- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- Automation using OSPF and RIP: route redistribution based on tags and EEM actions
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on 11-24-2018 03:27 AM
INTRODUCTION
This article discusses a route redistribution between OSPF and RIP protocols to automate actions if some network devices have a malfunction. The goal is to demonstrate нow can you change the data flows if certain conditions occur. The described concept works for both two and 1000 branches.
This article will be interesting to those who have just begun to learn the mysterious world of data networks as well as those who have long known about OSPF Type 5 LSAs and route tags.
NETWORK DESCRIPTION
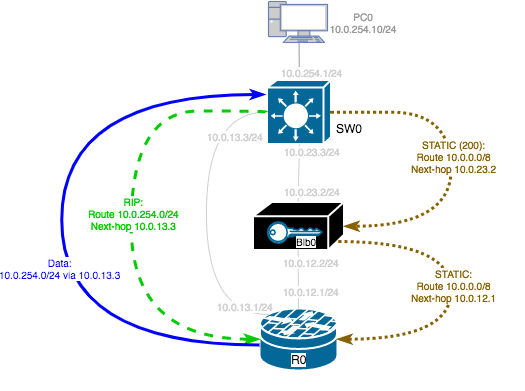
Let’s look at the network of a small company that has a headquarter (HQ) and two branches (Office # 1 and Office # 2). A network layout consists of the following devices (see Figure 1):
- Routers R0, R1 and R2
- LAN switches SW0, SW1, and SW2
- Black boxes Blb0, Blb1 and Blb2
LAN switches have IP base license, so they support static routes, RIP, EIGRP stub, and OSPF for routed access.
Following dynamic routing protocols are used:
- RIP between SWx switch and Rx router in the same office
- OSPF between routers in the HQ and branches
Black boxes work as security gateways in IPsec tunnel mode. It means they mask LAN networks and outgoing packets have the address of the external interface of the black box.
Additional requirements:
- If a black box is available, all data streams should follow the path LANx <-> SWx <-> BLBx <-> Rx.
- In the event of black box failure, users with IP addresses 10.x.254.2 - 10.x.254.14 should have access to resources of HQ or other branches.
Figure 1. Connecting network devices in HQ and branches
HOW IT WORKS
This solution implements automation by changing and adding routes when certain events in the network are triggered. For these purposes we use the dynamic routing protocols RIP and OSPF, as well as IP SLA services for sending ICMP requests and Embedded Event Manager (EEM) for performing actions when IP SLA probes are lost.
Below you can find a detailed explanation of how it works for the case of Office # 1 black box failure.
It is also necessary to take into account that it is required to change the data routing in both directions.
Step 1. Changing the routing table on the SW1 switch
IP SLA service is used on the R1 router in Office #1 to track the BLB1 black box availability.
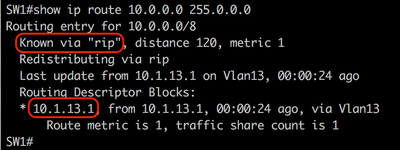
Event manager applet on R1 router sends 10.0.0.0/8 route to SW1 switch by RIP if IP SLA probe gets status "failed". On switch SW1, Cisco Administrative Distances have been changed that RIP routes are preferable over static routes.
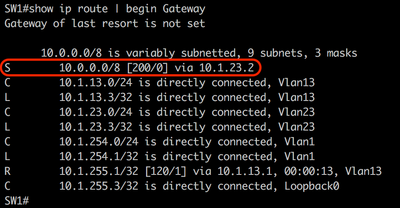
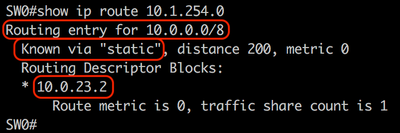
Show ip route command outputs from switch SW1 are shown below:
- if Blb1 is available, then the SW1 switch uses a static route 10.0.0.0/8 with an Administrative Distance value of 200;
- if Blb1 is unavailable, then the SW1 switch receives the 10.0.0.0/8 route from R1 router by the RIP protocol with an Administrative Distance value of 120. Accordingly, SW1 chooses the 10.0.0.0/8 route received by the RIP.
The following messages appear in the console and the logging when actions are triggered in the event manager applet service:
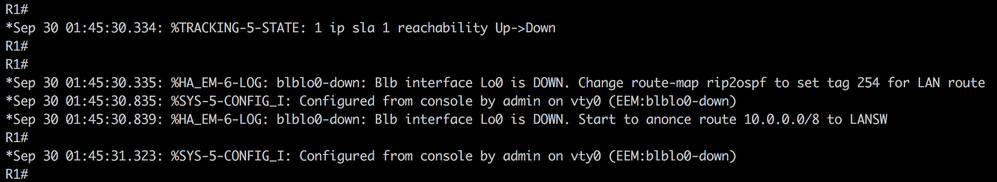
Note: The event manager applet is triggered on the state of the object in “track 1”, which has the IP SLA test attached.
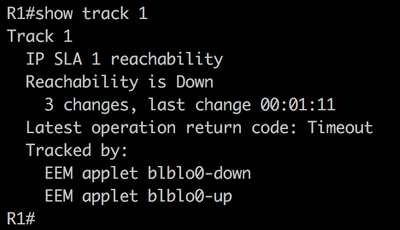 R1: show track 1
R1: show track 1
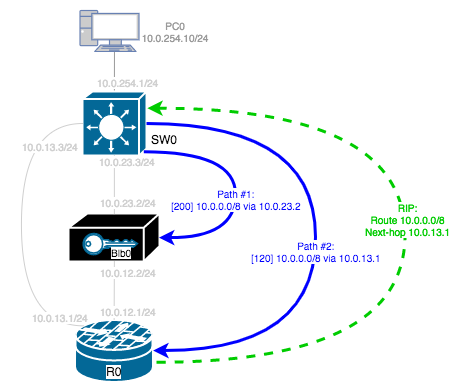
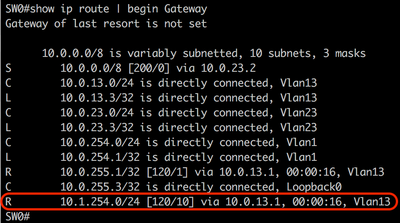
Step 2: Changing the routing table on the SW0 switch at the HQ
The next step is to affect the SW0 routing table and the SW2 routing table as well. It is required to return traffic to Office # 1, these switches temporarily bypass their local “black boxes” Blb0 and Blb2, respectively. At the same time, traffic to “normal” (not problematic) branches should be unchanged. Now imagine that the number of branches has increased to 10 or even to 100?
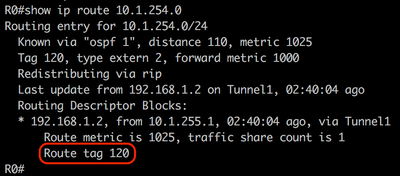
In this step, a route redistribution from RIP to OSPF is used on router R1 with adding a tag. Then R0 and R2 routers use the tag for reverse route redistribution from OSPF to RIP (Figure 4).
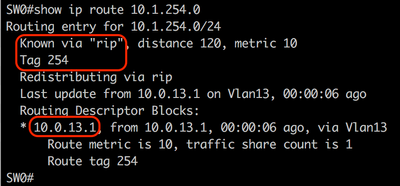
- If the Blb1 black box is unavailable, the local R1 router in Office # 1 redistributes the LAN route 10.1.254.0/24 from RIP to OSPF and changes the route tag value from 120 to 254
- R0 router in HQ redistributes the route with the tag value 254 from OSPF to RIP
- Local switch SW0 in HQ adds the route 10.1.254.0/24 in the routing table, and it uses the route to pass traffic through R0 instead of Blb0
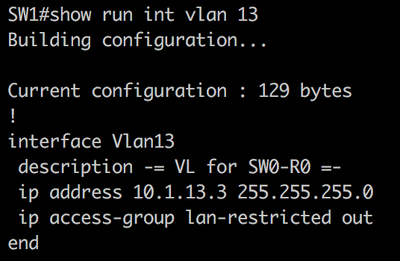
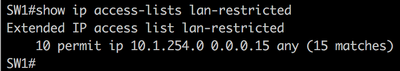
Additionally, an access list is configured to limit the LAN addresses that are allowed to transfer data for the duration of the local black box failure. The access list is applied on VLAN 13 interface of the SW1 switch - that is the interface on SW1 towards router R1.
If it needs to change this range of IP addresses later, it can be done by adding or removing some items from the access list.

Command outputs from switch SW0 and router R0 are shown below.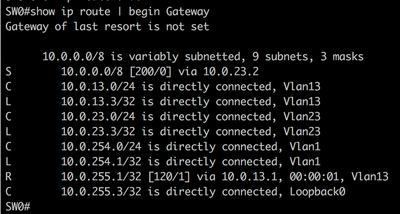

Сommand outputs from switch SW1 are shown below.
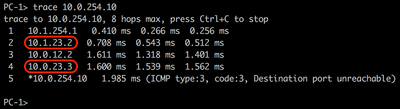
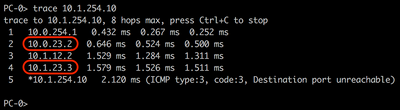
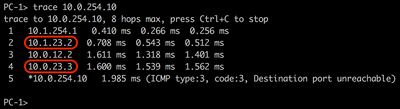
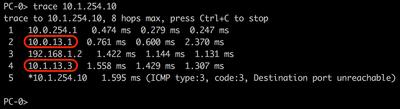
Trace output from PC-1 (10.1.254.10) and PC-0 (10.0.254.10) are shown below.
When the Blb1 device gets available (IP 10.1.255.2), then an event manager applet is triggered on R1 router, and the network returns to its original state.
Network convergence to a temporary scheme and back depends on the configured IP SLA timers, event manager applet timers and RIP timers.
CONCLUSION
The described solution works even the number of branches increases. A traffic bypass in a branch or the HQ if a black box is unavailable in another branch and doesn't affect other ones. IT staff need to monitor the status of network devices using a network management system (NMS) and analyze incidents.
P.S. Congratulations! You have read this article to the end. Уou can find device configurations by links R0, R1, SW0, and SW1.
If you still have any questions after having read this article, please feel free to ask them.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: