- Cisco Community
- Technology and Support
- Security
- Network Security
- Zone Interface Configuration Disconnecting VPN Users from Server
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-05-2013 12:11 PM - edited 03-11-2019 08:13 PM
Hello Friends
I have a problem with zone based firewall.
As per diagram my vpn server is configured on ASA.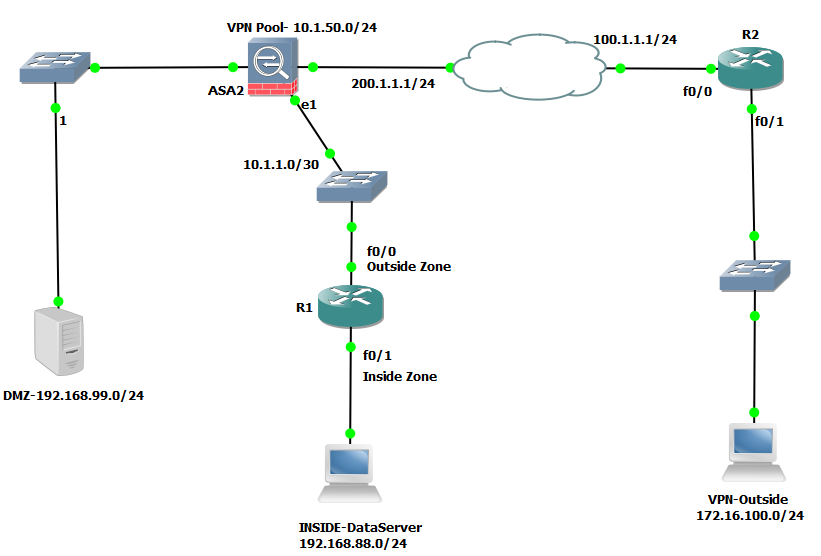 Kindly help This is very Important.
Kindly help This is very Important.
ASA is not able to block torrent traffic so i am configuring Zone Base Firewall on my ISR Router.
After configuration router is blocking the torrent traffic but it is not allowing my VPN users to connect to internal Database Server, as soon as I put interfaces in different zones, data connection is diconnecting (coz Server is in inside zone) but VPN connection is still working & client are connected to ASA.
I tried many things but not able to solve the problem pls help friends coz torrents are consuming my bandwidth.
Here is the configuration configured on the Router
interface FastEthernet0/0
ip address 10.1.1.2 255.255.255.252
zone-member security outsideduplex auto
speed auto
!
interface FastEthernet0/1
ip address 192.168.88.1 255.255.255.0
zone-member security insideduplex auto
speed auto
!
router ospf 100
log-adjacency-changes
passive-interface FastEthernet0/1
network 10.1.1.2 0.0.0.0 area 0
network 192.168.88.0 0.0.0.255 area 0
class-map type inspect match-all HTTP-ACCESS-CLS
match protocol http
class-map type inspect match-any PERMITTED-TRAFFIC-CLS-1
match protocol pptp
match protocol dns
match protocol https
match protocol icmp
match protocol smtp
match protocol pop3
match protocol tcp
match protocol udp
exit
class-map type inspect match-all PERMITTED-TRAFFIC-CLS-2
match class PERMITTED-TRAFFIC-CLS-1
Class-map type inspect http match-any HTTP-PORT-MISUSE
match request port-misuse p2p
match request port-misuse tunnel
policy-map type inspect http PLCY-HTTP-PORT-MISUSE
class type inspect http HTTP-PORT-MISUSE
log
reset
class-map type inspect match-any P2P-BLOCK-CLS-1
match protocol edonkey signature
match protocol gnutella signature
match protocol kazaa2 signature
match protocol fasttrack signature
match protocol bittorrent signature
class-map type inspect match-all P2P-BLOCK-CLS-2
match class-map P2P-BLOCK-CLS-1
parameter-map type urlf-glob FACEBOOK
pattern facebook.com
pattern *.facebook.com
parameter-map type urlf-glob YOUTUBE
pattern youtube.com
pattern *.youtube.com
parameter-map type urlf-glob DAILYMOTION
pattern dailymotion.com
pattern *.dailymotion.com
parameter-map type urlf-glob VIMEO
pattern vimeo.com
pattern *.vimeo.com
parameter-map type urlf-glob MEATACAFE
pattern Metacafe.com
pattern *.metacafe.com
parameter-map type urlf-glob HULU
pattern hulu.com
pattern *.hulu.com
parameter-map type urlf-glob VEOH
pattern veoh.com
pattern *.veoh.com
parameter-map type urlf-glob PERMITTED-SITES
pattern *
class-map type urlfilter match-any BLOCKED-SITES
match server-domain urlf-glob FACEBOOK
match server-domain urlf-glob YOUTUBE
match server-domain urlf-glob VEOH
match server-domain urlf-glob HULU
match server-domain urlf-glob MEATACAFE
match server-domain urlf-glob VIMEO
match server-domain urlf-glob DAILYMOTION
class-map type urlfilter match-any PERMITTED-SITES
match server-domain urlf-glob PERMITTED-SITES
policy-map type inspect urlfilter CONTENT-FILTERING
class type urlfilter BLOCKED-SITES
log
reset
class type urlfilter PERMITTED-SITES
allow
ip access-list extended ACL-IN-TO-OUT
permit ip host 192.168.88.x 10.1.50.0 0.0.0.255
class-map type inspect match-any CLS-IN-TO-OUT
match access-group name ACL-IN-TO-OUT
ip access-list extended ACL-OUT-TO-IN
PERmit IP 10.1.50.0 0.0.0.255 host 192.168.88.x
class-map type inspect match-any CLS-OUT-TO-IN
match access-group name ACL-OUT-TO-IN
policy-map type inspect PLCY-OUT-TO-IN
class type inspect CLS-OUT-TO-IN
inspect
policy-map type inspect TRAFFIC-INSPECT-IN-TO-OUT
class type inspect HTTP-ACCESS-CLS
inspect
service-policy http PLCY-HTTP-PORT-MISUSE
class type inspect HTTP-ACCESS-CLS
inspect
service-policy urlfilter CONTENT-FILTERING
class type inspect P2P-BLOCK-CLS-2
drop log
class type inspect PERMITTED-TRAFFIC-CLS-2
inspect
class type inspect CLS-IN-TO-OUT
inspect
zone-pair security OUT-TO-in source OUTSIDE destination INSIDE
service-policy type inspect PLCY-OUT-TO-IN
zone security OUTSIDE
zone security INSIDE
zone-pair security IN-TO-OUT source INSIDE destination OUTSIDE
service-policy type inspect TRAFFIC-INSPECT-IN-TO-OUT
Thanks & Regards
Sabby
Solved! Go to Solution.
- Labels:
-
NGFW Firewalls
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-05-2013 08:17 PM
Hello,
Is the VPN pool from the 10.1.50.0/24 subnet ?
If yes, then traffic should be allowed
So do
ip inspect log drop-pkt
And then attempt to connect
After it fails do a
show looging | include x.x.x.x (Internal server IP address)
and provide us the log
Rate all of the helpful posts!!!
Regards,
Jcarvaja
Follow me on http://laguiadelnetworking.com
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2013 04:20 AM
Hello Sarbjit,
Those logs basically thing the IOS FW thinks the session does not honor a valid TCP session, there.
(this could be because of Asymetric routing, invalid payload,etc,etc) so the inspection is actually breaking this.
If you set a Pass/Pass rule for traffic comming from the VPN users to that server then this will work.
My recommendation:
Enabled packet-captures on the IOS Router (Embedded packet-captures) in order to see what the FW is seeing.
Rate all of the helpful posts!!!
Regards,
Jcarvaja
Follow me on http://laguiadelnetworking.com
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-05-2013 08:17 PM
Hello,
Is the VPN pool from the 10.1.50.0/24 subnet ?
If yes, then traffic should be allowed
So do
ip inspect log drop-pkt
And then attempt to connect
After it fails do a
show looging | include x.x.x.x (Internal server IP address)
and provide us the log
Rate all of the helpful posts!!!
Regards,
Jcarvaja
Follow me on http://laguiadelnetworking.com
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2013 01:29 AM
Hi
Thanks For reply
here is the log am getting..
%FW-6-DROP_PKT: Dropping tcp session 10.1.50.20:49198 192.168.88.x:PORT due to policy match failure with ip ident 0
Thanks
Sabby
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2013 04:20 AM
Hello Sarbjit,
Those logs basically thing the IOS FW thinks the session does not honor a valid TCP session, there.
(this could be because of Asymetric routing, invalid payload,etc,etc) so the inspection is actually breaking this.
If you set a Pass/Pass rule for traffic comming from the VPN users to that server then this will work.
My recommendation:
Enabled packet-captures on the IOS Router (Embedded packet-captures) in order to see what the FW is seeing.
Rate all of the helpful posts!!!
Regards,
Jcarvaja
Follow me on http://laguiadelnetworking.com
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2013 04:58 AM
Jcarvaja thanks for you help
I will change & check the result.
Thanks agian
Regards
Sabby
Sent from Cisco Technical Support
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-06-2013 05:00 AM
Hello,
No problem just remember to rate all of the helpful replies
Regards,
Jcarvaja
Follow me on http://laguiadelnetworking.com
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-07-2013 02:34 AM
Hello Jcarvaja
I tried to change as you suggested but did nt work.
The changed config is bold & underlined.
ip access-list extended ACL-IN-TO-OUT
permit ip host 192.168.88.x 10.1.50.0 0.0.0.255
class-map type inspect match-any CLS-IN-TO-OUT
match access-group name ACL-IN-TO-OUT
policy-map type inspect TRAFFIC-INSPECT-IN-TO-OUT
class type inspect CLS-IN-TO-OUT
pass
-----
ip access-list extended ACL-OUT-TO-IN
PERmit IP 10.1.50.0 0.0.0.255 host 192.168.88.x
class-map type inspect match-any CLS-OUT-TO-IN
match access-group name ACL-OUT-TO-IN
policy-map type inspect PLCY-OUT-TO-IN
class type inspect CLS-OUT-TO-IN
pass
So I changed few more config settings.
policy-map type inspect TRAFFIC-INSPECT-IN-TO-OUT
class type inspect PERMITTED-TRAFFIC-CLS-2
no inspect
pass
with this config vpn was now working but internet connection from inside network were stooped.
so to trick it, I created another class map for matching only for pptp & I map it under policy-map as pass and now everything is working.r
here is my final configuration:
class-map type inspect match-all HTTP-ACCESS-CLS
match protocol http
class-map type inspect match-any PERMITTED-TRAFFIC-CLS-1
match protocol pptp
class-map type inspect match-all PERMITTED-TRAFFIC-CLS-2
match class-map PERMITTED-TRAFFIC-CLS-1
class-map type inspect match-any PERMITTED-TRAFFIC-CLS-3 (New Class-Map)
match protocol dns
match protocol http
match protocol https
match protocol udp
match protocol tcp
match protocol smtp
match protocol pop3
match protocol icmp
!
!
policy-map type inspect TRAFFIC-INSPECT-IN-TO-OUT
class type inspect HTTP-ACCESS-CLS
inspect
service-policy http PLCY-HTTP-PORT-MISUSE
service-policy urlfilter CONTENT-FILTERING
class type inspect P2P-BLOCK-CLS-2
drop log
class type inspect PERMITTED-TRAFFIC-CLS-2
pass
class type inspect CLS-IN-TO-OUT
pass
class type inspect PERMITTED-TRAFFIC-CLS-3
inspect
class class-default
drop
policy-map type inspect PLCY-OUT-TO-IN
class type inspect CLS-OUT-TO-IN
pass
class class-default
drop
Thank You for your help
Regards
Sabby
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-07-2013 06:28 AM
Hello Sarbit,
Ofcourse you needed the previous defined policies for the internet traffic.
Hey a pleasure to help
Rate all of the helpful posts!!!
Regards,
Jcarvaja
Follow me on http://laguiadelnetworking.com
Senior Network Security and Core Specialist
CCIE #42930, 2xCCNP, JNCIP-SEC
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide
