Hi all
We have an ASA 5510 which was installed at a site some time ago, however I have recently migrated the site's traffic to it away from a previous router (Meraki device of some description)
There is a CUCM server with a SIP trunk to the internet
Since the migration took place, the SIP trunk has stopped working (when a call is placed the destination number doesn't even ring)
I have tried with both SIP inspection enabled and disabled and this doesn't help
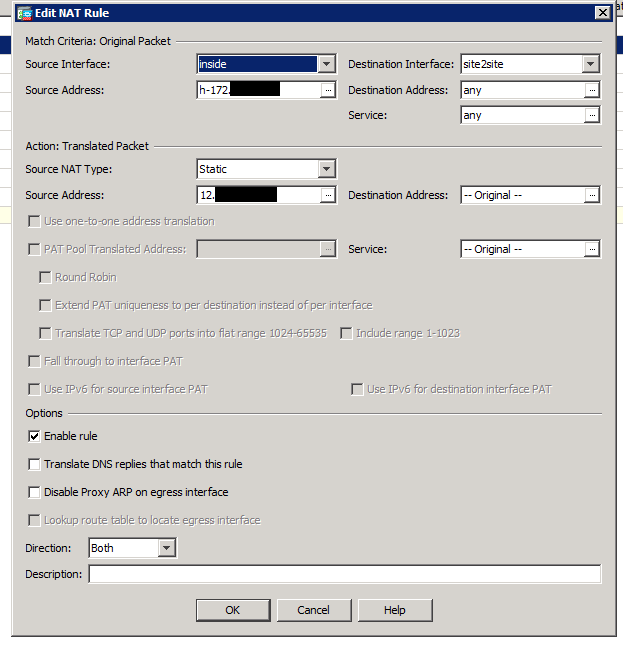
The ASA is set up with a one to one NAT rule from one of site's public IPs to the internal IP of the CUCM (site2site is the name of the internet-facing interface on the device... for some reason)
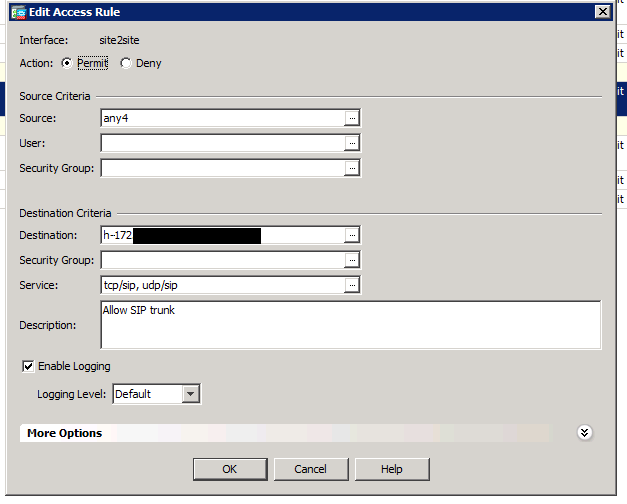
There is an inbound firewall rule configured to allow access from the SIP trunk back to the CUCM server internal IP, and the equivalent outgoing rule for the traffic to the IP of the sip trunk (80.xxx):

I can't see any blocked traffic whatsoever in the logs relating to this connectivity. Packet tracer says the traffic is allowed and NAT-ed correctly
We spoke to the SIP provider and performed a packet capture using the ASA capture wizard and sent the files to them,
After analysis, they said that we were sending a private IP in the data shown here, which is the reason for the failure (as their end doesn't know the IP to send traffic back to):
The trace was performed with SIP inspection on (but the call also fails with it turned off)
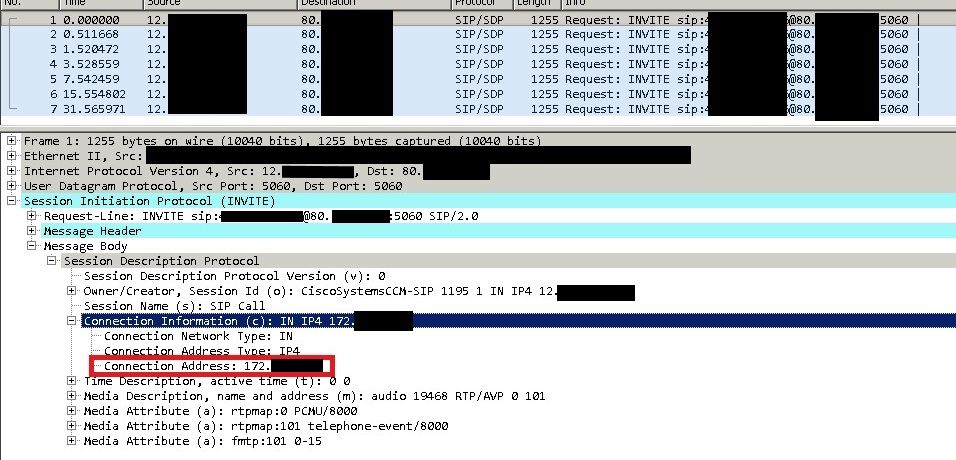
I've removed any information that could be personally identifiable from the data but I hope that it still all makes sense
Does anyone have any thoughts on next steps I can try? Really stuck as to where I can go from here and how this was working on the past
Thanks in advance