Introduction
This document describes an issue faced by users where "interfaces resets when signatures are disabled".
Problem
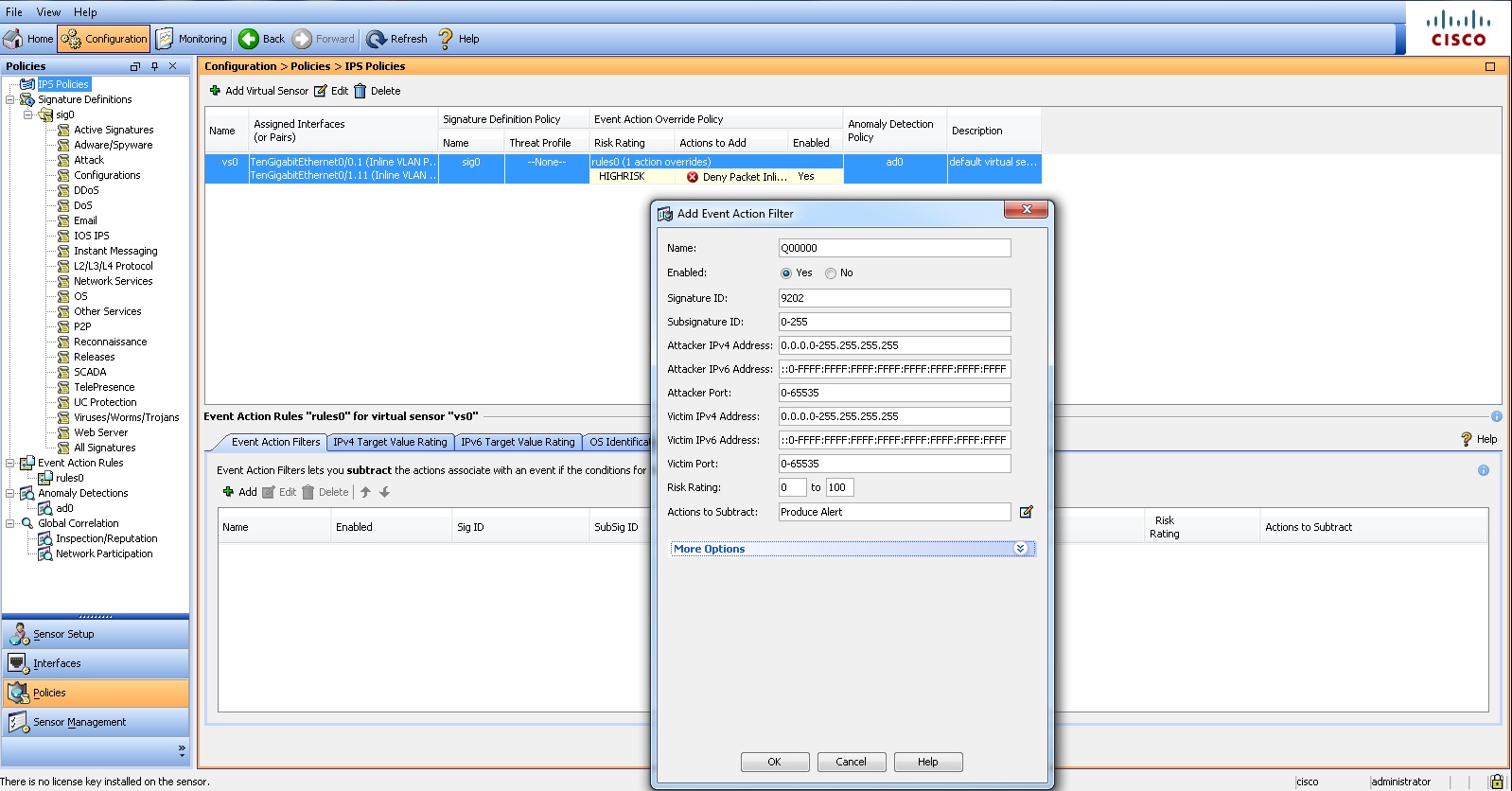
When user ingress the next script in order to disable signature, the interfaces of the Ips cisco 4240 restarts,
Script used by user
config term
service signature-definition sig0
signatures 9202 0
status
enabled false
exit
exit
Log from terminal
Aug 13 23:59:35.229: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet1/0/25, changed state to up
Aug 13 23:59:35.280: %LINEPROTO-5-UPDOWN: Line protocol on Interface GigabitEthernet2/0/26, changed state to up
GigabitEthernet1/0/25 is up, line protocol is up (connected)
Hardware is Gigabit Ethernet, address is e8b7.4843.b099 (bia e8b7.4843.b099)
Description: **** IPS-A ****
GigabitEthernet1/0/26 is up, line protocol is up (connected)
Hardware is Gigabit Ethernet, address is e8b7.4843.b09a (bia e8b7.4843.b09a)
Description: **** IPS-B ***
Solution
The interfaces flap because of the bypass mode off setting. When user is tuning a signature ( enable/disable) , sensor goes into bypass. With bypass-mode off , the interface will go down when the sensor goes intp bypass and remain down unitl sensor is out of bypass. User will not see this behaviour when the bypass-mode is configured as Auto.
Scenario 2
Problem:
User have an ASA5540X firewall with the internal (software based) IPS module. The module has the up-to-date signatures and seems to be running correctly. However, after enabling anomaly detection (ad0), and specifying the internal zones, He don't see any "Learned OS" in IME
His settings are pretty basic for the sensor
access-list ips_traffic extended permit ip any any
access-list ips_traffic extended permit udp any any
class-map ips_class
match access-list ips_traffic
policy-map global_policy
class ips_class
ips inline fail-open
Solution
Learned OS maps—OS maps observed by the sensor through the fingerprinting of TCP packets with the SYN control bit set. Learned OS maps are local to the virtual sensor that sees the traffic.
you can verify the OS finger printing by using command:
sensor# show os-identification learned
Enable passive-traffic-analysis {enabled | disabled}
Source Discussion