- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- Configure Anyconnect with LDAP Authentication
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
08-30-2013 03:59 PM - edited 08-23-2017 10:27 PM
- Introduction:
- Prerequesites:
- Components Used:
- Network Diagram
- Anyconnect Configuration
- LDAP configuration on ASA
Introduction:
This document provides step-by-step instructions on how to allow Cisco AnyConnect VPN client access to the Internet while they are tunneled into a Cisco Adaptive Security Appliance (ASA) 8.4(2). This configuration allows the client secure access to corporate resources via SSL while giving unsecured access to the Internet using split tunneling. This document will also give you information on how to use LDAP for user authentication.
Prerequesites:
This document requires a basic understanding of SSL protocol and LDAP. Ensure that you meet these requirements before you attempt this configuration:
- ASA Security Appliance needs to run version 8.x
- Cisco AnyConnect VPN Client 2.x or above.
Components Used:
- Cisco 5500 Series ASA that runs software version 8.4(2)
- Cisco AnyConnect SSL VPN Client version for Windows 2.5.6005
- Microsoft windows 2008 R2 Server
- Windows 7 PC
Network Diagram
Anyconnect Configuration
1. Upload and Identify the SSL VPN Client Image:
ciscoasa(config)#copy tftp://192.168.47.100/anyconnect-win-2.5.6005-k9.pkg flash
Address or name of remote host [192.168.47.100]?
Source filename [anyconnect-win-2.5.6005-k9.pkg]?
Destination filename [anyconnect-win-2.5.6005-k9.pkg]?
Accessing tftp://192.168.47.100/anyconnect-win-2.5.6005-k9.pkg...!!!!!!!!!!!!!
Writing file disk0:/ anyconnect-win-2.5.6005-k9.pkg...
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!
2635734 bytes copied in 4.480 secs (658933 bytes/sec)
***192.168.47.100 is the IP of the TFTP server.
2. Enable Anyconnect Access:
webvpn
enable outside
anyconnect image disk0:/anyconnect-win-2.5.6005-k9.pkg 1
anyconnect enable
tunnel-group-list enable
3. Configure the VPN pool:
ip local pool anyconnect 192.168.100.100-192.168.100.200 mask 255.255.255.0
4. Configure the Split tunnel access-list:
access-list split standard permit 192.168.47.0 255.255.255.0
5. Configure the group-policy:
group-policy GroupPolicy_test_anyconnect internal
group-policy GroupPolicy_test_anyconnect attributes
wins-server 192.168.47.100
dns-server value 192.168.47.100
vpn-tunnel-protocol ssl-client ssl-clientless
split-tunnel-policy tunnelspecified
split-tunnel-network-list value split
default-domain value mydomain.com
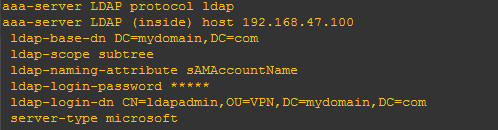
6. Configure the AAA-SERVER (LDAP)
aaa-server LDAP protocol ldap
aaa-server LDAP (inside) host 192.168.47.100
ldap-base-dn DC=mydomain,DC=com
ldap-scope subtree
ldap-naming-attribute sAMAccountName
ldap-login-password *****
ldap-login-dn CN=ldapadmin,OU=VPN,DC=mydomain,DC=com
server-type microsoft
7. Configure Tunnel-group:
tunnel-group anyconnect type remote-access
tunnel-group anyconnect general-attributes
address-pool anyconnect
authentication-server-group LDAP
default-group-policy GroupPolicy_test_anyconnect
tunnel-group anyconnect webvpn-attributes
group-alias anyconnect enable
8. Configure NAT exempt:
object network NETWORK_OBJ_192.168.47.0_24
subnet 192.168.47.0 255.255.255.0
object network NETWORK_OBJ_192.168.100.0_24
subnet 192.168.100.0 255.255.255.0
nat (inside,outside) source static NETWORK_OBJ_192.168.47.0_24 NETWORK_OBJ_192.168.47.0_24 destination static NETWORK_OBJ_192.168.100.0_24 NETWORK_OBJ_192.168.100.0_24 no-proxy-arp route-lookup
LDAP configuration on ASA
To Configure LDAP authentication on ASA you need the following information:
- IP address of the ldap server 192.168.47.100
- Base DN information ldap-base-dn DC=mydomain,DC=com
- Ldap login DN information CN=ldapadmin,OU=VPN,DC=mydomain,DC=com
- ldap-login-password welcome@12
In case if you do not have the login DN information but you do have the access of the AD server you can do the following:
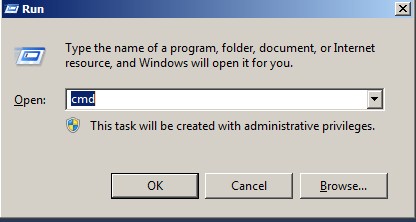
- Log on to the AD server and open RUN and type CMD
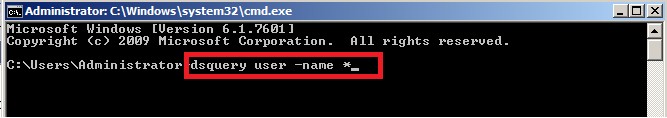
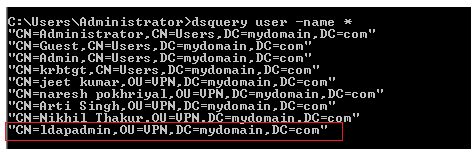
- Then type the command dsquery user –name * and it will show you list of all configured user:
- Then out of those select any one user and take his value and define that as the login-dn. In our case I used ldapadmin.
- Then log on to the ASA and configured the aaa-server group:
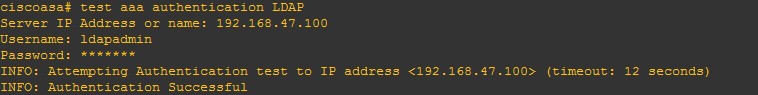
- Run a test authentication command on ASA to check your settings:
Establish the SSL VPN Connection
Complete these steps in order to establish a SSL VPN connection with ASA:
- Enter the URL or IP address of the ASA's WebVPN interface in your web browser in the format as shown.
https://<IP address of the ASA WebVPN interface>
- Enter your username and password. Also, choose your respective group from the drop down list as shown:
- This window appears before the SSL VPN connection is established:
- You receive this window once the connection is established:
- Click the lock which appears in the task bar of your computer:
- This window appears and provides information about the SSL connection. For example, 192.168.100.100 is the assigned IP by the ASA, etc.
show vpn-sessiondb anyconnect: Displays the information about the current SSL connections
debug webvpn anyconnect <1-255> Provides the real time webvpn events in order to establish the session:
ciscoasa(config)# webvpn_rx_data_tunnel_connect
CSTP state = HEADER_PROCESSING
http_parse_cstp_method()
...input: 'CONNECT /CSCOSSLC/tunnel HTTP/1.1'
webvpn_cstp_parse_request_field()
...input: 'Host: h1s47a47n47.user.nortelnetworks.com'
Processing CSTP header line: 'Host: h1s47a47n47.user.nortelnetworks.com'
webvpn_cstp_parse_request_field()
...input: 'User-Agent: Cisco AnyConnect VPN Agent for Windows 2.5.6005'
Processing CSTP header line: 'User-Agent: Cisco AnyConnect VPN Agent for Windows 2.5.6005'
Setting user-agent to: 'Cisco AnyConnect VPN Agent for Windows 2.5.6005'
webvpn_cstp_parse_request_field()
...input: 'Cookie: webvpn=20527417@36864@1377929256@2975C09701C59C9A2562179C3E3ECEA0B4DA53A9'
Processing CSTP header line: 'Cookie: webvpn=20527417@36864@1377929256@2975C09701C59C9A2562179C3E3ECEA0B4DA53A9'
Found WebVPN cookie: 'webvpn=20527417@36864@1377929256@2975C09701C59C9A2562179C3E3ECEA0B4DA53A9'
WebVPN Cookie: 'webvpn=20527417@36864@1377929256@2975C09701C59C9A2562179C3E3ECEA0B4DA53A9'
IPADDR: '20527417', INDEX: '36864', LOGIN: '1377929256'
webvpn_cstp_parse_request_field()
...input: 'X-CSTP-Version: 1'
Processing CSTP header line: 'X-CSTP-Version: 1'
Setting version to '1'
webvpn_cstp_parse_request_field()
...input: 'X-CSTP-Hostname: xxxxxx-PC'
Processing CSTP header line: 'X-CSTP-Hostname: Arjeeta-PC'
Setting hostname to: 'xxxxx-PC'
webvpn_cstp_parse_request_field()
...input: 'X-CSTP-Accept-Encoding: deflate;q=1.0'
Processing CSTP header line: 'X-CSTP-Accept-Encoding: deflate;q=1.0'
webvpn_cstp_parse_request_field()
...input: 'X-CSTP-MTU: 1406'
Processing CSTP header line: 'X-CSTP-MTU: 1406'
webvpn_cstp_parse_request_field()
...input: 'X-CSTP-Address-Type: IPv6,IPv4'
Processing CSTP header line: 'X-CSTP-Address-Type: IPv6,IPv4'
webvpn_cstp_parse_request_field()
...input: 'X-DTLS-Master-Secret: 08F3C896EF934DD1381A79B6163198E1BE50117FF81B522E0DBEFADCCD6CE1558713C69910892732117C9472DA854790'
Processing CSTP header line: 'X-DTLS-Master-Secret: 08F3C896EF934DD1381A79B6163198E1BE50117FF81B522E0DBEFADCCD6CE1558713C69910892732117C9472DA854790'
webvpn_cstp_parse_request_field()
...input: 'X-DTLS-CipherSuite: AES256-SHA:AES128-SHA:DES-CBC3-SHA:DES-CBC-SHA'
Processing CSTP header line: 'X-DTLS-CipherSuite: AES256-SHA:AES128-SHA:DES-CBC3-SHA:DES-CBC-SHA'
webvpn_cstp_parse_request_field()
...input: 'X-CSTP-Protocol: Copyright (c) 2004 Cisco Systems, Inc.'
Processing CSTP header line: 'X-CSTP-Protocol: Copyright (c) 2004 Cisco Systems, Inc.'
Validating address: 0.0.0.0
CSTP state = WAIT_FOR_ADDRESS
webvpn_cstp_accept_address: 192.168.100.100/255.255.255.0
webvpn_cstp_accept_ipv6_address: No IPv6 Address
CSTP state = HAVE_ADDRESS
SVC: NP setup
np_svc_create_session(0x9000, 0xb62afb20, TRUE)
webvpn_svc_np_setup
SVC ACL Name: NULL
SVC ACL ID: -1
SVC ACL ID: -1
vpn_put_uauth success!
SVC IPv6 ACL Name: NULL
SVC IPv6 ACL ID: -1
SVC: adding to sessmgmt
SVC: Sending response
Sending X-CSTP-FW-RULE msgs: Start
Sending X-CSTP-FW-RULE msgs: Done
Sending X-CSTP-Quarantine: false
Sending X-CSTP-Disable-Always-On-VPN: false
CSTP state = CONNECTED
.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Nice write-up! Very useful ...
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Useful Information..
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Excellent document.. Very well summed up. Keep it going.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks.....I will be glad if it will help someone....
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Excellent Write Up. Very helpful indeed!!
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Very Helpful.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi.
I want to get your help.
I have only one question, subtree ldap-scope
where is subtree? what does it mean?Where can I find this parameter, because I did not see the word in the CMD
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:

