- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- SecureX Frequently Asked Questions
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
03-01-2021 08:33 AM - edited 08-01-2023 06:43 AM
- General
- Which Cisco Secure products include access to SecureX?
- Where can I find a curated, start-to-finish learning experience to teach me about SecureX?
- What are the SecureX data retention/privacy policies?
- What is SSE?
- How can I unlink my smart account from SSE and link it to a new account?
- Do I have to use the same SSE region as the SecureX region I am using?
- What is the browser plugin and how can I get it?
- Sign In
- Sign in methods
- Since SecureX include SecureX Signon, why are there three signon methods?
- Which of the sign in methods should I use?
- How do I access SecureX using CSA (Cisco Security Account) credentials?
- I would like to use a third party identity provider with SecureX Signon. Which ones are supported?
- I have other Sign On questions
- Cisco Threat Response migration
- How does SecureX relate to and/or compare to Threat Response?
- I signed up for SecureX and signed in with SecureX Sign-On. When I arrived in SecureX, the modules and users I had setup in CTR were missing. How do I get that back?
- SecureX threat response
- Is there a limit to how much input I can provide to an investigation?
- Is there a limit to how many nodes can be shown in the Relations Graph?
- I have another question about SecureXthreat response
- SecureX orchestration
- I launched SecureX orchestration and got an "upstream connect error"?
- How do I get a workflow I wrote to appear in the threat response/ribbon/etc pivot menus on observables?
- If I use the Python Adapter, where does my Python script actually run?
- What modules are available in the Python Adapter?
- How can I use local, on-premise devices in orchestration workflows?
- Using SecureX with Cisco Products
- General
- Is an integration with [insert Cisco Security product] on the roadmap?
- What scopes are needed for the API Client used by the SecureX ribbon?
- Cisco Secure Endpoint (Formerly known as AMP for Endpoints)
- What features are enabled by integrating AMP into SecureX?
- How can I set up AMP in SecureX?
- Firepower Devices (NGFW)
- What features are enabled by tying Firepower devices into SecureX?
- What version of the Firepower software is required to support SecureX functions?
- How can I set up my Firepower device in SecureX?
- Can Firepower devices licensed via a Smart Software Satellite Server be integrated with SecureX?
- SMA (Security Management Appliance)
- What version of SMA is needed to use it with SecureX?
- Cisco Secure Email (Formerly Cisco Email Security Appliance)
- What version of AsyncOS is required to enable the SecureX features?
- Cisco Secure Analytics (Formerly known as Stealthwatch Enterprise or SWE)
- What version of SWE is needed to use it with SecureX?
- Stealthwatch Cloud
- What capabilities does SWC support in SecureX, and vice versa?
- Where can I get directions how how to integrate SWC with SecureX?
- Using SecureX with Third Party Products
- Browser plugins
- What browsers support the SecureX plugin?
- What does the browser plugin do?
- How is the plugin configured?
- Integration Status
- Is there an integration with [insert product]... What is the current list of third party integrations with SecureX?
- Relay Modules
- What is a Relay Module?
- Who hosts the relay?
- Where can I get the relay code?
- What are the IPs I need to allow to connect to my relay module?
- SecureX Administration
- What are the differences between the "User" and "Admin" account roles?
General
Which Cisco Secure products include access to SecureX?
Eventually, all will. At the current time, a license to any of the Cisco products listed here grants immediate rights to use the SecureX platform:
https://www.cisco.com/c/en/us/products/security/securex/securex-integrations.html
Note that for many of the on-premise products, there will also be version number requirements - consult the relevant documentation for more information.
Where can I find a curated, start-to-finish learning experience to teach me about SecureX?
The guided and curated SecureX learning experience is at SecureX Academy. There are hundreds of videos, FAQs, documents, etc all about SecureX available online, but this takes the best of them and organizes them into a meaningful curriculum that is easily followed and progresses in a logical, consumable order.
What are the SecureX data retention/privacy policies?
The short, functional answer: SecureX doesn't keep data. We are not a data aggregator, we are an API aggregator. The products keep their own data; SecureX only asks questions. Each product has its own data retention policies. We ask our questions, we get our answers, and we keep those answers for as long as the user is looking at them, and no longer. Users can store data in SecureX... Incidents, snapshots, casebooks, judgments. That is opt in only. And we store each of those until the user opts to delete it.
The longer, legalese answer: SecureX adheres to the general Cisco Cloud Services privacy policies, and the specific SecureX document can be seen here.
What is SSE?
SSE (Security Services Exchange) is the cloud-hosted data and authentication broker that facilitates communication between SecureX and on-premise devices such as Firewalls and Email / Web security appliances. Authentication to and through SSE is handled by tokens and/or Smart Accounts.
How can I unlink my smart account from SSE and link it to a new account?
In order to unlink your Smart Account from your Security Services Exchanges (SSE) organization you use the controls available in SSE. You can then link that Smart Account to another SSE organization in the usual fashion.
Do I have to use the same SSE region as the SecureX region I am using?
Yes. There is no option or reason to do otherwise, and all inter-service communications started by either service assume that the other service's region is the same as its own.
What is the browser plugin and how can I get it?
The browser plugin is an applet that lives in your browser (for Chromium and Firefox based browsers, including MS Edge). It allows you to take all the tools in the Ribbon with you everywhere you go on the web, including the Incident Manager, casebook and Orbital ribbon apps, and the ability to scrape browser content for observables and immediately take response actions and/or pivot into details investigations of them in your environment.
More information on obtaining and configuring the browser plugin can be found in the plugin FAQ here:
https://community.cisco.com/t5/security-documents/how-do-i-configure-the-securex-browser-plugin/ta-p/3935010
Sign In
Sign in methods
Since SecureX include SecureX Signon, why are there three signon methods?
SecureX includes SecureX Signon (SXSO), which is an identity provider (IdP). SecureX also, however, honors IdP services provided by Cisco Security (aka "CS", "CSA", or "Cisco Security Account") and Threat Grid. Users are given the option for backwards compatibility purposes. CS accounts will be migrated into SecureX Signon as SXSO accounts, and Threat Grid users will be migrated into using SecureX Signon as well.
Which of the sign in methods should I use?
ONLY If you are not already a user of Threat Response, Secure Endpoint (AMP for Endpoints), or the Secure File Analysis (Threat Grid) cloud portal, you should create a SecureX account.
If you are already a user of any of those products, please refer to this document for further instruction:
https://www.cisco.com/c/en/us/td/docs/security/securex/sign-on/securex-sign-on-guide.html
How do I access SecureX using CSA (Cisco Security Account) credentials?
Navigate directly to securex.us.security.cisco.com and choose 'Cisco Security' as the identity provider. From here you will be redirected to https://auth.amp.cisco.com/ where you can enter a username and password or choose single sign-on (users managed at https://castle.amp.cisco.com).
I would like to use a third party identity provider with SecureX Signon. Which ones are supported?
More info about 3rd party IdP support is available here:
https://www.cisco.com/c/en/us/td/docs/security/secure-sign-on/sso-third-party-idp.html
I have other Sign On questions
An excellent introduction to the concepts and operation of SecureX Signon is available here:
As well, please refer to this page for more SecureX Sign on answers and guidance:
Cisco Threat Response migration
How does SecureX relate to and/or compare to Threat Response?
Threat Response, released in early 2018, is now part of SecureX. Threat Response features, configurations, saved data etc, will remain intact for existing users who are now accessing Threat Response as part of SecureX. For more information, see this document: https://www.cisco.com/c/dam/en/us/products/se/2020/7/Collateral/securex-threat-res-faq.pdf
I signed up for SecureX and signed in with SecureX Sign-On. When I arrived in SecureX, the modules and users I had setup in CTR were missing. How do I get that back?
CTR did not use SecureX sign-on accounts. CTR used and still uses a different login, either a "Cisco Security Account" or a Threat Grid login. You signed into SecureX with an account that's not connected to your CTR organization. If you’re already using CTR, keep using the same account for SecureX. That will connect SecureX to CTR for you. You can keep your SecureX sign-on account and use it to connect to other products including Umbrella, Cisco Defense Orchestrator, Stealthwatch Cloud, Meraki, and Cloudlock. In the future, we'll migrate Cisco Security Accounts to SecureX sign-on. For more information, see this article.
SecureX threat response
Is there a limit to how much input I can provide to an investigation?
It is recommended that input be no more than 2000 characters. Longer inputs can be chunked for inspection (the process of discovering observables in the text) and then the resultant observables, if less than 2000 characters, can be submitted for a single unified investigation.
Is there a limit to how many nodes can be shown in the Relations Graph?
Yes, the graph will not show more than 200 nodes at a time. If that limit is exceeded in the data, there is a hierarchy applied and only the top 200 will be drawn.
I have another question about SecureX threat response
While we consolidate resources, please check in the Threat Response FAQ for answers to questions about SecureX Threat response.
SecureX orchestration
I launched SecureX orchestration and got an "upstream connect error"?
If you launch orchestration and come across an error that says "upstream connect error or disconnect/reset before headers. reset reason: connection termination" please clear your browser cache and launch orchestration again. This is a known issue the SecureX team is working to resolve.
How do I get a workflow I wrote to appear in the threat response/ribbon/etc pivot menus on observables?
For a custom workflow to appear in the pivot menu, two things have to be true. It has to have a category label of "response" applied to it, and it has to have been validated. For it to work, it also has to take two input variables, "observable_type" and "observable_value". These corresponding to the two pieces of information about the observable that are provided to the workflow by SecureX threat response when the workflow is called from that observable's menu.
If I use the Python Adapter, where does my Python script actually run?
The Python interpreter is included in the Action Orchestrator interpreter, which is hosted in the SecureX cloud infrastructure.
What modules are available in the Python Adapter?
You can check at any time by running the following python command as a part of, or as the entirety of, the script to be run in the adapter:
help("modules")
How can I use local, on-premise devices in orchestration workflows?
A remote adapter has been developed to address this need. See https://ciscosecurity.github.io/sxo-05-security-workflows/remote/
Using SecureX with Cisco Products
General
Is an integration with [insert Cisco Security product] on the roadmap?
Yes. All Cisco Security products will be SecureX-capable.
What scopes are needed for the API Client used by the SecureX ribbon?
To enable the Ribbon in other products, generate an API client with the following scopes enabled (checked):
[casebook, enrich, global-intel, inspect, integration, orbital, private-intel, profile, registry, response, telemetry, users].
The credentials for this API Client can then be provided to all ribbon-capable products to enable all Ribbon features in that product's UI.
Cisco Secure Endpoint (Formerly known as AMP for Endpoints)
What features are enabled by integrating AMP into SecureX?
AMP for Endpoints provides Visibility and Control. By adding AMP for Endpoints to SecureX, investigators will be able to search for IP addresses, domains, URLs and file hashes that have been recorded by AMP for Endpoints. AMP for Endpoints also provides you the capabilities within Threat Response to block a file SHA or isolate an affected host.
How can I set up AMP in SecureX?
To integrate AMP for Endpoints with SecureX, you may follow the in product configuration steps or check out our AMP module configuration video on YouTube.
Firepower Devices (NGFW)
What features are enabled by tying Firepower devices into SecureX?
With this integration, investigators can see intrusion and other events from Firepower devices correlated with enrichment from other Cisco Security products, adding greater context and helping the SOC investigate incidents with broader internal visibility.
The Firepower integration also supports Incident Manager, in which investigators can see, manage, and investigate curated high urgency intrusion events in Threat Response. Intrusion events from Firepower are the first data source that populates the Incident Manager (with more coming soon).
What version of the Firepower software is required to support SecureX functions?
At least v6.3 for a syslog integration, although 6.5+ is highly recommended. Direct event forwarding is supported in 6.4+ in the NAM region, and 6.5+ in the EU and APJC regions. As well, the 6.5 upgrade introduced the ability to forward additional even types to be used as enrichment data and potential Incident tracking.
How can I set up my Firepower device in SecureX?
To integrate Firepower with the SecureX threat response and incident manager tools, you may use the start guide for Firepower and further details on the Firepower Integration FAQs.
Can Firepower devices licensed via a Smart Software Satellite Server be integrated with SecureX?
Yes, they can still contribute to SecureX by using the CSSP syslog relay as described in the documentation here.
SMA (Security Management Appliance)
What version of SMA is needed to use it with SecureX?
SMA was SecureX-capable as a module in threat response as of AsyncOS version 12.0. To get SMA tiles in the SecureX dashboard, the SMA needs to be at version 13.6.2 or higher.
Cisco Secure Email (Formerly Cisco Email Security Appliance)
What version of AsyncOS is required to enable the SecureX features?
AsyncOS 13.0 and higher support Threat Response functions; the ability to search the history of observed email in the course of investigations.
AsyncOS 13.5.2 or higher is required to also have Cisco Secure Email tiles in the SecureX doashboard.
Cisco Secure Analytics (Formerly known as Stealthwatch Enterprise or SWE)
What version of SWE is needed to use it with SecureX?
SWE 7.2.1 and higher supports SecureX dashboards and SecureX threat response functions. (integration guide)
SWE 7.1.2 and 7.1.3 will support SecureX threat response functions only. (integration guide)
Stealthwatch Cloud
What capabilities does SWC support in SecureX, and vice versa?
After integration, the SecureX Ribbon is available in the SWC console, bringing threat intelligence and response capabilities from the rest of your combined SecureX stack. Also, SWC contributes tiles into the SecureX dashboard, allowing key metrics from that stack, including SWC, to be viewed in one place at any time.
Where can I get directions how how to integrate SWC with SecureX?
https://www.cisco.com/c/dam/en/us/td/docs/security/stealthwatch/cloud/SecureX/SWC_SecureX_DV_1_0.pdf
Using SecureX with Third Party Products
Browser plugins
What browsers support the SecureX plugin?
Current and recent versions of Chrome, Firefox, and Edge
What does the browser plugin do?
The browser plugin allows you to leverage SecureX ribbon capabilities on and with browser content. For example, you can pivot directly into investigations in SecureX Threat Response with observables automatically extracted from any web page, such as your favorite infosec blog or the web management console of any security or networking product. You can also immediately pivot into any of your connected SecureX-capable Cisco or 3rd party tools, and natively use ribbon apps like Incident Manager and Orbital.
How is the plugin configured?
The configuration process is very straightforward and is described here.
Integration Status
Is there an integration with [insert product]... What is the current list of third party integrations with SecureX?
Our partner ecosystem catalog is available at http://cs.co/CSTA
There is also this blog article: https://blogs.cisco.com/security/securex-threat-response-ecosystem
Relay Modules
What is a Relay Module?
A Relay Module is how SecureX can leverage a third party product for to use it as an information source in investigations and response actions in threat response. It requires a relay, hence the name. The relay translates from Cisco SecureX APIs and data model (CTIM) on one side, and the third party product's API and data model on the other. The existence of this relay greatly accelerates the speed at which third party product integrations can be developed and deployed.
Who hosts the relay?
Relays can be hosted by users, or by the vendors of the integrated products, or in some integrations by SecureX.
Where can I get the relay code?
For supported 3rd party integrations, you do not need to host the code yourself. Cisco hosts the relay on your behalf. To see the code, eg to use it as templates to build your own, you can find them at http://github.com/CiscoSecurity
What are the IPs I need to allow to connect to my relay module?
NAM: 35.168.234.165, 35.172.5.95, 34.225.249.84 EU:34.251.83.242, 52.49.85.99, 52.208.164.206 APJC: 54.248.49.240, 52.198.165.128, 52.196.126.178
SecureX Administration
What are the differences between the "User" and "Admin" account roles?
The capabilities granted to Admin accounts but not Users are:
- Create, Invite, and/or Modify User accounts
- Add and configure Integration Modules
- Enable Orchestration for the organization
- Create new Orchestration Workflows, Atomics, Targets, and similar Orchestration objects
- Edit all Orchestration workflows (individual workflows may be protected from editing by User level accounts)
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
New users are unable to setup secure X . Any issue is going on?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
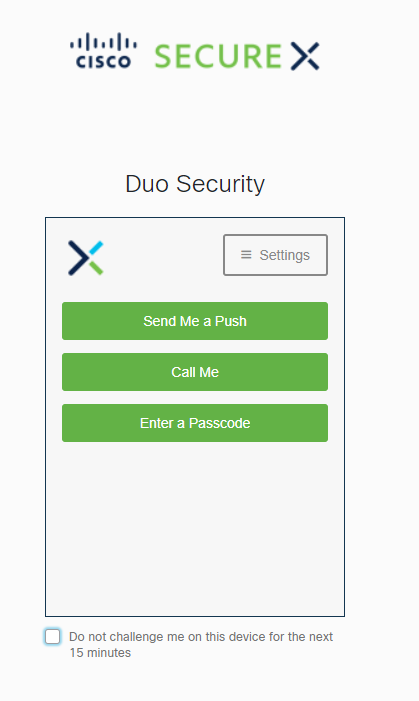
Once you receive the verification email you should be prompted to set up DUO MFA.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
I don't have a DUO backup. how can i login SecureX.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
^ If you got that far, you must have set up DUO on a mobile device. If you click "send me a push", you should get a prompt on that device, which when approved will allow you to enter.
If any of that is not true or does not happen, please contact tech support.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
I have tried all the ways, tried everything shown(push, call) but nothing happens, no calls, no messages, no push. Nothing.
I opened a case with TAC. Hope it will be resolved soon.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Would it be possible to connect to multiple SSE?
I am working as consultant and need to assist multiple customers.
Regards
Thomas
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
^ SSE is a cloud service to which SecureX is already connected; there is no need to connect to "multiple SSE" You can have multiple devices (firewalls, email security appliances, etc) using SSE in one account, definitely.
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: