- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- Managing ONS with Radius Credentials
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
09-24-2013 07:58 AM - edited 02-21-2020 10:00 PM
Introduction
Users with Superuser security privileges can configure nodes to use RADIUS authentication.
An ONS node operates as a client of RADIUS. The client passes user information to designated RADIUS servers, and then acts on the response. RADIUS servers receive user connection requests, authenticate the user, and return all configuration information necessary for the client to deliver service to the user.
Configuration
- Create a user on ACS with CiscoSecure PAP password that we will use to login ONS
- Assign the above created user 454supper to FullAccessGroup group by going tp Group Setup.
- Defining ONS as a Radius client
- Login To ACS
- Click on Network Configuration.
- Click on ADD Entry.
- Name the Client hostname unique.
- Enter the ip address of the ONS node.
- Enter the shared secret key, should be same as Node/ONS config.
- Make sure Authenticate Using set to "Radius(CiscoIOS/PIX 6.0)
User Security Group Mapping
The possible security levels are Retrieve, Maintenance, Provisioning, and Superuser.
An attribute-value (AV) pair represents a variable and one of the possible values that the variable can hold. Within ONS, users are mapped to different security groups based on Cisco AV Pair. Here is an example:
"shell:priv-lvl=X" where X can be value of 0 to 3: 0 represents Retrieve . 1 represents Maintenance 2 represents Provisioning 3 represents Super
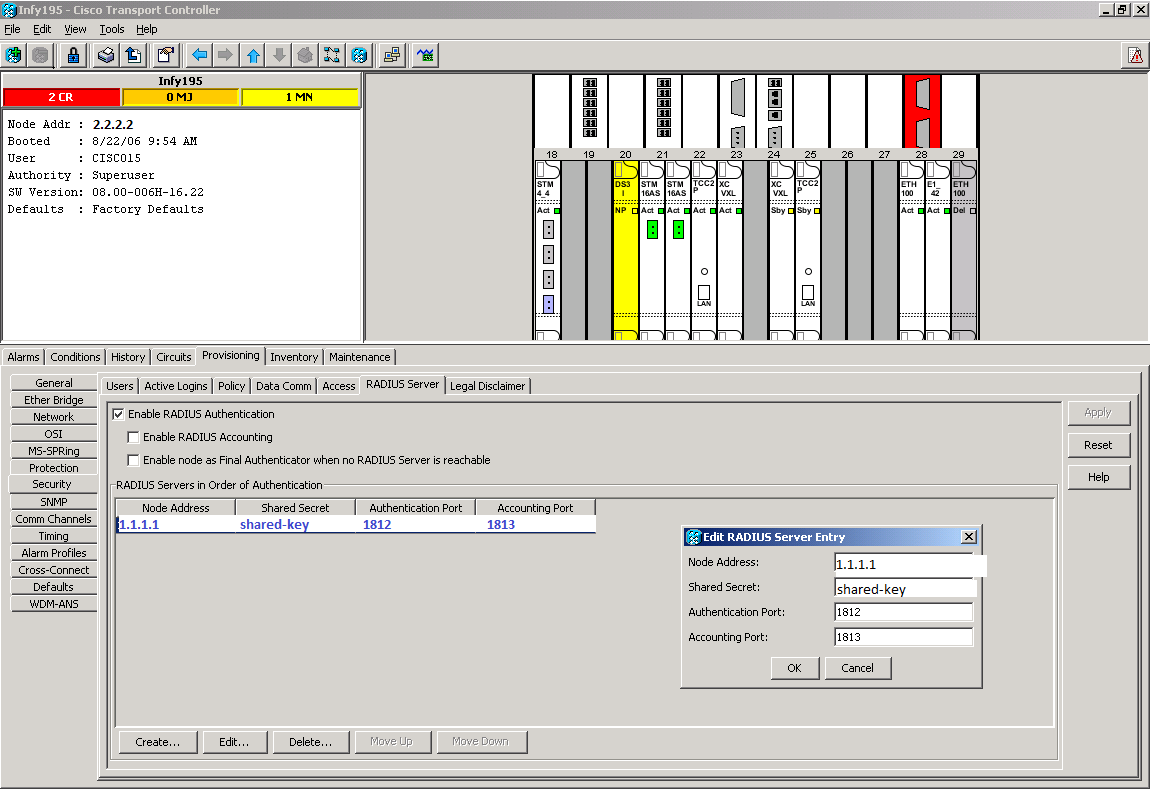
Defining RADIUS Server On ONS
- Log into Cisco Transport Controller (CTC).
- Go to the Network view.
- Select a specific ONS in order to go to the Shelf view.
- Click Provisioning > Security > RADIUS Server.
- Type the IP address of the RADIUS server in the IP Address field.
- Type a shared secret in the Shared Secret field. A shared secret is a text string that serves as a password between a RADIUS client and RADIUS server.
- Type the RADIUS authentication port number in the Authentication Port field.
- The default authentication port number is 1812.
- Type the RADIUS accounting port number in the Accounting Port field. The default accounting port number is 1813.
Troubleshooting
- Check ACS logs under reports and activities > failed authentication.
- Make sure shared-secret key is same on both the sides.
- In order to get rds.log file, set the logging level to full and generate package.cab file.
- In some cases even your configuration is correct and you see an extra attribute "aaa:supplicant-name=<username>" in the RDS logs pushing down to ONS then this will cause ONS to fail authorization. In order to fix this go to Interface Configuration > RADIUS (Cisco IOS/PIX 6.x) and uncheck the "Enable Authenticated Port cisco-av-pair" option.
Reference
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi
I have this working on ACS 4.2 but I have upgraded to ACS Version : 5.5.0.46 and I am now unable to login. I have configured the rules and ACS logs are showing it's successful but on CTC I get error
EID-2199
Login failed on <IP address>
Exception = The Login did not succeed
Any chance you can update this article for the configuration required for ACS 5.x?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Cuellar52
Not sure if you got your answer, but you have to configure a custom attribute. Here are the steps:
Policy Elements>Authorization and Permissions>Network Access>Authorization Profiles>Create
Under the "General" tab
Name: Cisco ONS Profile
Under "RADIUS Attributes" tab
Under Manually Entered:
Dictionary Type: RADIUS-Cisco
RADIUS Attribute: cisco-av-pair
Attribute Type: String
Attribute Value: Static
Attribute Value: "shell:priv-lvl=3"
Click - ADD
Dictionary Type: RADIUS-IETF
RADIUS Attribute: Service-Type
Attribute Type: Enumeration
Attribute Value: Static
Attribute Value: Login (Click the Select button to the right and select "Login" and click "OK)
Click - ADD
Then click "Submit"
Add a rule to Authorize Authentication
Access Policies > Access Services > Default Network Access > Authorization
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: