session deny tcp any4 any4
no xlate per-session deny tcp any4 any6
no xlate per-session deny tcp any6 any4
no xlate per-session deny tcp any6 any6
no xlate per-session deny udp any4 any4 eq domain
no xlate per-session deny udp any4 any6 eq domain
no xlate per-session deny udp any6 any4 eq domain
no xlate per-session deny udp any6 any6 eq domain
========[ verification ] ========
Phase: 13
Type: ROUTE-LOOKUP
Subtype: Resolve Egress Interface
Result: ALLOW
Config:
Additional Information:
found next-hop 192.168.201.111 using egress ifc outside
Phase: 14
Type: ADJACENCY-LOOKUP
Subtype: next-hop and adjacency
Result: ALLOW
Config:
Additional Information:
adjacency Active
next-hop mac address 5254.0094.9ec5 hits 31930 reference 3
Result:
input-interface: inside
input-status: up
input-line-status: up
output-interface: outside
output-status: up
output-line-status: up
Action: allow
Kind Regards,
Hossam
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-01-2020 09:34 PM
Hi,
This is either a bug, either there is no valid adjacency (IP-to-MAC binding) for the next-hop.
Regards,
Cristian Matei.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2020 09:59 PM
Hi,
I use that version
ASA# show version
Cisco Adaptive Security Appliance Software Version 9.9(1)
Firepower Extensible Operating System Version 2.3(1.54)
Device Manager Version 7.9(1)
Compiled on Thu 30-Nov-17 20:21 PST by builders
System image file is "boot:/asa991-smp-k8.bin"
Config file at boot was "startup-config"
ASA up 2 hours 24 mins
Hardware: ASAv, 4096 MB RAM, CPU Pentium II 1699 MHz, 1 CPU (2 cores)
Model Id: ASAv30
Internal ATA Compact Flash, 129024MB
Slot 1: ATA Compact Flash, 129024MB
BIOS Flash Firmware Hub @ 0x0, 0KB
0: Ext: Management0/0 : address is 5254.003c.3c2c, irq 11
1: Ext: GigabitEthernet0/0 : address is 5254.a4a4.0f4e, irq 11
2: Ext: GigabitEthernet0/1 : address is 5254.b1b1.0ee7, irq 10
License mode: Smart Licensing
ASAv Platform License State: Unlicensed
◄================================== ►
◄================[config: -]================== ►
access-list OUTSIDE_INBOUND extended permit icmp any any
icmp unreachable rate-limit 1 burst-size 1
icmp permit any echo outside
icmp permit any echo-reply outside
icmp permit any outside
icmp permit any echo inside
icmp permit any echo-reply inside
icmp permit any inside
access-group OUTSIDE_INBOUND in interface outside
access-group OUTSIDE_INBOUND out interface outside
access-group OUTSIDE_INBOUND in interface inside
access-group OUTSIDE_INBOUND out interface inside
policy-map global_policy
class inspection_default
inspect icmp
inspect icmp error
no xlate per-session deny tcp any4 any4
no xlate per-session deny tcp any4 any6
no xlate per-session deny tcp any6 any4
no xlate per-session deny tcp any6 any6
no xlate per-session deny udp any4 any4 eq domain
no xlate per-session deny udp any4 any6 eq domain
no xlate per-session deny udp any6 any4 eq domain
no xlate per-session deny udp any6 any6 eq domain
may be we should open bug with cisco
Regards,
Hossam
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide