- Cisco Community
- Technology and Support
- Security
- Network Access Control
- ISE 2.4 patch 9 -> AD Test User not working
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-05-2019 01:24 AM
I have found a bug in Cisco ISE Patch 9
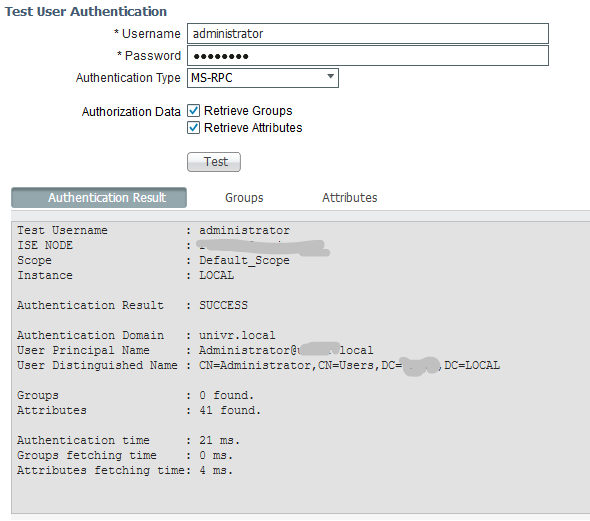
In ISE 2.4 menu Administration/Identity Management/External Identity Source/, after installing the ISE 2.4 patch 9 it’s not possible to retrieve the groups of AD user
I’ve tried in with Kerberos, Lookup, MS-RPC, but the result is the same
Luckily, I have verified that this behavior does not affect the authentication and authorization process, so the policies are applied correctly.
That’s an environment that can easily be reproduced in a lab test:
You have to install ISE 2.4, join to AD, install patch 8, test the AD user, install patch 9, test the AD user and try to see what’s happening
I use this tool often, it's very useful to troubleshoot the user groups and attributes, and also to check the status of AD connection.
Any suggestion?
Best Regards
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-08-2019 05:50 AM
Known Fixed Releases: (2)
2.6.0.156-Patch2
2.4.0.357-Patch10
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-05-2019 07:31 AM
Yes, I was able to reproduce. Please open a TAC SR and have them reference CSCvq78503. May not be visible to you yet as it was just created. Unfortunately I do not see a workaround for this defect. Thank you for reporting it to us.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-16-2019 06:47 AM
Hi,
I also had this problem after installing patch 9.
I,m using Microsoft cmd line commands to find out group memberships for
machines and users....
examples: net group "Domain Computers" /domain | find "machine name" or net user xxxx /domain
waiting for patch 10 :)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-16-2019 08:54 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-08-2019 05:50 AM
Known Fixed Releases: (2)
2.6.0.156-Patch2
2.4.0.357-Patch10
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-15-2019 12:39 AM
Hey,
How did you solved your problem ?
thanks for reply
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide