- Cisco Community
- Technology and Support
- Security
- Network Security
- FTP inspection on FTD?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
FTP inspection on FTD?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-27-2019 12:21 AM - edited 02-21-2020 08:52 AM
Hi,
what is the correct way to configure the FTD 21XX so that the internal clients can use FTP on external ftp servers.
I know that on ASAs we had ftp inspection that worked but i have hard time to find out how to configure the Firepower.
I see that clients can connect to servers on dest port 21 but they are blocked as soon as the server tries to make new connection to clients on source port 21 and then on high numbered ports.
I tried to configure access rules with ports and with applications but with same results.
Output from FTD cli:
> show running-config | include ftp
ftp mode passive
...
inspect ftp
Thanks in advance
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-27-2019 12:58 AM
Hello dejan_jov1
This may can be done using the flexconfig
Objects --> Object Management --> FlexConfig --> FlexConfig Object
Find the "Default_Inspection_protocol_disable edit it
and on the "variables place write the value ftp
Then on devices Flexconfig create a new policy on your ftd and add the Default_Inspection_protocol_disable
Save and apply
Hope that works
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-27-2019 01:37 AM
Hi,
Thanks for your reply!
Do I understand this correctly: I need to disable "inspect ftp" over Flexconfig so that my internal users can use active and passive ftp?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-27-2019 01:42 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-27-2019 02:16 AM
I configured the "no inspect ftp" on FTD trough CLI I see that it is turned off in global_policy map, but unfortunatelly it is still not working. Maybe I haven't corectly explained it but this ist the problem that I have:
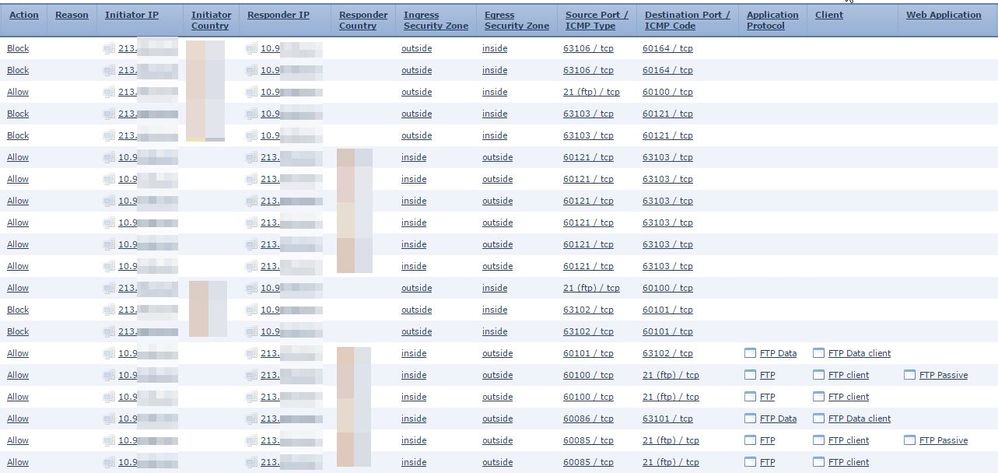
In event logs I see this Block action that is causing the problems:
In my Access policies I allowed that my internal Users can reach external FTP servers and here I even allowed that the exernal servers can reach my internal users with TCP source port 21.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-27-2019 02:47 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-27-2019 03:57 AM
I can't open all the ports that the ftp is using, it's simply to many of them. This is normal behavior of FTP that the server is trying to open a second channel to client but I don't want to open the whole range of ports for FTP to work...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-12-2019 07:39 AM
Hi,
As a Workaround I configured an Prefilter Policy with Fastpath Action for TCP 21 port and it works this way.
But this is also only an temporary solution because this way we have no advanced features for this traffic.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2020 03:25 AM
I have exactly the same problem.
But I don´t want the traffic goes through FTD without inspection.
What is your idea in this regard.
Thanks in advance.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-08-2020 12:34 AM
Even if you fastpath through FTD using a prefilter rule, the flow should still hit any configured ALG (Application Layer Gateway = service policy-based inspection) that's configured in the LINA code.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide