- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- FTD URL Filtering - How it works?
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
03-12-2018 11:37 PM - edited 03-08-2019 07:03 PM
- FP URL filtering capability can classify the URLs based on:
- Categories (classification)
- Reputation (risk level)
- This varies from High Risk (level 1) to Well Known (level 5)
- Category + Reputation
- Manual URLs
- If you select a reputation level to allow, all level below it will be allowed. Similarly, if you select a reputation level to block, all above levels will be blocked
|
Selected Reputation Level |
Selected Rule Action |
|
|
|
|
|
|
High Risk |
Suspicious Site |
Benign Site with Security Risk |
Benign Site |
Well Known |
|
1 - High Risk |
Block, Allow |
Allow |
Allow |
Allow |
Allow |
|
2 - Suspicious Sites |
Block |
Block, Allow |
Allow |
Allow |
Allow |
|
3 - Benign Sites with Security Risk |
Block |
Block |
Block, Allow |
Allow |
Allow |
|
4 - Benign Sites |
Block |
Block |
Block |
Block, Allow |
Allow |
|
5 - Well Known |
Block |
Block |
Block |
Block |
Block, Allow |
- URL filtering can be configured in
- HTTP
- FP will perform URL filtering for plain text traffic (either HTTP traffic or decrypted HTTPS traffic)
- Its configured in ACP by matching HTTP application and configuring URL Filter
- HTTPS Filtering
- FP detects the URL during SSL handshake from the certificate CN
- HTTPS URL filtering disregards subdomains in the CN and matches the root domain only (unlike HTTP which consider subdomains in HTTP requests)
- For example, if the CN contains www.example.com, FP will match example.com only
- Its configured in ACP by matching HTTPS application and configuring URL Filter
- SSL
- Manual URL filtering isn't supported in SSL
- Its configured in SSL Policy to match categories
- Manual URL Filtering
- You can override URL Categories and Groups by configurating manual URLs
- Wildcard isn't support
- For example, if you block a URL category which contains a single URL to be whitelisted, you can configure a rule with the whitelisted URL added manually before the blocking rule
- When configuring Manual URLs, any match of the URL string will trigger action. For example, if you allow all traffic to example.com, your users could browse to URLs including:
Note: To see URL category and reputation information in events and application details, you must create at least one rule with a URL condition
- Limitations of URL Filtering
- Connection will establish 3-way TCP handshake. Once SSL Exchange starts or HTTP request received, FP will be able to action (3-5 packets)
- Uncategorized URLs will pass through FP unless they are explicitly blocked
- FP won't block searches on blocked categories. For example, using a web search to search for amazon.com is not blocked, but browsing to amazon.com is blocked
- Due to low memory, low level appliances will use more generic matches. Example, the system might evaluate mail.google.com using the google.com category and reputation
- Impacted models are ASA5506-X, ASA5506H-X, ASA5506W-X, ASA5508-X, ASA5512-X, ASA5515-X, ASA5516-X, and ASA5525-X
- You can configure HTTP Response page (which will be displayed when ACP action is Block/Block with reset) and Interactive HTTP Response page (which will be displayed when ACP action is Interactive Block/Interactive Block with reset)
- It won't be displayed for HTTPS blocked URLs
TIP
- You can use URL filtering rule for allowing HTTPS access to a website while blocking HTTP access which is for security reason
- Create an ACP rule which matches HTTPS application and X URL - Action Allow
- Create an ACP rule which matches HTTP application and X URL - Action Block
How URL Lookup Process works?
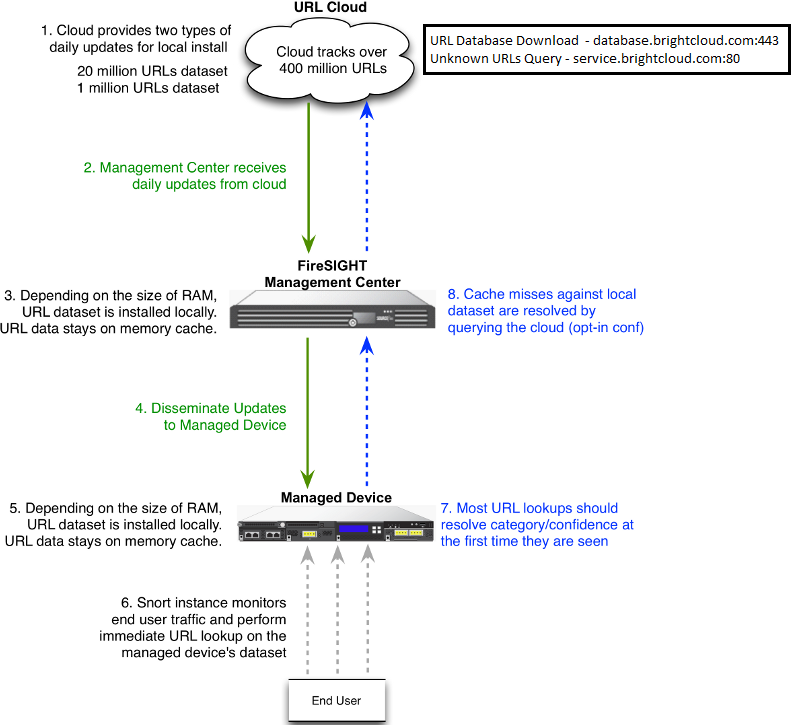
In order to accelerate the URL lookup process, the URL filtering provides a dataset that is installed on a Firepower System locally. Dependent upon the amount of memory (RAM) available on an appliance, there are two types of datasets:
|
Type of Dataset |
Memory Requirement |
|
|
|
On Version 5.3 |
On Version 5.4 or higher |
|
20 Million URL Dataset |
> 2GB |
> 3.4 GB |
|
1 Million URL Dataset |
<= 2GB |
<= 3.4 GB |
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hello,
How do you notify a worker that the HTTPS website he visited is blocked by the IT department?
I dont understand how the worker can know that if you cannot configure HTTP response page for HTTPS blocked URL.
Thanks in advance,
Lucas
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Lucas,
You can configure a HTTP block page as normal and use SSL decryption to decrypt blocked sites first, this way the end user will still see a block page response, rather than a timeout on those blocked pages.
Kind Regards,
David
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi,sir
- Due to low memory, low level appliances will use more generic matches. Example, the system might evaluate mail.google.com using the google.com category and reputation
- Impacted models are ASA5506-X, ASA5506H-X, ASA5506W-X, ASA5508-X, ASA5512-X, ASA5515-X, ASA5516-X, and ASA5525-X
I want to know if it affects Manual URL Filtering? I wanted to use the FTD's Manual URL Filtering to manage the whitelist strategy for data center access to the Internet.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi @Mohammed al Baqari ,
Can I use URL filtering together with application control? My use case is to allow FTP using a specific URL.
Thanks
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community:

