- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
IPS Errors
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-18-2011 07:23 AM - edited 03-10-2019 05:24 AM
Hi to ye all,
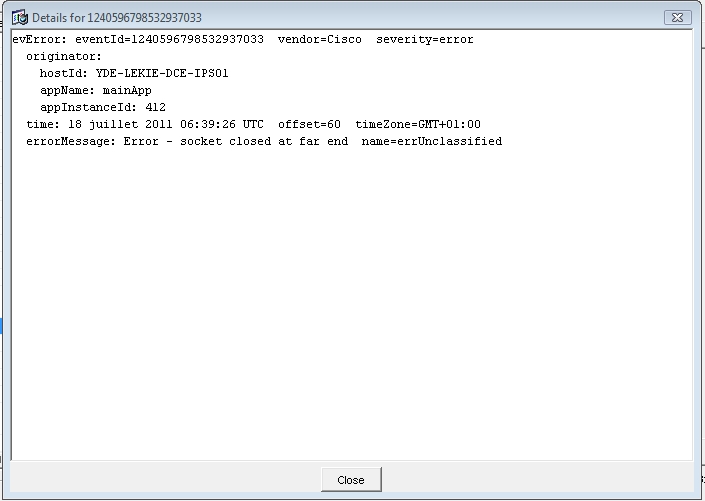
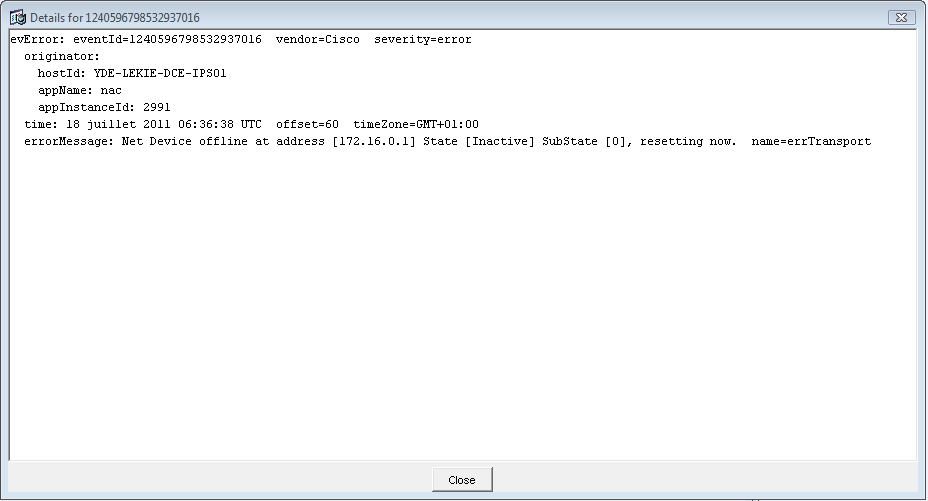
I an ASA 5520 with an AIP-SSM-10 module. Blocking Host Connection has been activated on some signatures and I get the following errors in the diagrams below. I'll like to know their cause and what I can do to solve them


thanks for your help
- Labels:
-
IPS and IDS
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-18-2011 09:55 AM
It looks like you are trying to shun to a PIX firewall.
Have you added the PX to the allowed hosts and the PIX's TLS and SSH keys in the sensor?
Allowed Hosts:
conf t
service host
access-list 192.168.0.1/24 (ip address of your PIX)
exit
exit [yes]
config
Adding TLS and SSH keys:
conf t
ssh host-key 192.168.0.1
tls trusted-host ip-addess 192.168.0.1
- Bob
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-20-2011 12:14 AM
Hye rhermes,
no i haven't done all that. it's an ASA 5520 firewall
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-20-2011 08:23 AM
Even if you are shunning to an ASA you will need to perform those tasks.
- Bob
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-21-2011 03:51 AM
Hye Bob,
When i try generating the trusted key I get this error

- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-21-2011 04:10 AM
Also I have been encountering the following phenomena. See screen captures


In the 1st Screen Capture, it says the source address couldn't be blocked but it was finally blocked so i do not understand what caused that message.
As for the 2nd Screen Capture, when Connection Block Enabled is at True, the Host is not blocked but when it'a at false, the host is blocked. I do not quite understand.
Thanks for all your tips in advance.
bye
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-21-2011 06:50 AM
Don't worry about the TLS connections, those are used between sensors when you make one sensor a Master Blocking Sensor (they need a trust relationship). Is you sensor ssh'ed into your firewall?
you can check with this command (or there should be soem GUI version of this as well). Look for the bold active:
IDSM-slot6# sh stat network-access
Current Configuration
LogAllBlockEventsAndSensors = true
EnableNvramWrite = false
EnableAclLogging = false
AllowSensorBlock = false
BlockMaxEntries = 250
MaxDeviceInterfaces = 250
NetDevice
Type = Cisco
IP = 10.0.0.113
NATAddr = 0.0.0.0
Communications = ssh-3des
ResponseCapabilities = block
BlockInterface
InterfaceName = vlan101
InterfaceDirection = out
BlockInterface
InterfaceName = vlan102
InterfaceDirection = out
State
BlockEnable = true
NetDevice
IP = 10.0.0.113
AclSupport = uses Named ACLs
Version = 12.2
State = Active
- Bob
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-21-2011 08:06 AM
ASA
interface GigabitEthernet0/1.1
nameif inside
security-level 100
ip address 192.168.0.1 255.255.255.128
ASA (Config): ssh 192.168.0.20 255.255.255.255 inside
AIP-SSM
Sensor (Config) # ssh host-key 192.168.0.1
Find above the existing configuration in my ASA5520 and AIP-SSM-10
I have also added the ASA 5520 (192.168.0.1) to the list of Allowed Hosts
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
