- Cisco Community
- Technology and Support
- Networking
- Routing
- Re: Forwarding Packet to Another Public IP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Forwarding Packet to Another Public IP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-17-2019 01:25 AM - edited 05-17-2019 01:28 AM
Hello guys, so i have 2 sites it's Site A & B. We have server farm in site B that used to be in site A and the we're migrated and that's so happened. So my boss wanted not stop this site A but instead he wanted still using it because our client white listing our ip pub in site A. So i have to configure every packet that hit site A will be forwarded to site B in doing so, i tried built tunnel between the sites using DMVPN so the server from B can be access from Site A. And after i config that i can ping the server that in site B but when i NAT the traffic to that server it failed, not works. I try to solve this very hard but if someone can really help i would be appreciate it. Thank you
- Labels:
-
Routing Protocols
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-17-2019 05:14 AM
How did you set up your NAT? What does routing look like. Ie at site B towards client.
One possible point of failure I can see is if you do DNAT at Site A for customer traffic servers on site B might route return traffic to clients directly instead of going via site A.
So you would have to do both DNAT and SNAT to make sure that traffic goes via site A both ways.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-17-2019 05:43 AM
We also need information about the addressing used. What is the public IP of sites A and B? What is the LAN subnet(s) of site A and B? What is the IP addresses of the servers that are now at site B? Did that subnet move from site A to site B or is part of that subnet still at site A?
HTH
Rick
Rick
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-17-2019 08:43 PM
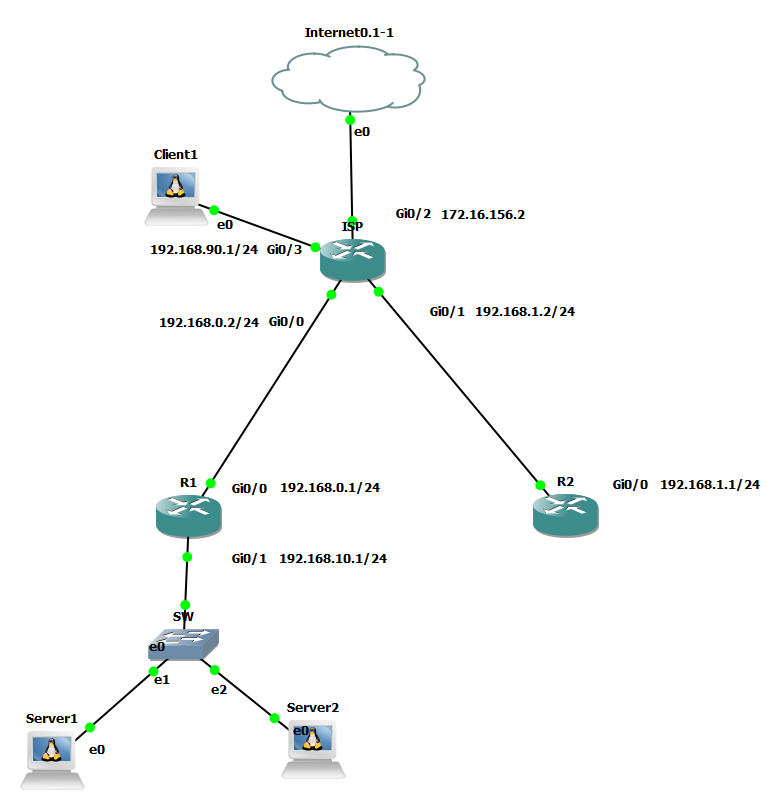
So this is example
Public ip in site A is 1.1.1.1 and B is 2.2.2.2
no lan subnet on site A because it will only forward traffic
in site B the lan is 100.100.1.1
The subnet is move from site A to site B
but to make like it's in site A so i configure DMVPN and routing it with EIGRP
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-17-2019 08:38 PM
In site A im using static nat , the routing im using to connect site A and B is with eigrp across DMVPN.
Can you give me example how to do DNAT and SNAT?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-20-2019 04:26 AM
Unfortunately I can't really give you a guide to follow, because exact implementation would depend on what product you are using, and not knowing the exact setup.
