- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- AMP for Endpoints: How to Activate and Use SecureX FAQ
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
09-16-2020 03:40 PM - edited 09-16-2020 04:25 PM
What is SecureX?
All AMP for Endpoints subscriptions include Cisco SecureX, which is built-in. SecureX is a cloud-native platform that turns your infrastructure into a fully integrated ecosystem, by aggregating capabilities across the Cisco Security portfolio as well as 3rd party tools. It’s designed to simplify your security environment, improve visibility and context, and maximize your team’s efficiency.
What can I do with SecureX?
- Dashboard: Get visibility to key operational metrics across your security portfolio together with your AMP for Endpoints data.
- Threat Response: Instead of having to log into multiple platforms to try and correlate information, Threat Response will take the observables you paste in and automatically correlate intelligence from various sources to help you visualize your environment.
- Ribbon: Pivot and investigate faster with relevant context that you take with you as you move from AMP for Endpoints user interface back to the platform. If you have AMP for Endpoints Advantage, you can query Orbital directly from the SecureX ribbon.
- Orchestration (Beta): Improve your efficiency through automated workflows to cut down time spent on routine tasks. A drag-and-drop interface helps you combine actions across multiple products, even 3rd party products. For example, you could create a workflow to trigger a ServiceNow ticket each time you isolate a host.
How do I connect to SecureX?
Click here for a YouTube video with instructions, or follow the step-by-step instructions below.
- After you log in to AMP for Endpoints, click the Ribbon on the bottom to expand it. Then, click Get SecureX.
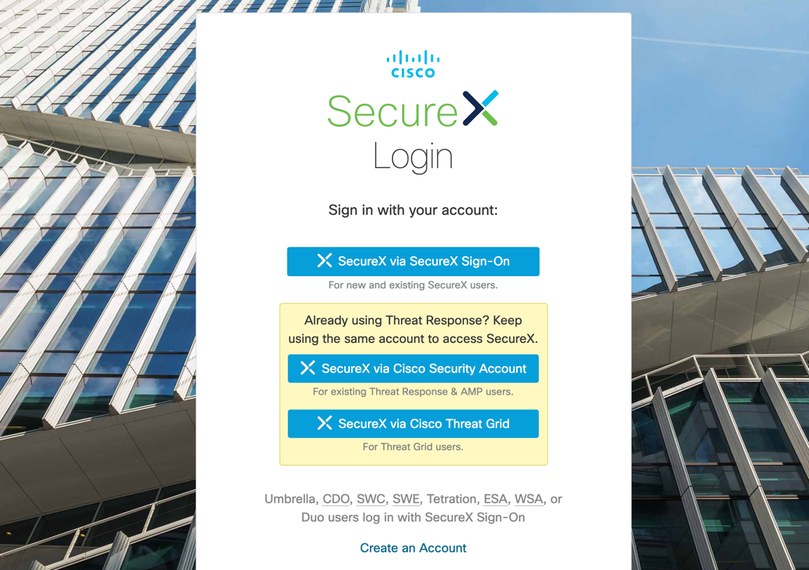
- As an existing AMP for Endpoints user, click the middle button to log in to SecureX.
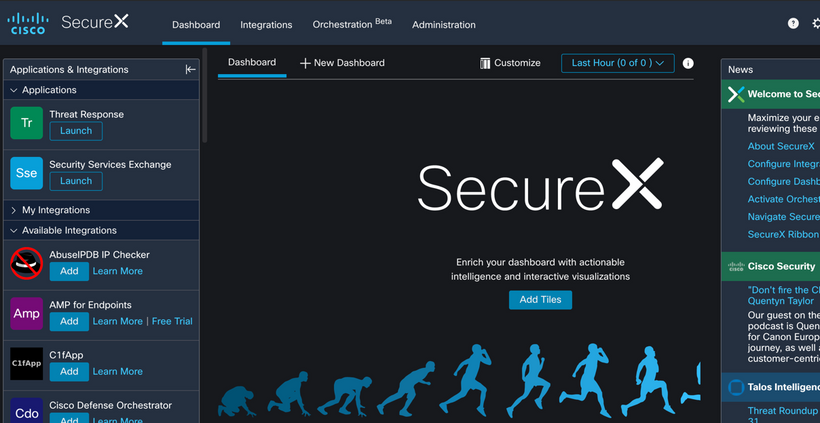
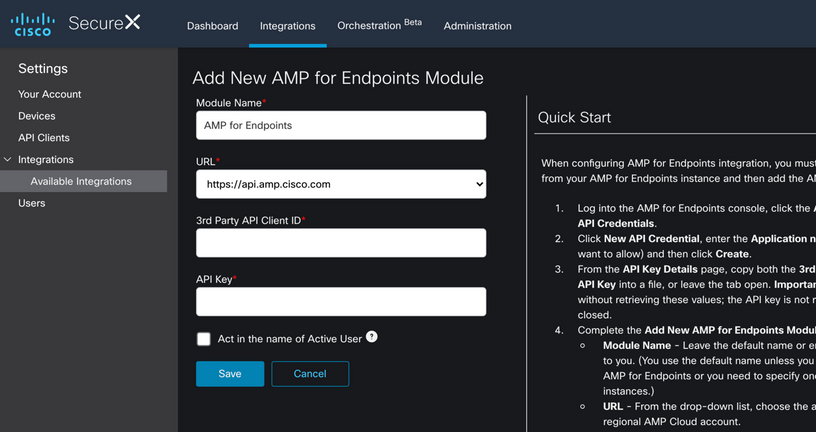
- You’re now on the SecureX home screen. Find AMP in the Available Integrations section and click Add.
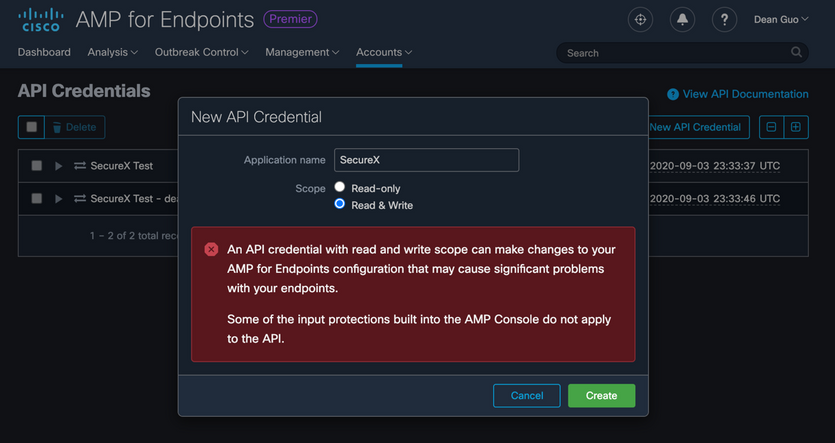
- Navigate back over to the AMP for Endpoints Console to generate the API Credential. Go to Accounts -> API Credentials, and click New API Credential.
- Give the new API key Read & Write access. Click Create.
- Navigate back to SecureX and paste the Client ID and API Key in.
- You’re all set to start using SecureX!
What’s an example of SecureX in action?
- In this example, we will show you how to do a threat hunt using SecureX Threat Response. Hashes you obtain of IOCs can be quickly searched in AMP for Endpoints with one click.Log into SecureX and launch Threat Response from either the Applications section or the Ribbon.
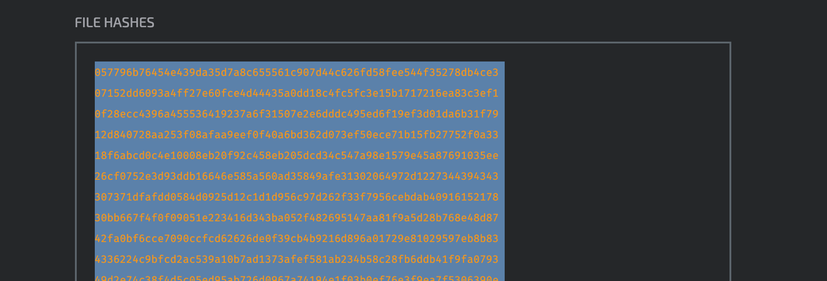
- Go to a source of IOCs, like a recent Threat Roundup from Talos Blog.
- Copy the hashes that you want to search for in your environment.
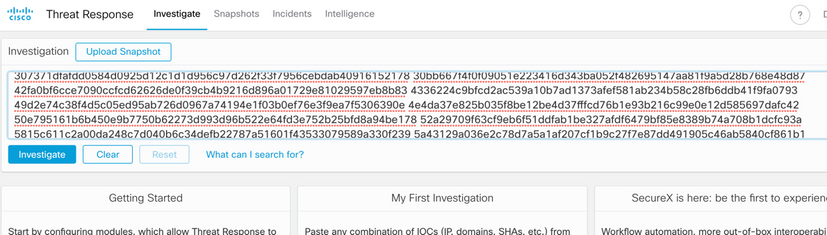
- Drop them directly into the Investigation box in Threat Response – no formatting required. Using Threat Response, we can search for hundreds of hashes at a time, instead of individually in the AMP console.
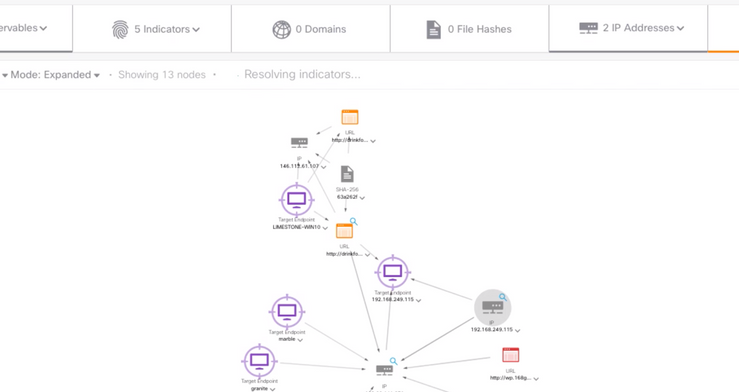
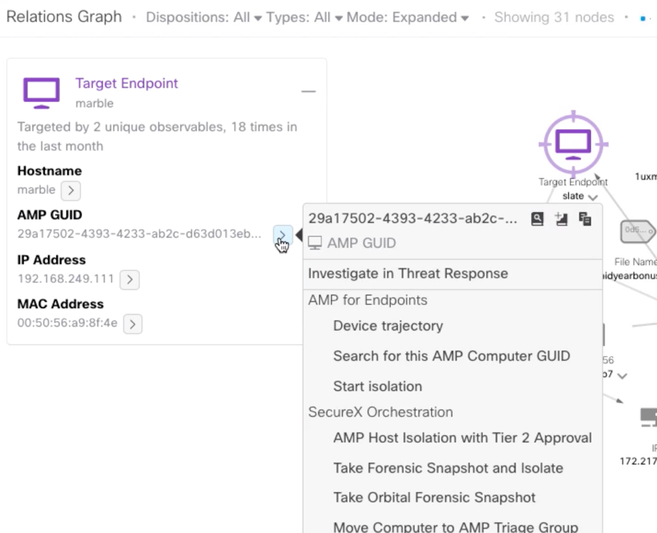
- Click Investigate. SecureX performs the investigation by checking all of your Cisco Security modules to see what each of them knows about the observables. All results are displayed in the Relations Graph, with the relationships between the observables and any relevant data elements highlighted. This can include information such as parent files, URLs from which the observables originated, and endpoints that may have been impacted in your environment.
- With SecureX, you can then take action on the endpoint directly from the Threat Response console, such as isolating the host. With Orchestration (Beta) enabled, you’ll be able to take even more complex workflows and turn it into one click from the console.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Great information on AMP for Endpoints. Plus very helpful links within this post.
Thank you for sharing!
Regards,
Gus
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
In Umbrella we can thankfully turn OFF the SecureX bar -- it takes up WAY too much space on the screen in the current iteration. Why is it so big when it's not even being used? Is it just to get attention?
How do we turn it off or hide the SecureX bar in AMP4EP so it's not taking up the entire bottom of the screen? Unfortunately, clicking "X" just makes it bigger -- it behaves like adware in this respect: it won't go away.
In full-screen Device Trajectory, the SecureX bar makes it hard to work by significantly reducing the amount of screen available. In that view, we need as much of the screen as possible and the SecureX bar does not help.
Hope something can be done to make this better soon. Right now I can't stand SecureX for this reason. Thanks!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi @md11, we do want to increase awareness of the SecureX feature, but we definitely don't want it to be intrusive. Thanks for the feedback.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: