[toc:faq]
Introduction
This document explains the way of Securing Terminal Line.
Prerequisites
Router running Security Feature set.
Description:
One biggest security risk on Cisco-based network is the VTY lines of routers and switches. These lines are used for remote access (via telnet, by default) and are suseptible to brute force password attacks. Below mentioned are few simple steps you can follow to ensure your security at VTV lines.
1.) Enabling username / password based authentication: There are many solutions for authentication ranging from the incredibly complicated to the exceptionally simple. Here you can see the easiest way to enable username / password authentication.
First, you will enable username / password authentication. For this example, we'll use the local user database and only create one user, tiger.
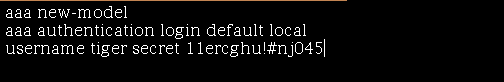
The first line turns on the new authentication model. The second line sets the default authentication mechanism to the "local" database — that's the list of users you are going to be entering by hand. The final line adds a user called 'tiger' with password '11ercghu!#nj045'. The password is hashed inside the configuration.
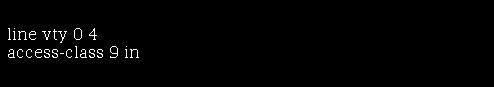
2.) Restricting VTY line access with an access-list: Once you've defined a list of management addresses, you should apply the list to your VTY lines in order to prevent requests from unwanted IP addresses for connection.
Brute force password attacks attempts happen on network devices all day every day. All it takes is one weak password for your device to be compromised. If we lock out all machines that should not be attempting to access the system, we've done a great deal to prevent maliciousness.
We'll use an access-list to define a block of IPs that should be allowed to access our Cisco router (or IOS-based Catalyst switch) and then apply it to our virtual terminal (VTY) lines.

We are using a standard access-list rather than an extended access-list because we are not concerned with matching sources and destinations. We have allowed the first 16 consecutive IPs from 172.16.9.0 through 172.16.9.15. By way of example, we'll assume these are the IP addresses of the hosts used by our network administrators. A single host at 172.16.9.99 is also permitted to access the system. A monitoring server, perhaps. Finally, we deny access by all other hosts.
3.) Use SSH-enabled version of IOS: telnet traffic is sent clear text or unencrypted and represents a major security risk on the network. Even if your devices are behind a firewall, you are still exposing your telnet and enable passwords to your internal network. Using telnet should be avoided.
Once we've installed an SSH-enabled version of IOS, the SSH server will start automatically once you generate the encryption keys with the command mentioned below:
crypto key generate rsa
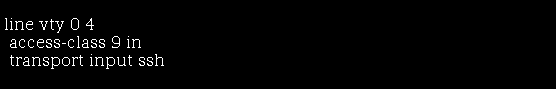
You need to apply the access-list to the VTY lines and force users to use SSH as shown below: