- Cisco Community
- Technology and Support
- Security
- Network Security
- Trigger Failover without Standby Address Configuration
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Trigger Failover without Standby Address Configuration
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-14-2012 10:55 PM - edited 03-11-2019 05:23 PM
So, fair warning - I'm new to ASAs and am open to advice on best practices if anyone sees any red flags here.
I am trying to establish EIGRP neighborships with my inside switches (3750s) over the "Internal" interface, shown in green. The outside interface is g0/0 and don't worry, I've ensured EIGRP is not running there.
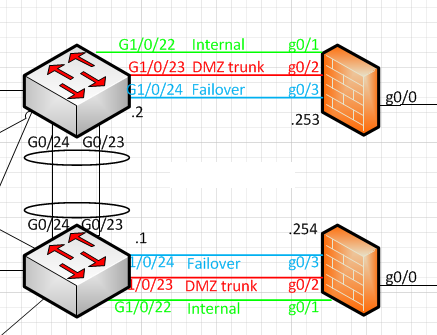
The problem I'm having is that I need to monitor the "Internal" link so that if it goes down, the ASA triggers the failover to the secondary firewall connected to the other switch. I was told that the "secondary" keyword was what enabled this:
interface GigabitEthernet0/1
nameif Inside
security-level 100
ip address 10.10.2.2 255.255.255.0 standby 10.10.2.3
This is fine since I am able to compare this config to the firewalls that are currently in production elsewhere in the environment and this is what's in use there. However, in order to run EIGRP all the way to the firewall and not rely on something else like HSRP for the inbound traffic, I'd like to run the corresponding links (Gi1/0/22) on the inside switches as routed ports (no switchport) so that I don't have to establish neighborships with SVIs or something like that. I want the routing to be done directly to the port, leaving the interfaces for failover and our DMZ set up as switchports, since those can be layer 2.
It's saying the Internal interface has failed now, probably because it cannot send hellos through this, since it's a routed port on the switch side. I'm wondering if this simply is an impossible design, unless there's a way to track this interface and trigger a failover if it goes down using another method. That's what I'm looking for here - a method that allows me to track that internal interface (Gi0/1) and trigger a failover if it goes down.
Thoughts?
- Labels:
-
NGFW Firewalls
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-21-2012 05:29 PM
Hello Matt,
Failover is based on the exchange of this well known hello packets in order to determine when an interface is up/down so failover can be triggered....
That being said with this particular desing if you want to implement failover on this internal interface you will need to place a switch in between so this two boxes can exchange this packets and ofcourse build the EIGRP neigborship,, that will be the only way around..
Regards,
Julio
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