Also it was quite some time since I did anything remotely similar, so I'm a bit rusty regarding this, perhaps someone else that has more recent working experience can chime in if I'm way off here.
The problem as I see this is that when you use NAT (I'm assuming you set up destination nat) at site A to redirect traffic to servers on site B that only affects traffic going from client to servers. If the return traffic does not get routed back symmetrically through site A on it's way back to the client it will not work.
I can think of 2 possible ways to work around this.
One is to use SNAT (source nat) to make it look like the client is located at site A.
The second alternative is to use policy based routing to get the return traffic to go through site A.
Both should work, but without being able to try it out in a lab/test environment it's just what comes to mind.
In the end it's a bit hard to give truly reliable advice here with extremely limited information and knowledge about the environment.
Have you considered bringing in a consultant on this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-23-2019 07:26 AM - edited 05-23-2019 08:53 AM
Ok so on site A i'm using cisco 881m series and on site B i'm using cisco 4321.
On site A there is no server or anything just router connect to isp
On site B im doing ip sla pbr because it's using 2 isp and for lan there're plenty server farm so im using subinterface
Because i want to redirect traffic from site A to B so i configured eigrp on both site and connect them with dmvpn, so there will be route to server B from A and then i just configured nat inside static from A but that's problem start.
The problem is when i ssh or telnet from site A to server in site B it works but it'll not work with nat, im confused.
do you want to see the configuration?
This is my topology and configuration, hope it'll help
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-24-2019 05:50 AM
From what I can tell your problem should be related to asymmetric routing in combination with NAT.
Ie return traffic will come back with IP from Site B instead of the IP from Site A.
Are the relevant servers exclusively used for clients coming via site A?
Or are they also getting traffic directly going to site B?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-24-2019 06:48 AM
Do you kmow how fix that asymmetric problem sir? Is it in eigrp configuration that i need to add?
Server also getting traffic to site B like connecting to internet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-24-2019 09:53 AM - edited 05-24-2019 09:55 AM
You could try something similar to this on R2.
access-list 1 permit 192.168.1.5 access-list 1 permit 192.168.1.10 ip nat pool MYPOOLEXAMPLE 10.0.5.1 10.0.5.254 prefix 24 ip nat outside source list 1 pool MYPOOLEXAMPLE add-route
Note that I have not tried this, but from looking at this cisco doc it should work.
Change the IP in the pool as appropriate for your environment.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-24-2019 11:23 AM - edited 05-24-2019 11:37 AM
im a bit confused about your ip arrangement, so i should configure this in R2 right? that has no server in it.
and in your acl is that lan address of R1?
and in nat pool is it wan address of R2?
thanks sir
should i configure like this
R2 access-list 1 permit 192.168.10.2 #LAN in R1 access-list 1 permit 192.168.10.3 #LAN in R1 ip nat pool MYPOOL 192.168.1.1 192.168.1.254 prefix-length 24 #WAN in R2 ip nat outside source list 1 pool MYPOOL add-route ip nat inside source static tcp 192.168.10.2 22 192.168.1.10 22000 extendable #i should add this right so from outside can access it
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-28-2019 03:07 AM - edited 05-28-2019 03:09 AM
Yes, the commands I suggested should be implemented on R2 in this case. (The router without the servers.)
The addresses in my acl are supposed to be the public IP that the customers are using to connect to you.
If this doesn't work as intended you could try an extended acl instead with any as source (unless you know what IPs the customer are coming from) and the public "server" IPs as destination.
The NAT pool can be just about any IP that will look like it's located at the R2 site.
In this case using private addresses are fine.
The NAT command should add the routes to your IGP (EIGRP?) so that R1 knows how to reach them.
Or you can add the network manually with an add route command.
What we are trying to do is to change the source address of the customer/clients connections to look like they are coming from the R2 site. So if you have public IPs that you can use that would also work, but in this case the translated addresses should only be seen by your network which is why using private IPs works just fine.
This will make sure that the return traffic from the R1 site goes via R2 on its way back to the customer.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-28-2019 07:43 AM - edited 05-28-2019 07:44 AM
still no luck sir, here's full conf on R2
R2(config-router)#do sh run Building configuration... Current configuration : 5132 bytes ! ! Last configuration change at 14:25:25 UTC Tue May 28 2019 by cisco ! version 15.6 service timestamps debug datetime msec service timestamps log datetime msec service password-encryption ! hostname R2 ! boot-start-marker boot-end-marker ! ! enable secret 5 $1$0/dN$qW9rec2AXm3OMgyMWgTHC0 enable password 7 02050D4808095E731F1A5C ! no aaa new-model ethernet lmi ce ! ! ! no process cpu autoprofile hog mmi polling-interval 60 no mmi auto-configure no mmi pvc mmi snmp-timeout 180 ! ! ! ! ! no ip icmp rate-limit unreachable ! ! ! ! ! ! ip domain name cisco2 ip name-server 8.8.8.8 ip name-server 8.8.4.4 ip cef no ipv6 cef ! multilink bundle-name authenticated ! ! ! ! username cisco privilege 15 secret 5 $1$tg.v$L1RLWDbYLO4mqT2rr3qJK/ ! redundancy ! no cdp log mismatch duplex no cdp run ! ip tcp synwait-time 5 ! ! ! ! ! crypto isakmp policy 10 hash md5 authentication pre-share crypto isakmp key spinku12345 address 0.0.0.0 ! ! crypto ipsec transform-set trset esp-3des esp-md5-hmac mode tunnel ! ! crypto ipsec profile test2 set security-association lifetime seconds 120 set transform-set trset ! ! ! ! ! ! interface Loopback0 ip address 10.0.0.1 255.255.255.255 ip nat inside ip virtual-reassembly in ! interface Tunnel0 bandwidth 1000000 ip address 172.16.0.2 255.255.255.0 no ip redirects ip mtu 1500 ip nhrp authentication cisco123 ip nhrp map multicast dynamic ip nhrp map 172.16.0.1 192.168.0.1 ip nhrp map multicast 192.168.0.1 ip nhrp network-id 1 ip nhrp nhs 172.16.0.1 delay 1 tunnel source GigabitEthernet0/0 tunnel mode gre multipoint tunnel key 0 tunnel protection ipsec profile test2 ! interface GigabitEthernet0/0 ip address 192.168.1.1 255.255.255.0 ip access-group INBOUND_FIREWALL in ip nat outside ip virtual-reassembly in duplex auto speed auto media-type rj45 no cdp enable ! interface GigabitEthernet0/1 ip address 192.168.100.1 255.255.255.0 ip nat inside ip virtual-reassembly in duplex auto speed auto media-type rj45 no cdp enable ! interface GigabitEthernet0/2 no ip address shutdown duplex auto speed auto media-type rj45 no cdp enable ! interface GigabitEthernet0/3 no ip address shutdown duplex auto speed auto media-type rj45 no cdp enable ! ! router eigrp 90 network 10.0.0.1 0.0.0.0 network 172.16.0.0 network 192.168.50.0 ! ip forward-protocol nd ! ! no ip http server no ip http secure-server ip dns server ip nat pool MYPOOL 192.168.50.1 192.168.50.254 prefix-length 24 ip nat inside source list NAT interface GigabitEthernet0/0 overload ip nat inside source static tcp 192.168.100.1 22 192.168.1.1 6914 extendable ip nat inside source static tcp 192.168.10.2 22 192.168.1.10 22000 extendable ip nat outside source list 100 pool MYPOOL add-route ip route 0.0.0.0 0.0.0.0 192.168.1.2 ip ssh version 2 ! ip access-list standard INBOUND_FIREWALL permit any ip access-list standard NAT permit any ! ! ! access-list 100 permit ip any host 192.168.1.10 ! control-plane ! line con 0 exec-timeout 0 0 privilege level 15 password 7 045802150C2E1D1C5A logging synchronous login local transport output ssh line aux 0 exec-timeout 0 0 privilege level 15 logging synchronous line vty 0 4 login local transport input ssh transport output ssh ! no scheduler allocate ! end
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-04-2019 01:42 AM
Well not sure if I have any more ideas, could be a lot of things.
Does the nat statements work as intended?
ie output of show ip nat translations (possibly with optional tag 'verbose')
Does the route for the 192.168.50.x addresses show up on R1?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-19-2019 10:02 AM
can someone help please?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide