- Cisco Community
- Technology and Support
- Security
- Network Security
- Internal Firewall Placement
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Internal Firewall Placement
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-27-2017 06:11 AM - edited 02-21-2020 06:50 AM
Gents,
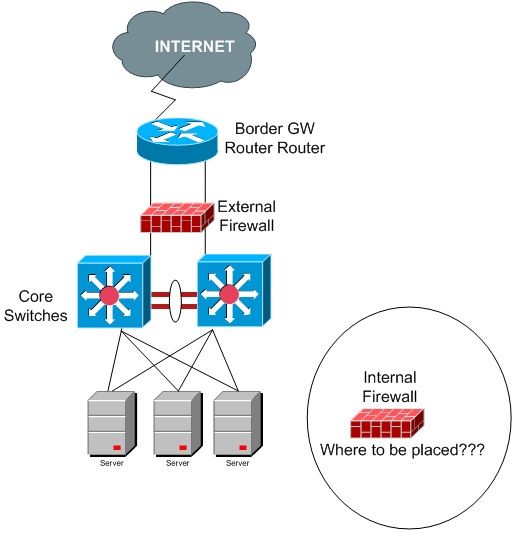
I've a scenario where:
1) All my servers are directly connected to the Core switch.
2) I have only one external firewall that's sitting between the Core and Border Gateway router connected to the internet.
Now client needs their servers to be protected from the internal threats as well.
Luckily, I managed to arrange another ASA that can be used as an internal firewall but don't know where it will sit as all my servers are directly connected to Core switch and we do not have a separate server farm node.
Below is the topology
Please advise!
Kind Regards
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-27-2017 07:00 AM - edited 11-27-2017 07:02 AM
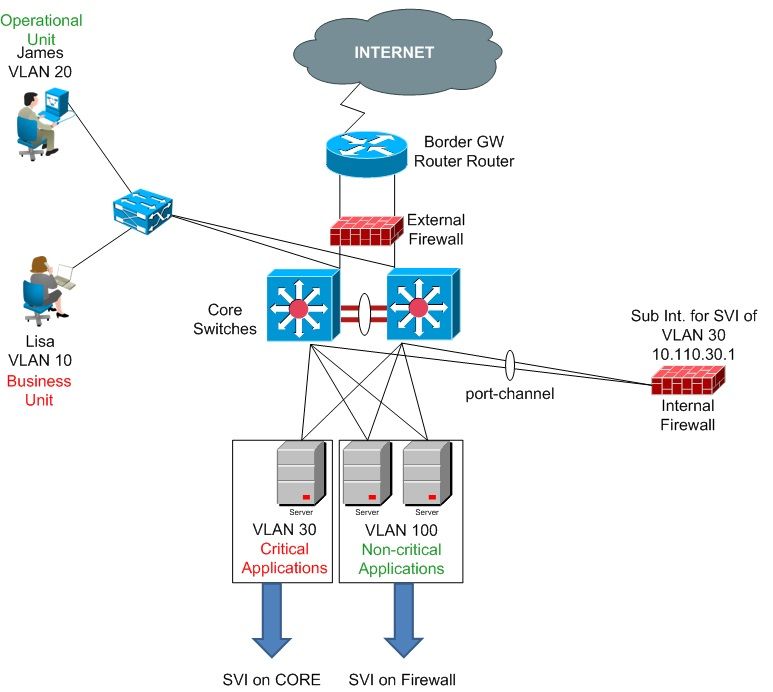
There are multiple options available here. one common scenario is to use the firewall on a stick:
Lets assume your users are on VLAN10, your servers are on VLAN20. On the core-switch you have two vlan-interfaces for VLAN10 and vlan20.
You connect the ASA with a port-channel to the core-switch. On that port-channel you configure a new subinterface for vlan30. This interface will become a transfer-network between the core and the ASA.
On the Core-switch you remove the VLAN-interface for VLAN20 and configure that also as a subinterface of the ASA. On the core you configure also VLAN30 and use the ASA-IP of VLAN30 as the next-hop for the server-VLANs. On the ASA you need a default-route pointing to the core-IP of VLAN30.
Optionally you could use the ASA in transparent mode which would remove the additional transfer-network. And if you want to firewall most to all traffic, then you could just move all VLAN-interfaces to the ASA and have only the ASA as L3-instance.
Have you also thought about that this internal firewall needs quite much throughput and also has to be redundant?
If you found this post helpful, please give it Kudos. If my answer solves your problem, please click Accept as Solution so others can benefit from it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-27-2017 07:57 AM - edited 11-27-2017 12:08 PM
Thanks Brother,
Considering the below (one of the options you discussed) whenever an operational staff member needs to access something from the business unit data resources, the traffic needs to hit the firewall and the connection needs to be approved there on ASA.
Is there anything wrong is this design, please let me know
BTW I'm not configuring any VRFs here, just VLANs.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-27-2017 12:54 PM
You would put the SVIs for the critical applications on the firewall to protect them. The uncritical applications can still be handled (with more throughput) on the core.
If you found this post helpful, please give it Kudos. If my answer solves your problem, please click Accept as Solution so others can benefit from it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-27-2017 12:58 PM
Thanks Bro, seems in this case I do not even need to create the sub-interface.
I mean I just need to configure the SVIs of critical app servers' vlans and rest all the gateways stay on the CORE.
Let me know if there's still need of sub-interfaces.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide