Introduction
This document describes a configuration example of Cisco Identity Services Engine (ISE) used for device administration of Cambium Devices using RADIUS protocol.
Prerequisites
Requirements
Cisco recommends that you have knowledge of these topics:
- Basic knowledge of Device Administration
- Fundamental knowledge of Radius Protocol
- Familiarity with Cambium Devices
Components Used
The information in this document is based on these software and hardware versions:
- Cisco Identity Services Engine (ISE) 2.4.0.357
- Cambium Networks Canopy PMP 450i Wireless Broadband Access Point
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any configuration.
Configuration
ISE Configuration
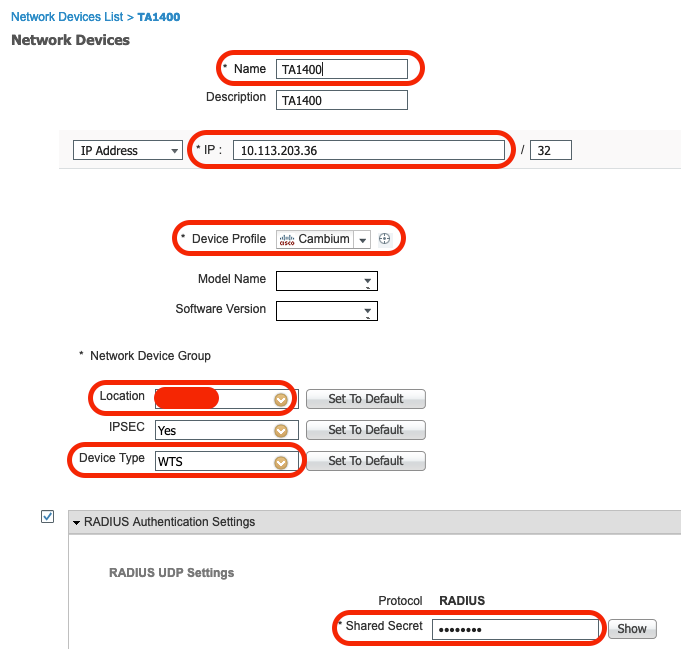
1. Add Cambium Device : with Radius secret key
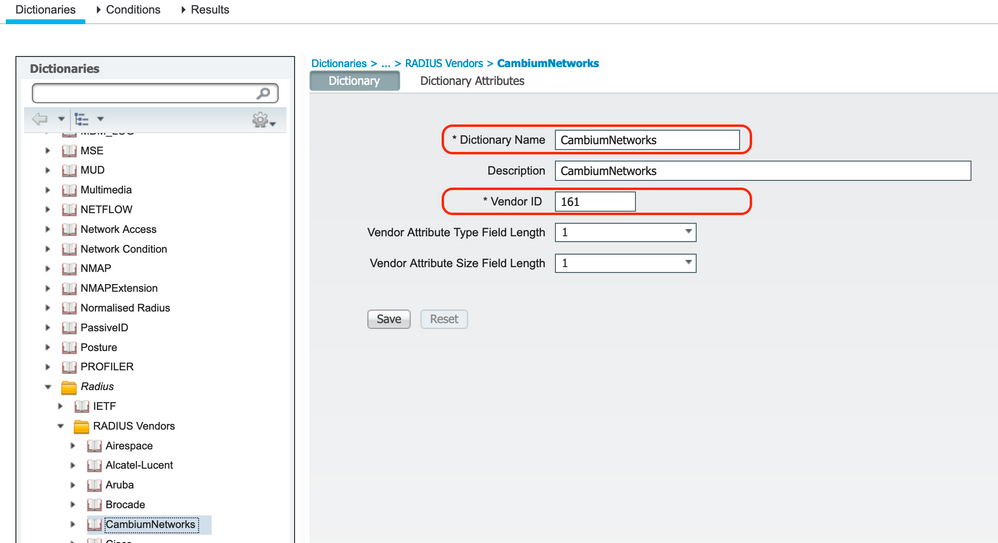
2. Add Cambium Vendor in Radius Dictionary :
Navigate to the path : Dictionary >> Radius >> Radius Vendors
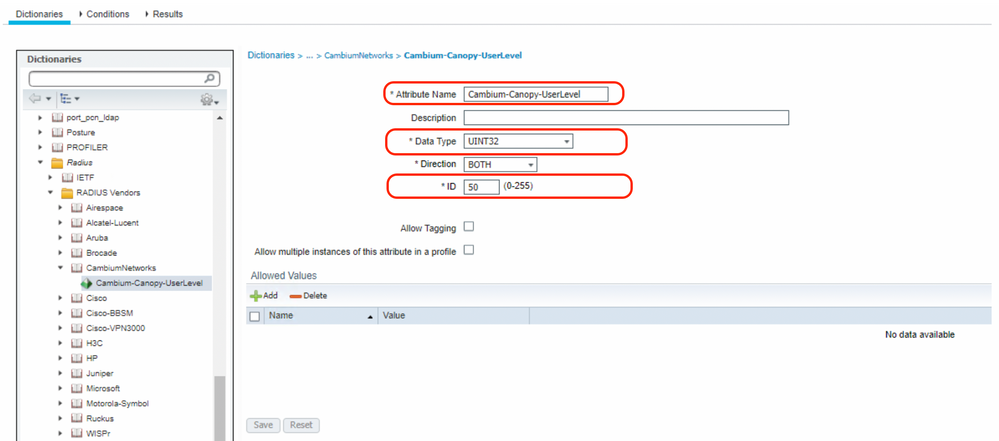
3. Add Cambium Vendor Attribute ID “Cambium-Canopy-UserLevel” ID : 50
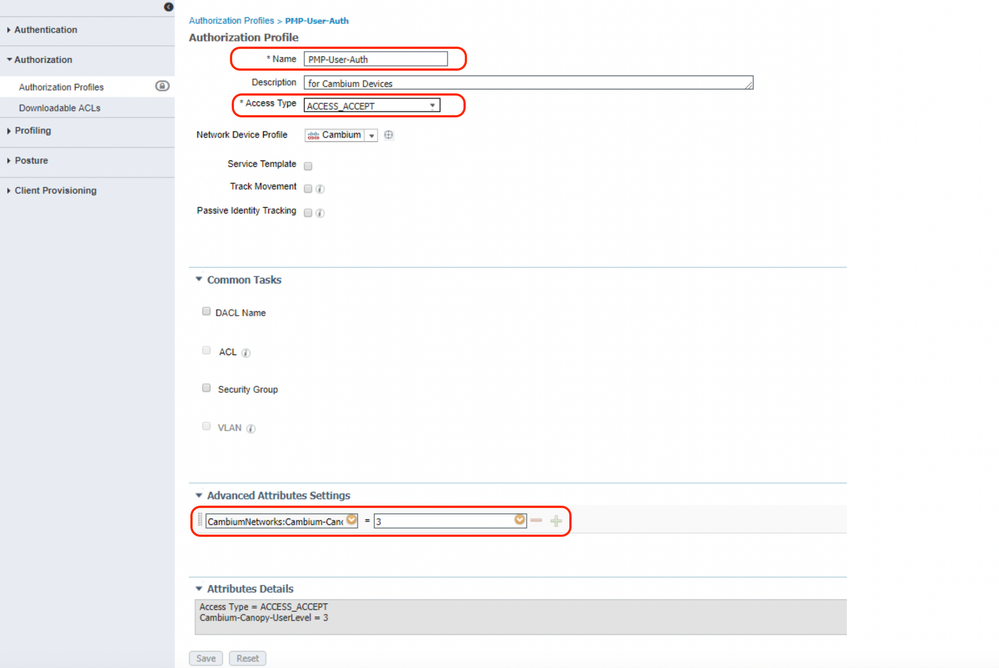
4. Authorization Profile
Values for device administration are as follows:
| Role |
Attribute Value |
| Installer |
1 |
| Technician |
2 |
| Admin |
3 |
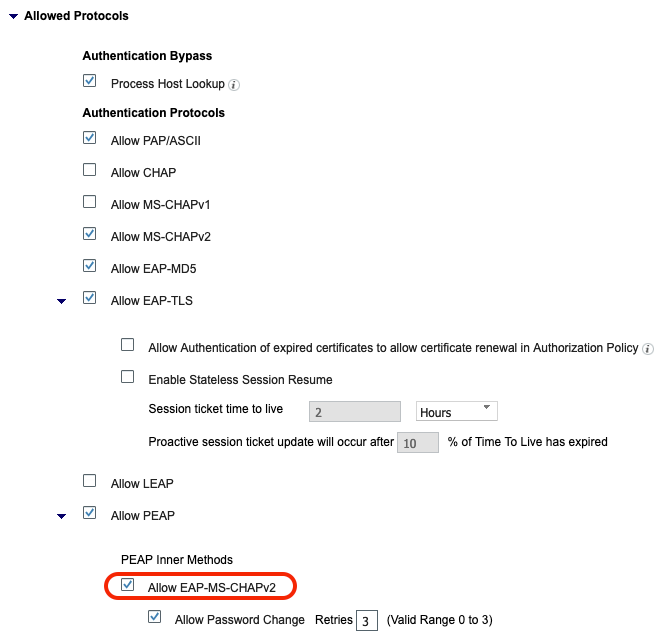
5. Allowed Protocols:
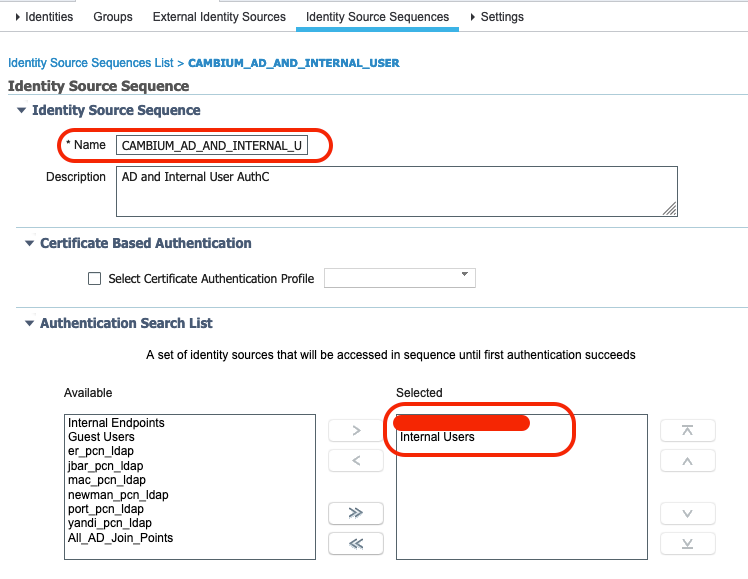
6. Identity Sequence based on AD and Internal users
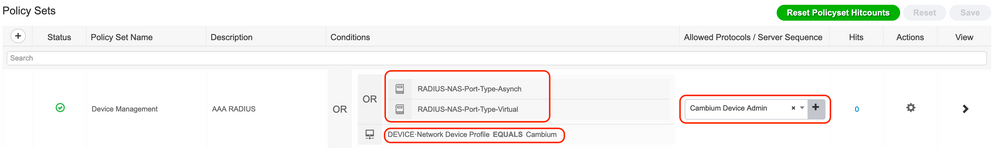
7. Policy Set
8. Authentication Policy

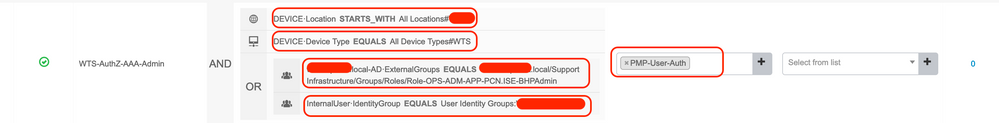
9. Authorization Policy
10. Cambium Device Configuration:
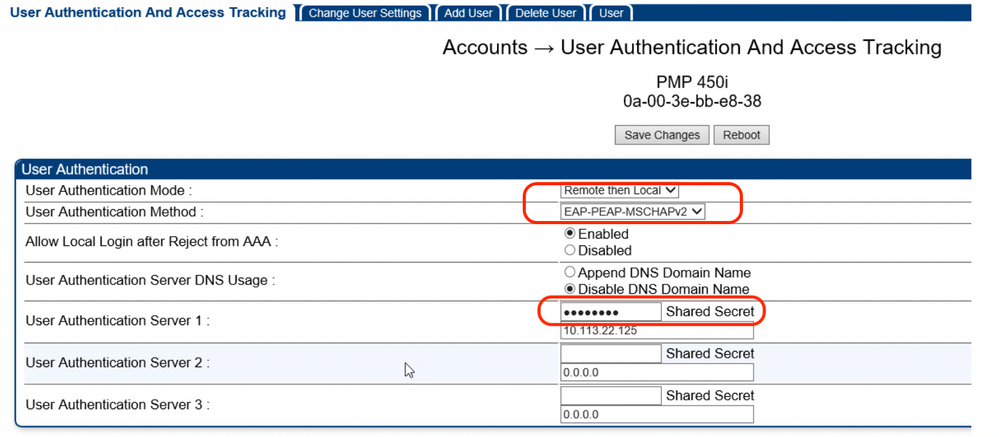
Please note that if you are using AD for user authentication, then Cambium device cannot be configured for EAP-MD5 as AD doesn't support that protocol.
In such case, device administration fails with the following error:
22043 Current Identity Store does not support the authentication method; Skipping it
Resolution is to configure Cambium device for EAP-PEAP-MSCHAPv2 rather EAP-MD5
Verify
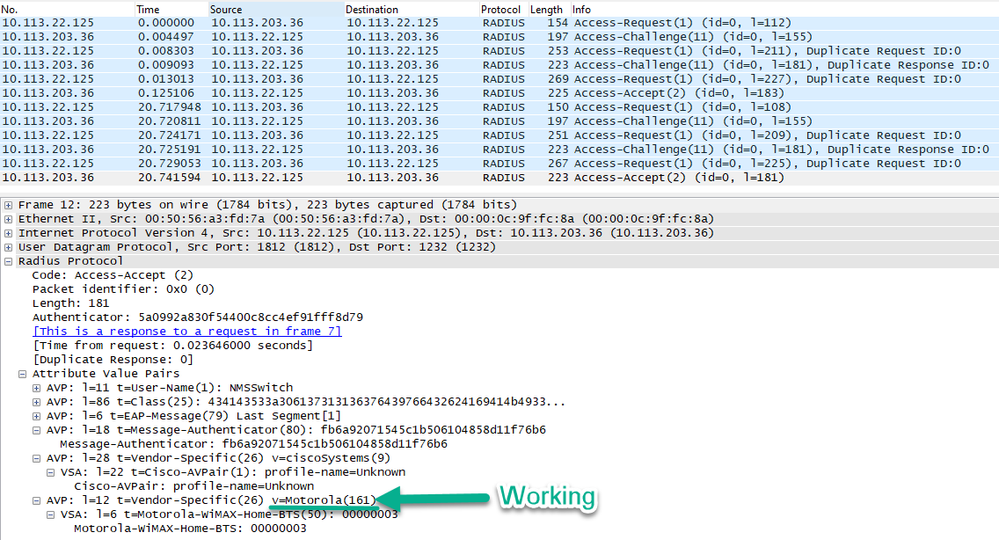
Working scenario should ideally show the below attributes being sent from ISE to Cambium device
Related information:
https://community.cambiumnetworks.com/t5/cnMaestro/Setting-up-Cisco-ISE-for-RADIUS-Services-to-Support-Cambium/td-p/91013
http://community.cambiumnetworks.com/t5/PMP-Best-Practices-and-Examples/Using-RADIUS-Server-with-PMP-450/m-p/52305#M22
http://community.cambiumnetworks.com/t5/PMP-Best-Practices-and-Examples/Cisco-ACS-RADIUS-Server-Support/m-p/48627#U48627