What should I do if I have ACS 4.x? Can I migrate to ISE 2.x?
You have a two options here.
Option 1:
Install ISE 2.3 that will have a complete set of features that ACS 4.x/5.x offered with some exceptions.
Please see ACS vs ISE Comparison for details.
Installing ISE from scratch is the better option since you can renew your policies that was not looked into for a long time.
ISE 2.3 offers custom user attributes supports newer data type such as Date and IP address. So if you have user defined
attributes in ACS you can easily configure in ISE.
ISE 2.3 also has new Policy UI with hit counts that was a feature brought in from ACS 5.x. ISE 2.3 also support TACACS+ support for IPv6 and for TACACS+ proxy.
Option 2
If Option 1 is not for you, then you have ISE 2.3 migration tool that migrates key configuration from ACS 4.x to ISE 2.3 includes only ( User, Groups, User attributes, Network devices, Network device groups). You can download the migration tool from here and try out.
(Note: This tool has to be installed in the same machine that runs ACS 4.x that has VNC. Requires Java 7)
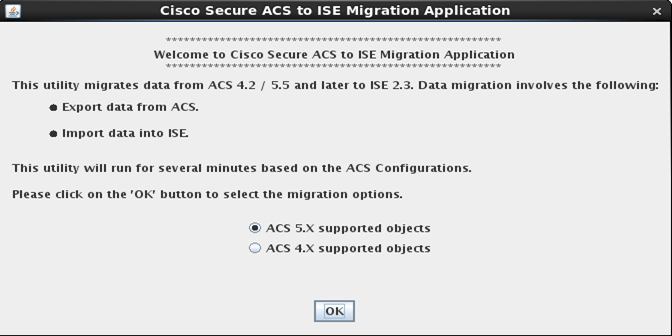
Here is the screenshot of the migration tool that initially asks you to choose the version of ACS you are migrating from
Once you select ACS 4.x supported objects you will be presented with a screen that shows the objects migrated from ACS to ISE.
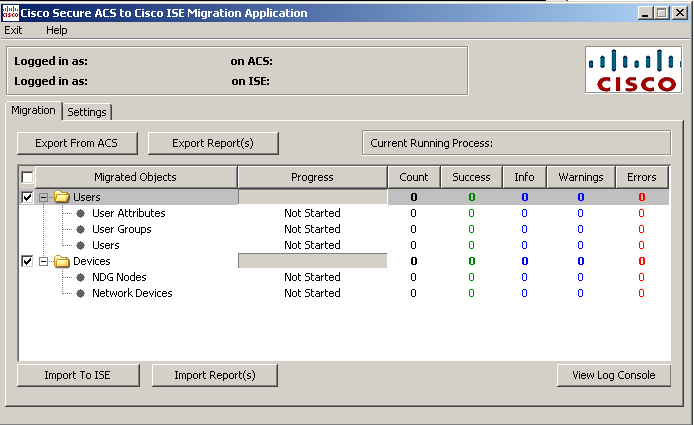
Remember you have to manually configure inline conditions, policy elements, authentication, authorization policies etc. The policy architecture of ISE is simpler than ACS 5.x however other associated objects in the policies are the same such as policy elements( shell profiles, command sets). You can additional details in migration from ACS 4.x to 5.x document.
If you have an older version of ACS, here is my blog that will help you.decide.