Hello All,
This document is intended to explain how to use CBAC to block http websites. The command that we are going to use is called ip urlfilter in conjunction with the Legacy Firewall (CBAC).
Requirements
- An image that Supports CBAC (Normally Advanced security or Adavanced IP services)
- The ip urlfilter command introduced in 12.2.(15)T.
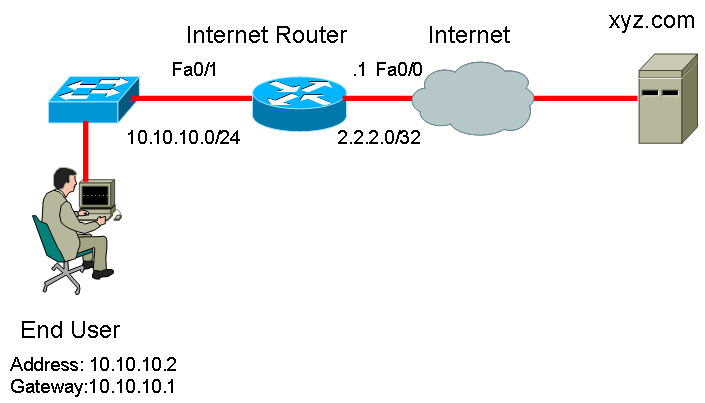
This is the scenario that we are going to use:
Configuration:
- Create the URLfilter policy with the command IP urlfilter
Command structure
ip urlfilter exclusive-domain <permit/deny> <website_name >
Example:
ip urlfilter exclusive-domain deny xyz.com
The exclusive domain will be the name of the website you want to allow/deny.
2. Select what to do with the sites that are not specified:
Command structure
ip urlfilter allow-mode <on/off>
This is a fail open, fail close mechanism, if it is turned on, all the rest of the websites not specified are going to be allowed, if it is set to off, all the websites will be blocked.
3. Create the Firewall policy in order for the Router to inspect the payload and block/allow the website
Command structure
ip inspect name <name> protocol
In order to configure the urlfilter policy, we need to inspect http protocol
Example:
ip inspect name Webfilter http urlfilter
The url filter will call the filter policy that we created.
4. Apply the url filter on the interfae
Command structure
ip inspect <name> <in/out>
This is in order to set the direction on the filter. In case that you want to filter specific users on an specific interface, you will need to apply it closest to the user, if you want to configure it globally, just put it on the outbound direction on the internet facing interface.
Example
Int fa 0/0 (Facing internet interface)
ip inspect Webfilter out
Final configuration
ip urlfilter exclusive-domain deny xyz.com
ip urlfilter allow-mode on
ip inspect name Webfilter http urlfilter
Interface fa0/0
ip inspect Webfilter out
When the customer tries to access website xyz.com the user will get the following page on the web browser: