- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- Network Access and Segmentation with DUO MFA and ISE Configuration Guide
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
on
12-13-2018
06:00 PM
- edited on
01-21-2020
12:49 PM
by
thomas
![]()
Overview
Securing the network by ensuring the right users, the right access, to the right set of resources is the core function of Cisco’s Identity Services Engine (ISE). ISE builds context about users (Who), device type (What), access time (When), access location (Where), access type (wired/wireless/VPN) (How), and most important threats, and vulnerabilities. All of these pieces of contextual data is fed into defining logical policy groups, called Scalable Group Tags, for every connected endpoint. These context-aware tags are then used to form the basis of security policies, centrally managed on ISE and enforced on different parts of the network in a traditional way or using the network fabric- as part of Software Defined Access (SDA).
Duo Security is highly aligned to our intent-based networking vision and strategy, and reinforces our existing ISE and DNA Center capabilities. Additionally, it will help accelerate the adoption of SDA, by extending policy into the cloud and by unifying network segmentation with cloud access control. We are bringing together zero trust workforce capabilities from Duo, with zero trust workplace capabilities from SDA, to create the industry's only comprehensive Zero Trust capable network
Configuration Objective:
“I have employees and contractors on my network. My objective is to securely connect these users by using MFA and then assign them a secure network policy by using ISE for segmentation. Employees and Contractor’s are on the same network but they cannot talk to each other. Employee’s get full access to my on-prem network resources or network resources in my data center, Contractors get limited network access.
Configuration Overview:
Configure ISE’s web-based authentication portal as a protected application with Duo MFA. After successful 2FA, ISE grants users network access based upon Group-Based Policies.
Segmentation Policy:
- Employees connect to the network and get a network policy with SGT=Employee
- Contractors connect to the network and get a network policy with SGT=Contractor
Connection flow: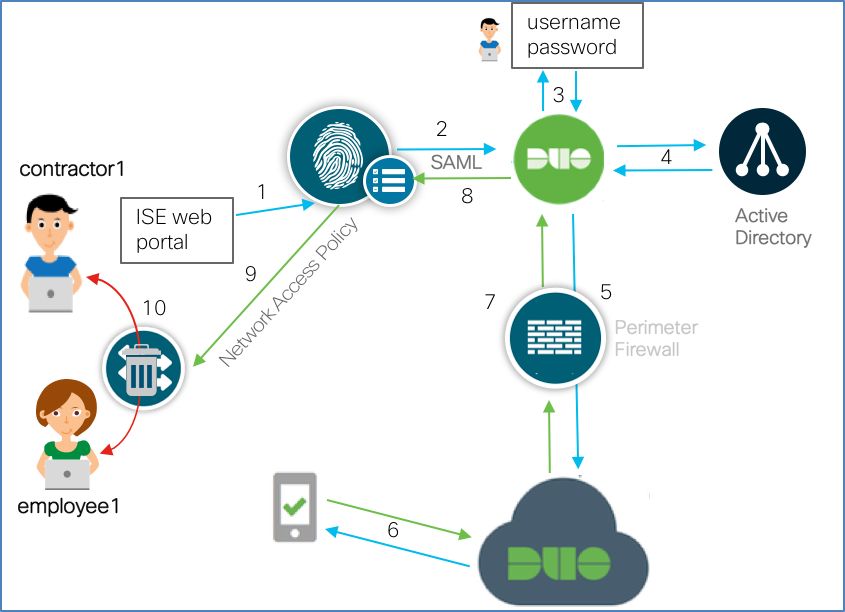
- Users connects and is redirected to ISE portal
- ISE redirects the unauthenticated request to the Duo Access Gateway (DAG)
- Because the ISE portal is a protected application, prompts the user for authentication
- Users’s credentials are verified against Active Directory
- DAG then sends notification for MFA
- Users get a notification for DUO PUSH, Users click “Approve” on mobile device
- DAG receives authentication success notification.
- ISE receives response
- ISE authorizes network access and pushes Employee or Contractor Scalable Group Tag (SGT)
- As per SGT-based network policy, Employees and contractors are on the same Layer 2 network but cannot talk to each other (East-West segmentation/Microsegmentation)
Configuration Part 1: Protecting ISE web portal with Duo MFA
The Duo terminology “protecting an application” simply means that access to that application is redirected through the Duo Access Gateway. This redirection is necessary to add in second factor authentication before allowing application access (this assumes that network layer access is not restricted). In addition, the DAG can also enforce additional application policies such as checking the user, device, and network permissions specified by the DUO Administration panel.
Adding an application to Duo
Note: Before proceeding it is assumed that an identity source has been configured. If this step has not been done, please reference Duo Access Gateway for more details.
The steps below ties in the ISE Guest web portal as a protected application to add in the secondary authentication sequence with Duo PUSH. ISE Guest allows users to gain network access via a HTTP or HTTPS login. Duo Single Sign on will then initiate the 2nd authentication back to the user via DUO push.
- Log into your DUO Access Gateway
- In the left side bar, navigate to Applications
- Scroll down to the center of the page to the MetaData section and click “download XML metadata” and save the file
- Log into ISE
- Navigate to Administration->Identity Management->External Identity Sources->SAML ID Providers
- Click ADD
- On the resulting window, starting from left to right, configure the settings within each tab menu item as follows:
- In the General tab, use “duoSAML” as the Id Provider Name
- In the Identity Provider Config tab, upload the xml file from Step 3
- Skip the Service Provider Info tab, you’ll come back to it later
- In the Groups tab, select the user groups relevant to your authentication requirements
- Click Submit
8. Navigate to Work Centers->Guest Access->Portals & Components->Guest Portals
9. Click the link Sponsored Guest Portal (default)
10. Expand “Portal Settings” and select the profile name configured in step 5a. (e.g. duoSAML)
11. Click Save
12. Navigate back to Administration->Identity Management->External Identity Sources->SAML ID Providers-duoSAML
13. From the Service Provider Info tab, click Export and save the resulting zip file.
Note: The files in this zip contain the application configuration data required to bind Duo to the ISE guest portal
Binding ISE web authentication portal with Duo
15. Extract the zip and view the extracted xml file
16. Search for the "Entity ID" string and copy the resulting string ( the string would look something link this: "http://CiscoISE/f079c670-7159-11e7-a355-005056aba474")
17. Log in to the Duo Admin Panel and click Applications, and then click Protect an Application
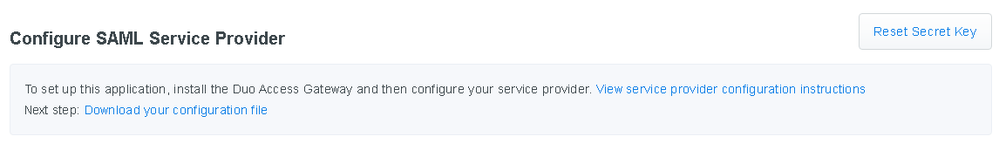
18. Locate SAML Service Provider in the list of applications, and then click the Protect this Application link.
19. Enter the following information:
| Name | Description |
| Service Provider Name | e.g. ISE Portal |
| Entity ID | copied string from Step 16 |
| Assertion Consumer Service | https://<ISE FDQN>:8443/portal/SSOLoginResponse.action |
20. Scroll to the bottom and click Save Configuration button and download the configuration file.
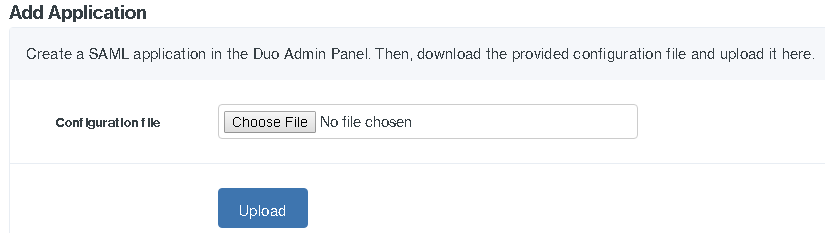
Add ISE Portal to Duo Access Gateway
21. Log in to the Duo Access Gateway
22. Navigate to Applications. Upload the .json configuration file from Step 20
Verifying ISE and DUO MFA
23. On ISE, navigate to Work Centers->Guest Access->Portals -> Components->Guest Portals
24. Click the link Sponsored Guest Portal (default)
25. Right click and copy the link for “Portal Test URL”
- Paste the link address into a text editor
- Change the link address from using the ISE IP to the ISE FQDN (include port 8443)
Note: These steps are to workaround an ISE defect
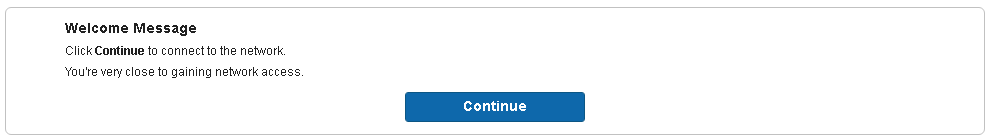
26. Paste the edited link into a browser. After successfully authenticating, you should see the following pop up
27. Click Continue. This concludes the test
Finalizing ISE and Duo MFA Integration
In the steps below, you will enable web authentication so that users are redirected to the ISE Guest Portal to start the MFA process.
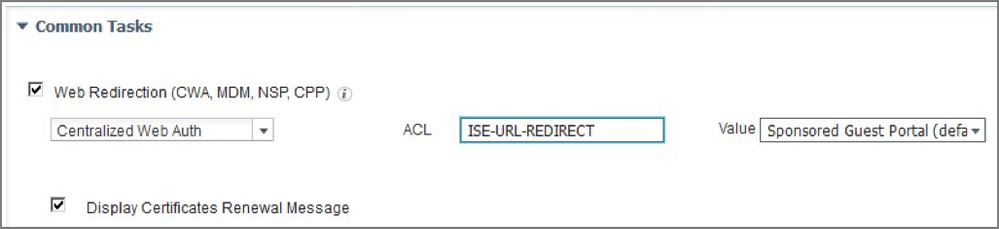
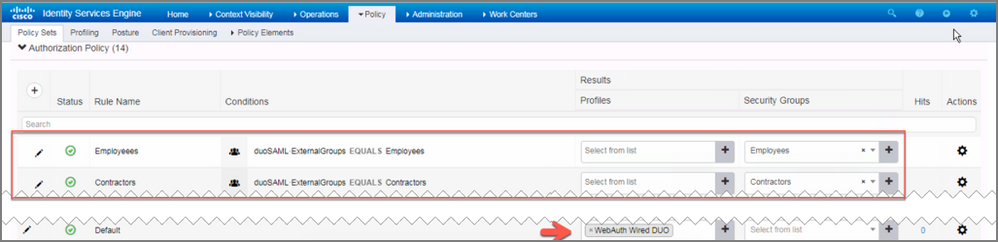
28. Log into ISE, navigate to Policy->Policy Elements->Results->Authorization->Authorization Profiles
29. Create an authorization profile, such as “WebAuth Wired DUO”, with the following configuration:
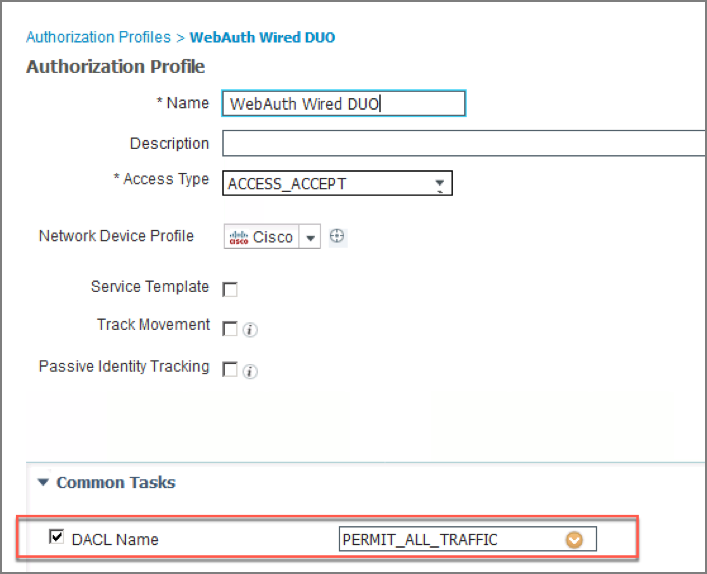
30. Continue to scroll down within Common Tasks to select “Web Redirection”. Configure as follows:
31. Click Submit
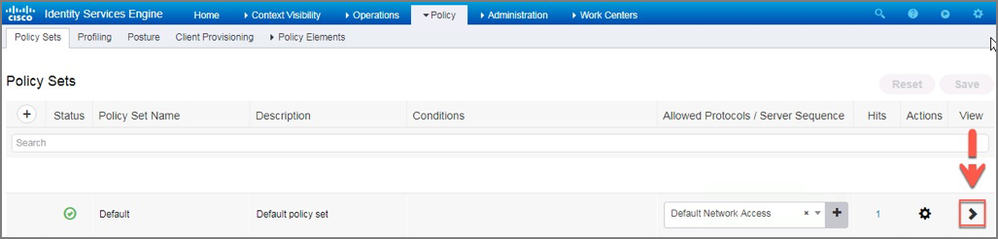
32. Navigate to Policy->Policy Sets
33. Expand the default policy set by clicking the > on the right of the screen
The resulting view will look like this:
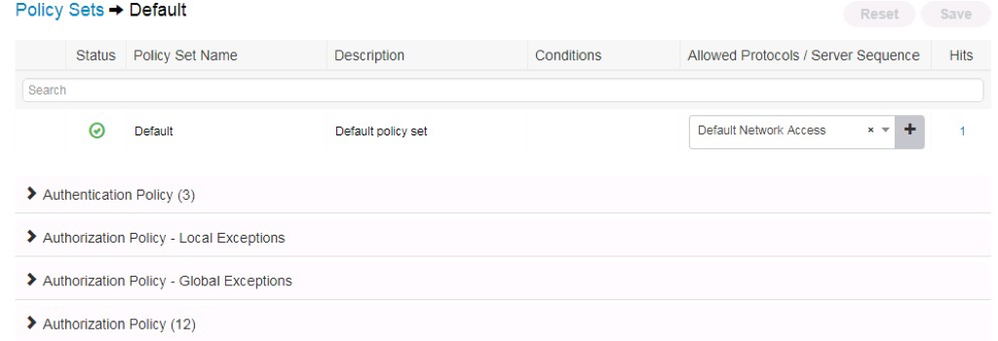
34. Expand Authorization Policy. Add new policies that reference the SAML groups from Step 7. Also modify the Default policy to user the "WebAuth Wired DUO" profile rather than "Deny Access"
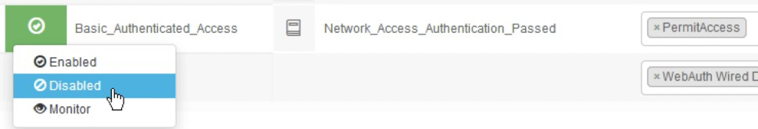
Note: Also disable the Basic_Authenticated_Access rule
Configuration Part 2: Securing Network Access with Micro-Segmentation
In the previous exercise you configured ISE and DUO to work together to secure the network connection process with Duo MFA. Now that the user is connected, in the steps below you will further secure network access using group-based segmentation. In the example below, the policy created will mitigate the spread of malware between Employees and Contractors.
Note: For clarity, configuration specific to backend TrustSec functions is omitted from the steps below. Please reference the Appendix for TrustSec specific configuration details.
1. On ISE, navigate to Work Centers->TrustSec->TrustSec Policy
2. Select ADD in the policy matrix menu
3. Configure new policies as follows:
4. Click Save
Note: The “Anti-Malware SGACL” contains rules that deny specific tcp and udp traffic. To review the rules contained within this SGACL, navigate to Work Centers->TrustSec->Components->Security Group ACLs
Appendix
TrustSec Configuration
Configuring Identity Services Engine for TrustSec
Classification
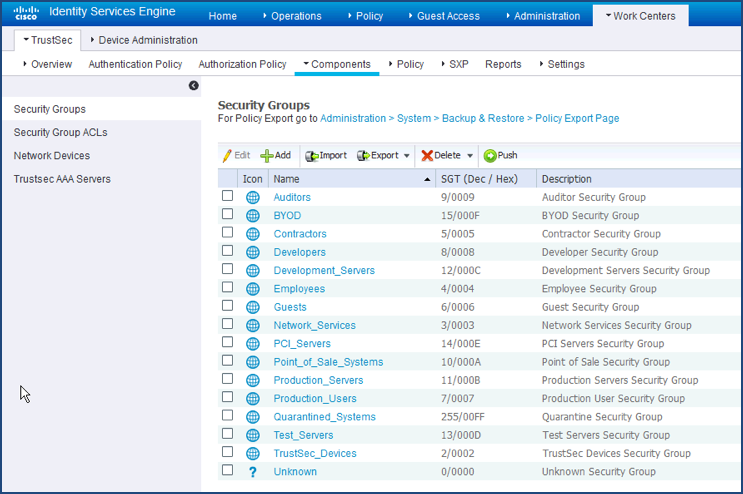
Every TrustSec deployment starts with classification. Classification is the process of defining and assigning a Security Group Tag (SGT) that is used to represent the group a server or user belongs to. These classifications are downloaded to TrustSec devices that will either forward them to other TrustSec devices and/or use them for enforcement.
This example has the users categorized as employees and contractors which are pre-defined security groups in ISE. By default, ISE has 16 pre-defined, commonly used, security groups.
1.
Defining TrustSec Devices within ISE
ISE communicates with network devices for many tasks. In the classification phase, network device queries ISE to authenticate and authorize users and devices. For enforcement, the enforcement device queries ISE to retrieve access policy and keeps its policy table up-to-date. In the following section you will register the 3k-access switch to exchange these pieces of information
TrustSec Switches
1. Navigate to Work Centers→TrustSec→Components→Network Devices
2. Edit/Add your access layer switch
3. Select the Advance TrustSec Settings checkbox. This expands the SGT attributes of the Network Device definition.
4. Set the password
5. Click Save
SGT Assignment
Device SGT
In a TrustSec enabled network, all switches that join the TrustSec domain are classified with a SGT (commonly referred as the “device SGT”). This classification occurs as result of the switches authenticating to ISE, a process called Network Device Admission Control (NDAC). Once the switches have this SGT, traffic that is initiated from the switch will be tagged with this SGT.
1. Navigate to Workcenters->TrustSec->Policy->Network Device Authorization
2. Click “Edit” (you may need to scroll to the right to see this)
3. Modify the rule to use the TrustSec_Device_SGT tag as shown below
4. Click Save
TrustSec Policy Acquisition
Policy Acquisition phase in the TrustSec architecture is to establish pipeline between network device and ISE, and eventually download necessary policies for enforcement. Information exchanged in this pipeline would be Security Group Tag value and its name, Device SGT, and other policy expiration timer to keep the policy up-to-date on each device.
In order for network device to query ISE and obtain appropriate policies or policy elements, network devices authenticate to ISE, claiming its privilege to download such policies. We are going through configurations based on the network device type.
Policy Acquisition on 3650
1. Configure the credentials that will used for NDAC
3k-access#cts credentials id 3k-access password ISEisC00L
2. Configure the 3650 to obtain policy from ISE. Enter configuration mode (configure terminal) and enter the following commands:
aaa authorization network CTS-MLIST group radius
cts authorization list CTS-MLIST
radius server ise-1
address ipv4 10.1.100.21 auth-port 1812 acct-port 1813
pac key ISEisC00L
exit
server name ise-1
Verifying Policy Acquisition on 3650
- Verify PAC is provisioned on 3650
3k-access#show cts pac
AID: 5CA42F60834DE482B716028EAA4EFA8B
PAC-Info:
PAC-type = Cisco Trustsec
AID: 5CA42F60834DE482B716028EAA4EFA8B
I-ID: 3k-access
A-ID-Info: Identity Services Engine
Credential Lifetime: 15:53:10 UTC Oct 29 2014
PAC-Opaque: 000200B800030001000400105CA42F60834DE482B716028EAA4EFA8B0006009C00030100DCC3AF447CA810C1442E417A2FB6F8720000001353D1ABB400093A808ACFEF1042BA878EB3585CEE1B108AE45D6F5896B493430DE24C25686AE418C5EEFDE44606C9D3FB09A0E8AB261C98D00EC9F42567D377636A88CC9125A3FDB458F9A4FBE8AF4530D616584C1B146B920913422B30EA50184D6C72923A364B1735F60857591440879815021F9404868FE2DAA13C1807FCB1464C2C57
Refresh timer is set for 12w4d
- Verify the CTS environment download data has been downloaded
3k-access#show cts environment-data
CTS Environment Data
====================
Current state = COMPLETE
Last status = Successful
Local Device SGT:
SGT tag = 2-00:TrustSec_Device_SGT
Server List Info:
Installed list: CTSServerList1-0001, 1 server(s):
*Server: 10.1.100.21, port 1812, A-ID 5CA42F60834DE482B716028EAA4EFA8B
Status = ALIVE
auto-test = TRUE, keywrap-enable = FALSE, idle-time = 60 mins, deadtime = 20 secs
Security Group Name Table:
0-00:Unknown
2-00:TrustSec_Device_SGT
3-00:Network_Services
4-00:Employees
5-00:Contractors
Environment Data Lifetime = 86400 secs
Last update time = 15:54:16 UTC Thu Jul 31 2014
Env-data expires in 0:23:46:47 (dd:hr:mm:sec)
Env-data refreshes in 0:23:46:47 (dd:hr:mm:sec)
Cache data applied = NONE
State Machine is running
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: