- Cisco Community
- Technology and Support
- Security
- Network Security
- How to disable ssh server version name and number?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-26-2018 12:38 PM - edited 02-21-2020 07:33 AM
Hello,
I am performing a switch hardening process. One of our clients has an issue with Cisco 6500 switch.
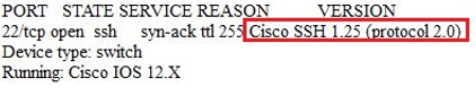
While performing a Nmap scan on our network. We get the following information as a result.
I would like to know this possible I can hide or remove or disable the Version information from the switch i.e Cisco SSH 1.25(protocol 2.0).
Thanks
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-28-2018 02:14 AM - edited 03-28-2018 02:14 AM
My suggestion was hypothetical. The IOS code is propriety, you would not be able to compile and re-bundle it.
You will have to live with the fact that IOS will leak information about the versions of some of its services. The best you can do is to run the latest IOS version which mitigates the current set of vulnerabilities which may affect those services.
cheers,
Seb.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2018 03:29 AM - edited 03-27-2018 03:33 AM
Hi there,
This information is given up as part of normal ssh client operation. Run your SSH client with the verbose flag and you will see the information which is exchanged before authentication takes place:
srupik@debian:~$ ssh -l srupik -v x.x.x.x OpenSSH_7.4p1 Debian-10+deb9u3, OpenSSL 1.0.2l 25 May 2017 debug1: Reading configuration data /etc/ssh/ssh_config ... debug1: Local version string SSH-2.0-OpenSSH_7.4p1 Debian-10+deb9u3 debug1: Remote protocol version 2.0, remote software version Cisco-1.25 debug1: match: Cisco-1.25 pat Cisco-1.* compat 0x60000000 ... password:
...in short, you cannot stop this information from being revealed... unless perhaps you re-compiled the ssh client binaries which are running in the IOS firmware...!
You mat also like to read:
https://nmap.org/book/vscan.html
cheers,
Seb.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-27-2018 05:31 AM
Thank you so much for the response. I have some question regarding your suggestion.
How can I re-compiled the ssh client binaries of IOS firmware.?
Could you please provide any guides for that? Or any CISCO custom binaries are available for the issue.
Please share it.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-28-2018 02:14 AM - edited 03-28-2018 02:14 AM
My suggestion was hypothetical. The IOS code is propriety, you would not be able to compile and re-bundle it.
You will have to live with the fact that IOS will leak information about the versions of some of its services. The best you can do is to run the latest IOS version which mitigates the current set of vulnerabilities which may affect those services.
cheers,
Seb.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide