Introduction
This document shows issue of "Events not getting generated" faced by a user.
Problem
Pls see below policy config of ASA.
============================
ASA-01# sh run policy-map
!
policy-map global_policy
class inspection_default
inspect ftp
inspect h323 h225
inspect h323 ras
inspect netbios
inspect rsh
inspect rtsp
inspect sqlnet
inspect sunrpc
inspect tftp
inspect sip
inspect xdmcp
inspect ip-options
inspect skinny
inspect icmp
class class-default
flow-export event-type all destination 10.xx.xx.xx
!
ASA-01# sh run class-map
!
class-map inspection_default
match default-inspection-traffic
.
Scenario 2
User trying to determine is it possible to create custom IPS signatures on the ASA-CX module? Not the ASA + Legacy IPS combo, but the ASA + ASA-CX (Application Detection, Web Filtering, IPS) combo. He couldn't find anything in the docs that said this was possible.
Solution
To the best of my knowledge, expired license does not stop the IPS from producing event actions.
On IDM or IME, go to Monitor -> Events click the "warning", "error", "fatal" and the "show status events" if not already checked. set "show pat even to at least 1hr. and click "view" at the bottom, You should see some events how ever these may not be created by any signature.
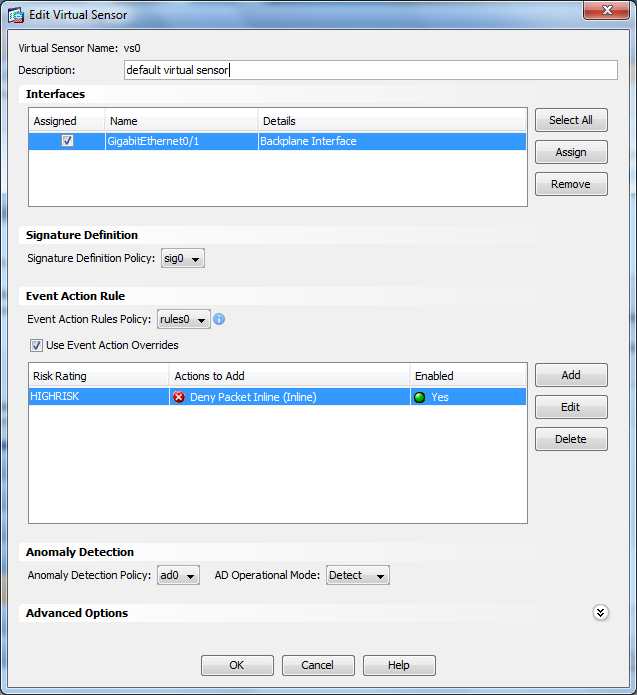
Click "configuration" ->Interfaces -> summary and see if any interface is assigned to a VS. If "none", then there lies the issue.
To fix this, goto
Configuration->IPS Policy, select the VS and click edit.
If the interface is not selected, click the check box to select the interface and click apply.
From above mentioned configuration there is no configuration on ASA that passes traffic to the IPS for inspection in your show run class-map and show run policy-map out put.
In global config mode type the following command below:
Access-list IPS_acl extended permit ip any any
class-map IPS_class
match access-list IPS_acl
policy-map IPS_policy
class IPS_class
ips promiscuous fail-open
service-policy IPS_policy global
Scenario 2
Not with the current release. Currently, Cisco ASA Next-Generation Firewall Services include a robust set of more than 1200 applications and 150000 micro-applications. The ability for administrators to create their own application signatures is a feature that will be included in a future release. No, those capabilities are not available with the NGFW IPS. Cisco currently recommends that the classic IPS (ASA module of stand-alone appliance) for customers requiring that capability. Expect this all to change significantly over the coming year though as more of the SourceFire technology is integrated into the ASA product line.
Source Discussion
IPS-SSM10-Events