- Cisco Community
- Technology and Support
- Security
- Security Knowledge Base
- Collection of ISE Auth and Service Flows
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
11-23-2017 04:06 AM - edited 02-21-2020 10:02 PM
I received request on depicting some of the ISE flows and therefore providing a collection that I compiled a while back. Some of the terms and use cases may be a bit dated, but core information still valid and hopefully useful to others.
- IEEE 802.1X -Port-based Access Control with Authentication
- IEEE 802.1X with Change of Authorization (CoA)
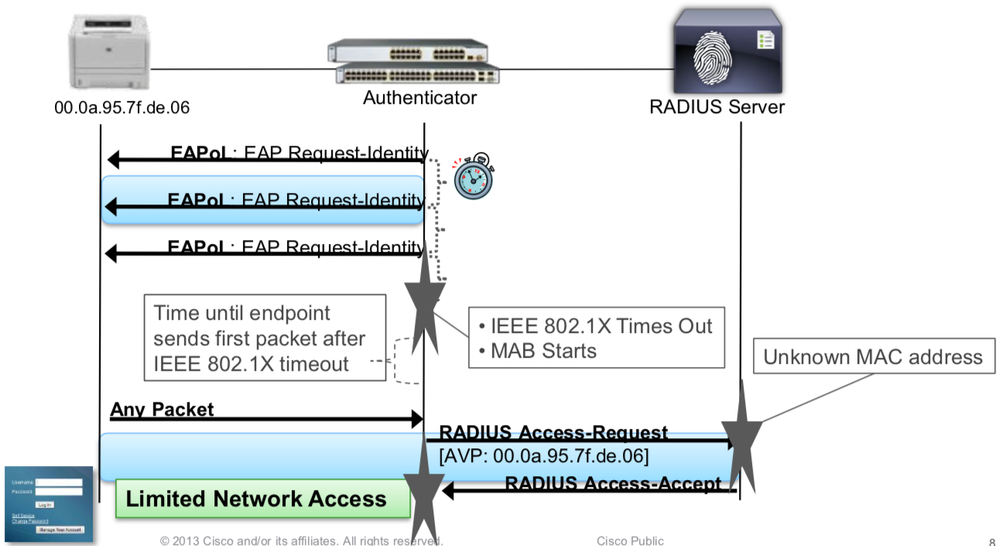
- MAC Authentication Bypass (MAB)
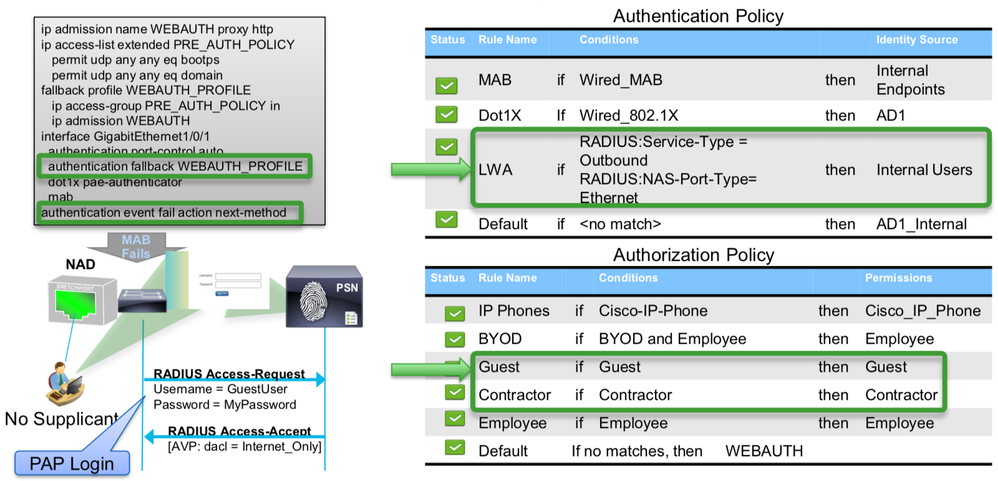
- Local Web Authentication (LWA) Session Flow
- Wireless Local Web Auth (LWA) Configuration
- Wired LWA Config
- Web Authentication
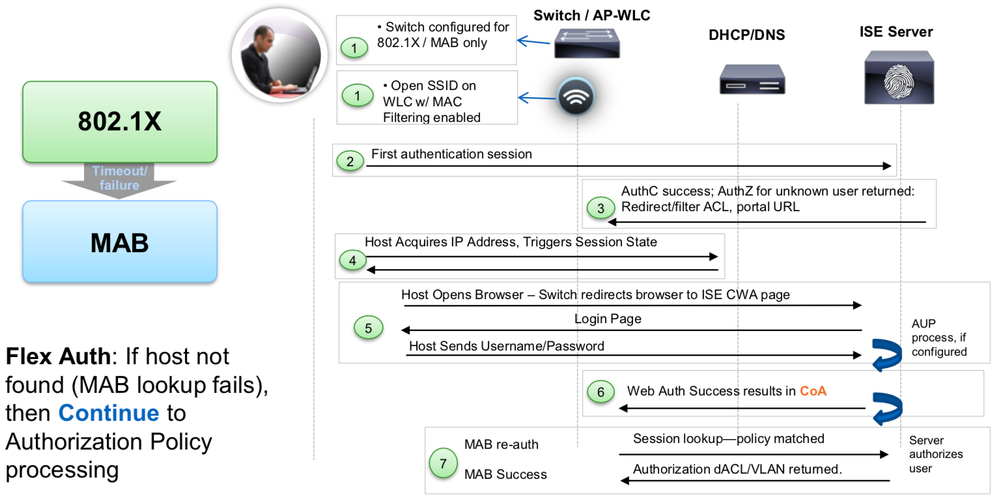
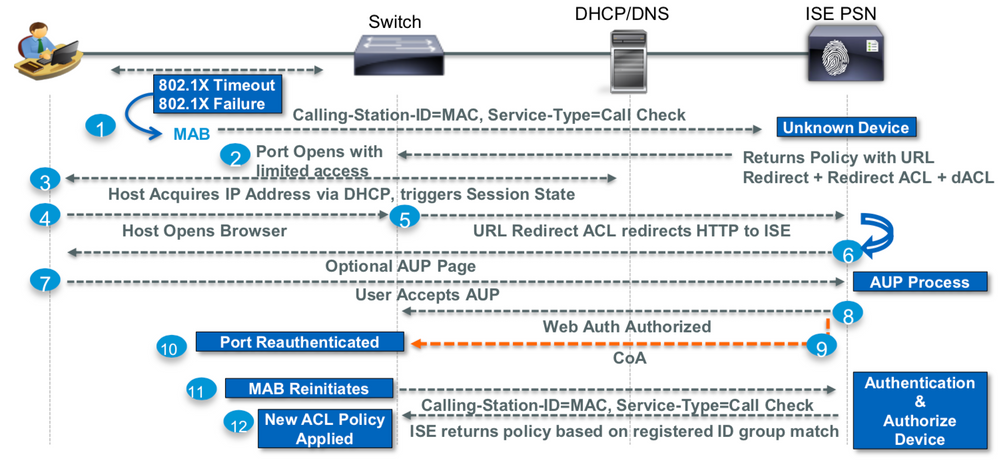
- CWA – Session Flow
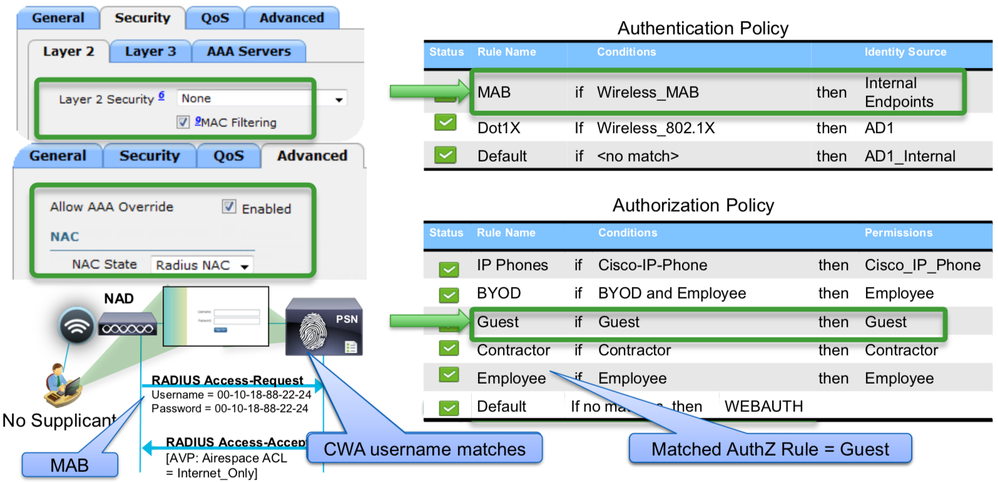
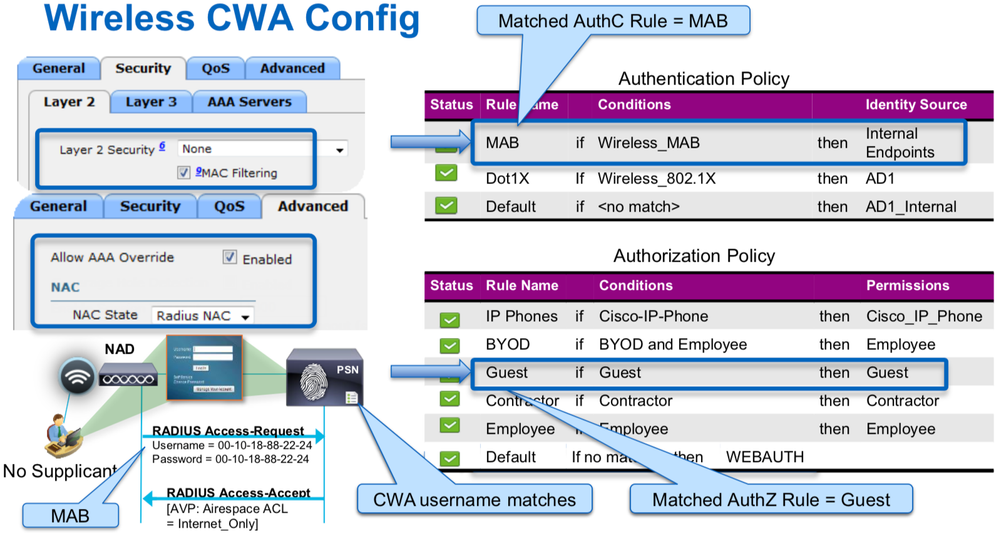
- Wireless CWA Config
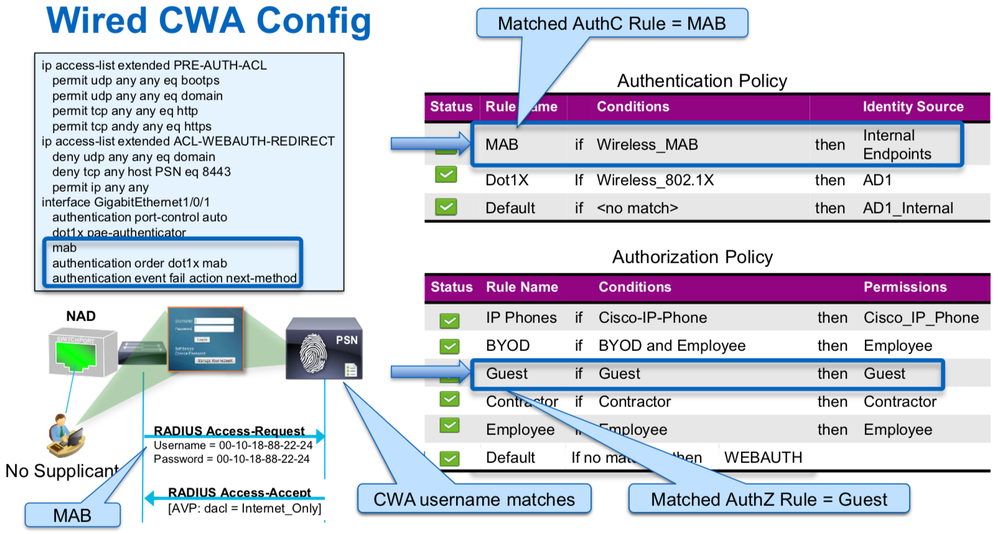
- Wired CWA Config
- Central Web Authentication (CWA) with ISE
- dACL + URL-Redirect for CWA
- Sample ACLs for CWA Redirection
- Wired Device Registration Web Auth (DRW) Flow
- Wired CWA Config
- Wireless CWA Config
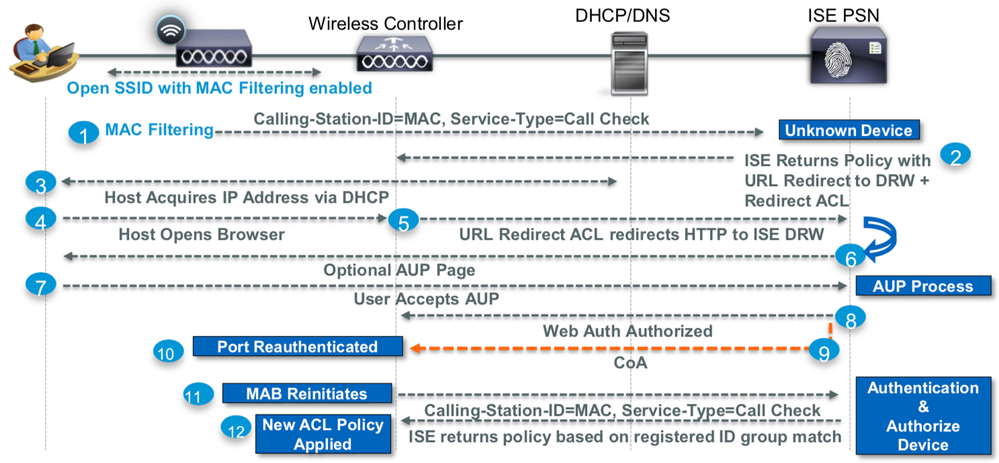
- Wireless DRW Flow
- Example of Profiling Flow with Multiple Probes
- Profiling without Probes
- Probeless Profiling
- 802.1X End User Authentication with Posture
- 802.1X End User Authentication with Posture
- Adding Posture to the Authorization Policy
- BYOD Authorization Policy
- Single SSID – Employee using PEAP
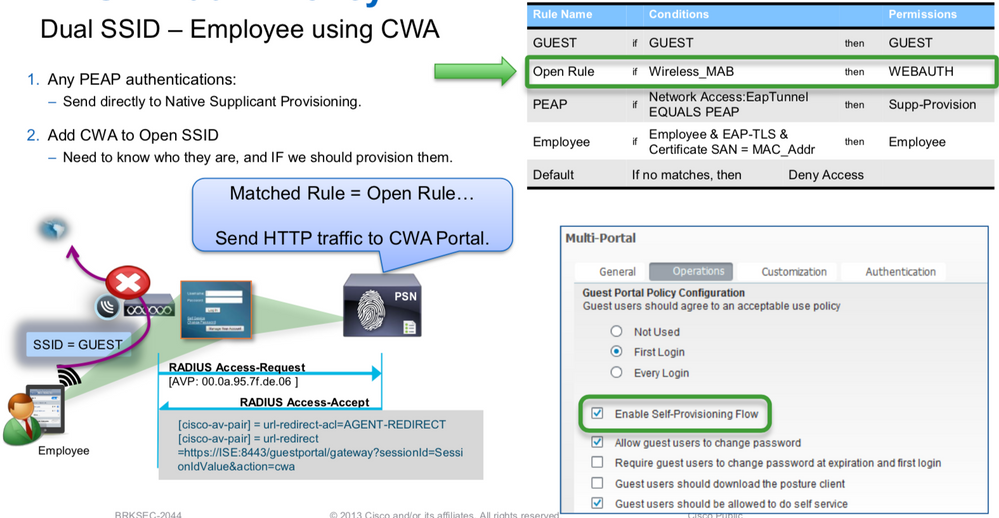
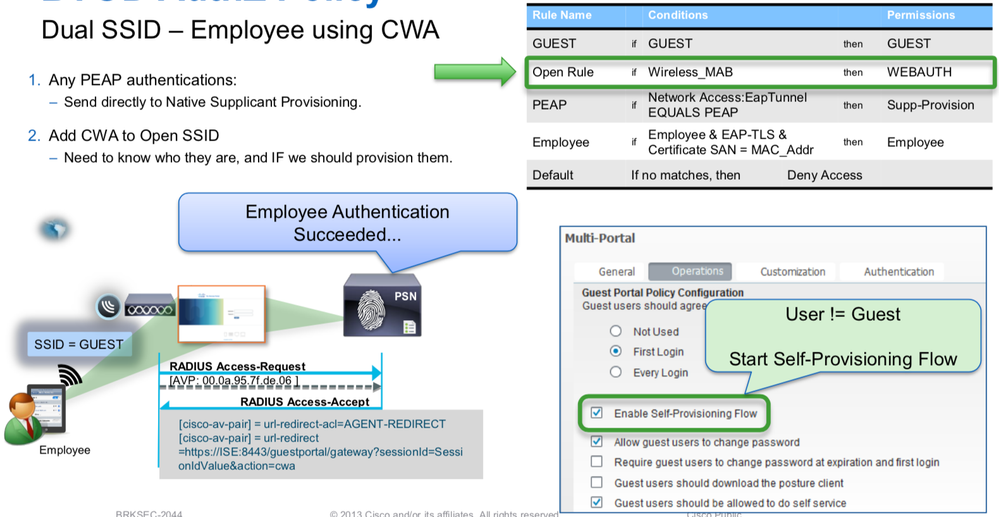
- Dual SSID – Employee using CWA
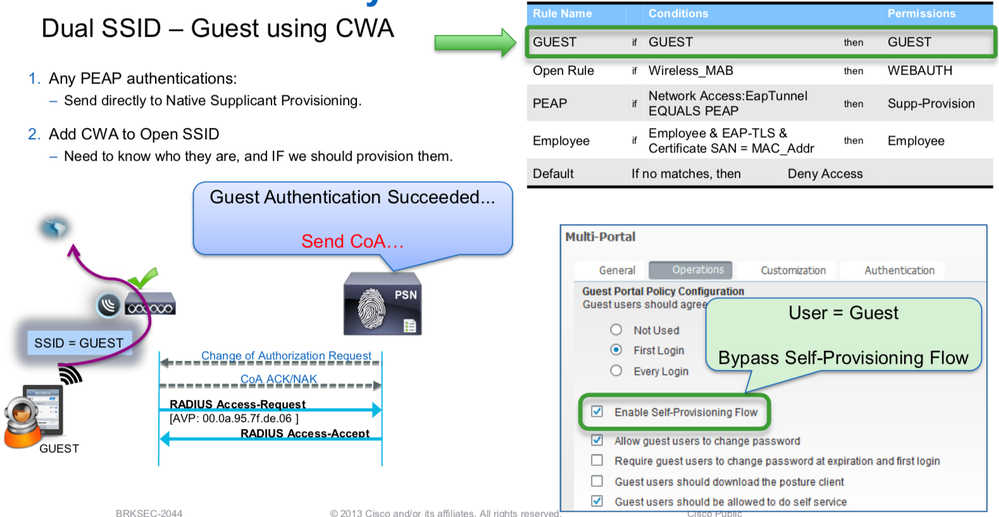
- Dual SSID – Guest using CWA
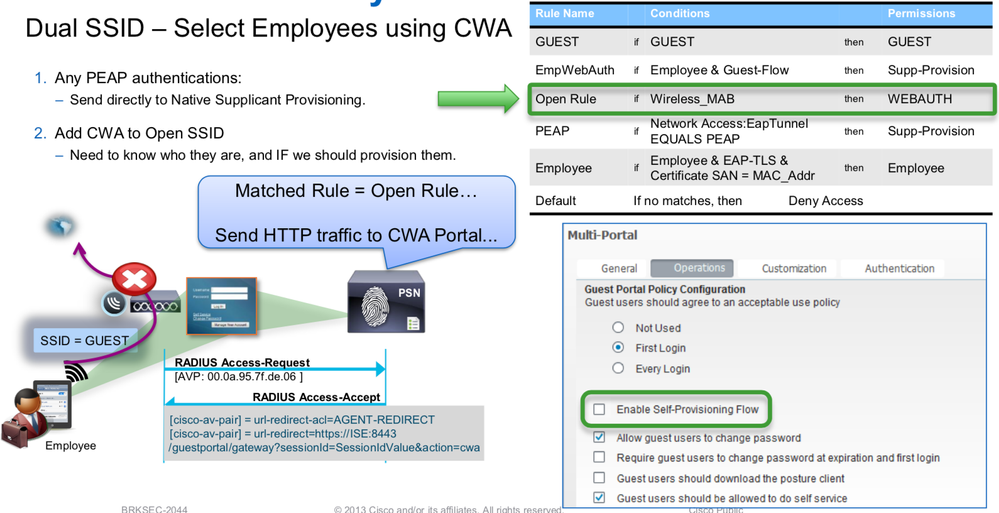
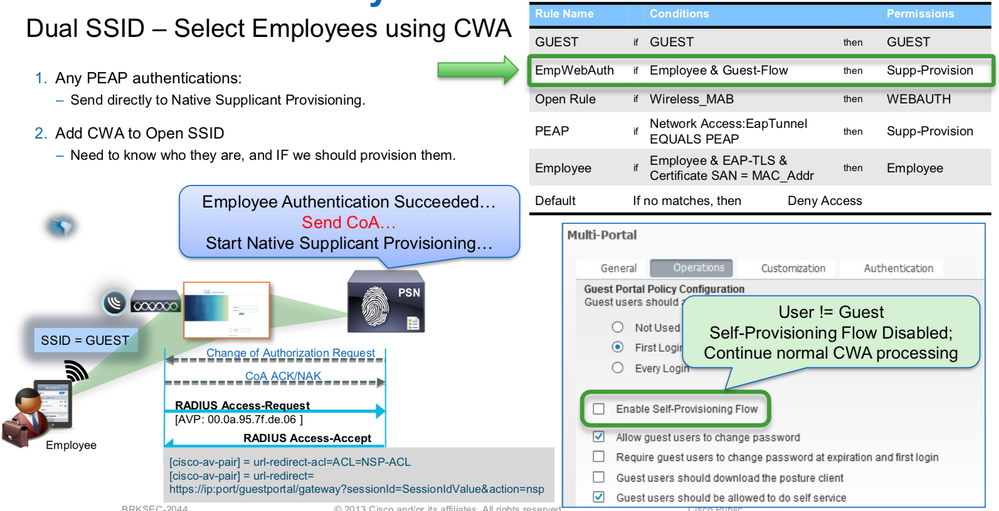
- Dual SSID – Select Employees using CWA
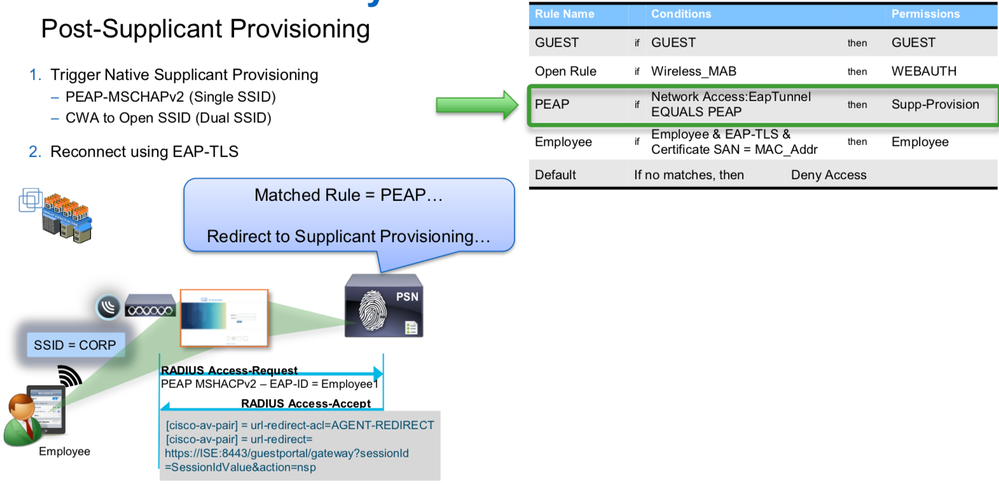
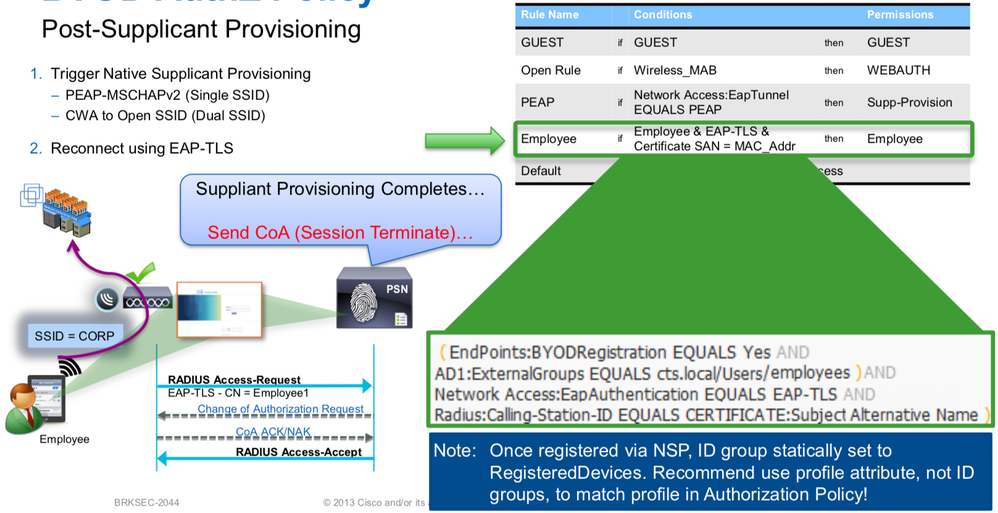
- Post-Supplicant Provisioning
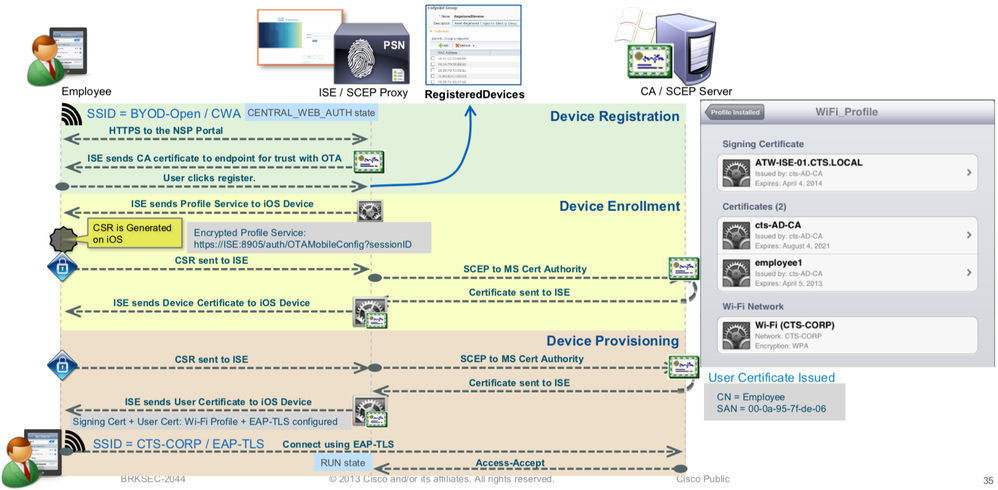
- Native Supplicant Provisioning (iOS Scenario)
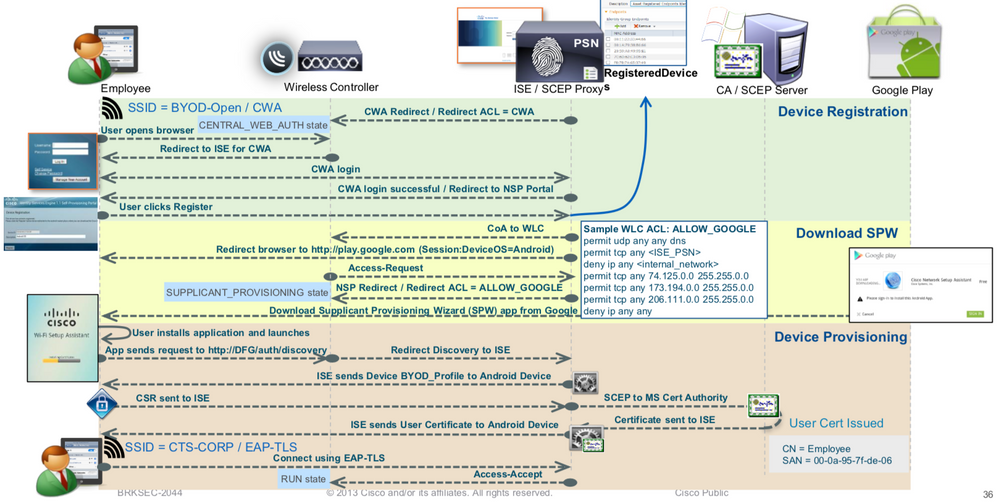
- Native Supplicant Provisioning (Android Scenario)
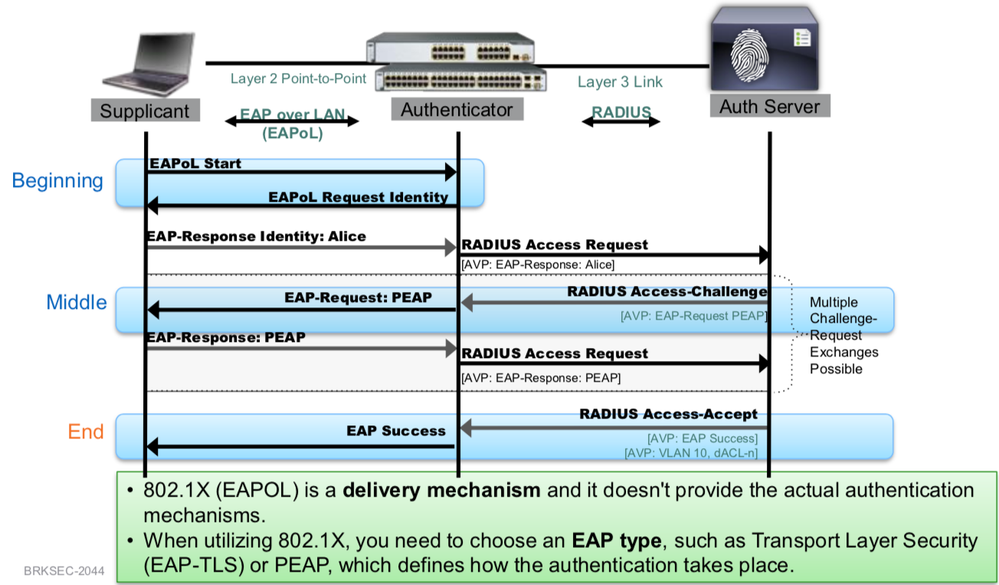
IEEE 802.1X -Port-based Access Control with Authentication
IEEE 802.1X with Change of Authorization (CoA)
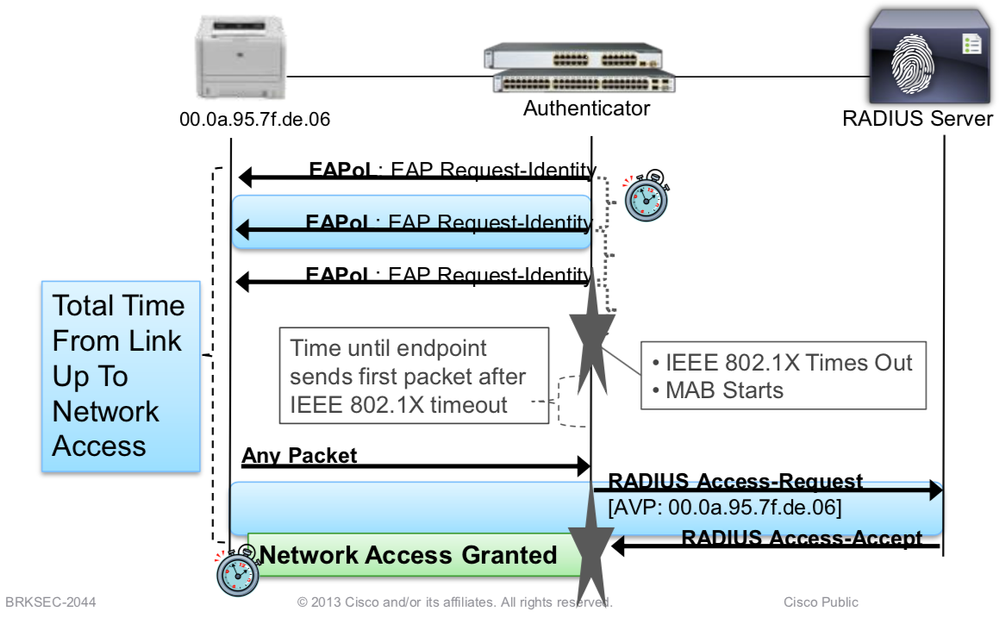
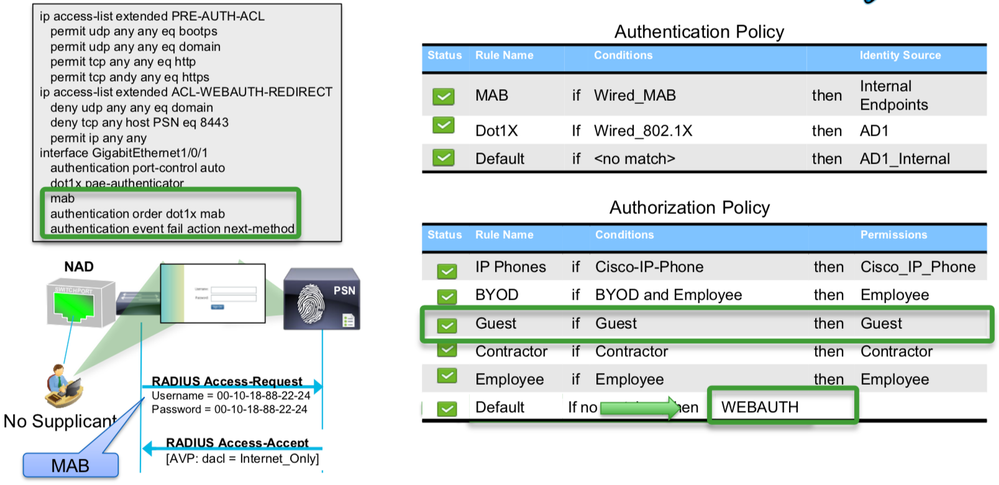
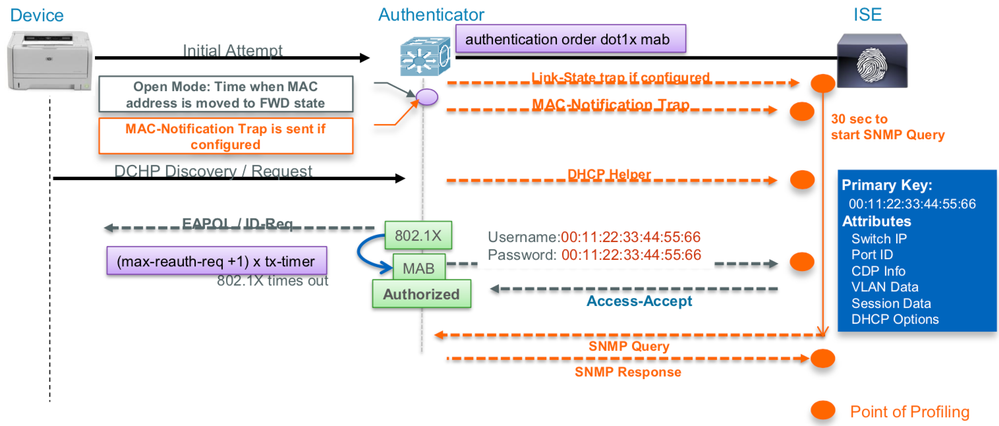
MAC Authentication Bypass (MAB)
Non-802.1X capable devices and no “user intelligence” behind
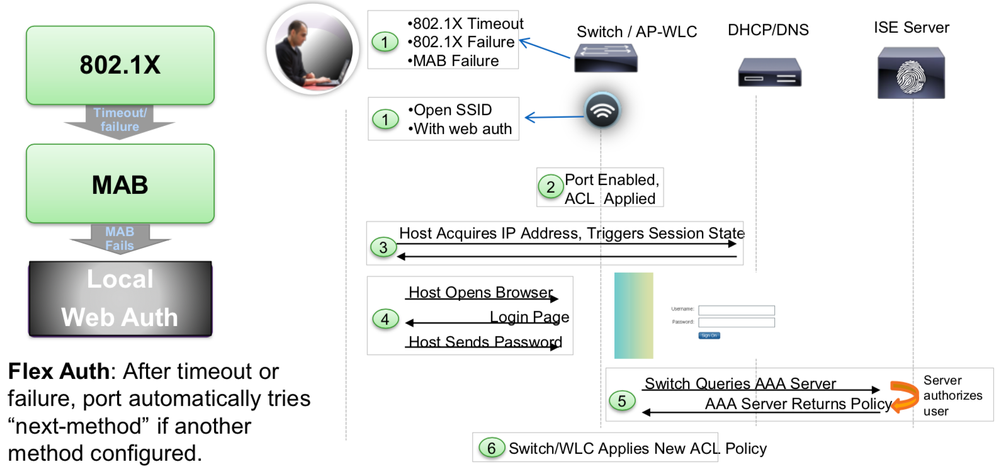
Local Web Authentication (LWA) Session Flow
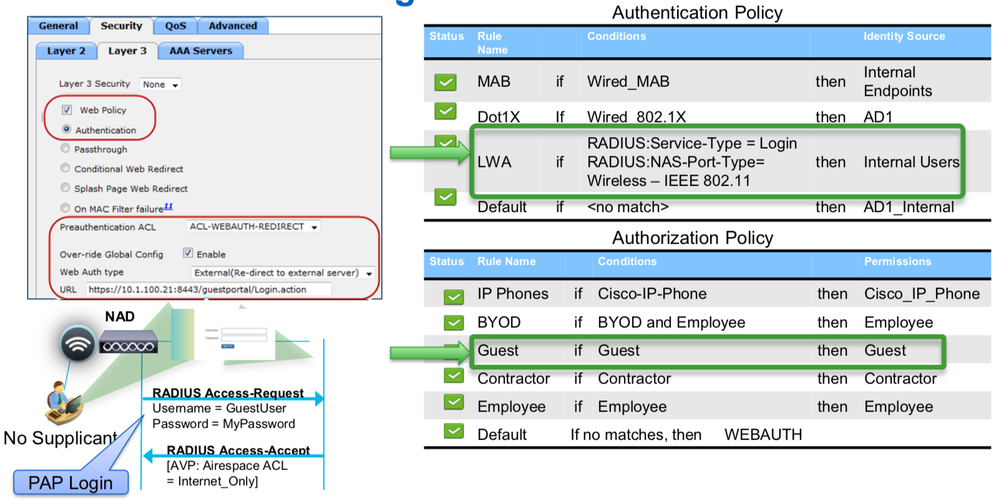
Wireless Local Web Auth (LWA) Configuration
Wired LWA Config
Web Authentication
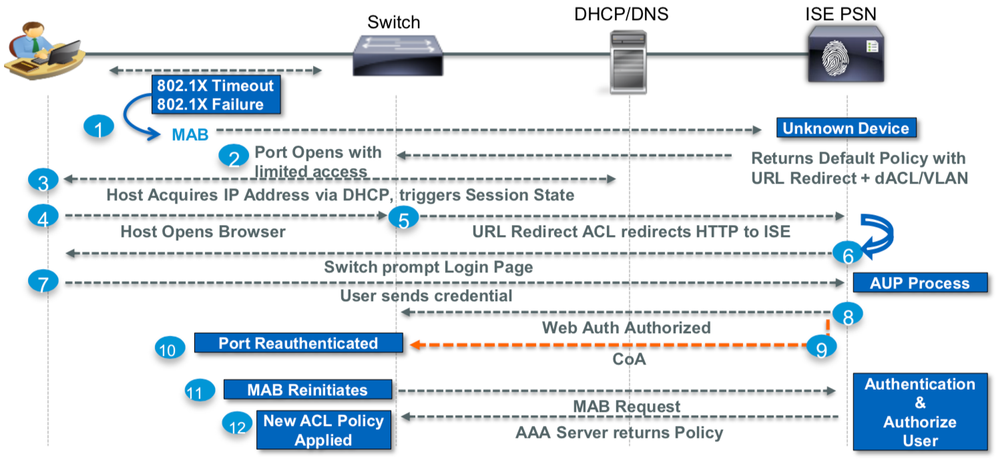
CWA – Session Flow
Wireless CWA Config
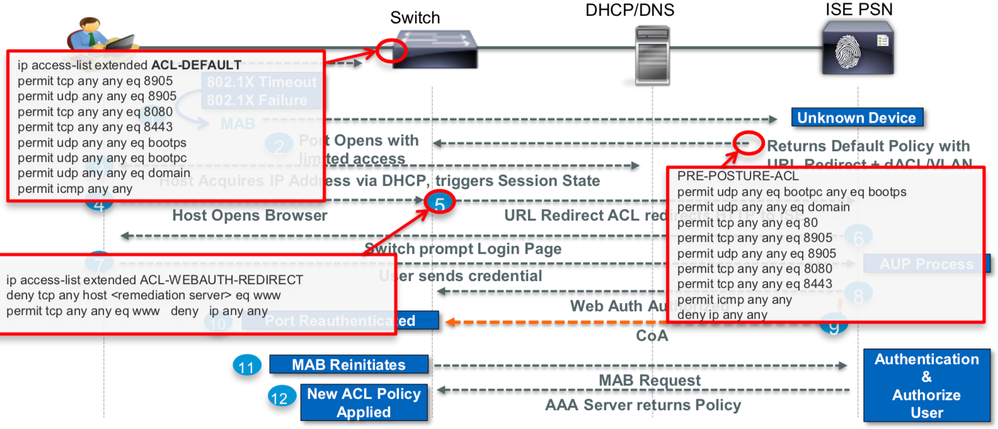
Wired CWA Config
Central Web Authentication (CWA) with ISE
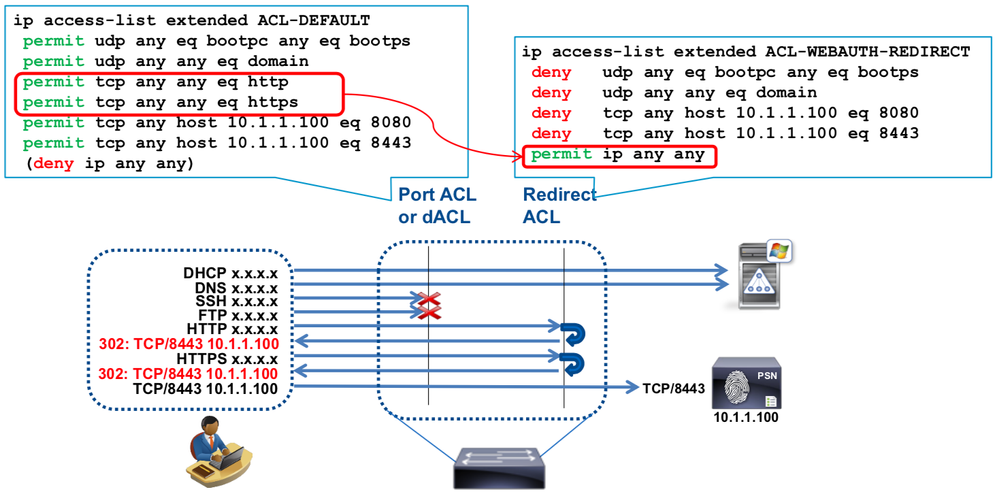
dACL + URL-Redirect for CWA
Sample ACLs for CWA Redirection
Wired Device Registration Web Auth (DRW) Flow
Wired CWA Config
Wireless CWA Config
Wireless DRW Flow
Example of Profiling Flow with Multiple Probes
SNMP Query, SNMP Trap, RADIUS, DHCP Helper
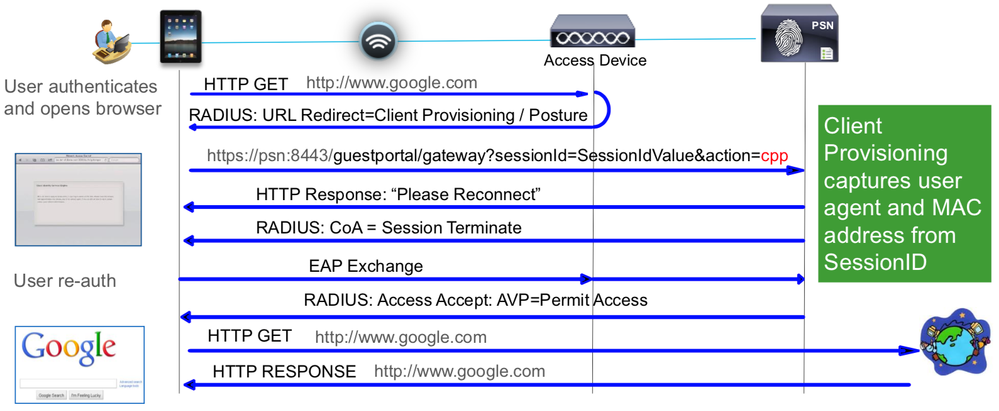
Profiling without Probes
Direct Profiling using Client Provisioning (Posture Agent or NSP)
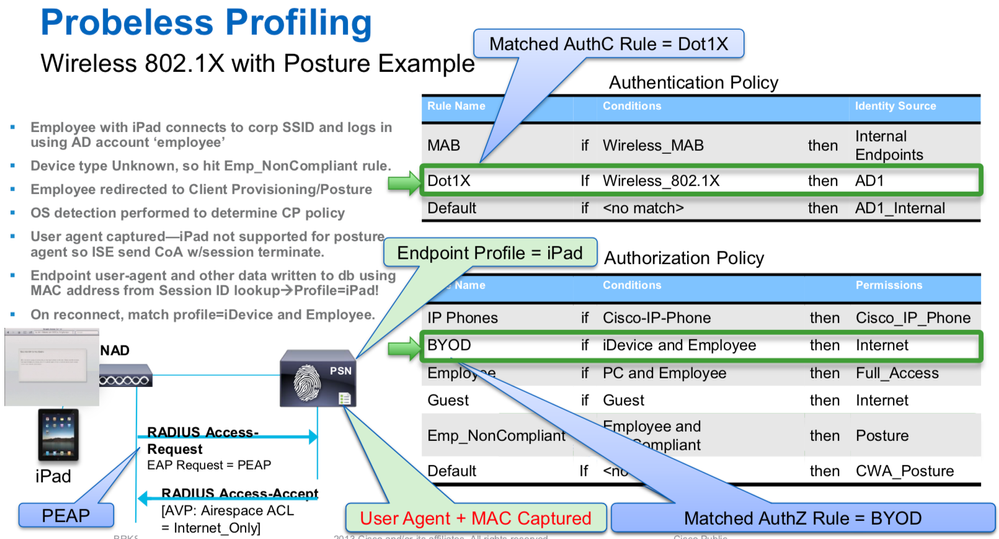
Probeless Profiling
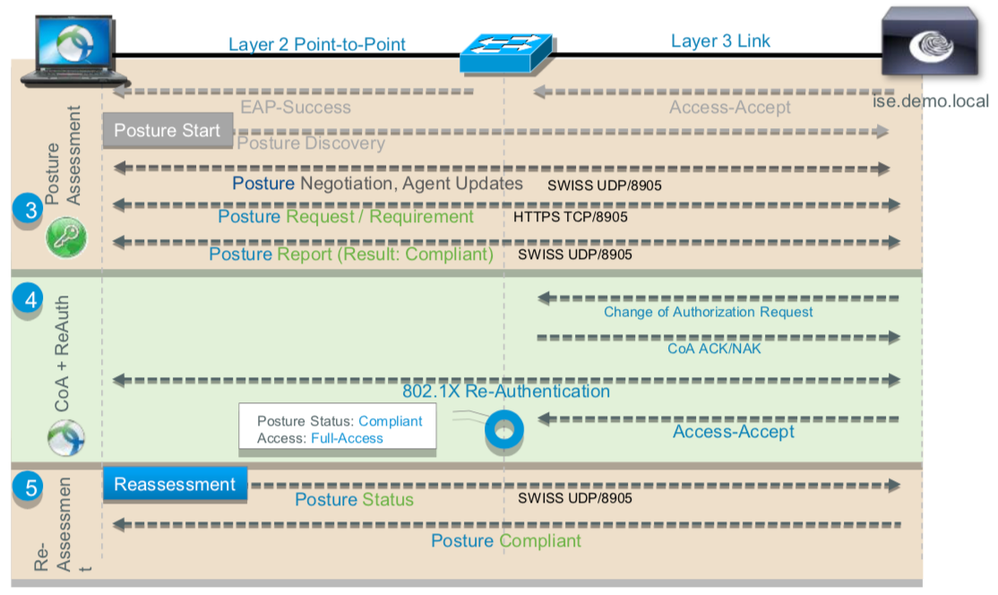
Wireless 802.1X with Posture Example
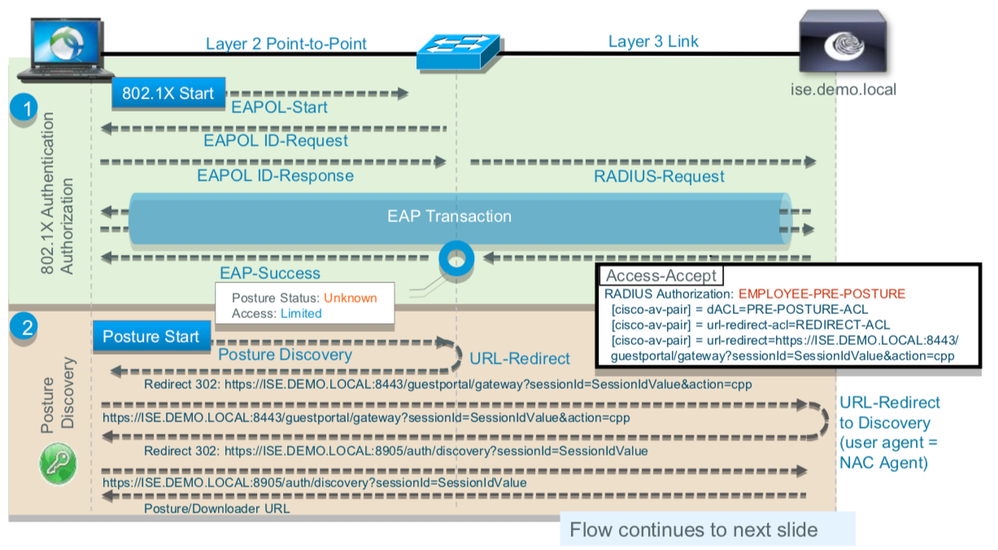
802.1X End User Authentication with Posture
802.1X End User Authentication with Posture
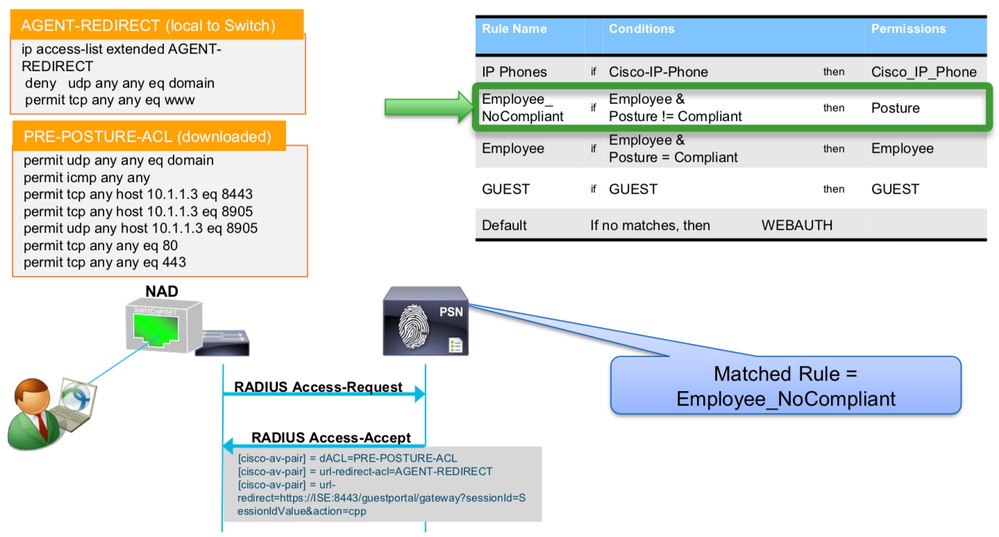
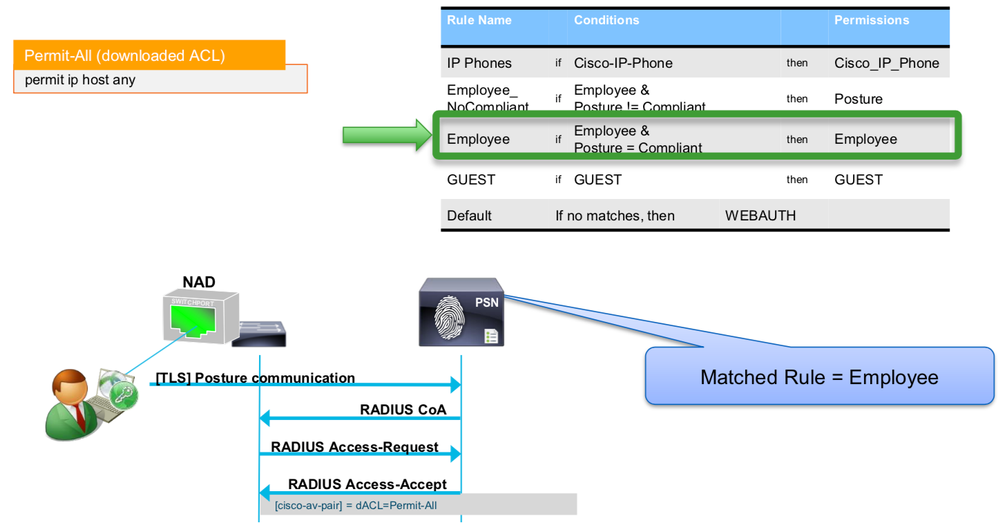
Adding Posture to the Authorization Policy
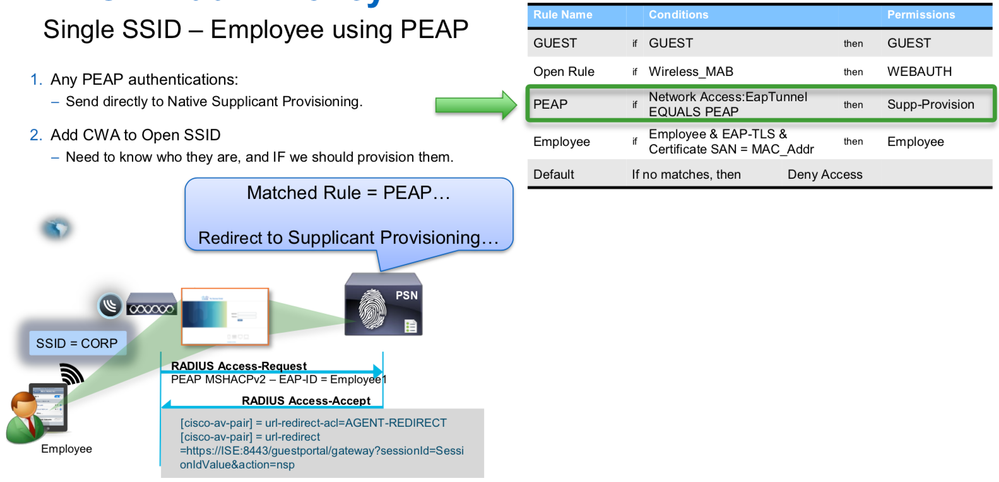
BYOD Authorization Policy
Single SSID – Employee using PEAP
Dual SSID – Employee using CWA
Dual SSID – Guest using CWA
Dual SSID – Select Employees using CWA
Post-Supplicant Provisioning
Native Supplicant Provisioning (iOS Scenario)
Native Supplicant Provisioning (Android Scenario)
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Thanks a lot and it is very helpful
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
WoW great workflows.... thanks...
it's always wonderful to read your articles.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
4 years later and this is still very helpful, thank you
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: