- Cisco Community
- Technology and Support
- Small Business Support Community
- Routers - Small Business
- RV345P - L2TP VPN with Windows 10 20H2
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
RV345P - L2TP VPN with Windows 10 20H2
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-06-2021 04:48 PM - edited 01-06-2021 05:18 PM
Hallo together,
i'm trying for days to set up an L2TP VPN on my RV345P in combination with the integrated Windows 10 Client.
I found those two topics about issues with it:
https://community.cisco.com/t5/small-business-routers/how-to-connect-to-rv340-on-windows-via-vpn/td-p/4105119
https://community.cisco.com/t5/small-business-support-documents/pptp-vpn-configuration-on-rv340-345-routers/ta-p/3220097
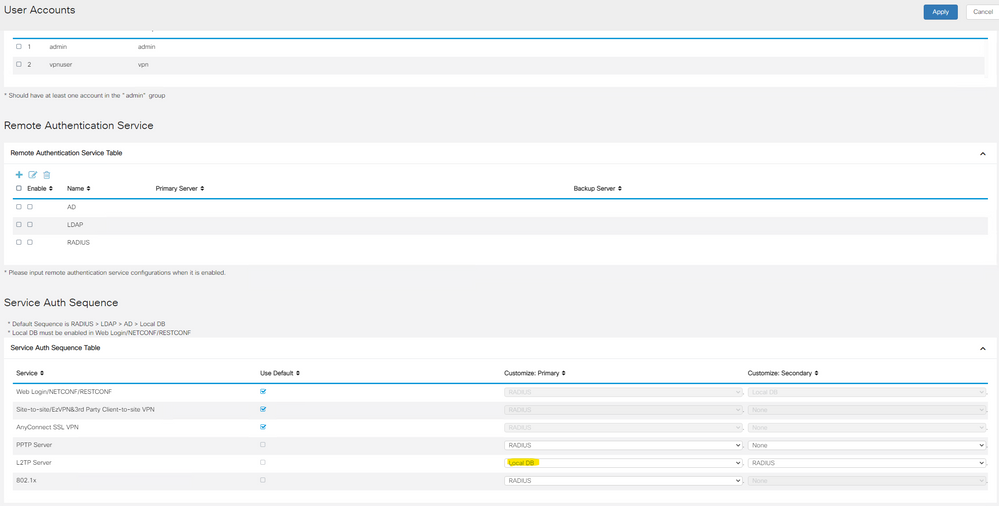
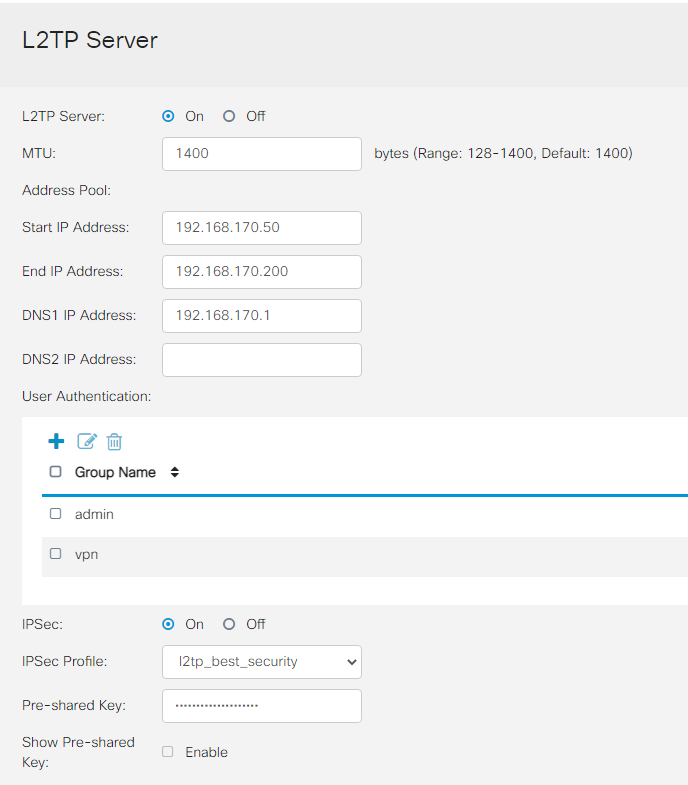
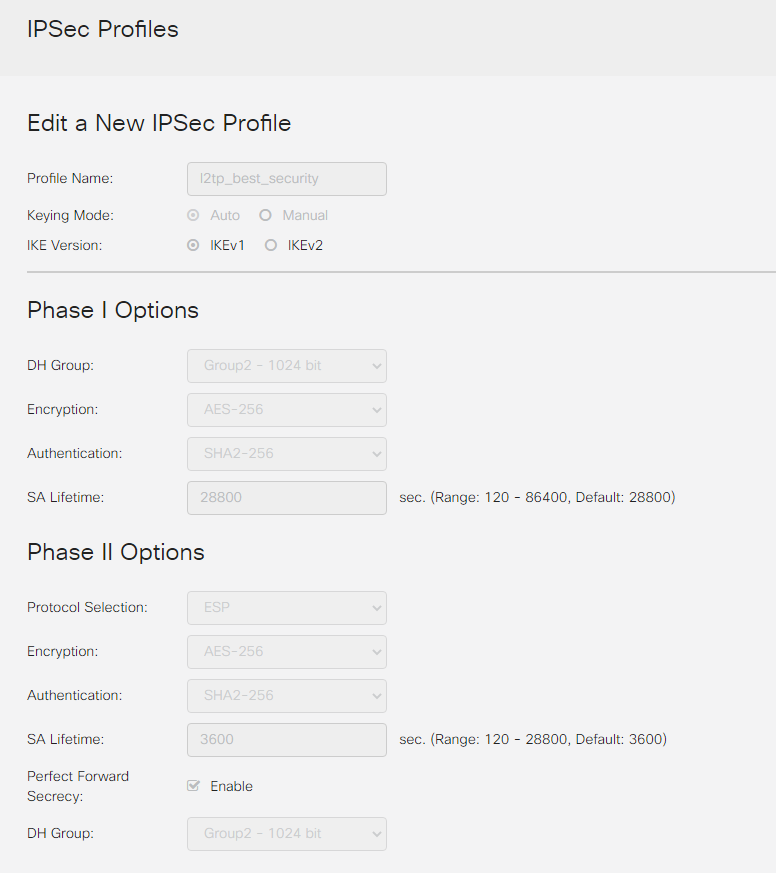
My settings are below, the user is the router admin account + the pre shared key.
The "error" is just some generic Windows message telling me that the connection could not be established. (The RV345P is currently configured as exposed host behind antoher router). I added the router logs of an connection attempt below.
2021-01-07T01:45:20+01:00 <info>charon: 14[IKE] IKE_SA (unnamed)[10] state change: CREATED => DESTROYING 2021-01-07T01:45:20+01:00 <info>charon: 14[NET] sending packet: from 192.168.178.85[500] to 88.152.XXX.YYY[63642] (40 bytes) 2021-01-07T01:45:20+01:00 <info>charon: 14[ENC] generating INFORMATIONAL_V1 request 1078446550 [ N(NO_PROP) ] 2021-01-07T01:45:20+01:00 <info>charon: 14[IKE] no IKE config found for 192.168.178.85...88.152.XXX.YYY, sending NO_PROPOSAL_CHOSEN 2021-01-07T01:45:20+01:00 <info>charon: 14[ENC] parsed ID_PROT request 0 [ SA V V V V V V V V ] 2021-01-07T01:45:20+01:00 <info>charon: 14[NET] received packet: from 88.152.XXX.YYY[63642] to 192.168.178.85[500] (408 bytes) 2021-01-07T01:45:17+01:00 <info>charon: 09[IKE] IKE_SA (unnamed)[9] state change: CREATED => DESTROYING 2021-01-07T01:45:17+01:00 <info>charon: 09[NET] sending packet: from 192.168.178.85[500] to 88.152.XXX.YYY[63642] (40 bytes) 2021-01-07T01:45:17+01:00 <info>charon: 09[ENC] generating INFORMATIONAL_V1 request 1602892568 [ N(NO_PROP) ] 2021-01-07T01:45:17+01:00 <info>charon: 09[IKE] no IKE config found for 192.168.178.85...88.152.XXX.YYY, sending NO_PROPOSAL_CHOSEN 2021-01-07T01:45:17+01:00 <info>charon: 09[ENC] parsed ID_PROT request 0 [ SA V V V V V V V V ] 2021-01-07T01:45:17+01:00 <info>charon: 09[NET] received packet: from 88.152.XXX.YYY[63642] to 192.168.178.85[500] (408 bytes) 2021-01-07T01:45:16+01:00 <info>charon: 13[IKE] IKE_SA (unnamed)[8] state change: CREATED => DESTROYING 2021-01-07T01:45:16+01:00 <info>charon: 13[NET] sending packet: from 192.168.178.85[500] to 88.152.XXX.YYY[63642] (40 bytes) 2021-01-07T01:45:16+01:00 <info>charon: 13[ENC] generating INFORMATIONAL_V1 request 730976270 [ N(NO_PROP) ] 2021-01-07T01:45:16+01:00 <info>charon: 13[IKE] no IKE config found for 192.168.178.85...88.152.XXX.YYY, sending NO_PROPOSAL_CHOSEN 2021-01-07T01:45:16+01:00 <info>charon: 13[ENC] parsed ID_PROT request 0 [ SA V V V V V V V V ] 2021-01-07T01:45:16+01:00 <info>charon: 13[NET] received packet: from 88.152.XXX.YYY[63642] to 192.168.178.85[500] (408 bytes) 2021-01-07T01:45:15+01:00 <info>charon: 05[IKE] IKE_SA (unnamed)[7] state change: CREATED => DESTROYING 2021-01-07T01:45:15+01:00 <info>charon: 05[NET] sending packet: from 192.168.178.85[500] to 88.152.XXX.YYY[63642] (40 bytes) 2021-01-07T01:45:15+01:00 <info>charon: 05[ENC] generating INFORMATIONAL_V1 request 2783688284 [ N(NO_PROP) ] 2021-01-07T01:45:15+01:00 <info>charon: 05[IKE] no IKE config found for 192.168.178.85...88.152.XXX.YYY, sending NO_PROPOSAL_CHOSEN 2021-01-07T01:45:15+01:00 <info>charon: 05[ENC] parsed ID_PROT request 0 [ SA V V V V V V V V ] 2021-01-07T01:45:15+01:00 <info>charon: 05[NET] received packet: from 88.152.XXX.YYY[63642] to 192.168.178.85[500] (408 bytes)
Is there anyone here who could help me getting this to work?
Edit i tried this settings https://community.cisco.com/t5/small-business-routers/rv345p-pptp-and-l2tp-clients-can-t-authenticate-to-local-db/m-p/3988588?attachment-id=196554#M38468:
2021-01-07T02:05:11+01:00 <info>charon: 06[IKE] closing CHILD_SA l2tp_l2tpOverIpsec_wan1{69} with SPIs cce45351_i (0 bytes) 68dd39d6_o (0 bytes) and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:05:11+01:00 <info>charon: 06[IKE] received DELETE for ESP CHILD_SA with SPI 68dd39d6
2021-01-07T02:05:11+01:00 <info>charon: 06[ENC] parsed INFORMATIONAL_V1 request 4199028481 [ HASH D ]
2021-01-07T02:05:11+01:00 <info>charon: 06[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (76 bytes)
2021-01-07T02:05:11+01:00 <info>charon: Last message '12[IKE] CHILD_SA l2t' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:05:11+01:00 <info>charon: 12[IKE] CHILD_SA l2tp_l2tpOverIpsec_wan1{70} established with SPIs c7abaca1_i 1efe867c_o and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:05:11+01:00 <info>charon: 12[CHD] SPI 0x1efe867c, src 192.168.178.85 dst 88.152.XXX.YYY
2021-01-07T02:05:11+01:00 <info>charon: 12[CHD] adding outbound ESP SA
2021-01-07T02:05:11+01:00 <info>charon: 12[CHD] SPI 0xc7abaca1, src 88.152.XXX.YYY dst 192.168.178.85
2021-01-07T02:05:11+01:00 <info>charon: 12[CHD] adding inbound ESP SA
2021-01-07T02:05:11+01:00 <info>charon: 12[CHD] using HMAC_SHA1_96 for integrity
2021-01-07T02:05:11+01:00 <info>charon: 12[CHD] using 3DES_CBC for encryption
2021-01-07T02:05:11+01:00 <info>charon: 12[ENC] parsed QUICK_MODE request 6 [ HASH ]
2021-01-07T02:05:11+01:00 <info>charon: 12[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (60 bytes)
2021-01-07T02:05:11+01:00 <info>charon: 07[NET] sending packet: from 192.168.178.85[4500] to 88.152.XXX.YYY[63646] (204 bytes)
2021-01-07T02:05:11+01:00 <info>charon: 07[ENC] generating QUICK_MODE response 6 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:05:11+01:00 <info>charon: 07[IKE] detected rekeying of CHILD_SA l2tp_l2tpOverIpsec_wan1{69}
2021-01-07T02:05:11+01:00 <info>charon: 07[IKE] received 250000000 lifebytes, configured 0
2021-01-07T02:05:11+01:00 <info>charon: 07[IKE] changing received traffic selectors 192.168.178.61/32[udp/l2f]=== 87.189.224.132/32[udp/l2f] due to NAT
2021-01-07T02:05:11+01:00 <info>charon: 07[ENC] parsed QUICK_MODE request 6 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:05:11+01:00 <info>charon: 07[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (276 bytes)
2021-01-07T02:05:11+01:00 <info>charon: Last message '09[IKE] closing CHIL' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:05:01+01:00 <info>charon: 09[IKE] closing CHILD_SA l2tp_l2tpOverIpsec_wan1{68} with SPIs c5dbf978_i (0 bytes) 8047451a_o (0 bytes) and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:05:01+01:00 <info>charon: 09[IKE] received DELETE for ESP CHILD_SA with SPI 8047451a
2021-01-07T02:05:01+01:00 <info>charon: 09[ENC] parsed INFORMATIONAL_V1 request 2144897911 [ HASH D ]
2021-01-07T02:05:01+01:00 <info>charon: 09[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (76 bytes)
2021-01-07T02:05:01+01:00 <info>charon: Last message '11[IKE] CHILD_SA l2t' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:05:01+01:00 <info>charon: 11[IKE] CHILD_SA l2tp_l2tpOverIpsec_wan1{69} established with SPIs cce45351_i 68dd39d6_o and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:05:01+01:00 <info>charon: 11[CHD] SPI 0x68dd39d6, src 192.168.178.85 dst 88.152.XXX.YYY
2021-01-07T02:05:01+01:00 <info>charon: 11[CHD] adding outbound ESP SA
2021-01-07T02:05:01+01:00 <info>charon: 11[CHD] SPI 0xcce45351, src 88.152.XXX.YYY dst 192.168.178.85
2021-01-07T02:05:01+01:00 <info>charon: 11[CHD] adding inbound ESP SA
2021-01-07T02:05:01+01:00 <info>charon: 11[CHD] using HMAC_SHA1_96 for integrity
2021-01-07T02:05:01+01:00 <info>charon: 11[CHD] using 3DES_CBC for encryption
2021-01-07T02:05:01+01:00 <info>charon: 11[ENC] parsed QUICK_MODE request 5 [ HASH ]
2021-01-07T02:05:01+01:00 <info>charon: 11[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (60 bytes)
2021-01-07T02:05:01+01:00 <info>charon: 15[NET] sending packet: from 192.168.178.85[4500] to 88.152.XXX.YYY[63646] (204 bytes)
2021-01-07T02:05:01+01:00 <info>charon: 15[ENC] generating QUICK_MODE response 5 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:05:01+01:00 <info>charon: 15[IKE] detected rekeying of CHILD_SA l2tp_l2tpOverIpsec_wan1{68}
2021-01-07T02:05:01+01:00 <info>charon: 15[IKE] received 250000000 lifebytes, configured 0
2021-01-07T02:05:01+01:00 <info>charon: 15[IKE] changing received traffic selectors 192.168.178.61/32[udp/l2f]=== 87.189.224.132/32[udp/l2f] due to NAT
2021-01-07T02:05:01+01:00 <info>charon: 15[ENC] parsed QUICK_MODE request 5 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:05:01+01:00 <info>charon: 15[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (276 bytes)
2021-01-07T02:05:01+01:00 <info>charon: Last message '10[IKE] closing CHIL' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:04:53+01:00 <info>charon: 10[IKE] closing CHILD_SA l2tp_l2tpOverIpsec_wan1{67} with SPIs cd63d69a_i (0 bytes) 4886ace0_o (0 bytes) and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:04:53+01:00 <info>charon: 10[IKE] received DELETE for ESP CHILD_SA with SPI 4886ace0
2021-01-07T02:04:53+01:00 <info>charon: 10[ENC] parsed INFORMATIONAL_V1 request 3450320100 [ HASH D ]
2021-01-07T02:04:53+01:00 <info>charon: 10[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (76 bytes)
2021-01-07T02:04:53+01:00 <info>charon: Last message '05[IKE] CHILD_SA l2t' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:04:53+01:00 <info>charon: 05[IKE] CHILD_SA l2tp_l2tpOverIpsec_wan1{68} established with SPIs c5dbf978_i 8047451a_o and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:04:53+01:00 <info>charon: 05[CHD] SPI 0x8047451a, src 192.168.178.85 dst 88.152.XXX.YYY
2021-01-07T02:04:53+01:00 <info>charon: 05[CHD] adding outbound ESP SA
2021-01-07T02:04:53+01:00 <info>charon: 05[CHD] SPI 0xc5dbf978, src 88.152.XXX.YYY dst 192.168.178.85
2021-01-07T02:04:53+01:00 <info>charon: 05[CHD] adding inbound ESP SA
2021-01-07T02:04:53+01:00 <info>charon: 05[CHD] using HMAC_SHA1_96 for integrity
2021-01-07T02:04:53+01:00 <info>charon: 05[CHD] using 3DES_CBC for encryption
2021-01-07T02:04:53+01:00 <info>charon: 05[ENC] parsed QUICK_MODE request 4 [ HASH ]
2021-01-07T02:04:53+01:00 <info>charon: 05[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (60 bytes)
2021-01-07T02:04:53+01:00 <info>charon: 16[NET] sending packet: from 192.168.178.85[4500] to 88.152.XXX.YYY[63646] (204 bytes)
2021-01-07T02:04:53+01:00 <info>charon: 16[ENC] generating QUICK_MODE response 4 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:04:53+01:00 <info>charon: 16[IKE] detected rekeying of CHILD_SA l2tp_l2tpOverIpsec_wan1{67}
2021-01-07T02:04:53+01:00 <info>charon: 16[IKE] received 250000000 lifebytes, configured 0
2021-01-07T02:04:53+01:00 <info>charon: 16[IKE] changing received traffic selectors 192.168.178.61/32[udp/l2f]=== 87.189.224.132/32[udp/l2f] due to NAT
2021-01-07T02:04:53+01:00 <info>charon: 16[ENC] parsed QUICK_MODE request 4 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:04:53+01:00 <info>charon: 16[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (276 bytes)
2021-01-07T02:04:53+01:00 <info>charon: Last message '14[IKE] closing CHIL' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:04:49+01:00 <info>charon: 14[IKE] closing CHILD_SA l2tp_l2tpOverIpsec_wan1{66} with SPIs c62e0b56_i (0 bytes) 1c283d02_o (0 bytes) and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:04:49+01:00 <info>charon: 14[IKE] received DELETE for ESP CHILD_SA with SPI 1c283d02
2021-01-07T02:04:49+01:00 <info>charon: 14[ENC] parsed INFORMATIONAL_V1 request 573402360 [ HASH D ]
2021-01-07T02:04:49+01:00 <info>charon: 14[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (76 bytes)
2021-01-07T02:04:49+01:00 <info>charon: Last message '08[IKE] CHILD_SA l2t' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:04:49+01:00 <info>charon: 08[IKE] CHILD_SA l2tp_l2tpOverIpsec_wan1{67} established with SPIs cd63d69a_i 4886ace0_o and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:04:49+01:00 <info>charon: 08[CHD] SPI 0x4886ace0, src 192.168.178.85 dst 88.152.XXX.YYY
2021-01-07T02:04:49+01:00 <info>charon: 08[CHD] adding outbound ESP SA
2021-01-07T02:04:49+01:00 <info>charon: 08[CHD] SPI 0xcd63d69a, src 88.152.XXX.YYY dst 192.168.178.85
2021-01-07T02:04:49+01:00 <info>charon: 08[CHD] adding inbound ESP SA
2021-01-07T02:04:49+01:00 <info>charon: 08[CHD] using HMAC_SHA1_96 for integrity
2021-01-07T02:04:49+01:00 <info>charon: 08[CHD] using 3DES_CBC for encryption
2021-01-07T02:04:49+01:00 <info>charon: 08[ENC] parsed QUICK_MODE request 3 [ HASH ]
2021-01-07T02:04:49+01:00 <info>charon: 08[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (60 bytes)
2021-01-07T02:04:49+01:00 <info>charon: 09[NET] sending packet: from 192.168.178.85[4500] to 88.152.XXX.YYY[63646] (204 bytes)
2021-01-07T02:04:49+01:00 <info>charon: 09[ENC] generating QUICK_MODE response 3 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:04:49+01:00 <info>charon: 09[IKE] detected rekeying of CHILD_SA l2tp_l2tpOverIpsec_wan1{66}
2021-01-07T02:04:49+01:00 <info>charon: 09[IKE] received 250000000 lifebytes, configured 0
2021-01-07T02:04:49+01:00 <info>charon: 09[IKE] changing received traffic selectors 192.168.178.61/32[udp/l2f]=== 87.189.224.132/32[udp/l2f] due to NAT
2021-01-07T02:04:49+01:00 <info>charon: 09[ENC] parsed QUICK_MODE request 3 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:04:49+01:00 <info>charon: 09[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (276 bytes)
2021-01-07T02:04:49+01:00 <info>charon: Last message '11[IKE] closing CHIL' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:04:46+01:00 <info>charon: 11[IKE] closing CHILD_SA l2tp_l2tpOverIpsec_wan1{65} with SPIs cbab1efd_i (0 bytes) 0c233a14_o (0 bytes) and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:04:46+01:00 <info>charon: 11[IKE] received DELETE for ESP CHILD_SA with SPI 0c233a14
2021-01-07T02:04:46+01:00 <info>charon: 11[ENC] parsed INFORMATIONAL_V1 request 1707320758 [ HASH D ]
2021-01-07T02:04:46+01:00 <info>charon: 11[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (76 bytes)
2021-01-07T02:04:46+01:00 <info>charon: Last message '15[IKE] CHILD_SA l2t' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:04:46+01:00 <info>charon: 15[IKE] CHILD_SA l2tp_l2tpOverIpsec_wan1{66} established with SPIs c62e0b56_i 1c283d02_o and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:04:46+01:00 <info>charon: 15[CHD] SPI 0x1c283d02, src 192.168.178.85 dst 88.152.XXX.YYY
2021-01-07T02:04:46+01:00 <info>charon: 15[CHD] adding outbound ESP SA
2021-01-07T02:04:46+01:00 <info>charon: 15[CHD] SPI 0xc62e0b56, src 88.152.XXX.YYY dst 192.168.178.85
2021-01-07T02:04:46+01:00 <info>charon: 15[CHD] adding inbound ESP SA
2021-01-07T02:04:46+01:00 <info>charon: 15[CHD] using HMAC_SHA1_96 for integrity
2021-01-07T02:04:46+01:00 <info>charon: 15[CHD] using 3DES_CBC for encryption
2021-01-07T02:04:46+01:00 <info>charon: 15[ENC] parsed QUICK_MODE request 2 [ HASH ]
2021-01-07T02:04:46+01:00 <info>charon: 15[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (60 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 13[NET] sending packet: from 192.168.178.85[4500] to 88.152.XXX.YYY[63646] (204 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 13[ENC] generating QUICK_MODE response 2 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:04:46+01:00 <info>charon: 13[IKE] detected rekeying of CHILD_SA l2tp_l2tpOverIpsec_wan1{65}
2021-01-07T02:04:46+01:00 <info>charon: 13[IKE] received 250000000 lifebytes, configured 0
2021-01-07T02:04:46+01:00 <info>charon: 13[IKE] changing received traffic selectors 192.168.178.61/32[udp/l2f]=== 87.189.224.132/32[udp/l2f] due to NAT
2021-01-07T02:04:46+01:00 <info>charon: 13[ENC] parsed QUICK_MODE request 2 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:04:46+01:00 <info>charon: 13[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (276 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 10[CHD] updown: uci: Entry not found
2021-01-07T02:04:46+01:00 <info>charon: Last message '10[IKE] CHILD_SA l2t' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:04:46+01:00 <info>charon: 10[IKE] CHILD_SA l2tp_l2tpOverIpsec_wan1{65} established with SPIs cbab1efd_i 0c233a14_o and TS 192.168.178.85/32[udp/l2f] === 88.152.XXX.YYY/32[udp/l2f]
2021-01-07T02:04:46+01:00 <info>charon: 10[CHD] SPI 0x0c233a14, src 192.168.178.85 dst 88.152.XXX.YYY
2021-01-07T02:04:46+01:00 <info>charon: 10[CHD] adding outbound ESP SA
2021-01-07T02:04:46+01:00 <info>charon: 10[CHD] SPI 0xcbab1efd, src 88.152.XXX.YYY dst 192.168.178.85
2021-01-07T02:04:46+01:00 <info>charon: 10[CHD] adding inbound ESP SA
2021-01-07T02:04:46+01:00 <info>charon: 10[CHD] using HMAC_SHA1_96 for integrity
2021-01-07T02:04:46+01:00 <info>charon: 10[CHD] using 3DES_CBC for encryption
2021-01-07T02:04:46+01:00 <info>charon: 10[ENC] parsed QUICK_MODE request 1 [ HASH ]
2021-01-07T02:04:46+01:00 <info>charon: 10[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (60 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 16[NET] sending packet: from 192.168.178.85[4500] to 88.152.XXX.YYY[63646] (204 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 16[ENC] generating QUICK_MODE response 1 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:04:46+01:00 <info>charon: 16[IKE] received 250000000 lifebytes, configured 0
2021-01-07T02:04:46+01:00 <info>charon: 16[IKE] changing received traffic selectors 192.168.178.61/32[udp/l2f]=== 87.189.224.132/32[udp/l2f] due to NAT
2021-01-07T02:04:46+01:00 <info>charon: 16[ENC] parsed QUICK_MODE request 1 [ HASH SA No ID ID NAT-OA NAT-OA ]
2021-01-07T02:04:46+01:00 <info>charon: 16[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (276 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 12[NET] sending packet: from 192.168.178.85[4500] to 88.152.XXX.YYY[63646] (68 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 12[ENC] generating ID_PROT response 0 [ ID HASH ]
2021-01-07T02:04:46+01:00 <info>charon: 12[IKE] DPD not supported by peer, disabled
2021-01-07T02:04:46+01:00 <info>charon: 12[IKE] maximum IKE_SA lifetime 28712s
2021-01-07T02:04:46+01:00 <info>charon: 12[IKE] scheduling reauthentication in 28532s
2021-01-07T02:04:46+01:00 <info>charon: 12[IKE] IKE_SA l2tp_l2tpOverIpsec_wan1[16] state change: CONNECTING => ESTABLISHED
2021-01-07T02:04:46+01:00 <info>charon: Last message '12[IKE] IKE_SA l2tp_' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:04:46+01:00 <info>charon: 12[IKE] IKE_SA l2tp_l2tpOverIpsec_wan1[16] established between 192.168.178.85[192.168.178.85]...88.152.XXX.YYY[192.168.178.61]
2021-01-07T02:04:46+01:00 <info>charon: 12[CFG] selected peer config l2tp_l2tpOverIpsec_wan1
2021-01-07T02:04:46+01:00 <info>charon: 12[CFG] looking for pre-shared key peer configs matching 192.168.178.85...88.152.XXX.YYY[192.168.178.61]
2021-01-07T02:04:46+01:00 <info>charon: 12[ENC] parsed ID_PROT request 0 [ ID HASH ]
2021-01-07T02:04:46+01:00 <info>charon: 12[NET] received packet: from 88.152.XXX.YYY[63646] to 192.168.178.85[4500] (68 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 07[NET] sending packet: from 192.168.178.85[500] to 88.152.XXX.YYY[63645] (244 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 07[ENC] generating ID_PROT response 0 [ KE No NAT-D NAT-D ]
2021-01-07T02:04:46+01:00 <info>charon: 07[IKE] FSLDBG: Now searching for PSK with :my_id,me,other_id,other: '192.168.178.85'[192.168.178.85] - '(null)'[88.152.XXX.YYY]
2021-01-07T02:04:46+01:00 <info>charon: 07[IKE] remote host is behind NAT
2021-01-07T02:04:46+01:00 <info>charon: 07[IKE] local host is behind NAT, sending keep alives
2021-01-07T02:04:46+01:00 <info>charon: 07[ENC] parsed ID_PROT request 0 [ KE No NAT-D NAT-D ]
2021-01-07T02:04:46+01:00 <info>charon: 07[NET] received packet: from 88.152.XXX.YYY[63645] to 192.168.178.85[500] (260 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 14[NET] sending packet: from 192.168.178.85[500] to 88.152.XXX.YYY[63645] (176 bytes)
2021-01-07T02:04:46+01:00 <info>charon: 14[ENC] generating ID_PROT response 0 [ SA V V V V V ]
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] sending NAT-T (RFC 3947) vendor ID
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] sending FRAGMENTATION vendor ID
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] sending Cisco Unity vendor ID
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] sending DPD vendor ID
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] sending XAuth vendor ID
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] IKE_SA (unnamed)[16] state change: CREATED => CONNECTING
2021-01-07T02:04:46+01:00 <info>charon: Last message '14[IKE] 88.152.XXX.YYY' repeated 1 times, supressed by syslog-ng on routerrv345p
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] 88.152.XXX.YYY is initiating a Main Mode IKE_SA
2021-01-07T02:04:46+01:00 <info>charon: 14[ENC] received unknown vendor ID: e3:a5:96:6a:76:37:9f:e7:07:22:82:31:e5:ce:86:52
2021-01-07T02:04:46+01:00 <info>charon: 14[ENC] received unknown vendor ID: 26:24:4d:38:ed:db:61:b3:17:2a:36:e3:d0:cf:b8:19
2021-01-07T02:04:46+01:00 <info>charon: 14[ENC] received unknown vendor ID: fb:1d:e3:cd:f3:41:b7:ea:16:b7:e5:be:08:55:f1:20
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] received FRAGMENTATION vendor ID
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] received draft-ietf-ipsec-nat-t-ike-02\n vendor ID
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] received NAT-T (RFC 3947) vendor ID
2021-01-07T02:04:46+01:00 <info>charon: 14[IKE] received MS NT5 ISAKMPOAKLEY vendor ID
2021-01-07T02:04:46+01:00 <info>charon: 14[ENC] received unknown vendor ID: 01:52:8b:bb:c0:06:96:12:18:49:ab:9a:1c:5b:2a:51:00:00:00:01
2021-01-07T02:04:46+01:00 <info>charon: 14[ENC] parsed ID_PROT request 0 [ SA V V V V V V V V ]
2021-01-07T02:04:46+01:00 <info>charon: 14[NET] received packet: from 88.152.XXX.YYY[63645] to 192.168.178.85[500] (408 bytes)Edit #2:
PPTP is working following this guide: https://community.cisco.com/t5/small-business-support-documents/pptp-vpn-configuration-on-rv340-345-routers/ta-p/3220097
Whats wrong with L2TP?
- Labels:
-
Small Business Routers
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-26-2021 06:45 AM
Hi
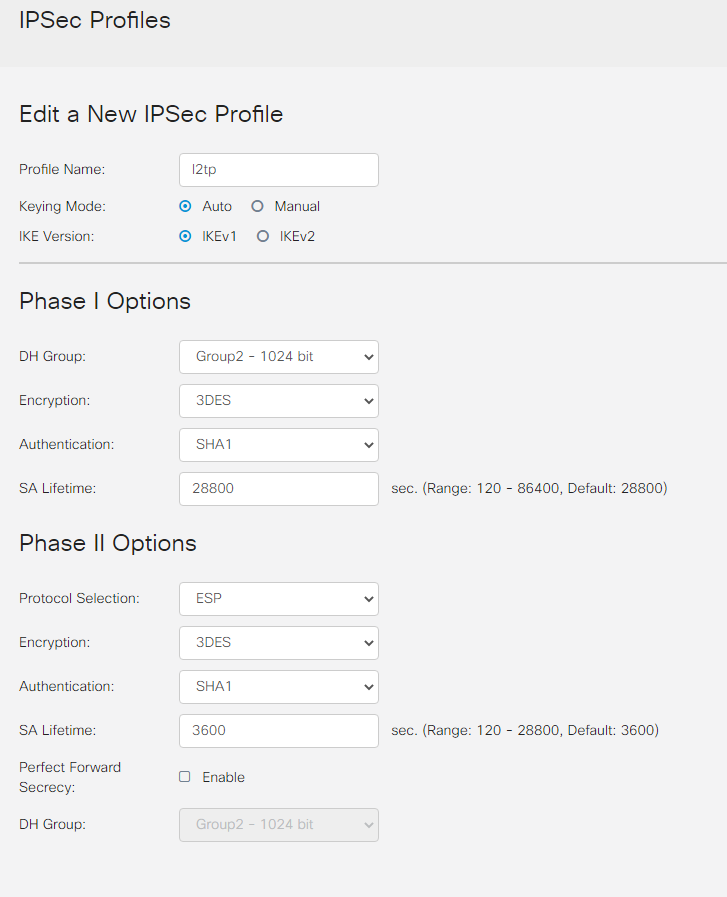
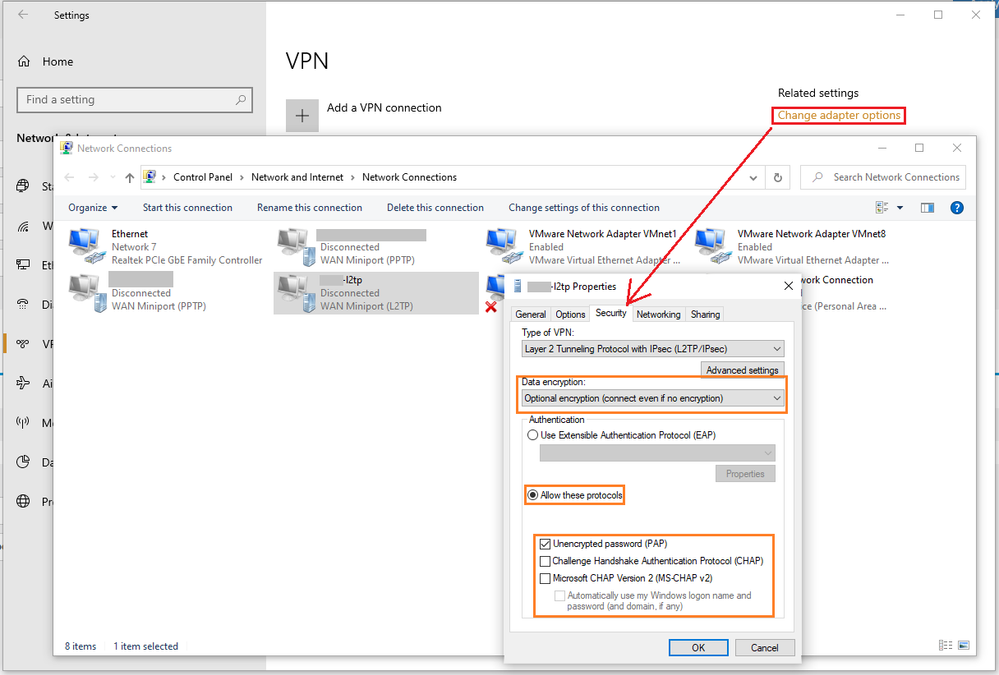
On Windows you have selected the default "optional encryption..." in data-encryption...so it generally means 3DES-sha1 will be be used for IPsec tunnel encryption algo, so on the RV345, you should select and apply the ipsec profile configured with 3DES-SHA1 in the l2tp-server config page
If you want to select the AES256 algo for l2tp-ipsec tunneling, then on the windows10 you should accordingly select one of the other options in "Data encryption" list as shown in attached screenshot...either "Require encryption..." OR "Maximum..." one of them has the support for AES256 in windows...try it out
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide