- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- SD-WAN Advanced Deployment version 2.0 | Part 2
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
12-17-2021 10:46 PM - edited 12-18-2021 08:34 PM
SD-WAN Advanced Deployment version 2.0 | Part 2
Today we going to write the part two of the SD-WAN Advanced Deployment and will include these :
- SD-Wan Policy
- Application Aware Routing.
- SD-wan Security Features include IPS/IDS services .
- Unified communication Voice
- Integration with Cisco umbrella
- cloud onRamp for Saas
- cloud onRamp for laas
- Software Repository & Upgrade
-----------------------------------------------------------------------
- SD-Wan Policy :-
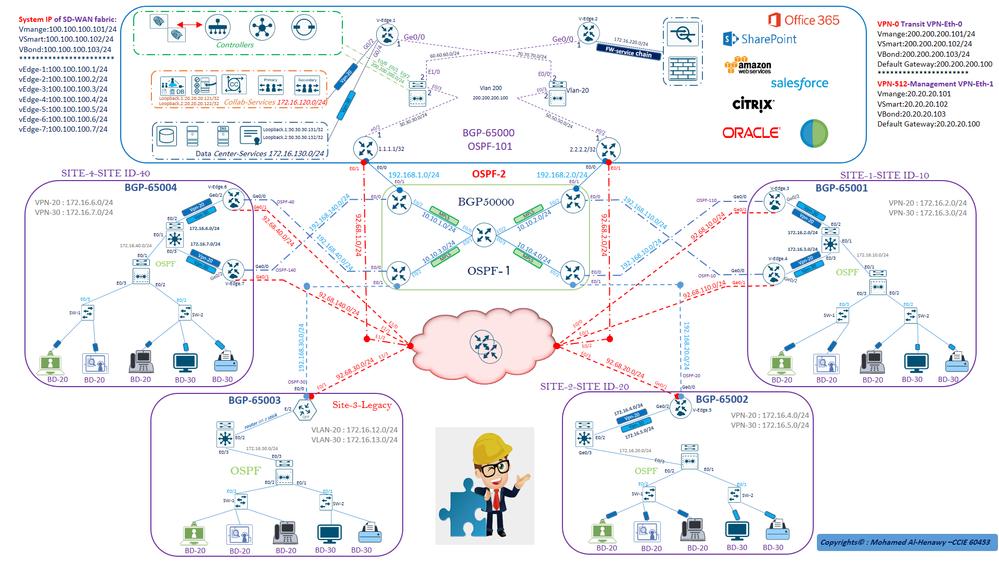
Viptela SD-WAN classified two types ( centralized policies or localized policies ) .
- The difference between ( centralized policies or localized policies )
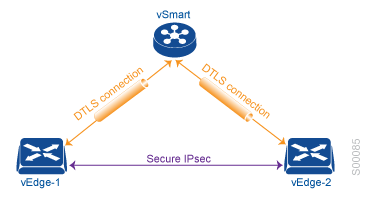
Centralized policies : Those policies that are applied on the vSmart on the overlay network.
Localized policies : Those policies that are applied locally on the vEdge routers on the overlay network .
Centralized policies has two polices ( Control Policy and data Policy )
Localized Policy : Pushed from vManage directly to Edge devices via a NETCONF transaction – affects will happened for specific devices requiring policies.
Centralized Control policies :- Used to manipulate the propagation of routing information in the control plane including OMP, TLOC, VPN Services .
Centralized Data policies : Commonly used to accomplish (DIA) for specific applications, network service insertion, Also data plane manipulations such as packet Forwarding Error Correction (FEC) .
NOTE : In traditional wan , configurations are typically applied on a device thorough CLI but cisco SD-WAN is came with a new era of the network which's SDN and it has been designed to overcome this by implementing a centralized management plane that implement on all devices without any human error.
NOTE : Before Appalling any policy please be consider this all vEdges routers will sent the local site network to vSmart controller via OMP protocols , All vEdges will send all TLOC routes to vSmart controller via OMP , All vEdge Router will send all service Routes to all vSmart via OMP.
- Application Aware Routing
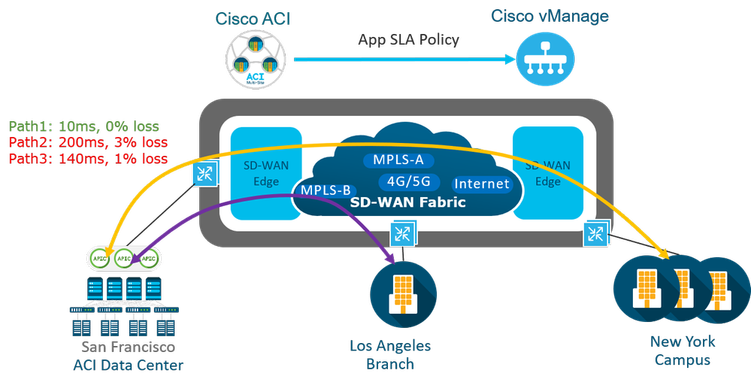
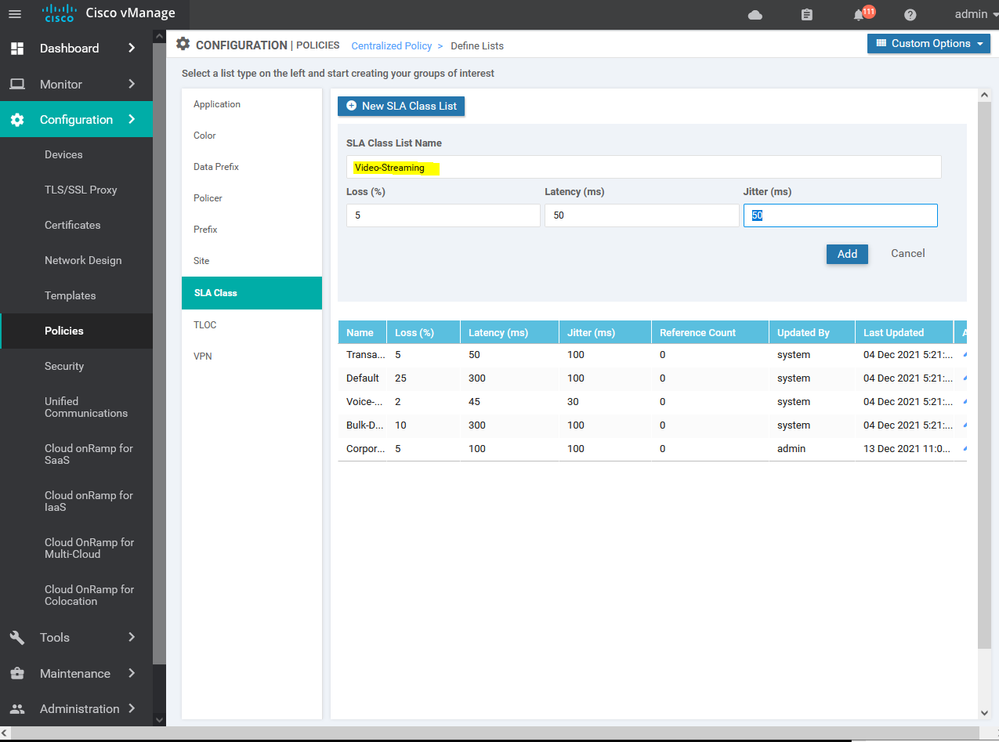
Application-Aware Routing is identify business critical traffic and specify the required SLA for that traffic classified . Viptela SD-WAN provides the ability to use multiple transports such as MPLS , BIZ-Internet, broadband , Etc... more than one method with high availability which 's will effect to the cost and operation . It provides the ability to use intelligent method through SLA detection for the application to used different transports based on the status .
Application-aware routing directs traffic based upon an application SLA LIST parameters and this defined application policies done though the vmanage and push to vSmart then to all SD-wan fabric Traffic is automatically sent to WAN links that have the important network characteristics and meet the SLA conditions to support these applications in production .
- SD-wan Security Features include IPS/IDS services
As we know the security is a critical part of today's networking infrastructure , Cisco Viptela SD-WAN align it self with this and from version 18.0 to latest version 20.6 the intrusion prevention/intrusion detection systems and URL filtering is available , and can apply this services for all the SD-WAN fabric .
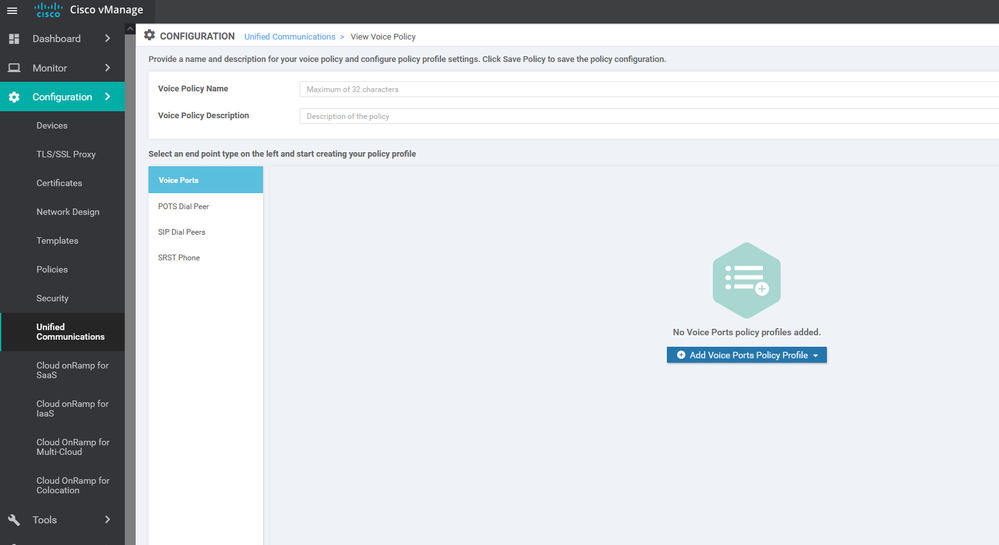
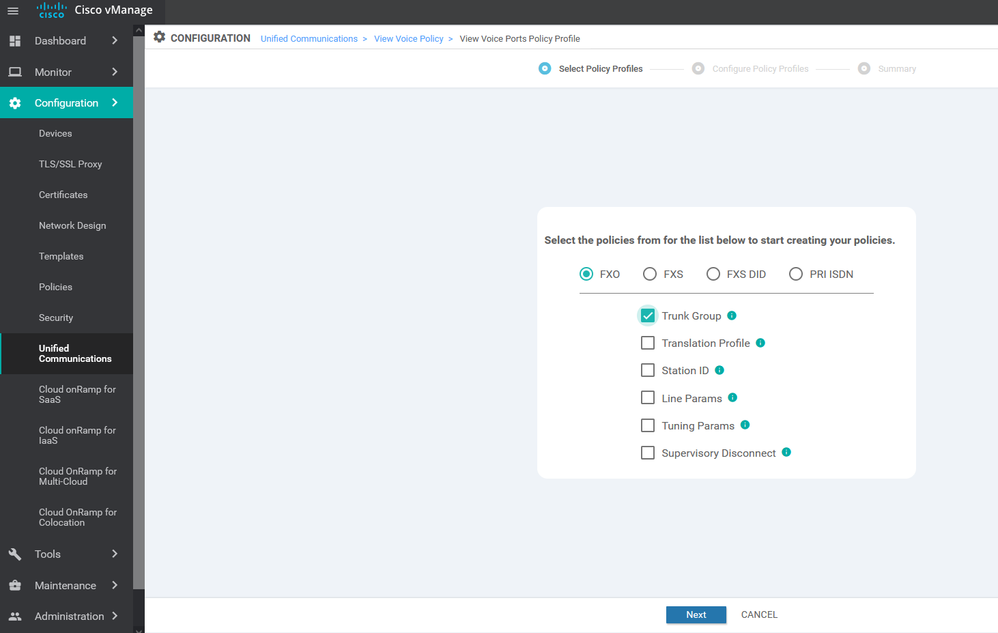
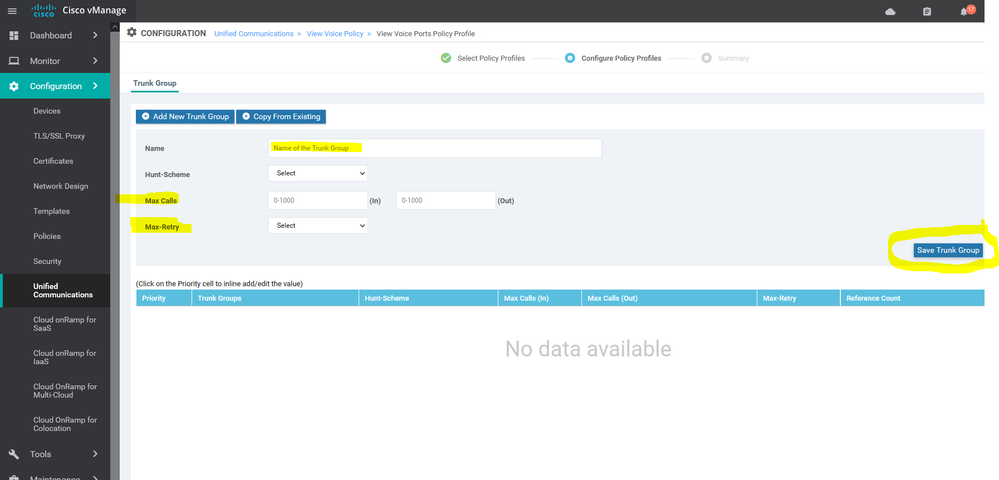
- Unified communication Voice
Cisco Unified Communications requires that Cisco vManage be running Cisco SD-WAN Release 20.1. You can configure feature templates and voice policies to enable Cisco Unified Communications voice services for supported routers. These templates and policies configure parameters for FXO, FXS . When Cisco voice services are enabled, routers can process calls for various endpoints, including voice ports, POTS dial peers, SIP dial peers, and phone profiles in Cisco Unified Survivable Remote Site Telephony mode. Also voice policy defines how the system define and manipulates calls for various endpoint types. Endpoints include voice ports, POTS dial peers, SIP dial peers, and Survivable Remote Site Telephony .
- Integration with Cisco umbrella
The security, availability, visibility, and performance of the IT sector are the key foundation of a solid business and service environment.
- what you will do if the attacker pivots and enter your network infrastructure to get your sensitive data, attackers need to register with your domain to start his attack, all of this will happen once you respond to the incident.
NOTE: You can get the Cisco umbrella solution in your enterprise within 10 minutes .
- Integration With cisco DNAC :-
Cisco DNA enables a blend of typical routing Lisp , BGP, DNS, etc. and security MACsec, ACLs, etc. capabilities for routing-only deployments for any organization. The network is managed by either Cisco DNA Center or vManage. Each is a single, centralized management console to monitor and manage the entire network , Cisco DNA can manage the WAN and security part and SD-WAN to manage the WAN side and Applications which's based on the cloud .
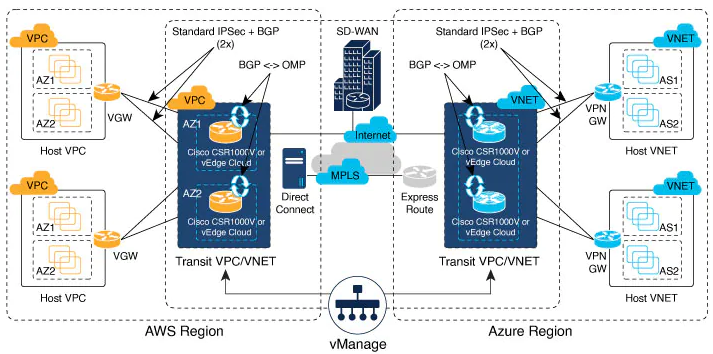
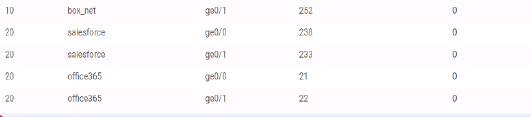
- cloud onRamp for Saas & laas :-
Cloud OnRamp for SaaS optimizes the performance of Software as a Service (SaaS) cloud applications based on network loss and latency SLA . Cloud OnRamp for SaaS provides clear visibility of the performance of individual applications and automatically chooses the best path for each one even MPLS , BIZ-Internet , 4 G Etc...
Although Cloud onRamp addresses both IaaS and SaaS providers, it's operate for the two types of cloud. With IaaS providers, such as AWS and Azure , Cloud OnRamp for SaaS calculates a value called the Viptela Quality of Experience , you also enable Cloud OnRamp for SaaS on the gateway site , viptela support some of the application now such as Microsoft Office 365 , oracle , sales forces , Zoho , Etc...
Cloud OnRamp for IaaS you can read more helpful details here :
The Cloud onRamp for IaaS works in conjunction with AWS virtual private clouds (VPCs) and Azure virtual networks (VNets). The following image provides a high level overview of multi-cloud onRamp for IaaS.
Let's start the configuration for SD-WAN advanced deployment :-
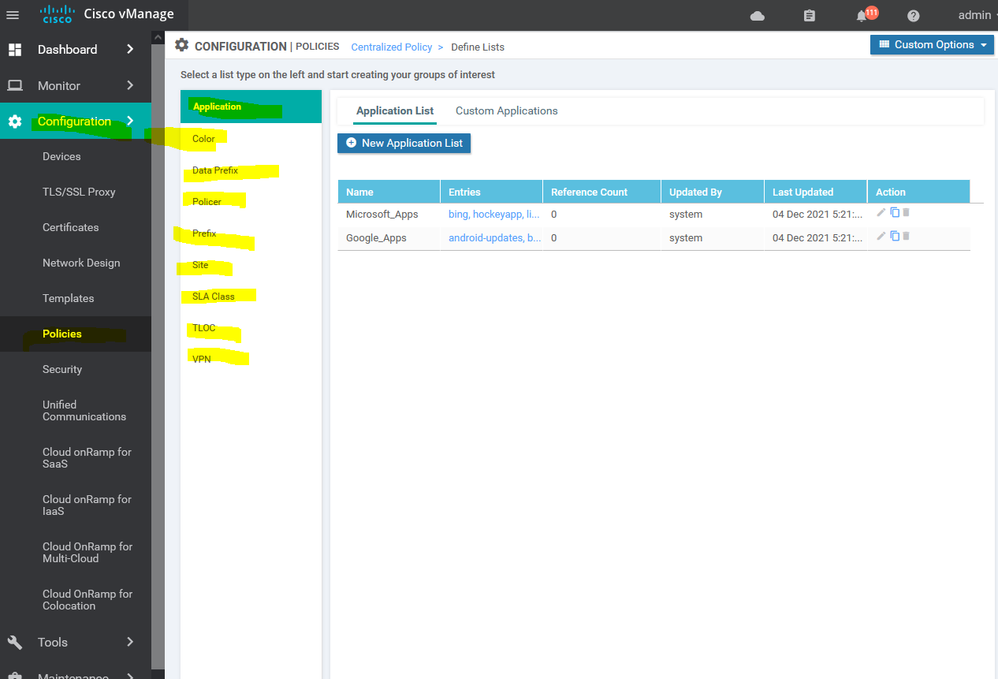
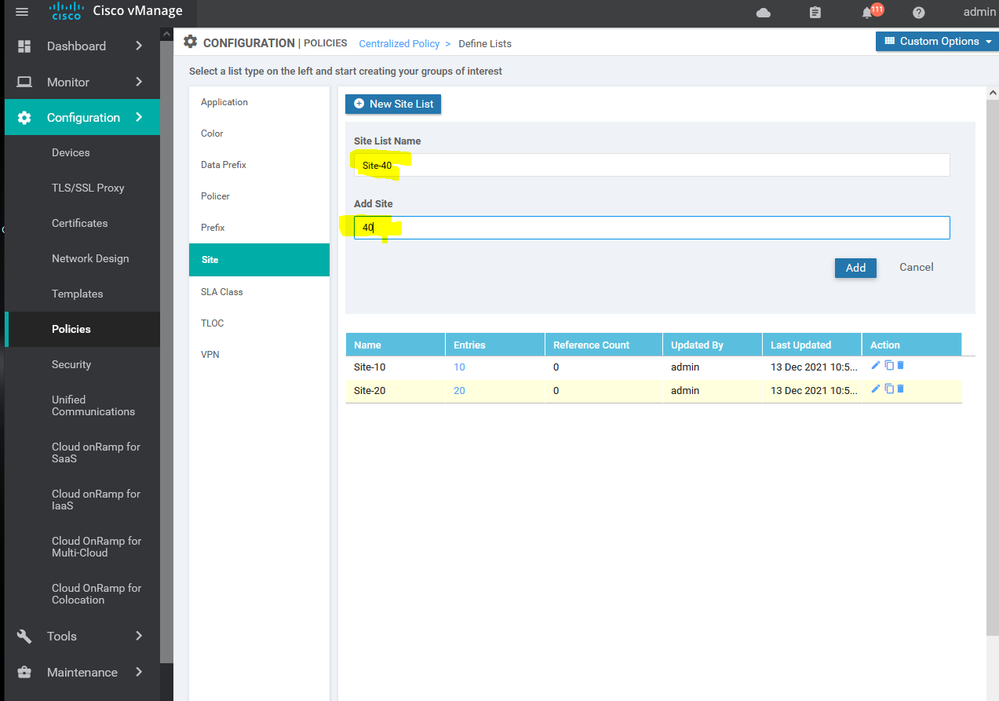
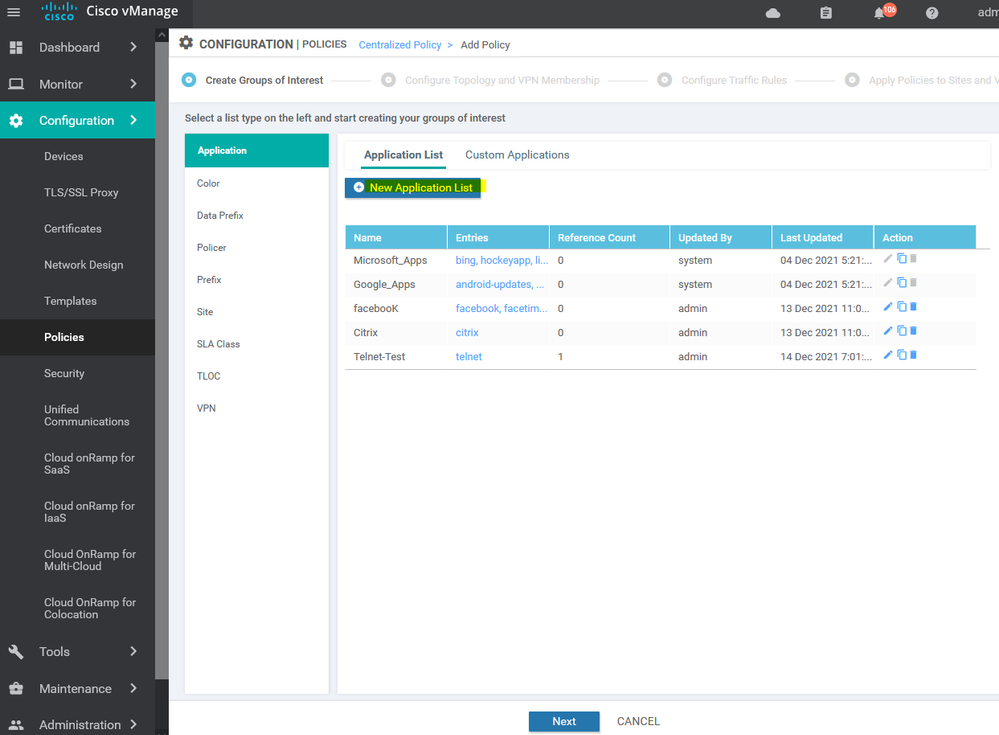
To create Policy we need some elements such as Site list , App list , VPN list , ETC...
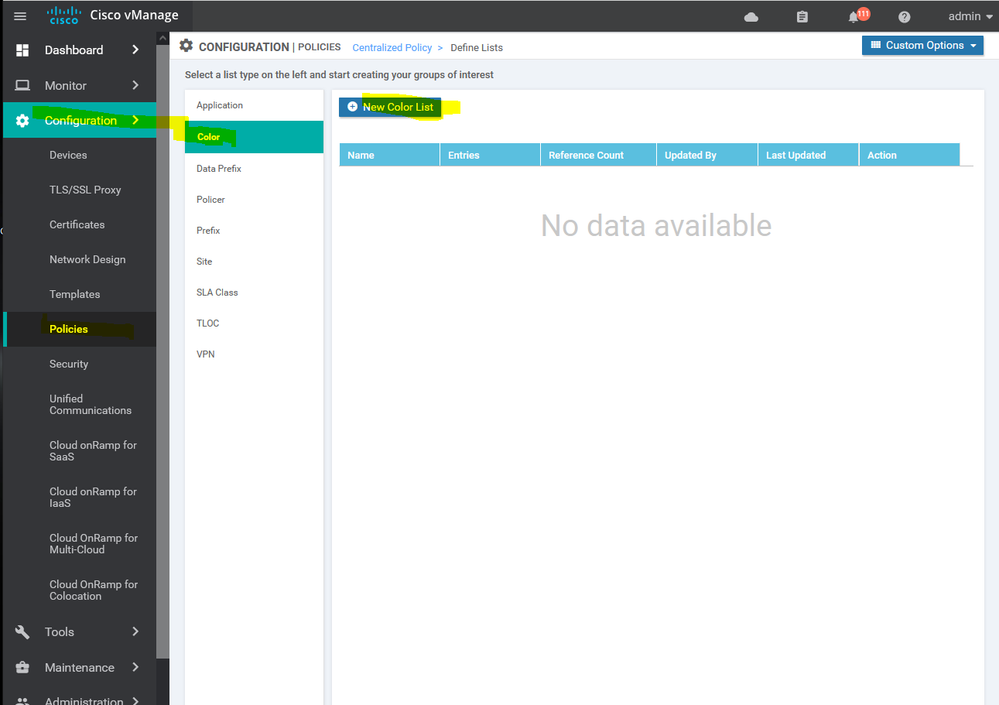
To create list Configuration > Policy > Customize options > Centralized policy > List > select from the list APP, VPN, Site Etc...
To create list Configuration > Policy > Customize options > Centralized policy > List > select
To create site list Configuration > Policy > Customize options > Centralized policy > List > site
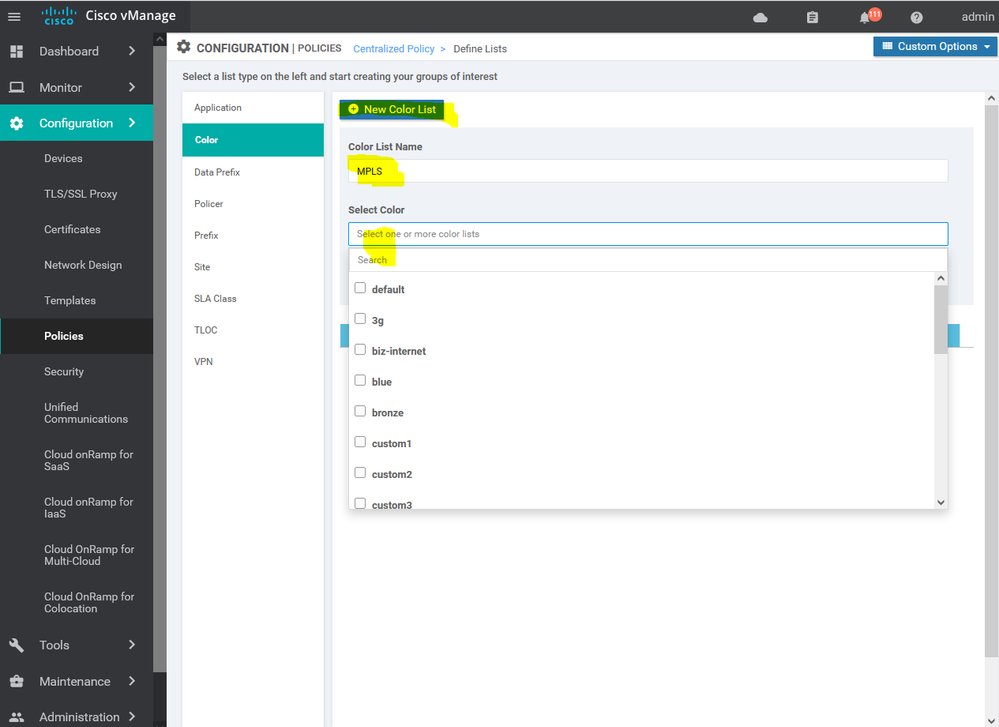
To create Color list Configuration > Policy > Customize options > Centralized policy > List > select color
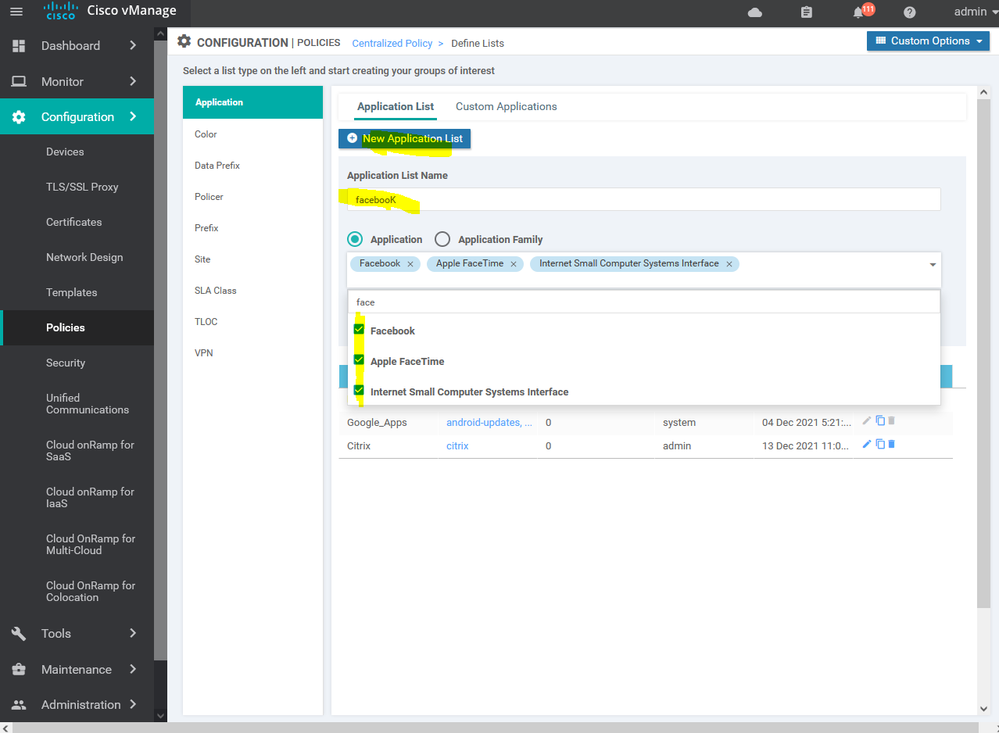
To create list of application Configuration > Policy > Customize options > Centralized policy > List > select application
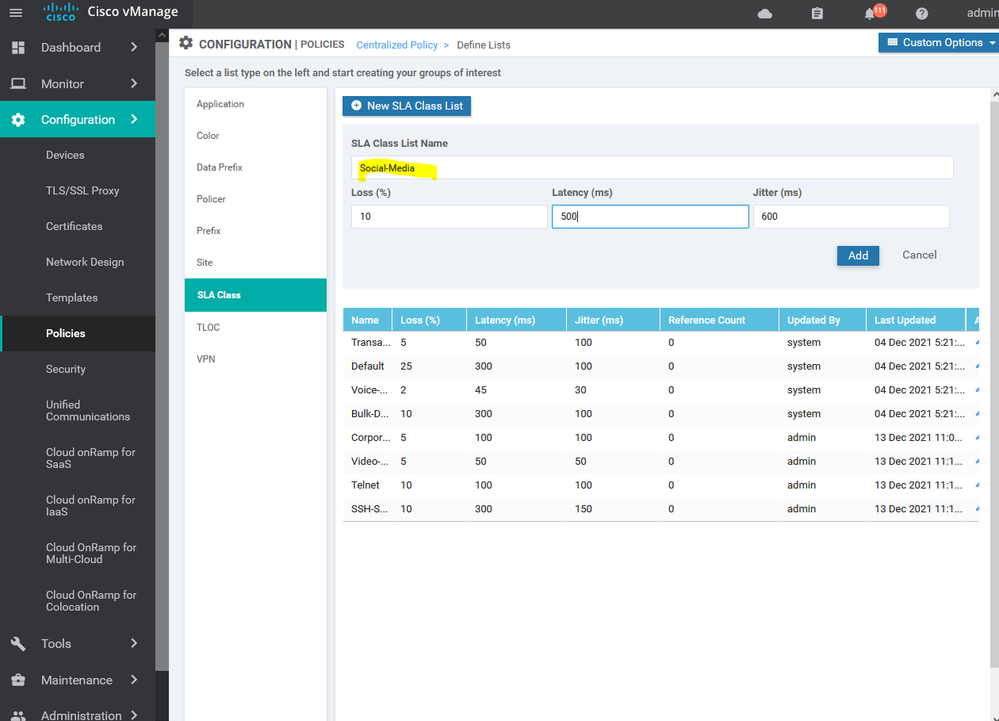
To create list of the Service level agreement SLA Configuration > Policy > Customize options > Centralized policy > List > SLA
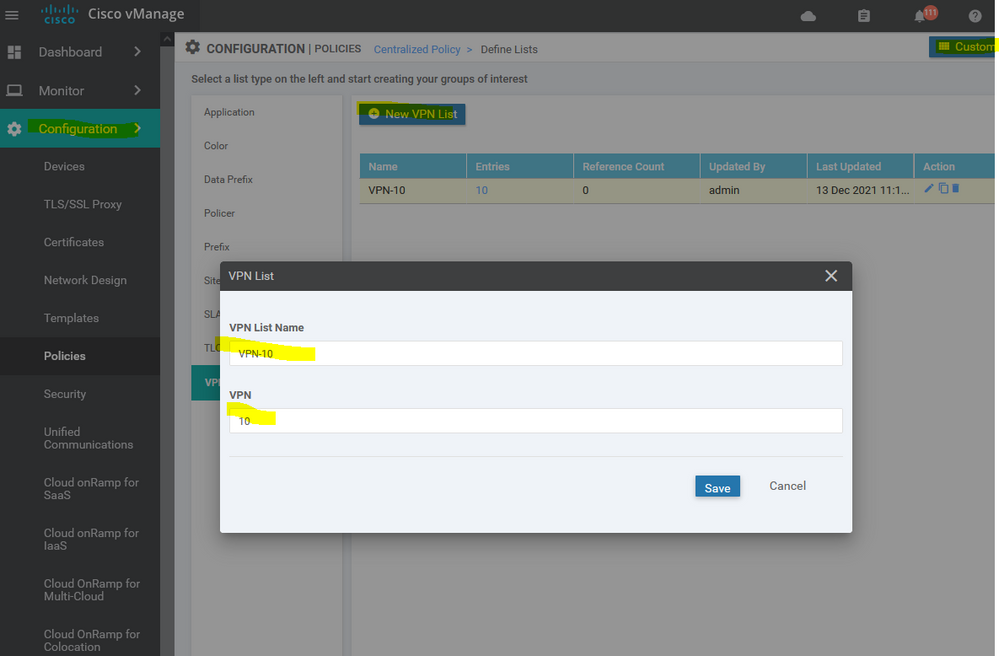
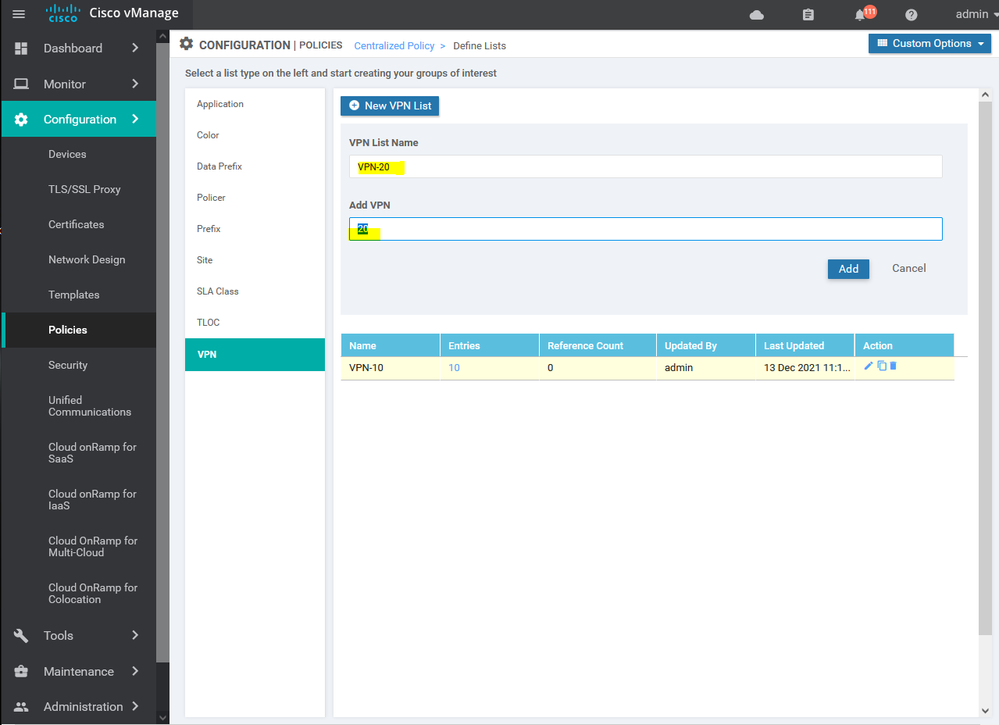
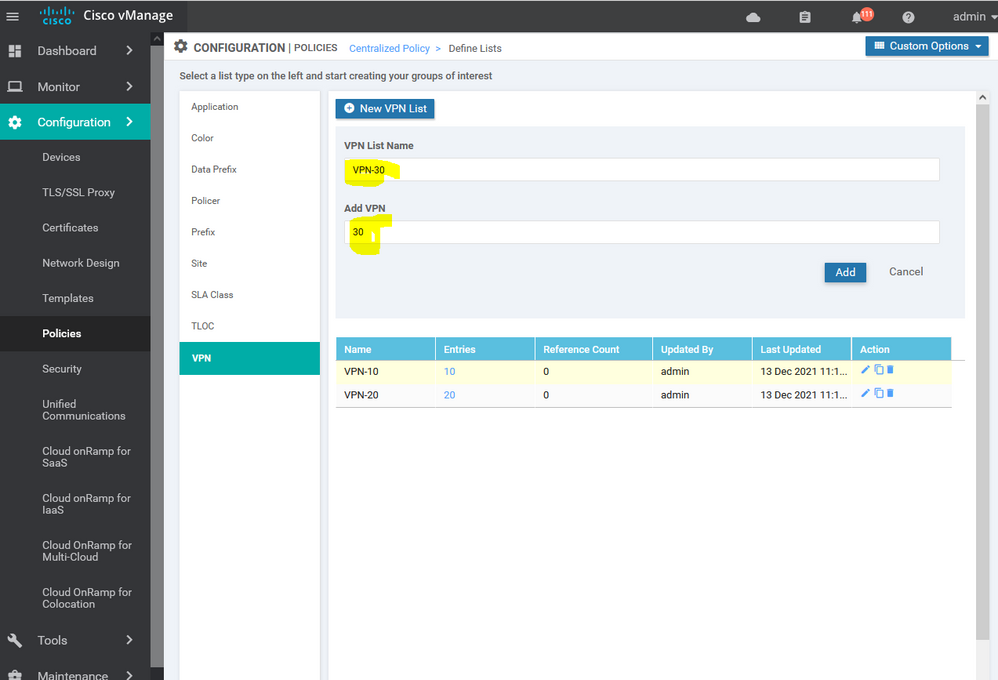
To create list of VPN Configuration > Policy > Customize options > Centralized policy > List > select VPN
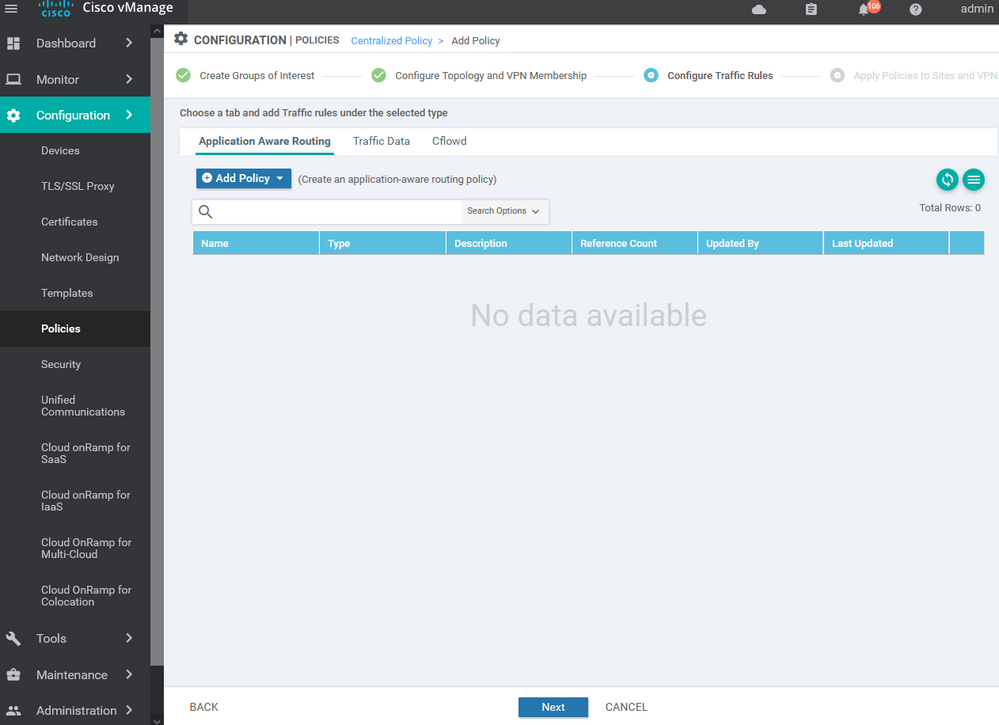
To create Policy and add all of the lists and elements of the policy Configuration > Policy > Customize options > Centralized policy > ADD
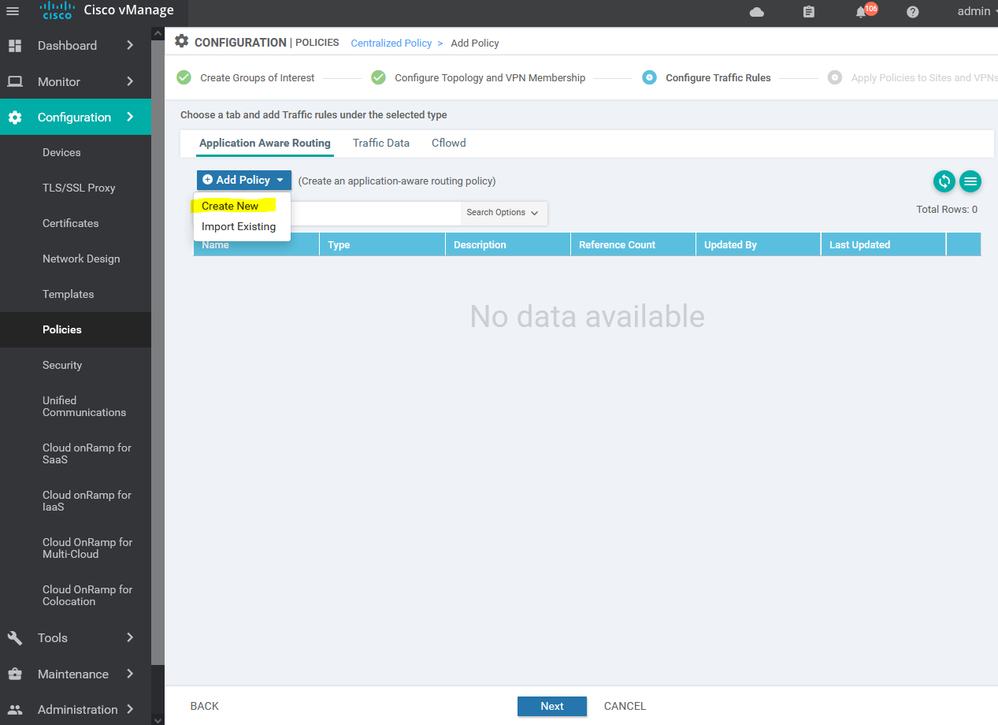
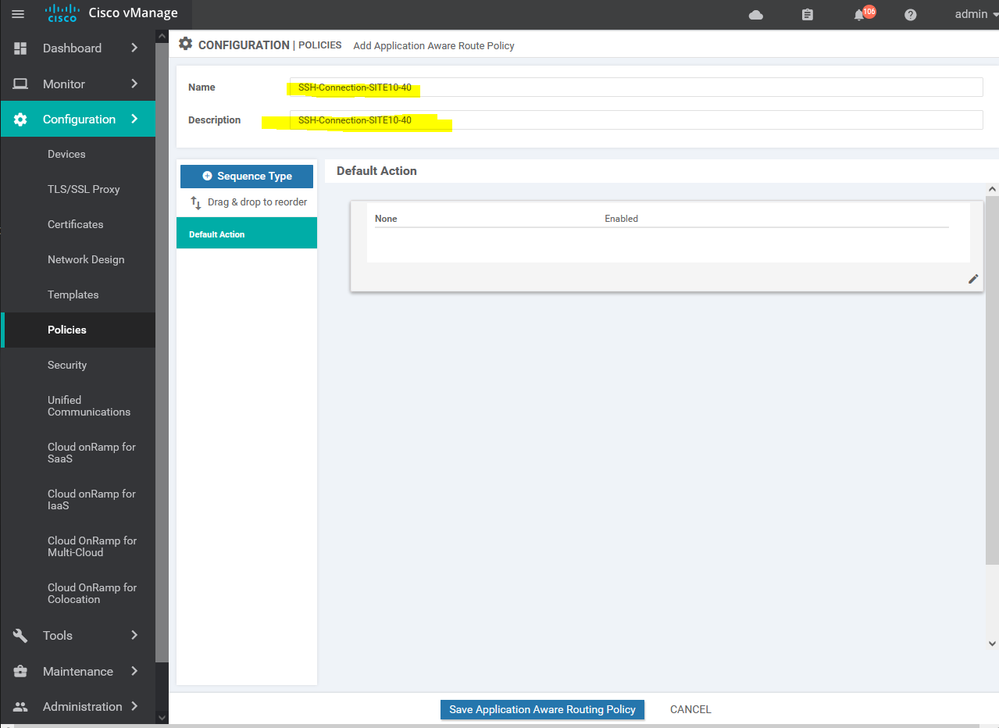
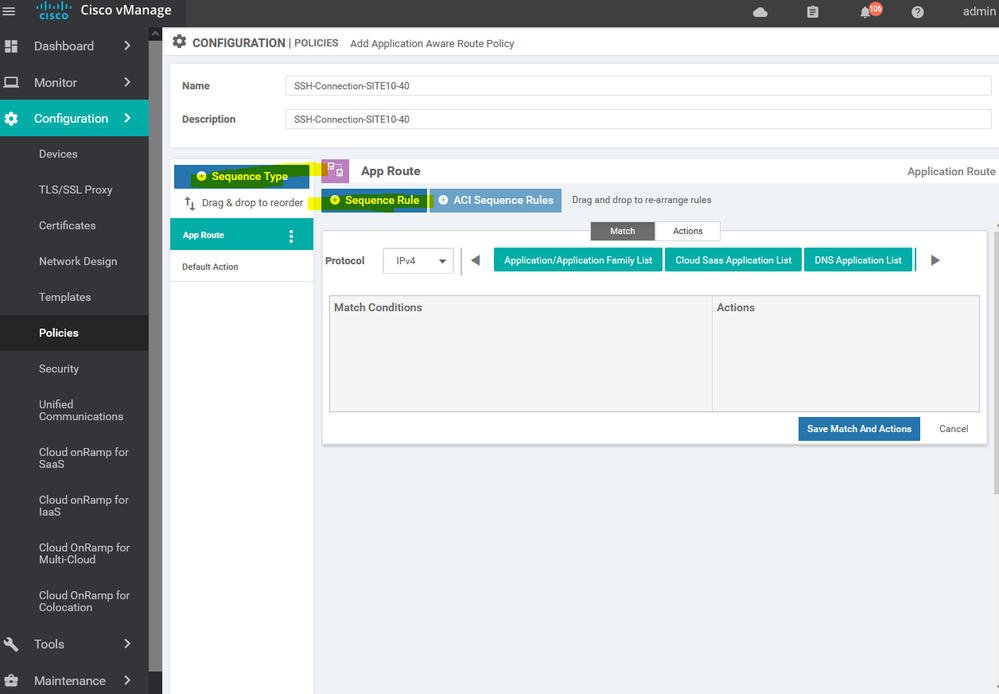
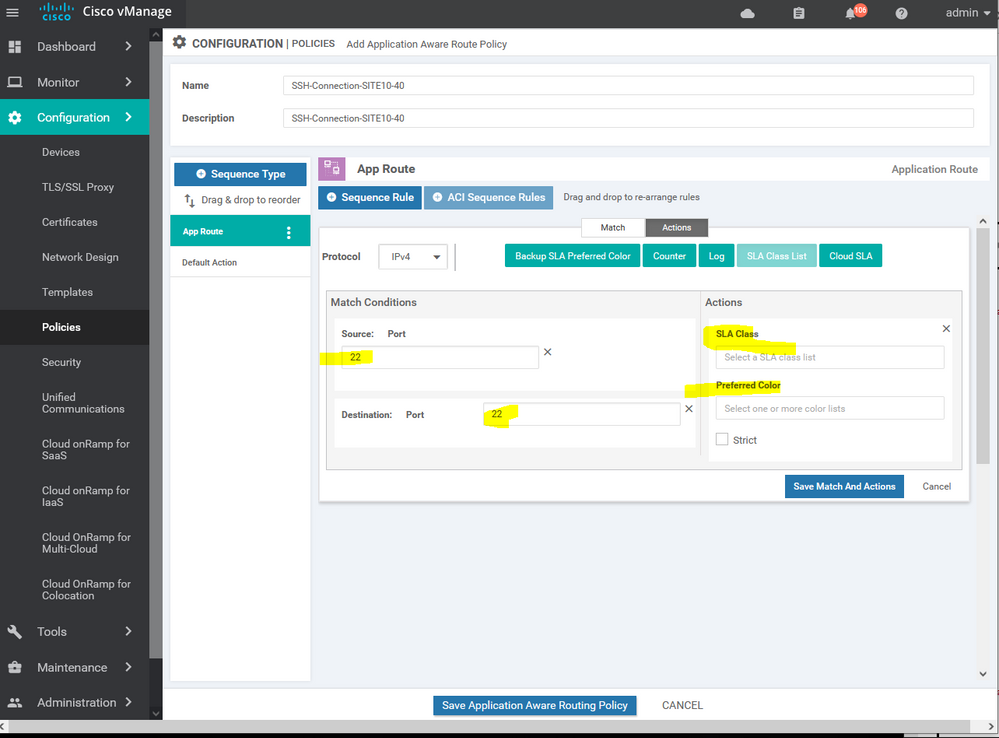
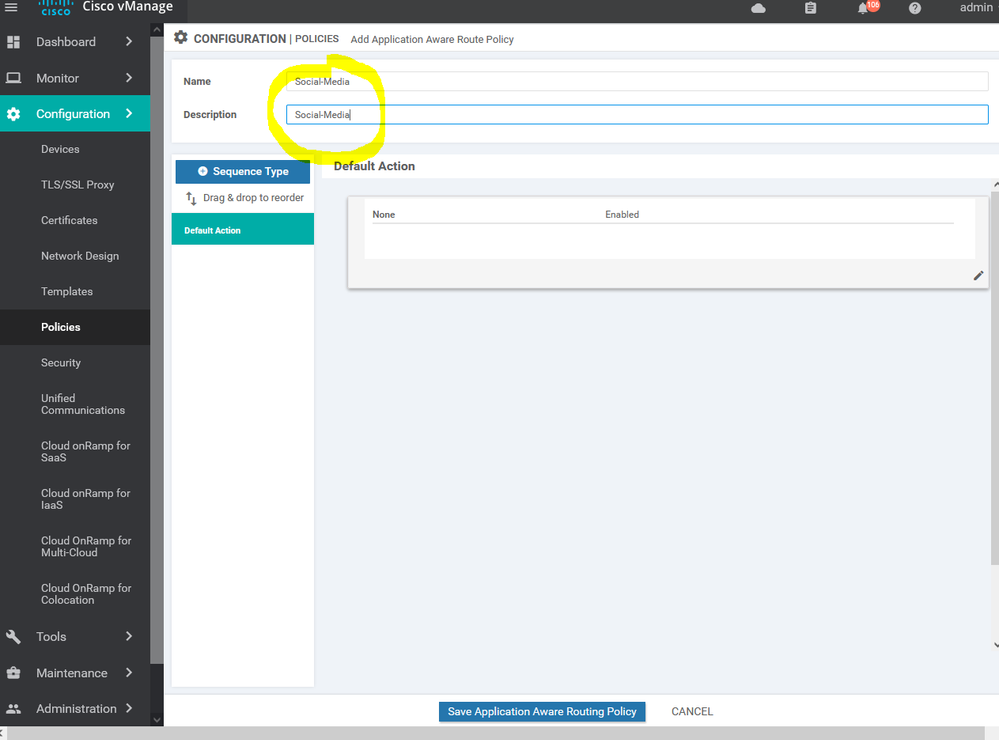
To create new application aware routing Configuration > Policy > Customize options > Centralized policy > ADD new policy > next > next > application aware routing > add policy > create new
NOTE : the default App route is allowed in version 20
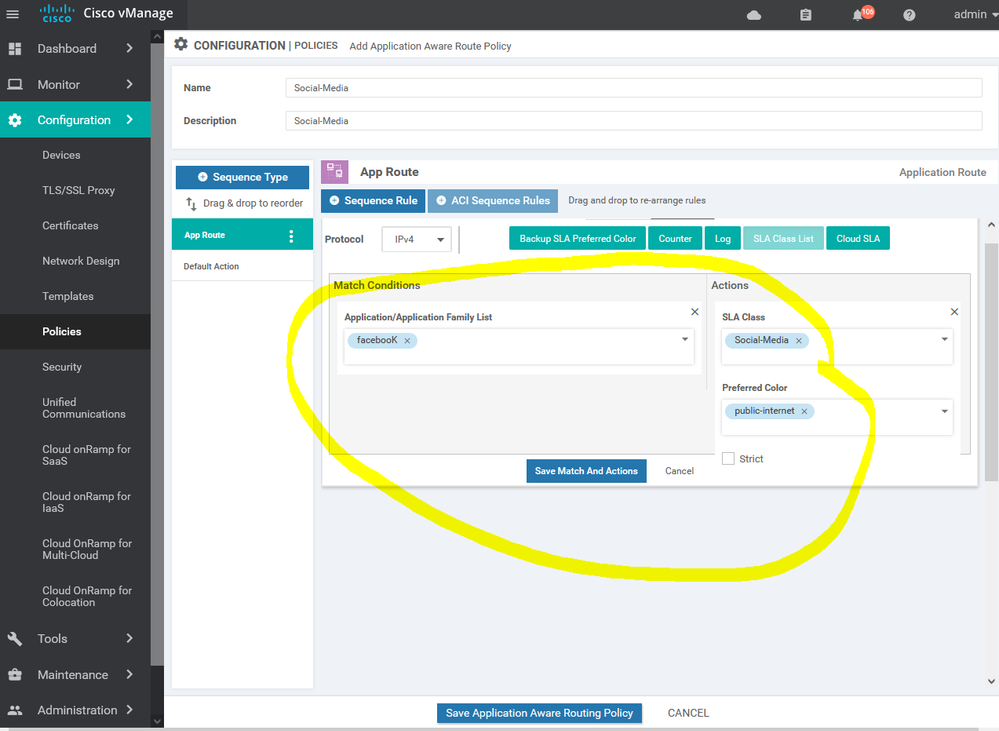
Here we using the SSH SLA which's including the percentage of the latency and jitter , ETc...
Here we using the MPLS for the SSH services and BIZ-Internet as a secondary if the MPLS is down
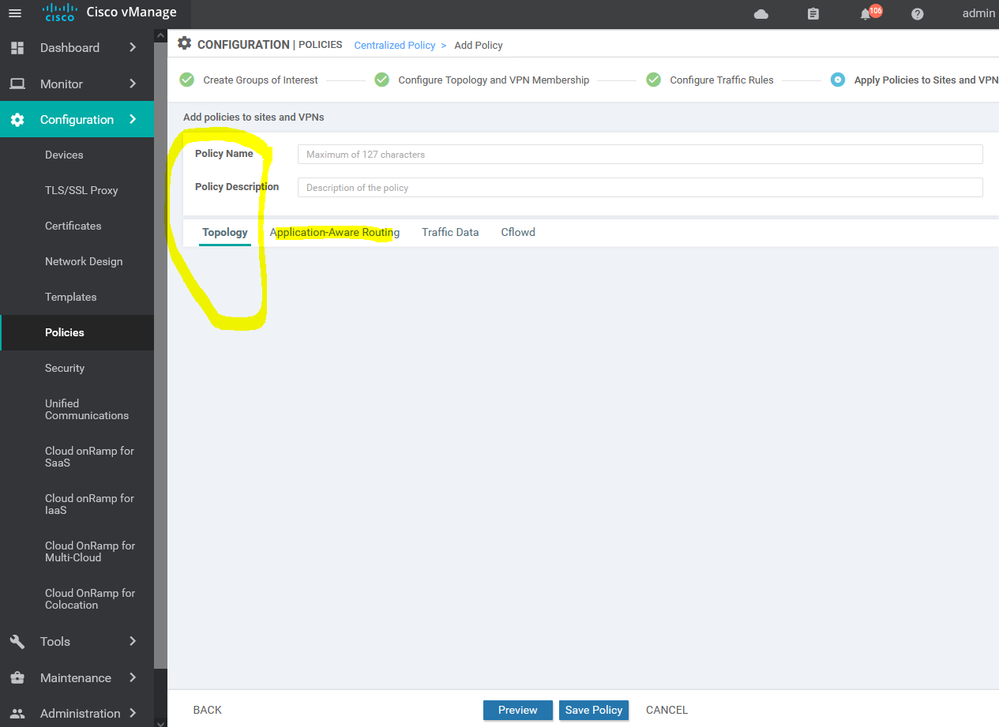
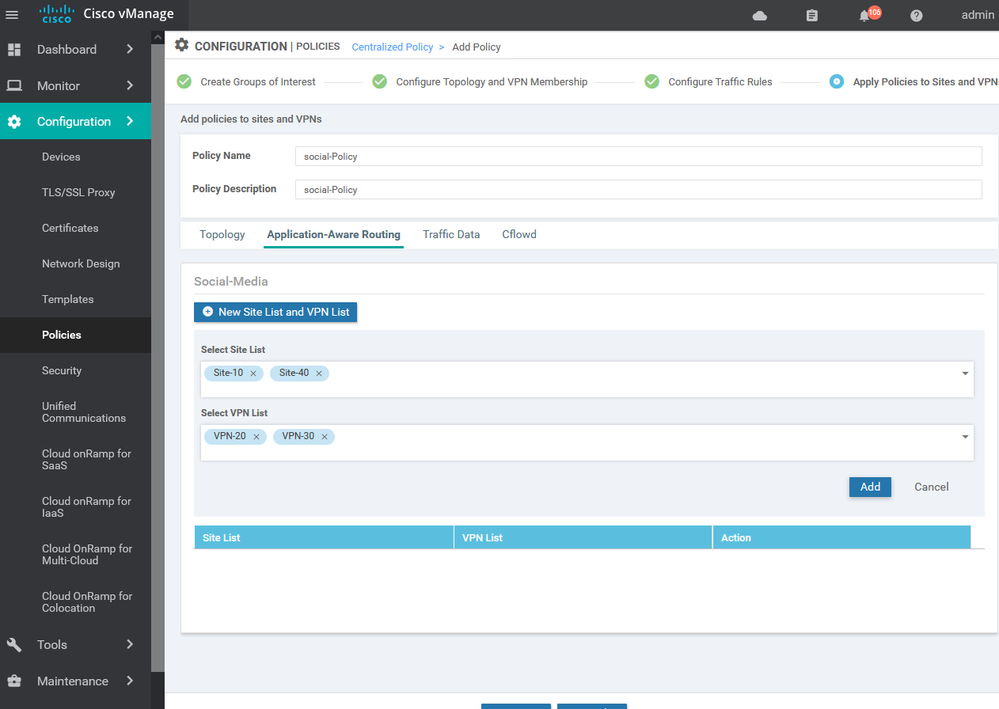
after creating the APPAR import the site list and vpn services list
To activate the policy press ... and choose activate .
NOTE : only one centralize policy can run in the real time .
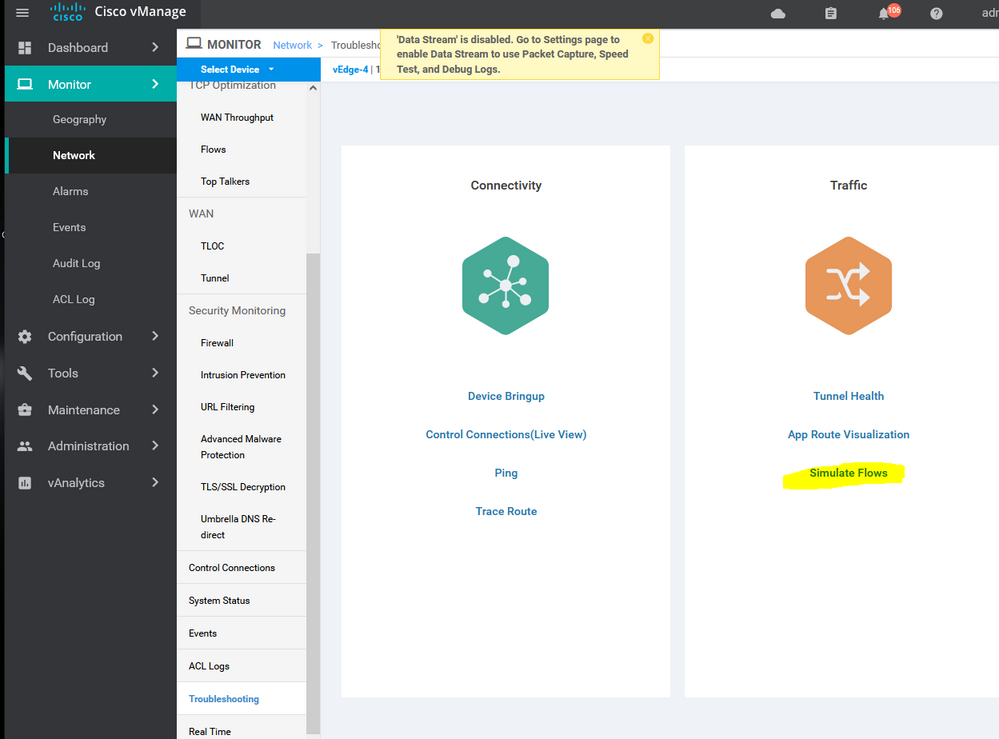
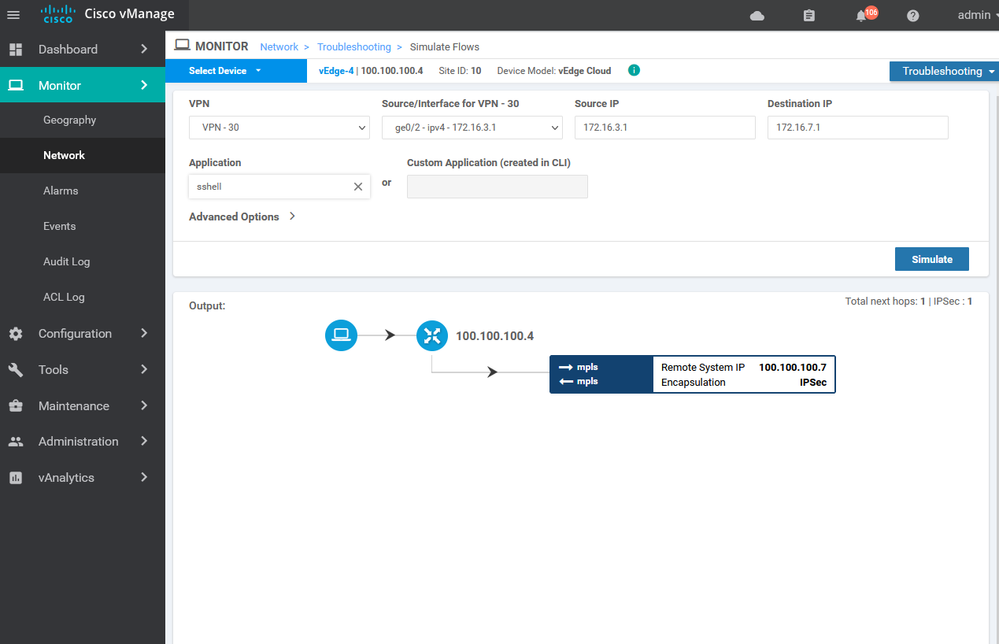
Verification :
Create new Application aware routing for social media : -
Choose the internet as the primary transit with specific SLA for each application : -
Choose the VPN services which will apply this policy for it .
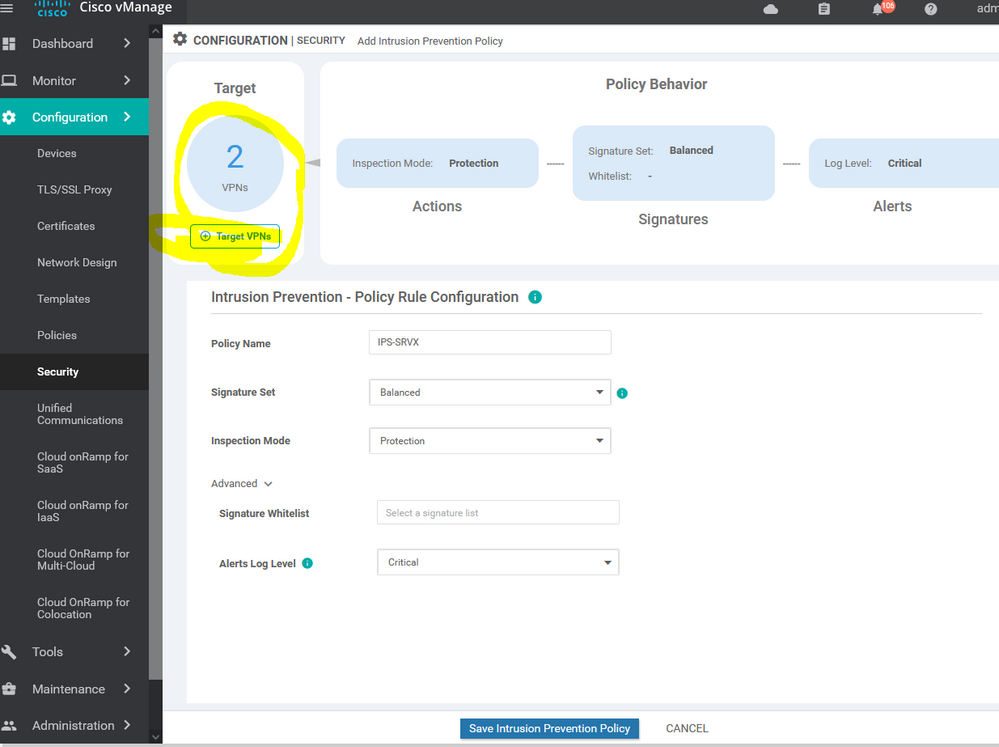
Viptela SD-WAN Security policy IPS/IDS services
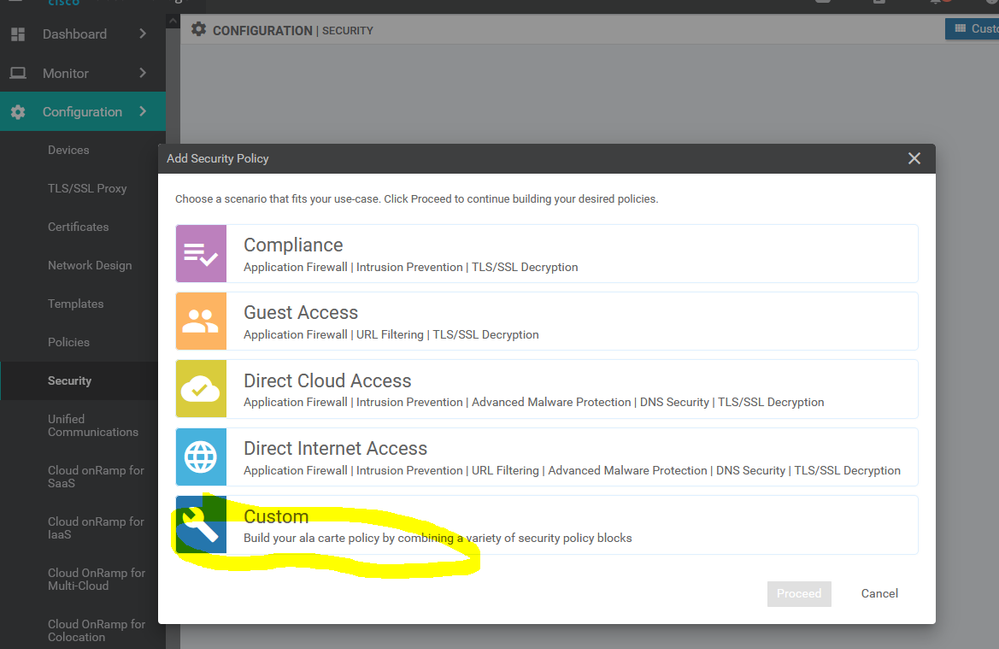
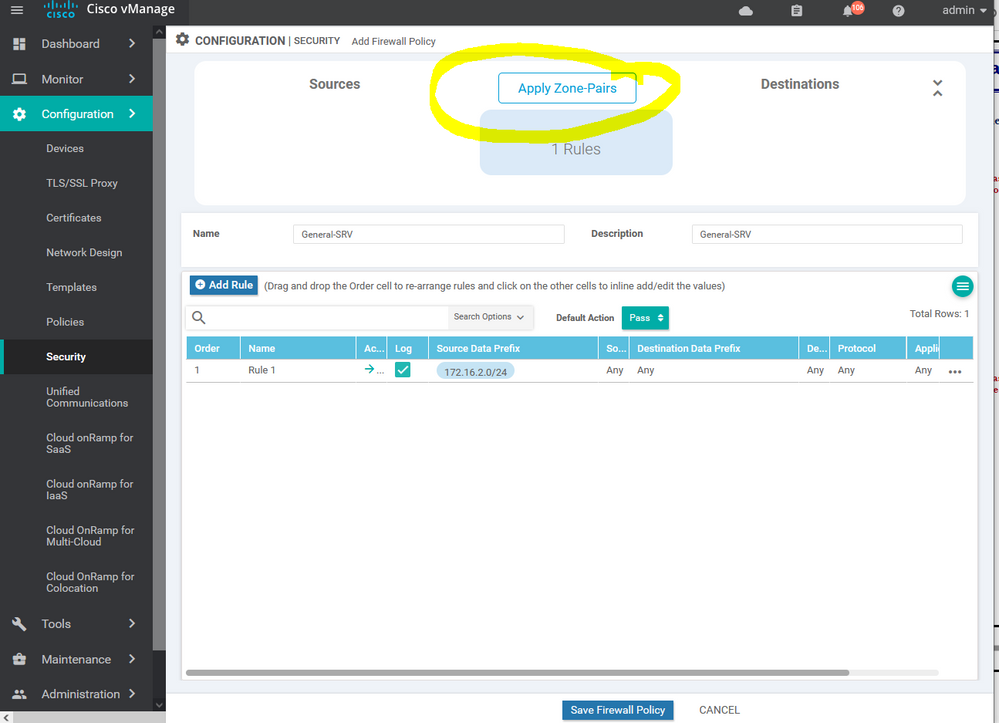
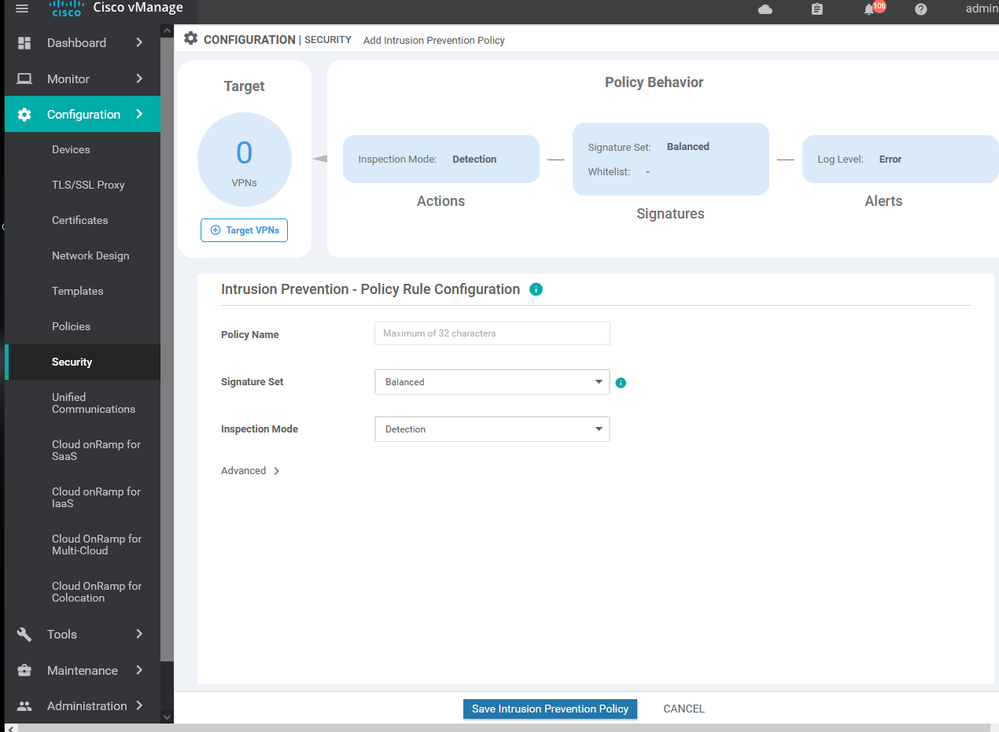
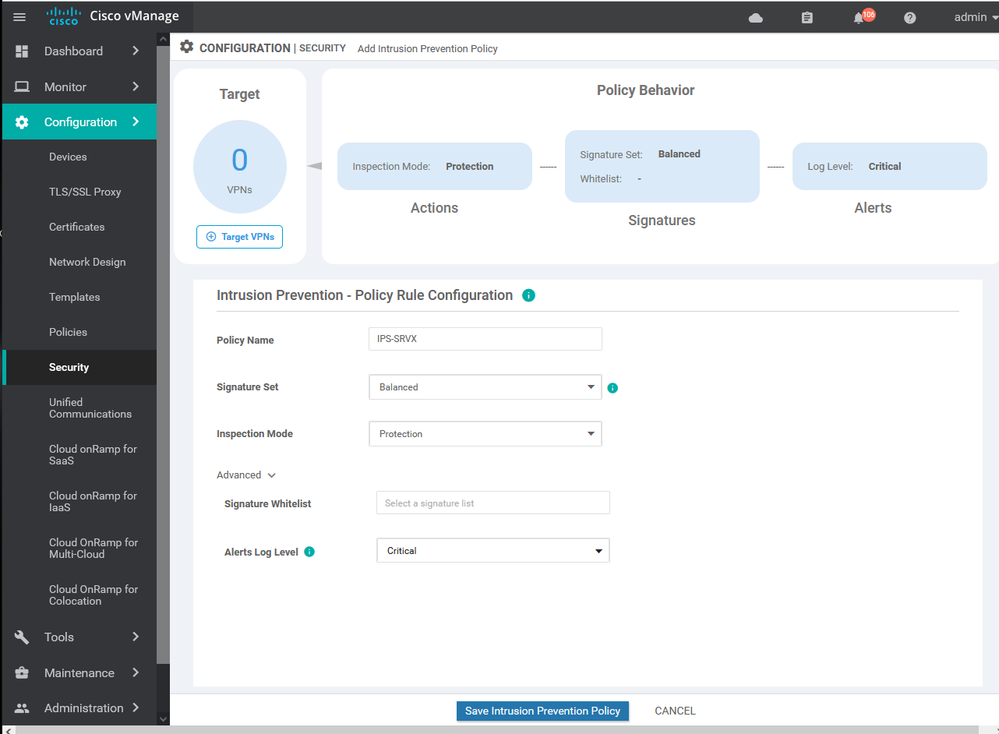
To create IPS/ IDS Services Configuration > Security > Add security policy > Custom >
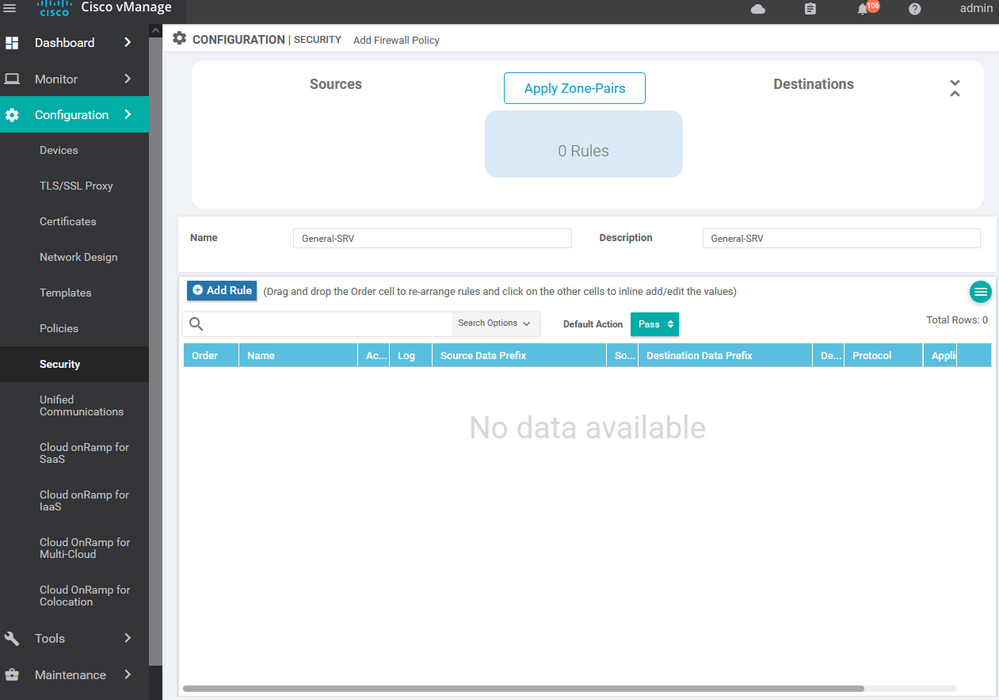
To create IPS/ IDS Services Configuration > Security > Add security policy > Custom > create new
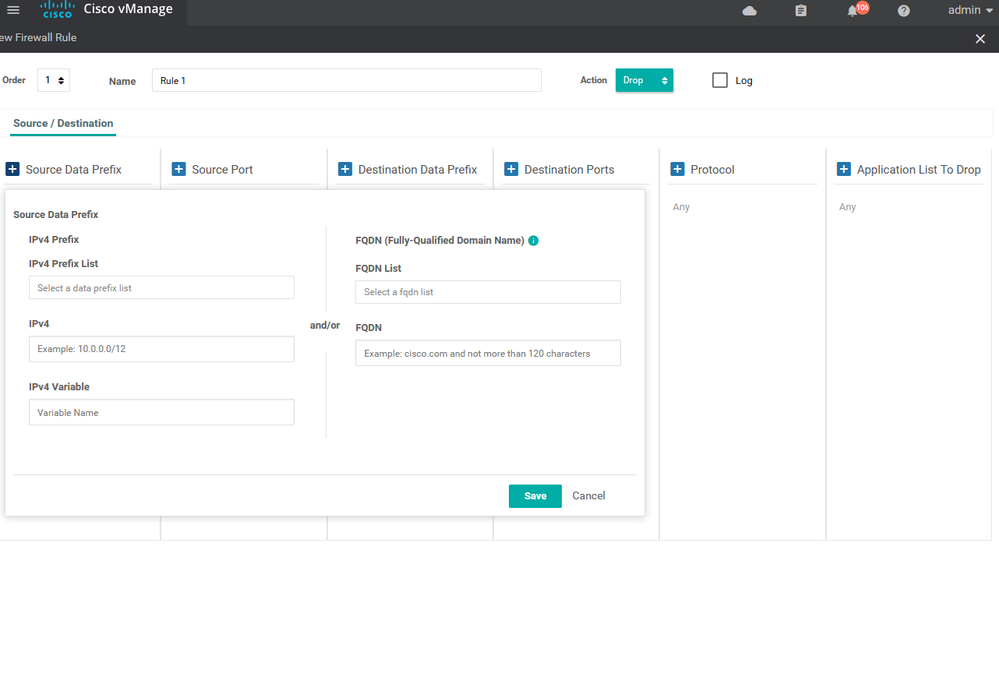
To create IPS/ IDS Services Configuration > Security > Add security policy > Custom > create new > Add role
To create IPS/ IDS Services Configuration > Security > Add security policy > Custom > create new > Add role > choose source and destination and port and protocols
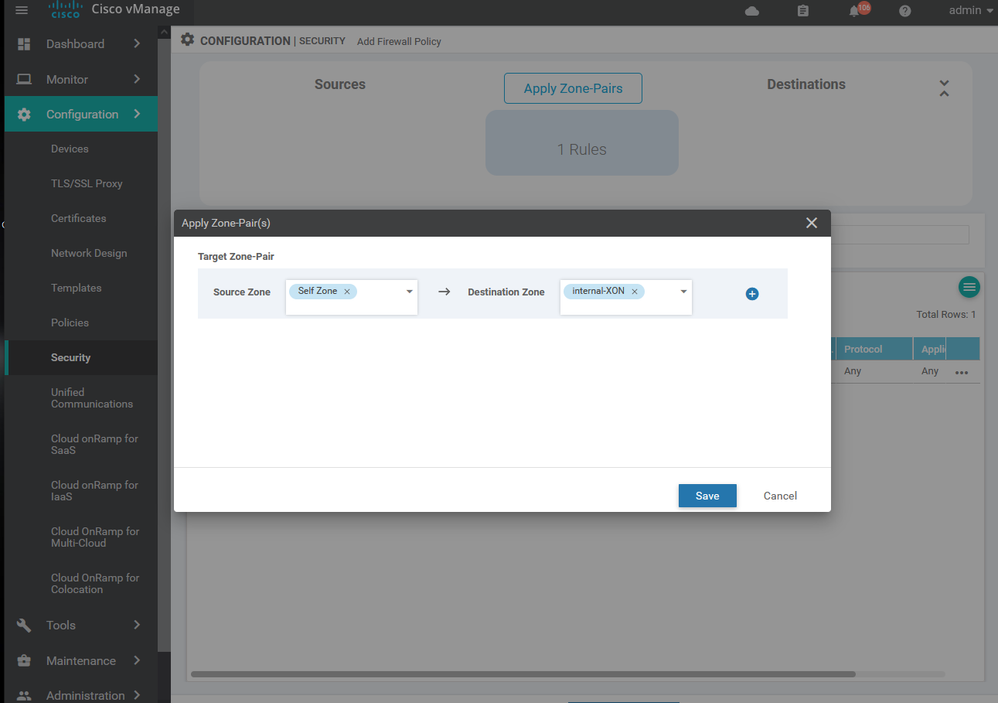
To create IPS/ IDS Services Configuration > Security > Add security policy > Custom > create new > Add role > choose source and destination and port and protocols> then apply to specific zone .
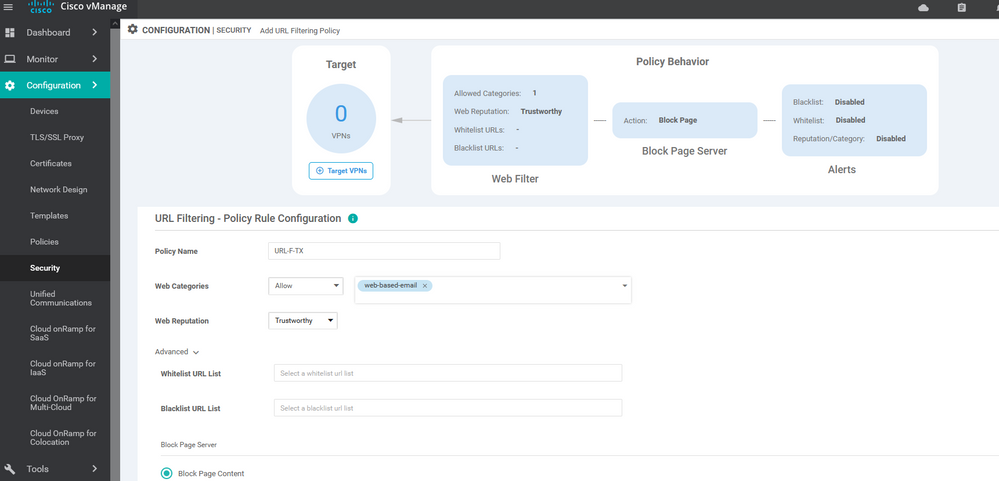
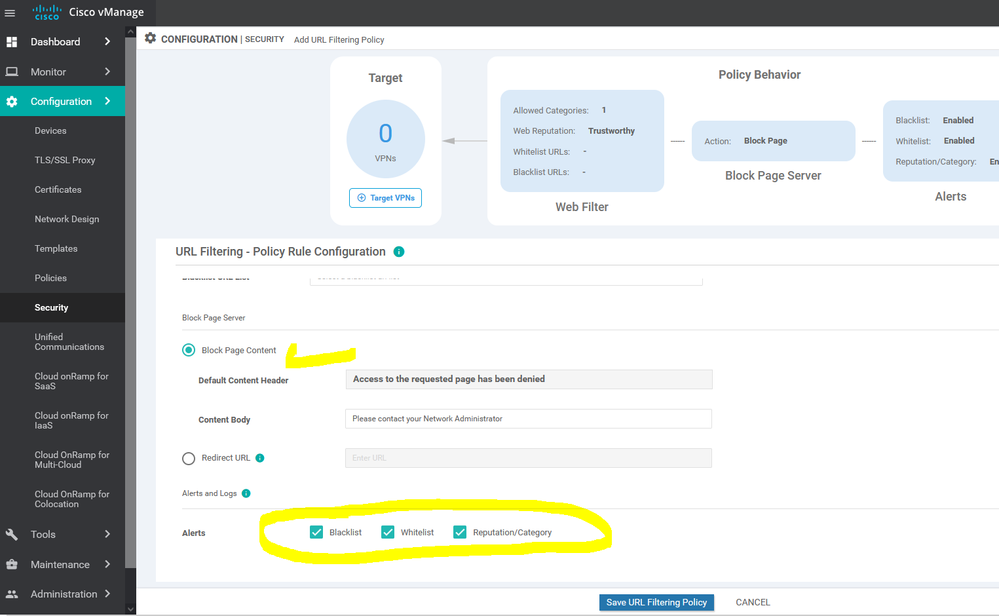
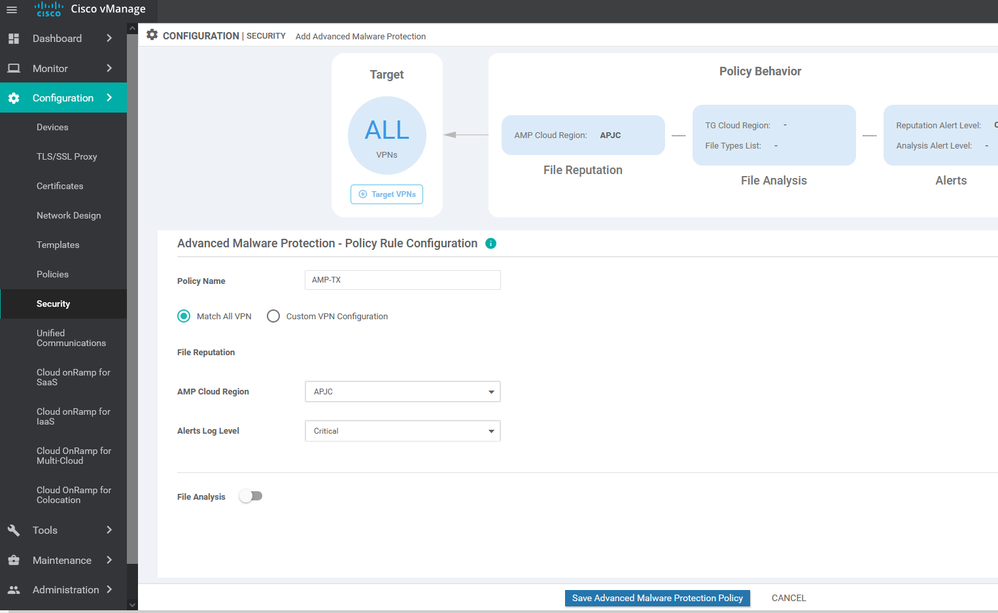
policy intrusion-prevention IPS-IDS security-level security inspection-mode detection log-level alert target-vpns 30 20 10 ! url-filtering URL-F-TX web-category-action allow web-categories travel uncategorized unconfirmed-spam-sources violence weapons block-threshold trustworthy block text Access to the requested page has been denied. Please contact your Network Administrator alert categories-reputation blacklist whitelist target-vpns 30 20 10 ! advanced-malware-protection AMP-TX file-reputation-cloud-server cloud-isr-asn.apjc.amp.cisco.com file-reputation-est-server cloud-isr-est.apjc.amp.cisco.com file-reputation-alert critical target-vpns matchAllVpn ! ! failure-mode open
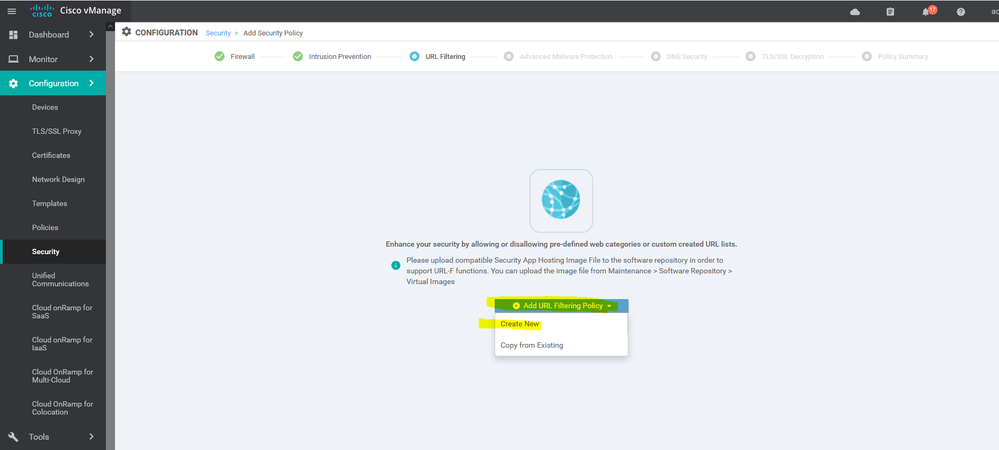
To create URL filtering configuration > Security > Add new > create > Next > next > URL filtering >
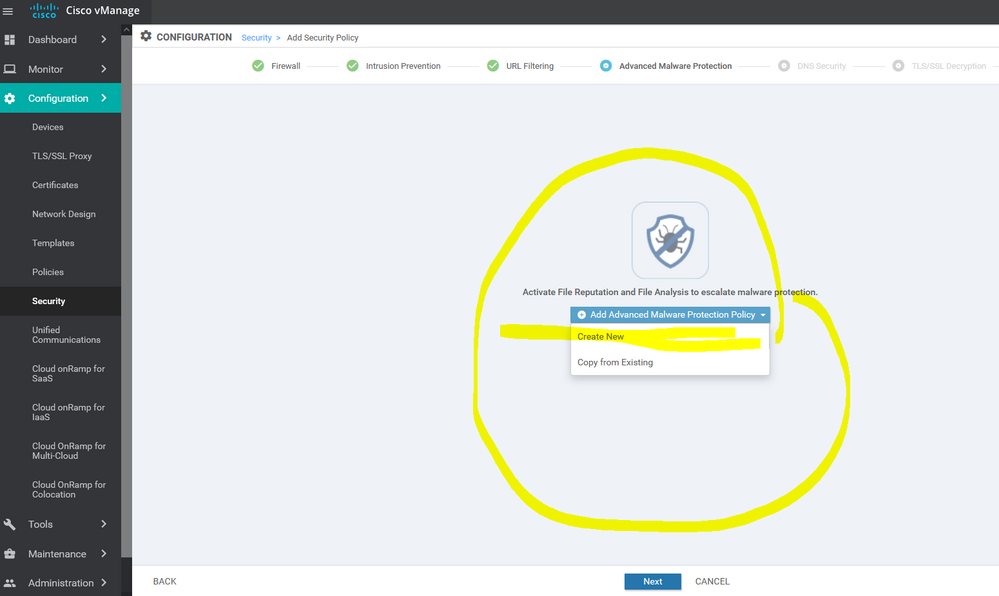
To create URL filtering configuration > Security > Add new > create > Next > next >next > Advanced Malware protection > create new
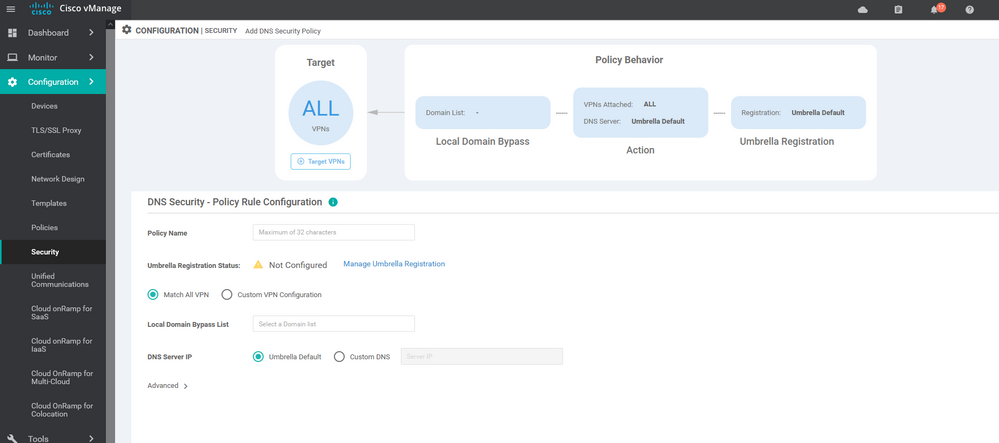
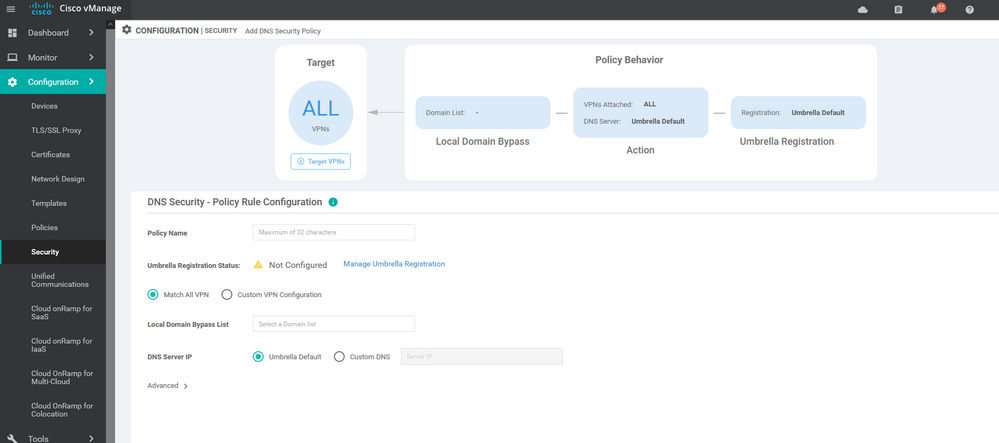
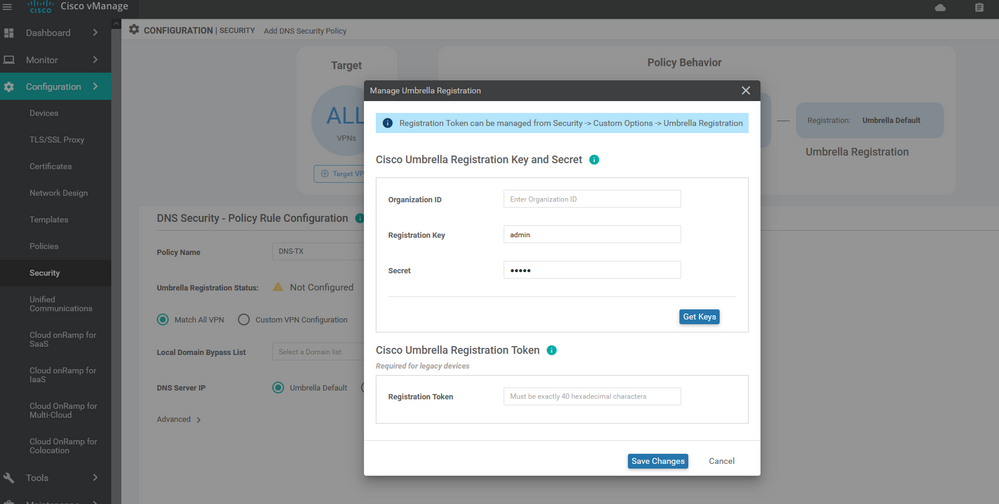
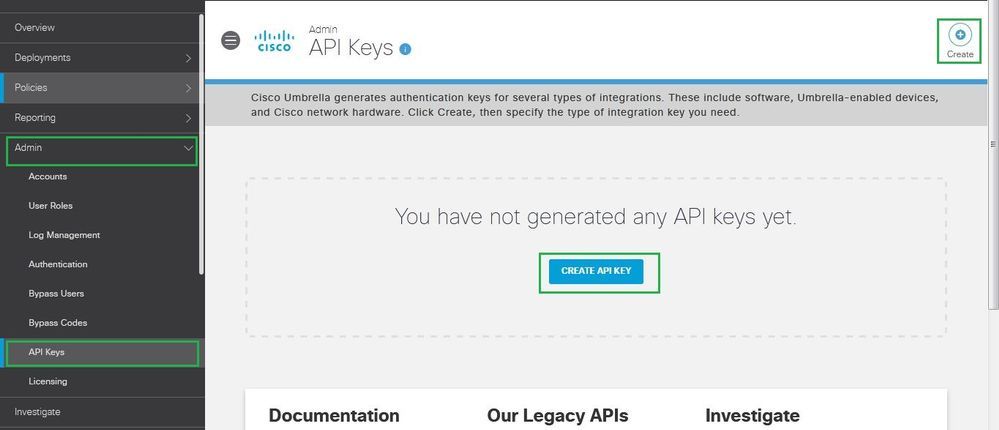
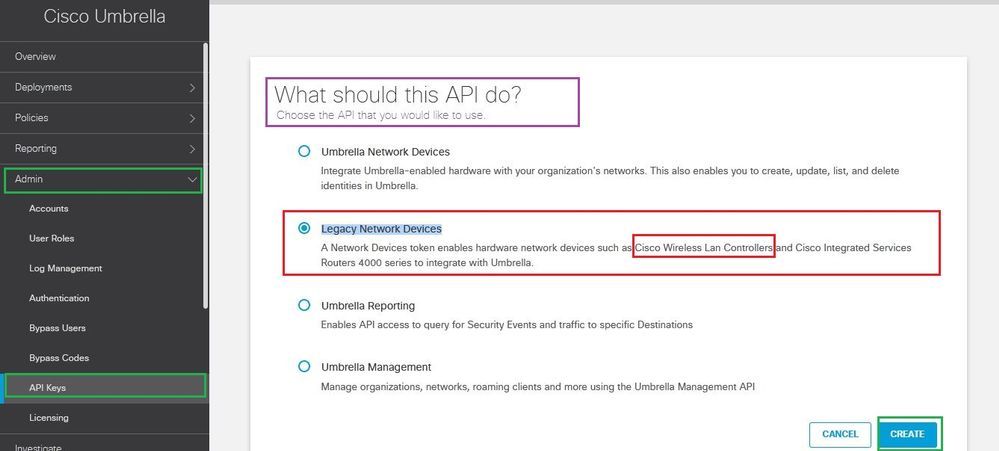
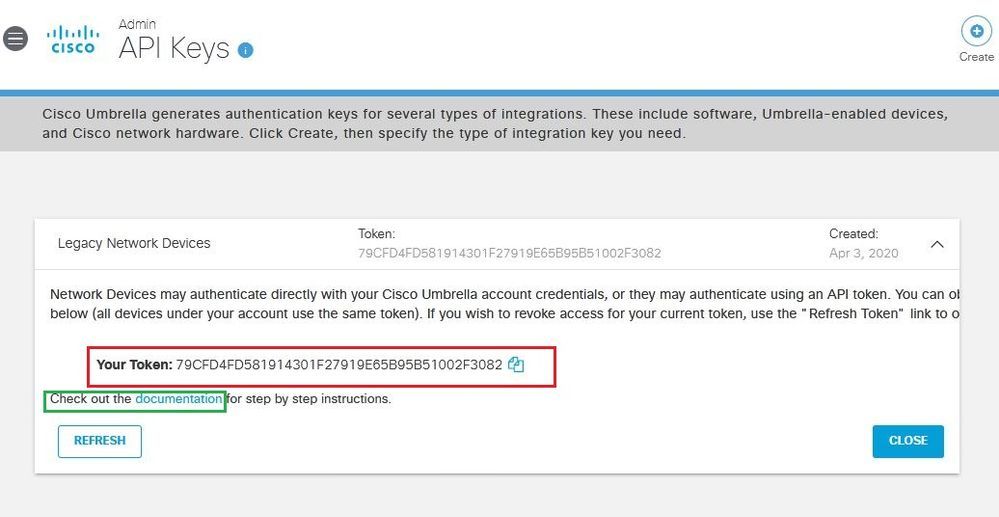
To create DNS Security> Security > Add new > create > Next > next >next > next >DNS Security> create new
- The first step add the public IP address of the enterprise on the Cisco umbrella
https://dashboard.umbrella.com Enter username & Password
Enter Deployment —> Core Identities —> Network —> Add —> write the name of the network —> Public Ip —> choose mask —> save
a DNS proxy for those users. The DNS server addresses that you specify need to be able to resolvethe SaaS Fully Qualified Domain Names (FQDNs) and need to be reachable from VPN 0 or the local Internet exit.
route for local exit: This guide assumes that the SD-WAN overlay is already operational. If so, you must have at least one default route defined under VPN 0 to allow the tunnel to connect to the remote sites and data centers through one or more of the physical interfaces. You can either statically define the configuration of this default route or obtain it via Dynamic Host Configuration Protocol (DHCP). For DIA and gateway sites, this default route gives the next-hop information for the direct Internet exits when the Cloud onRamp for SaaS feature is configured.
NOTE: The network connection may be a single public IP address ( dynamic) so you need to check mark this option [ This network has a dynamic IP address]
To add unified communication voice policy Configuration > unified communication > create new > Add voice ports policy profile
Cloud onRamp
To respect copyrights This note copy from cisco live document
vManage mode: Sites to be configured for Cloud onRamp for SaaS need to be in vManage mode as opposed to command-line interface (CLI) mode, meaning that the vManage GUI will control the configuration of the vEdge router as opposed to a user using the CLI to modify the configuration directly on a vEdge device. You need to apply a device template to the vEdge router from the vManage GUI in order to put it in vManage mode. Cisco vEdge software version: The minimum Cisco vEdge software version is 16.3.0 to configure DIA sites and 17.1.0 to configure gateway sites, but you should use the latest recommended maintenance release.
DIA or gateway sites only Network Address Translation (NAT) configuration: In order for SaaS traffic to be able to exit
the site locally (for both DIA and gateway sites), NAT configuration is required under each VPN 0 physical interface attached to the Internet or Internet path. This requirement is necessary for the interface to be a candidate for local exit, regardless of any other NAT configured for the site. Enabling NAT, by default, causes translation of the source IP address of a site user to
the outside IP address of the vEdge router when it uses the interface as a local exit to the SaaS applications.
DNS server configuration: Configure DNS server addresses in VPN 0 so the vEdge router can resolve the SaaS application hostnames and initiate performance statistics to those SaaS servers, as well as intercept DNS queries to the configured SaaS applications and act as a DNS proxy for those users. The DNS server addresses that you specify need to be able to resolve
the SaaS Fully Qualified Domain Names (FQDNs) and need to be reachable from VPN 0 or the local Internet exit.
Default route for local exit: This guide assumes that the SD-WAN overlay is already operational. If so, you must have at least one default route defined under VPN 0 to allow the tunnel to connect to the remote sites and data centers through one or more of the physical interfaces. You can either statically define the configuration of this default route or obtain it via Dynamic Host Configuration Protocol (DHCP). For DIA and gateway sites, this default route gives the next-hop information for the direct Internet exits when the Cloud onRamp for SaaS feature is configured.
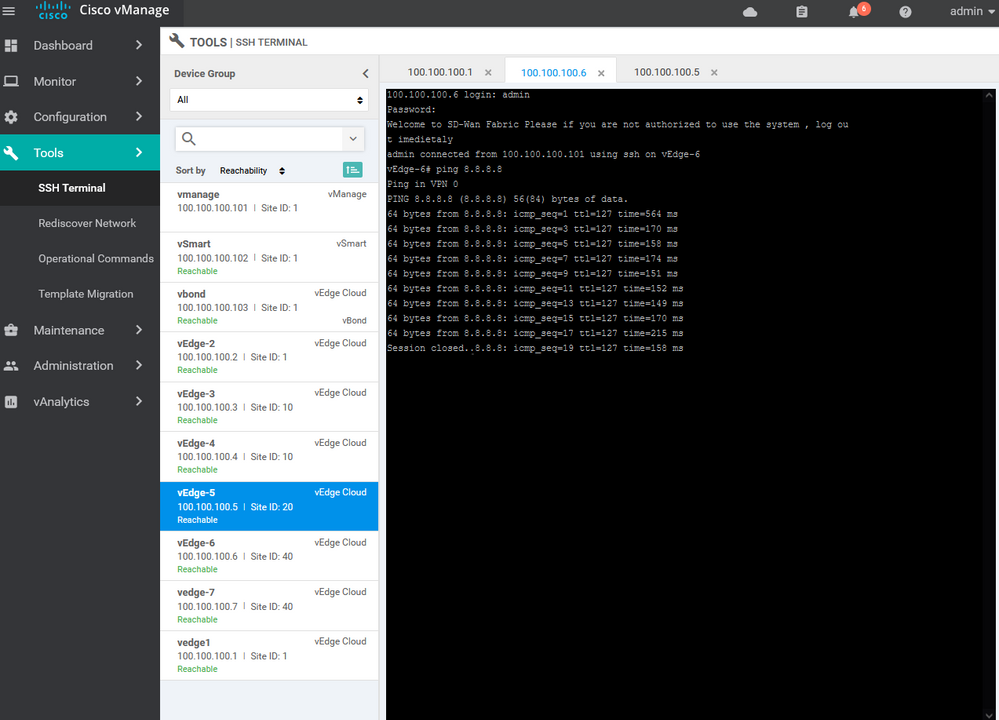
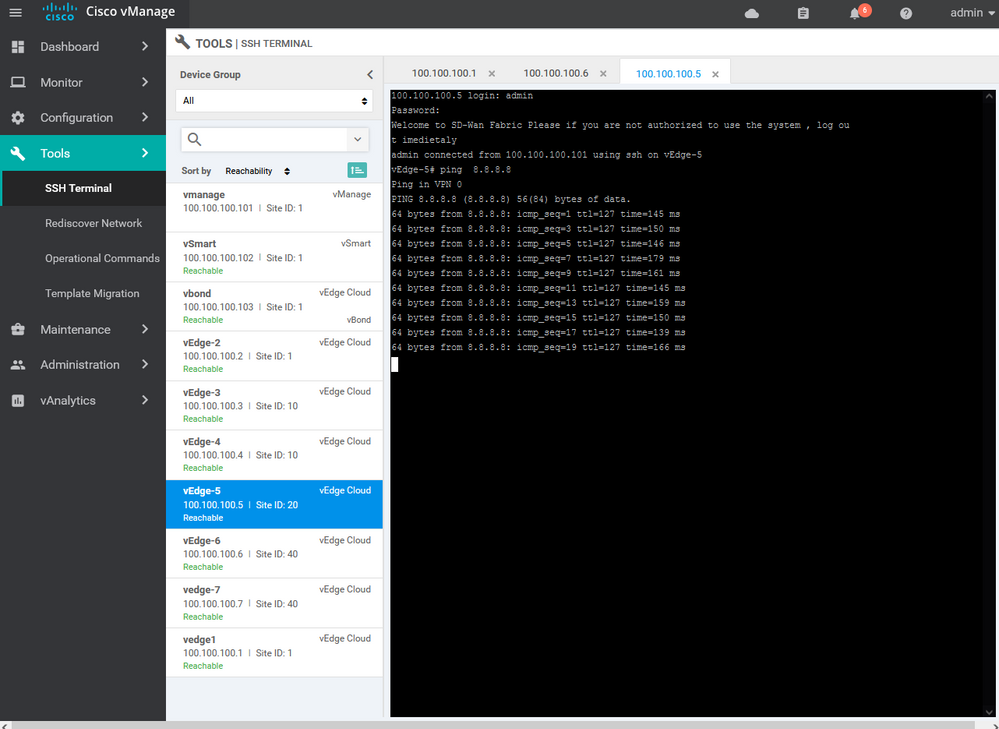
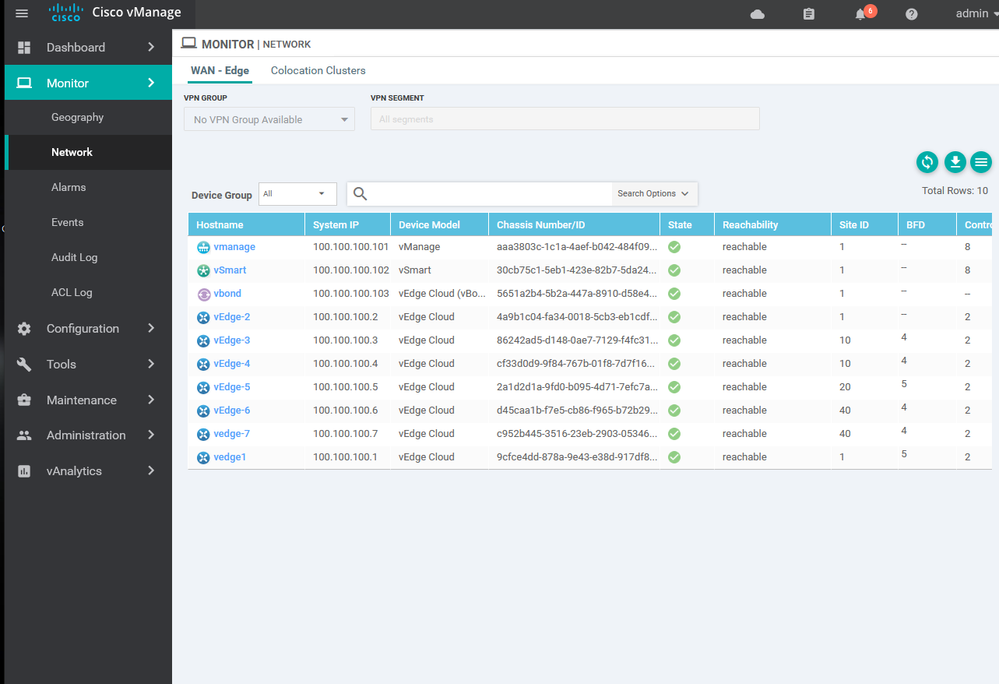
Let's Confirm the internet connection is working for the branches and data center
To enable the Cloud onRamp for SaaS feature, you must first enable it globally. Then the SaaS applications that will be used and monitored will be defined. After that, the various sites will be enabled (DIA, gateway, and client sites). You must complete the first two procedures before you can enable the sites; you can enable them in any order and in any combination.
If you define only DIA sites, then site users will use their local exits until the SaaS applications become unreachable or performance becomes unacceptable; at that point, the SaaS traffic will fall back to normal routing and follow the default route for Internet access. If you define client sites, you must also define gateway sites so that the client-site traffic will
have performance-monitored sites to use for Internet exits; otherwise this traffic will follow the normal default routed path.
If you define both gateway and DIA sites, the site users at a DIA site could use either the local exit or the gateway site for Internet access, depending on the performance of the application and path.
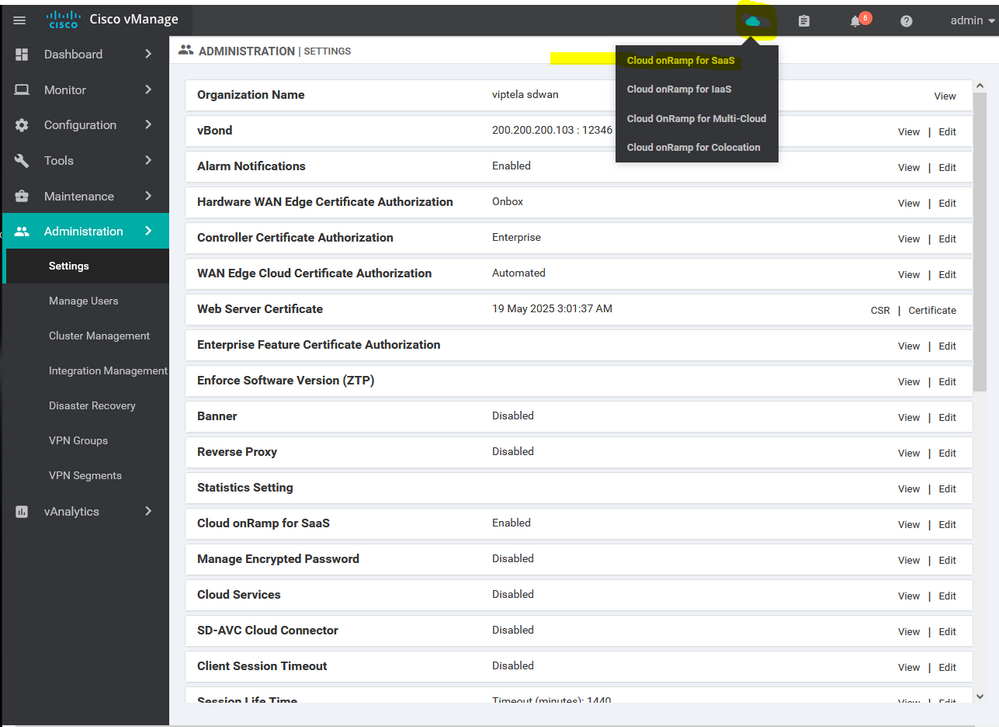
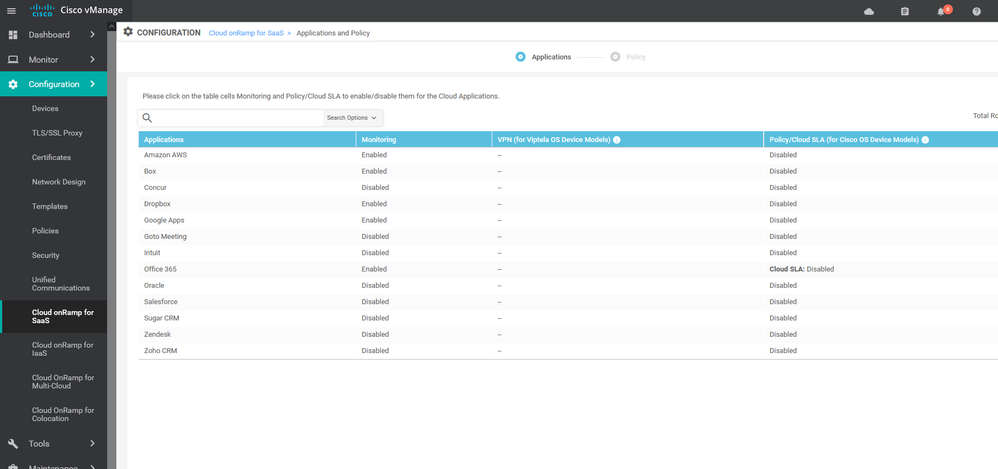
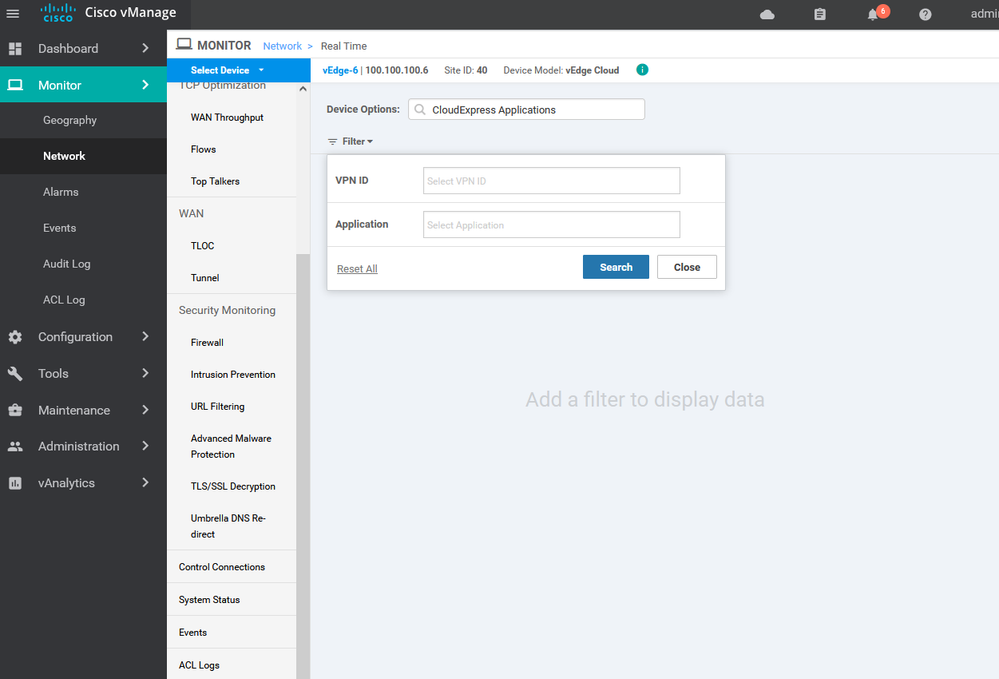
to Configure cloud onRamp for saas > administrator > setting > cloud onRamp for saas > enable > then Cloud icon > cloud onRamp for saas > add new application and policy
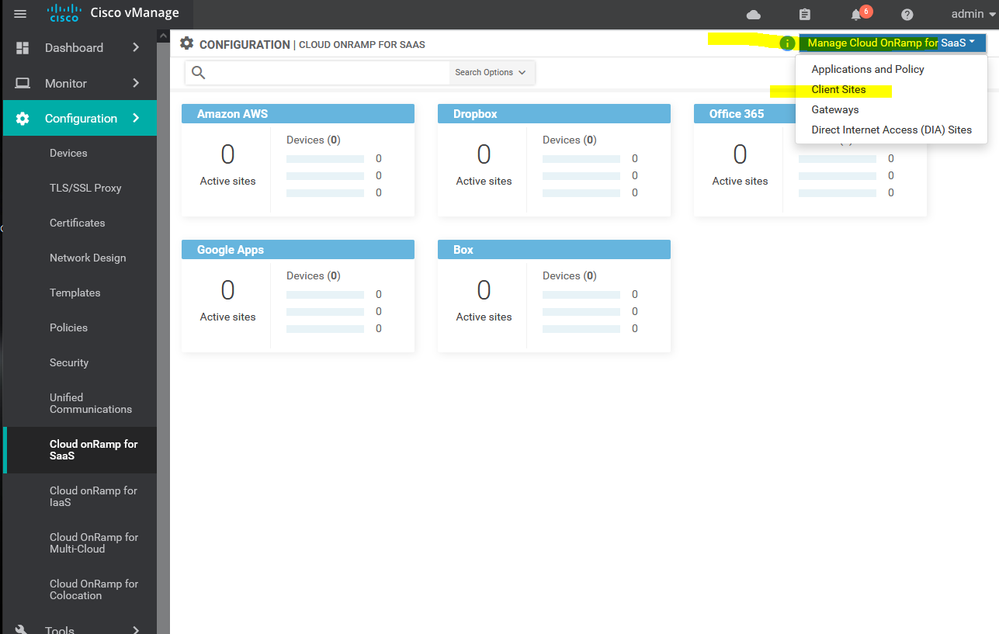
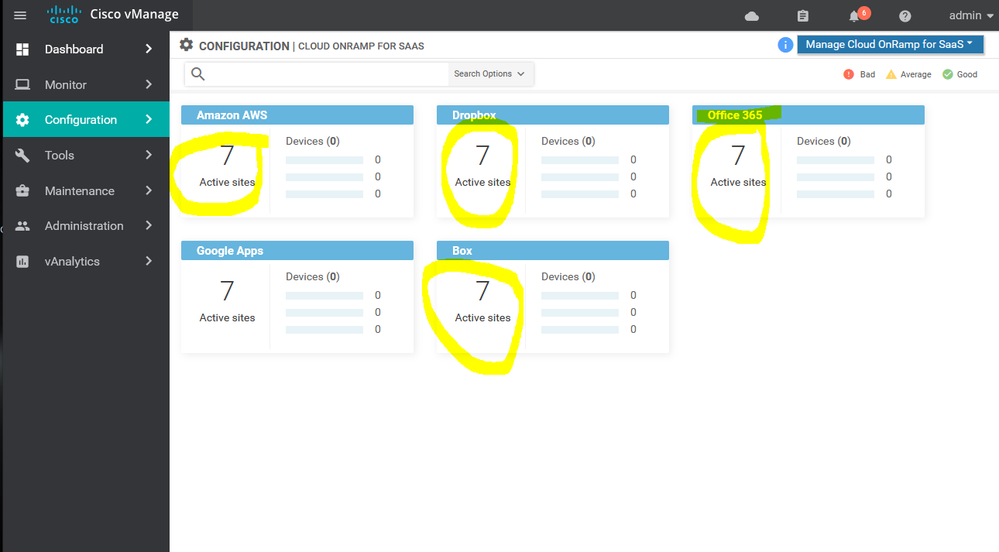
To Add site for cloud onRamp for saas > administrator > setting > cloud onRamp for saas > enable > then Cloud icon > cloud onRamp for saas > add client sites
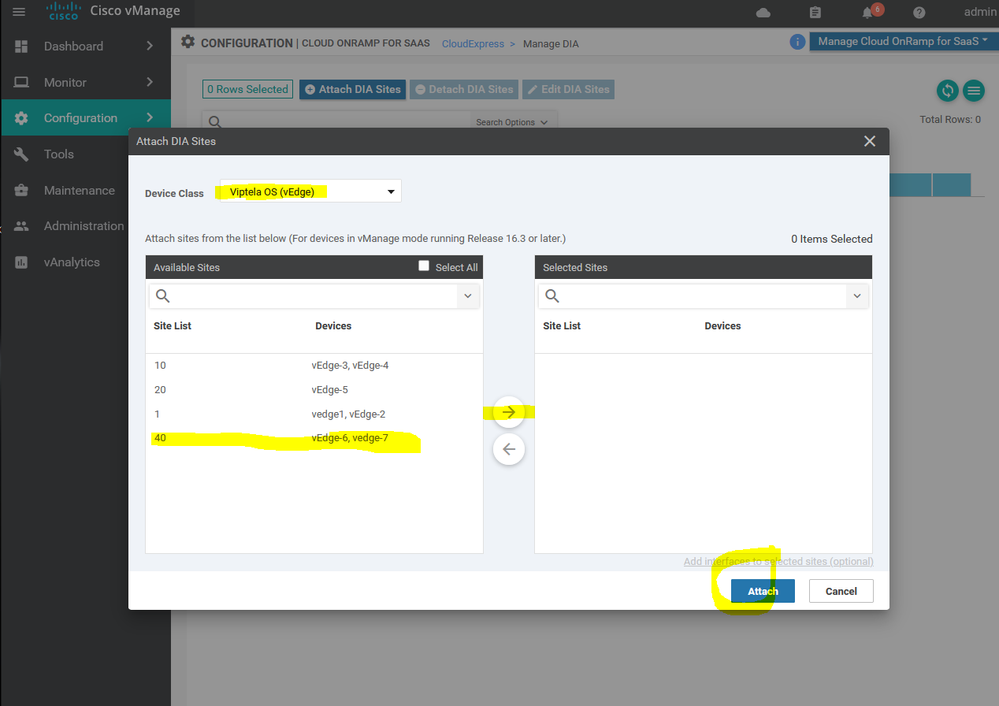
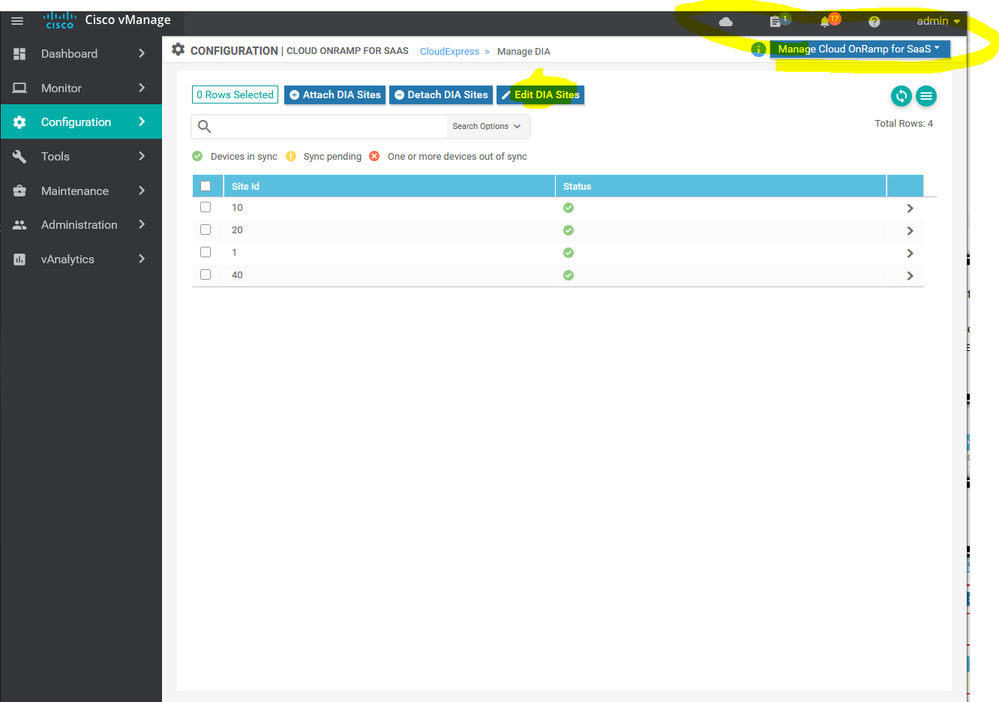
To configure DIA sites, select Manage Cloud onRamp for Saas >Direct Internet Access (DIA) Sites in the drop- Add site
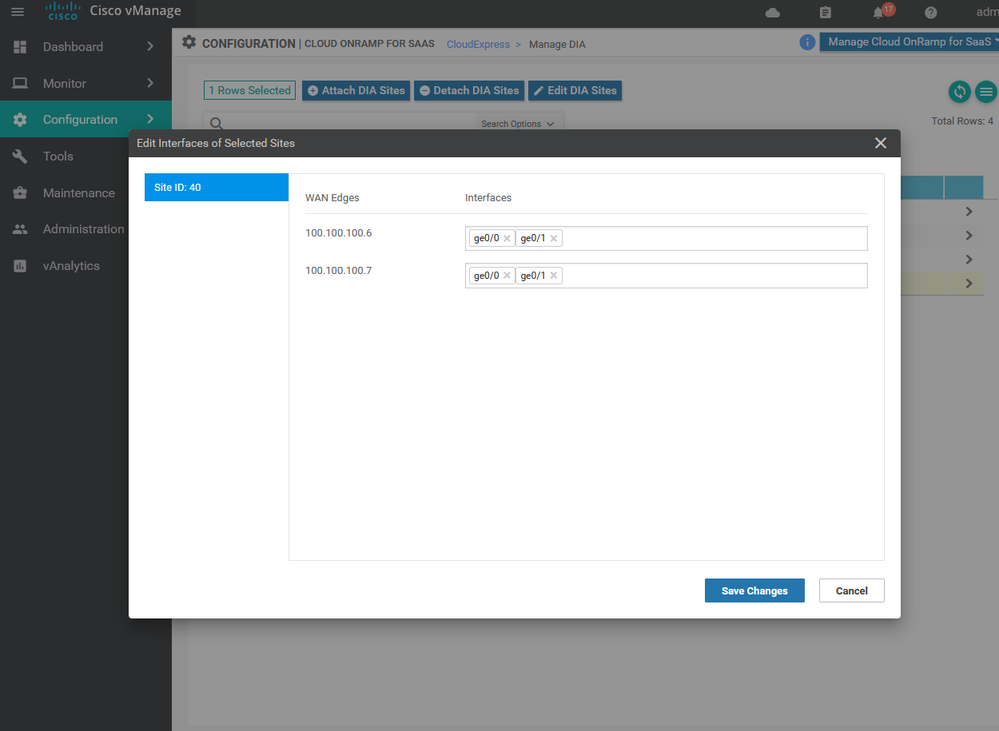
Adjust the DIA for the Site 4
***** I hope that has been informative for you and thank you *****
Mohamed Alhenawy
CCIE#60453
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: