- Cisco Community
- Technology and Support
- Security
- Network Security
- Re: Pulling hair out - ASA S2S IPSec VPN behind NAT router
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Pulling hair out - ASA S2S IPSec VPN behind NAT router
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-08-2019 03:01 PM - edited 02-21-2020 09:28 AM
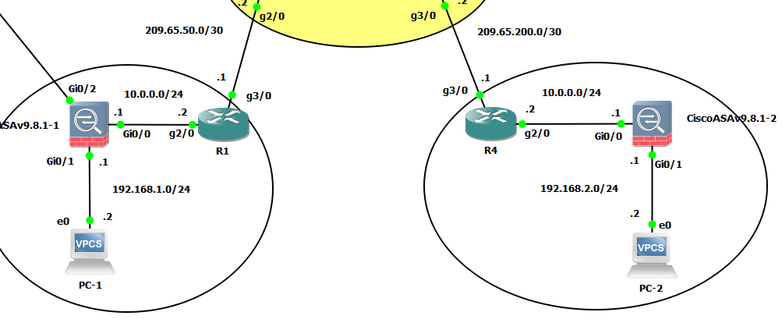
I don't give up and I hate asking for help. But, I've spent enough hours now trying to work out why I can't get the below to work. Just learning about the ASA, and trying to establish an IKEv2 IPSec VPN between the two host computers. R1 and R4 are exchanging routes over BGP (2 other routers not shown in image). Trying to bring the tunnel up with a ping.
Please could someone take a look and let me know what I'm doing wrong? I'd be very grateful of the help.
Many thanks.
R1 Config
============================
ip nat source static udp 10.0.0.1 500 interface GigabitEthernet3/0 500
ip nat source static udp 10.0.0.1 4500 interface GigabitEthernet3/0 4500
ip nat inside source list 1 interface GigabitEthernet3/0 overload
ip route 192.168.1.0 255.255.255.0 10.0.0.1
ASA on left of image
============================
interface GigabitEthernet0/0
nameif OUTSIDE
security-level 0
ip address 10.0.0.1 255.255.255.0
!
interface GigabitEthernet0/1
nameif INSIDE
security-level 100
ip address 192.168.1.1 255.255.255.0
!
interface GigabitEthernet0/2
nameif MGMT
security-level 100
ip address 192.168.30.10 255.255.255.0
!
interface GigabitEthernet0/3
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/4
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/5
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/6
shutdown
no nameif
no security-level
no ip address
!
interface Management0/0
shutdown
no nameif
no security-level
no ip address
!
ftp mode passive
access-list INTERNAL_TO_VPN extended permit ip 192.168.1.0 255.255.255.0 192.168.2.0 255.255.255.0
access-list INTERNAL_TO_VPN extended permit icmp 192.168.1.0 255.255.255.0 192.168.2.0 255.255.255.0
access-list ALLOWVPN extended permit ip 192.168.2.0 255.255.255.0 192.168.1.0 255.255.255.0
access-list ALLOWVPN extended permit icmp 192.168.2.0 255.255.255.0 192.168.1.0 255.255.255.0
access-list ALLOWVPN extended permit udp any any eq isakmp
access-list ALLOWVPN extended permit udp any any eq 4500
pager lines 23
logging buffered debugging
mtu OUTSIDE 1500
mtu INSIDE 1500
mtu MGMT 1500
no failover
no monitor-interface service-module
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
arp rate-limit 8192
access-group ALLOWVPN in interface OUTSIDE
route OUTSIDE 0.0.0.0 0.0.0.0 10.0.0.2 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
timeout conn-holddown 0:00:15
timeout igp stale-route 0:01:10
user-identity default-domain LOCAL
aaa authentication ssh console LOCAL
aaa authentication login-history
no snmp-server location
no snmp-server contact
crypto ipsec ikev2 ipsec-proposal JIM_IKEV2_PROPOSAL
protocol esp encryption aes-256
protocol esp integrity sha-256
crypto ipsec security-association pmtu-aging infinite
crypto map MY_MAP 1 match address INTERNAL_TO_VPN
crypto map MY_MAP 1 set peer 209.65.200.1
crypto map MY_MAP 1 set ikev2 ipsec-proposal JIM_IKEV2_PROPOSAL
crypto map MY_MAP interface OUTSIDE
crypto ca trustpoint _SmartCallHome_ServerCA
no validation-usage
crl configure
crypto ca trustpool policy
auto-import
crypto ca certificate chain _SmartCallHome_ServerCA
certificate ca 18dad19e267de8bb4a2158cdcc6b3b4a
308204d3 308203bb a0030201 02021018 dad19e26 7de8bb4a 2158cdcc 6b3b4a30
0d06092a 864886f7 0d010105 05003081 ca310b30 09060355 04061302 55533117
30150603 55040a13 0e566572 69536967 6e2c2049 6e632e31 1f301d06 0355040b
13165665 72695369 676e2054 72757374 204e6574 776f726b 313a3038 06035504
0b133128 63292032 30303620 56657269 5369676e 2c20496e 632e202d 20466f72
20617574 686f7269 7a656420 75736520 6f6e6c79 31453043 06035504 03133c56
65726953 69676e20 436c6173 73203320 5075626c 69632050 72696d61 72792043
65727469 66696361 74696f6e 20417574 686f7269 7479202d 20473530 1e170d30
36313130 38303030 3030305a 170d3336 30373136 32333539 35395a30 81ca310b
30090603 55040613 02555331 17301506 0355040a 130e5665 72695369 676e2c20
496e632e 311f301d 06035504 0b131656 65726953 69676e20 54727573 74204e65
74776f72 6b313a30 38060355 040b1331 28632920 32303036 20566572 69536967
6e2c2049 6e632e20 2d20466f 72206175 74686f72 697a6564 20757365 206f6e6c
79314530 43060355 0403133c 56657269 5369676e 20436c61 73732033 20507562
6c696320 5072696d 61727920 43657274 69666963 6174696f 6e204175 74686f72
69747920 2d204735 30820122 300d0609 2a864886 f70d0101 01050003 82010f00
3082010a 02820101 00af2408 08297a35 9e600caa e74b3b4e dc7cbc3c 451cbb2b
e0fe2902 f95708a3 64851527 f5f1adc8 31895d22 e82aaaa6 42b38ff8 b955b7b1
b74bb3fe 8f7e0757 ecef43db 66621561 cf600da4 d8def8e0 c362083d 5413eb49
ca595485 26e52b8f 1b9febf5 a191c233 49d84363 6a524bd2 8fe87051 4dd18969
7bc770f6 b3dc1274 db7b5d4b 56d396bf 1577a1b0 f4a225f2 af1c9267 18e5f406
04ef90b9 e400e4dd 3ab519ff 02baf43c eee08beb 378becf4 d7acf2f6 f03dafdd
75913319 1d1c40cb 74241921 93d914fe ac2a52c7 8fd50449 e48d6347 883c6983
cbfe47bd 2b7e4fc5 95ae0e9d d4d143c0 6773e314 087ee53f 9f73b833 0acf5d3f
3487968a ee53e825 15020301 0001a381 b23081af 300f0603 551d1301 01ff0405
30030101 ff300e06 03551d0f 0101ff04 04030201 06306d06 082b0601 05050701
0c046130 5fa15da0 5b305930 57305516 09696d61 67652f67 69663021 301f3007
06052b0e 03021a04 148fe5d3 1a86ac8d 8e6bc3cf 806ad448 182c7b19 2e302516
23687474 703a2f2f 6c6f676f 2e766572 69736967 6e2e636f 6d2f7673 6c6f676f
2e676966 301d0603 551d0e04 1604147f d365a7c2 ddecbbf0 3009f343 39fa02af
33313330 0d06092a 864886f7 0d010105 05000382 01010093 244a305f 62cfd81a
982f3dea dc992dbd 77f6a579 2238ecc4 a7a07812 ad620e45 7064c5e7 97662d98
097e5faf d6cc2865 f201aa08 1a47def9 f97c925a 0869200d d93e6d6e 3c0d6ed8
e6069140 18b9f8c1 eddfdb41 aae09620 c9cd6415 3881c994 eea28429 0b136f8e
db0cdd25 02dba48b 1944d241 7a05694a 584f60ca 7e826a0b 02aa2517 39b5db7f
e784652a 958abd86 de5e8116 832d10cc defda882 2a6d281f 0d0bc4e5 e71a2619
e1f4116f 10b595fc e7420532 dbce9d51 5e28b69e 85d35bef a57d4540 728eb70e
6b0e06fb 33354871 b89d278b c4655f0d 86769c44 7af6955c f65d3208 33a454b6
183f685c f2424a85 3854835f d1e82cf2 ac11d6a8 ed636a
quit
crypto ikev2 policy 10
encryption aes-256
integrity sha
group 5
prf sha256
lifetime seconds 3600
crypto ikev2 enable OUTSIDE
telnet timeout 5
ssh stricthostkeycheck
ssh 0.0.0.0 0.0.0.0 MGMT
ssh timeout 5
ssh key-exchange group dh-group1-sha1
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
dynamic-access-policy-record DfltAccessPolicy
username SSH password $sha512$5000$tfq81kC2eZCfrLsKRwNIWg==$Kl45kdEKX8GiZ/Lc++ujqA== pbkdf2 privilege 15
tunnel-group 209.65.200.1 type ipsec-l2l
tunnel-group 209.65.200.1 ipsec-attributes
ikev2 remote-authentication pre-shared-key Cisco123
ikev2 local-authentication pre-shared-key Cisco123
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
policy-map global_policy
class inspection_default
inspect ip-options
inspect netbios
inspect rtsp
inspect sunrpc
inspect tftp
inspect xdmcp
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect esmtp
inspect sqlnet
inspect sip
inspect skinny
inspect icmp
policy-map type inspect dns migrated_dns_map_2
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
policy-map type inspect dns migrated_dns_map_1
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
R4 Config
=======================================
ip nat source static udp 10.0.0.1 500 interface GigabitEthernet3/0 500
ip nat source static udp 10.0.0.1 4500 interface GigabitEthernet3/0 4500
ip nat inside source list 1 interface GigabitEthernet3/0 overload
ip route 192.168.2.0 255.255.255.0 10.0.0.1
ASA on right of image
========================================
interface GigabitEthernet0/0
nameif OUTSIDE
security-level 0
ip address 10.0.0.1 255.255.255.0
!
interface GigabitEthernet0/1
nameif INSIDE
security-level 100
ip address 192.168.2.1 255.255.255.0
!
interface GigabitEthernet0/2
nameif MGMT
security-level 100
ip address 192.168.30.10 255.255.255.0
!
interface GigabitEthernet0/3
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/4
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/5
shutdown
no nameif
no security-level
no ip address
!
interface GigabitEthernet0/6
shutdown
no nameif
no security-level
no ip address
!
interface Management0/0
shutdown
no nameif
no security-level
no ip address
!
ftp mode passive
access-list INTERNAL_TO_VPN extended permit ip 192.168.2.0 255.255.255.0 192.168.1.0 255.255.255.0
access-list INTERNAL_TO_VPN extended permit icmp 192.168.2.0 255.255.255.0 192.168.1.0 255.255.255.0
access-list ALLOWVPN extended permit ip 192.168.1.0 255.255.255.0 192.168.2.0 255.255.255.0
access-list ALLOWVPN extended permit icmp 192.168.1.0 255.255.255.0 192.168.2.0 255.255.255.0
access-list ALLOWVPN extended permit udp any any eq isakmp
access-list ALLOWVPN extended permit udp any any eq 4500
pager lines 23
logging enable
logging buffered debugging
logging asdm informational
mtu OUTSIDE 1500
mtu INSIDE 1500
mtu MGMT 1500
no failover
no monitor-interface service-module
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
no arp permit-nonconnected
arp rate-limit 8192
access-group ALLOWVPN in interface OUTSIDE
route OUTSIDE 0.0.0.0 0.0.0.0 10.0.0.2 1
timeout xlate 3:00:00
timeout pat-xlate 0:00:30
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 sctp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
timeout conn-holddown 0:00:15
timeout igp stale-route 0:01:10
user-identity default-domain LOCAL
aaa authentication ssh console LOCAL
aaa authentication http console LOCAL
aaa authentication login-history
http server enable
http 0.0.0.0 0.0.0.0 MGMT
no snmp-server location
no snmp-server contact
crypto ipsec ikev2 ipsec-proposal JIM_IKEV2_PROPOSAL
protocol esp encryption aes-256
protocol esp integrity sha-256
crypto ipsec security-association pmtu-aging infinite
crypto map MY_MAP 1 match address INTERNAL_TO_VPN
crypto map MY_MAP 1 set peer 209.65.50.1
crypto map MY_MAP 1 set ikev2 ipsec-proposal JIM_IKEV2_PROPOSAL
crypto map MY_MAP interface OUTSIDE
crypto ca trustpoint _SmartCallHome_ServerCA
no validation-usage
crl configure
crypto ca trustpool policy
auto-import
crypto ca certificate chain _SmartCallHome_ServerCA
certificate ca 18dad19e267de8bb4a2158cdcc6b3b4a
308204d3 308203bb a0030201 02021018 dad19e26 7de8bb4a 2158cdcc 6b3b4a30
0d06092a 864886f7 0d010105 05003081 ca310b30 09060355 04061302 55533117
30150603 55040a13 0e566572 69536967 6e2c2049 6e632e31 1f301d06 0355040b
13165665 72695369 676e2054 72757374 204e6574 776f726b 313a3038 06035504
0b133128 63292032 30303620 56657269 5369676e 2c20496e 632e202d 20466f72
20617574 686f7269 7a656420 75736520 6f6e6c79 31453043 06035504 03133c56
65726953 69676e20 436c6173 73203320 5075626c 69632050 72696d61 72792043
65727469 66696361 74696f6e 20417574 686f7269 7479202d 20473530 1e170d30
36313130 38303030 3030305a 170d3336 30373136 32333539 35395a30 81ca310b
30090603 55040613 02555331 17301506 0355040a 130e5665 72695369 676e2c20
496e632e 311f301d 06035504 0b131656 65726953 69676e20 54727573 74204e65
74776f72 6b313a30 38060355 040b1331 28632920 32303036 20566572 69536967
6e2c2049 6e632e20 2d20466f 72206175 74686f72 697a6564 20757365 206f6e6c
79314530 43060355 0403133c 56657269 5369676e 20436c61 73732033 20507562
6c696320 5072696d 61727920 43657274 69666963 6174696f 6e204175 74686f72
69747920 2d204735 30820122 300d0609 2a864886 f70d0101 01050003 82010f00
3082010a 02820101 00af2408 08297a35 9e600caa e74b3b4e dc7cbc3c 451cbb2b
e0fe2902 f95708a3 64851527 f5f1adc8 31895d22 e82aaaa6 42b38ff8 b955b7b1
b74bb3fe 8f7e0757 ecef43db 66621561 cf600da4 d8def8e0 c362083d 5413eb49
ca595485 26e52b8f 1b9febf5 a191c233 49d84363 6a524bd2 8fe87051 4dd18969
7bc770f6 b3dc1274 db7b5d4b 56d396bf 1577a1b0 f4a225f2 af1c9267 18e5f406
04ef90b9 e400e4dd 3ab519ff 02baf43c eee08beb 378becf4 d7acf2f6 f03dafdd
75913319 1d1c40cb 74241921 93d914fe ac2a52c7 8fd50449 e48d6347 883c6983
cbfe47bd 2b7e4fc5 95ae0e9d d4d143c0 6773e314 087ee53f 9f73b833 0acf5d3f
3487968a ee53e825 15020301 0001a381 b23081af 300f0603 551d1301 01ff0405
30030101 ff300e06 03551d0f 0101ff04 04030201 06306d06 082b0601 05050701
0c046130 5fa15da0 5b305930 57305516 09696d61 67652f67 69663021 301f3007
06052b0e 03021a04 148fe5d3 1a86ac8d 8e6bc3cf 806ad448 182c7b19 2e302516
23687474 703a2f2f 6c6f676f 2e766572 69736967 6e2e636f 6d2f7673 6c6f676f
2e676966 301d0603 551d0e04 1604147f d365a7c2 ddecbbf0 3009f343 39fa02af
33313330 0d06092a 864886f7 0d010105 05000382 01010093 244a305f 62cfd81a
982f3dea dc992dbd 77f6a579 2238ecc4 a7a07812 ad620e45 7064c5e7 97662d98
097e5faf d6cc2865 f201aa08 1a47def9 f97c925a 0869200d d93e6d6e 3c0d6ed8
e6069140 18b9f8c1 eddfdb41 aae09620 c9cd6415 3881c994 eea28429 0b136f8e
db0cdd25 02dba48b 1944d241 7a05694a 584f60ca 7e826a0b 02aa2517 39b5db7f
e784652a 958abd86 de5e8116 832d10cc defda882 2a6d281f 0d0bc4e5 e71a2619
e1f4116f 10b595fc e7420532 dbce9d51 5e28b69e 85d35bef a57d4540 728eb70e
6b0e06fb 33354871 b89d278b c4655f0d 86769c44 7af6955c f65d3208 33a454b6
183f685c f2424a85 3854835f d1e82cf2 ac11d6a8 ed636a
quit
crypto ikev2 policy 10
encryption aes-256
integrity sha
group 5
prf sha256
lifetime seconds 3600
crypto ikev2 enable OUTSIDE
telnet timeout 5
ssh stricthostkeycheck
ssh 0.0.0.0 0.0.0.0 MGMT
ssh timeout 5
ssh key-exchange group dh-group1-sha1
console timeout 0
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
dynamic-access-policy-record DfltAccessPolicy
username SSH password $sha512$5000$ZlbWZqAbmPW6tzNjyCptdw==$PmfribYXvWcrttPS/RjyyA== pbkdf2 privilege 15
tunnel-group 209.65.50.1 type ipsec-l2l
tunnel-group 209.65.50.1 ipsec-attributes
ikev2 remote-authentication pre-shared-key *****
ikev2 local-authentication pre-shared-key *****
!
class-map inspection_default
match default-inspection-traffic
!
!
policy-map type inspect dns preset_dns_map
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
policy-map global_policy
class inspection_default
inspect ip-options
inspect netbios
inspect rtsp
inspect sunrpc
inspect tftp
inspect xdmcp
inspect dns preset_dns_map
inspect ftp
inspect h323 h225
inspect h323 ras
inspect rsh
inspect esmtp
inspect sqlnet
inspect sip
inspect skinny
inspect icmp
policy-map type inspect dns migrated_dns_map_2
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
policy-map type inspect dns migrated_dns_map_1
parameters
message-length maximum client auto
message-length maximum 512
no tcp-inspection
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 07:23 AM
I am not sure about the BGP part and not expert in BGP. But, I think you are missing important Group Policy configuration for the IKEv2 and link that to tunnel-group.
!ON LEFT ASA ! group-policy GP internal group-policy GP attributes vpn-tunnel-protocol ikev2 ! tunnel-group 209.65.200.1 general-attributes default-group-policy GP !ON RIGHT ASA ! group-policy GP internal group-policy GP attributes vpn-tunnel-protocol ikev2 ! tunnel-group 209.65.50.1 general-attributes default-group-policy GP
I hope this help or else let me know, I can lab it up and send you the full configuration. (Without the BGP)
To Encourage, please rate helpful and/or select as answered.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 09:49 AM
Thank you for your response, although my config does already include a tunnel group.
I don't think a site-to-site IPSec VPN needs a group policy, that's more for an AnyConnect setup, if my studying has taught me anything!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 10:02 AM
The configuration is there to define that the tunnel is IKEv2.
I would suggest to give it a try in your lab environment.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 10:31 AM
Please provide ikev2 debugs from both ASAs.
Confirm NAT is working on both routers
Run a packet capture on the ASAs to confirm traffic inbound/outbound.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 12:49 PM - edited 09-09-2019 01:05 PM
Hi RJI,
Thank you or the reply.
1. NAT is working without issue, both PCs/VPCS are able to ping the outside interface of R1/R4. I believe I've port forwarded correctly (see above configs for R1 and R4).
2. I can confirm that 'default-group-policy DfltGrpPolicy' shows under 'show run all tunnel-group 209.65.50.1'
3. The information shown after using 'debug crypto ikev2 protocol 255' on the left ASA when a ping is initiated from 192.168.1.2 to 192.168.2.2 is:
IKEv2-PROTO-5: (3): SM Trace-> SA: I_SPI=7EB0B1824265D621 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_WAIT_INIT Event: EV_RE_XMT
IKEv2-PROTO-2: (3): Retransmitting packet
(3):
IKEv2-PROTO-2: (3): Sending Packet [To 209.65.200.1:500/From 10.0.0.1:500/VRF i0:f0]
(3): Initiator SPI : 7EB0B1824265D621 - Responder SPI : 0000000000000000 Message id: 0
(3): IKEv2 IKE_SA_INIT Exchange REQUESTIKEv2-PROTO-3: (3): Next payload: SA, version: 2.0 (3): Exchange type: IKE_SA_INIT, flags: INITIATOR (3): Message id: 0, length: 510(3):
Payload contents:
(3): SA(3): Next payload: KE, reserved: 0x0, length: 48
(3): last proposal: 0x0, reserved: 0x0, length: 44
Proposal: 1, Protocol id: IKE, SPI size: 0, #trans: 4(3): last transform: 0x3, reserved: 0x0: length: 12
type: 1, reserved: 0x0, id: AES-CBC
(3): last transform: 0x3, reserved: 0x0: length: 8
type: 2, reserved: 0x0, id: SHA256
(3): last transform: 0x3, reserved: 0x0: length: 8
type: 3, reserved: 0x0, id: SHA96
(3): last transform: 0x0, reserved: 0x0: length: 8
type: 4, reserved: 0x0, id: DH_GROUP_1536_MODP/Group 5
(3): KE(3): Next payload: N, reserved: 0x0, length: 200
(3): DH group: 5, Reserved: 0x0
(3):
(3): e9 4e 13 e4 b1 f2 d7 a8 9e bf e6 69 67 a9 f3 bd
(3): 41 1d d6 bd 16 52 ef e8 c1 2e f4 36 8a 21 ad de
(3): c0 85 37 a4 a0 0a 85 40 60 e1 de 81 2c 35 48 00
(3): 85 36 27 21 4d 72 50 6e 02 d9 a4 af ee dc ac 76
(3): c1 6c 44 0b a2 79 fc 54 28 4d bb 5e ac e4 10 0f
(3): 31 a1 c2 2d 10 1e d3 9f 1b 9b a8 28 77 75 13 7e
(3): 69 2d 48 41 33 f1 c9 95 d7 36 39 7b 07 9d fd 91
(3): 1a 8f 16 c9 7d af 69 0a 24 bf a1 f5 19 96 ec 27
(3): 56 b1 d6 a0 84 5e 6f 92 bb 86 48 50 a8 3c 88 78
(3): 5c 88 62 e1 83 99 ab 5b 6e 51 6b 96 69 6e c9 9c
(3): b1 3c 26 1f 08 37 43 47 4f 72 d0 f7 37 6f 1d d2
(3): 4d 0d b8 a9 32 d7 8c d9 86 1b db 6d 12 6c 51 02
(3): N(3): Next payload: VID, reserved: 0x0, length: 68
(3):
(3): 6b af 7d 72 39 b7 9d 47 33 ca f9 ad 8f d3 c9 ab
(3): f9 52 1f 96 db ab 6b 81 e6 5c 2e 64 be 22 3b e6
(3): af f6 1c f1 fc db 70 e7 b5 6a ef 84 eb 09 6e 76
(3): 6c a8 cf de 42 5e e5 b2 3d 49 87 ce 27 87 b4 40
(3): VID(3): Next payload: VID, reserved: 0x0, length: 23
(3):
(3): 43 49 53 43 4f 2d 44 45 4c 45 54 45 2d 52 45 41
(3): 53 4f 4e
(3): VID(3): Next payload: NOTIFY, reserved: 0x0, length: 59
(3):
(3): 43 49 53 43 4f 28 43 4f 50 59 52 49 47 48 54 29
(3): 26 43 6f 70 79 72 69 67 68 74 20 28 63 29 20 32
(3): 30 30 39 20 43 69 73 63 6f 20 53 79 73 74 65 6d
(3): 73 2c 20 49 6e 63 2e
(3): NOTIFY(NAT_DETECTION_SOURCE_IP)(3): Next payload: NOTIFY, reserved: 0x0, length: 28
(3): Security protocol id: IKE, spi size: 0, type: NAT_DETECTION_SOURCE_IP
(3):
(3): 9e 44 0f f3 b8 ab 04 b3 83 a8 ac fb f9 94 fc c9
(3): a4 23 18 07
(3): NOTIFY(NAT_DETECTION_DESTINATION_IP)(3): Next payload: NOTIFY, reserved: 0x0, length: 28
(3): Security protocol id: IKE, spi size: 0, type: NAT_DETECTION_DESTINATION_IP
(3):
(3): 79 a0 ca f1 a1 df fd 42 54 4a 41 60 35 84 99 3b
(3): d3 fa cb 8f
(3): NOTIFY(IKEV2_FRAGMENTATION_SUPPORTED)(3): Next payload: VID, reserved: 0x0, length: 8
(3): Security protocol id: Unknown - 0, spi size: 0, type: IKEV2_FRAGMENTATION_SUPPORTED
(3): VID(3): Next payload: NONE, reserved: 0x0, length: 20
(3):
(3): 40 48 b7 d5 6e bc e8 85 25 e7 de 7f 00 d6 c2 d3
(3):
IKEv2-PROTO-5: (3): SM Trace-> SA: I_SPI=7EB0B1824265D621 R_SPI=0000000000000000 (I) MsgID = 00000000 CurState: I_WAIT_INIT Event: EV_NO_EVENT
Does the posted config look reasonable? Are there any obvious errors in what has been configured?
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 01:12 PM - edited 09-09-2019 01:44 PM
I wanted the full debugs from both ASAs, the output will be different.
Test without the nat overload on both routers
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 02:01 PM
It looks as though the problem is either;
a. The port forwards on the edge routers
b. The outside ACL on the ASA
The ASAs show debug output when the local PC pings across the network, so I'm happy that the crypto map is working and that the building of the VPN tunnel is triggered by a ping to the other side. However, they show no output when the ping is initiated from the other side. The IKEv2 traffic is not hitting the ASA at all.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 02:11 PM
What is the output of "show crypto ipsec sa" on BOTH ASA when you believe the tunnel is up?
Are Decaps|Encaps increasing on both end?
If you still believe you have an issue, provide the full output of the debugs on both ASA if you still require assistance?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 02:27 PM
I haven't tried removing the PAT overload on the outside interfaces of the edge routers..but surely a lack of basic communication to the other side would prevent a tunnel from forming?!
I do not believe even phase 1 is completing, so haven't run 'show crypto ipsec sa' - there is no output for 'show crypto isakmp sa'
As mentioned, I cannot post any debug output from both ASAs, as output is shown when the local PC initiates a ping, not when the ASA is receiving anything from the other end - does that make sense?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 02:42 PM
It looks like you are running this in GNS3, open up wireshark on the hops in between the ASAs and determine if the udp/500 & 4500 is being sent and received. Find out where it isn't being transmitted and go from there.
I assume you can ping from one ASA to the other? Turn on icmp debug "debug icmp trace".
The ACL for isakmp on the OUTSIDE interface is not doing what you believe it's doing. It is currently doing nothing, as it's not applied on the control-plane. IKEv2 is enabled on both ASA due to the command "crypto ikev2 enable outside".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-09-2019 02:55 PM
Apologies, perhaps my wording wasn't as clear as it could be. I see debug output showing an attempt to build the tunnel when a ping is initiated, which is what told me that the ACL in the crypto map is matching the local PC subnet, 192.168.1.0 or 192.168.2.0
I did run a sniff on the router links, and spotted an ISAKMP entry with ICMP destination unreachable, port unreachable. This is why I wondered whether my port forwarding NAT statements on the edge routers were correct.
I know it's sometimes difficult to get problems across with just words, but just to say I really appreciate you taking the time to work through it with me.
I'm in the UK, so off to bed now. Will post again tomorrow.
Thank you again.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-10-2019 02:48 AM
I have lab the setup without BGP part. Find the attached configuration. The configuration is working here in my lab environment. If you still having issue please go step by step in packet capture and also you can run the debug commands at both the ASA.
Make sure your ROUTER is doing NAT properly, you can check NAT translations by "show ip nat tra".
Do let me know if you still having issue.
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-10-2019 06:12 AM
That is so kind of you to test - thank you. Your config looks similar to mine - is it working your end even without opening up the 500 and 4500 ports on the OUTSIDE interfaces of the ASAs?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-10-2019 07:03 AM
You don't have to open any port on the OUTSIDE interface of the ASAs.
This is working configuration. I have tested the same on EVE-NG.
You can use this configuration with minor changes in you GNS3 as well.
I would say, It may be a glitch of IOS/IOL or whatever image you are using for emulation you should check the "sh ip nat tra" , Wireshark and Debug logs to find out the problem.
If you still want help even I can look at your problem remotely through some live meeting session you feel comfortable with. I am from INDIA so we can arrange the time accordingly.
HTH
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide