- Cisco Community
- シスコ コミュニティ
- セキュリティ
- [TKB] セキュリティ ドキュメント
- ASA 電話プロキシのトラブルシューティングおよび一般的な問題
- RSS フィードを購読する
- 新着としてマーク
- 既読としてマーク
- ブックマーク
- 購読
- 印刷用ページ
- 不適切なコンテンツを報告
- RSS フィードを購読する
- 新着としてマーク
- 既読としてマーク
- ブックマーク
- 購読
- 印刷用ページ
- 不適切なコンテンツを報告
2011-05-24 12:20 PM 2017-08-30 06:50 AM 更新
目的
Cisco Adaptive Security Appliance(ASA)電話プロキシは、Cisco Unified Phone Proxy の代替製品です。このページは、ファイアウォール上の電話プロキシ機能に関する問題のトラブルシューティングを支援することを目的としています。
説明
Cisco ASA 電話プロキシ機能を使用すると、電話機は直接、ASA と安全な通信チャネルを確立できます。この安全な通信はファイアウォール上で直接終端し、ファイアウォールは電話機と Call Manager との間の音声通信を「プロキシ」します。
この機能により、Call Manager へのトラフィックを暗号化するために別のデバイスがなくても、現場に導入された電話機の安全な音声通信が実現します。
ドキュメンテーション
電話プロキシのトラブルシューティングに関する公式ドキュメント
ライセンス
電話プロキシに接続できるリモートの電話機の数を確認するには、「show version」コマンドを使用します。「UC Proxy Sessions」の行に注意してください。
PhoneProxyASA#show version
Cisco Adaptive Security Appliance Software Version 8.0(4)
Device Manager Version 5.2(4)
....
UC Proxy Sessions : 2
こ れは、同時に確立できる TLS プロキシ セッションの合計数です。たとえば、クラスタ内に CUCM が 1 つだけある場合は、電話プロキシによって登録できる電話機の合計数は 2 台です。クラスタ内にバックアップ CUCM とプライマリ CUCM がある場合は、電話機を 1 台だけ登録できます。これは、電話機がバックアップ CUCM との TLS 接続も開始して TLS 接続を消費するためです。ライセンスに関する詳細については、http://www.cisco.com/en/US/docs/security/asa/asa80/configuration/guide/unified_comm.html#wp1139894 を参照してください。
接続されている電話機を確認するには、「show tls-proxy session」コマンドを使用します。ライセンスを超えると、次の syslog が表示されます。
%ASA-4-446002: Denied TLS Proxy session from outside:10.10.10.2/49572 to
inside:192.168.1.2/2000, licensed UC Proxy session limit of 20 exceeded
ユーザの接続を切断し、すぐに別の IP アドレスから再接続すると、ファイアウォールは不具合(Bug ID CSCsu11361)により影響を受ける可能性があることに注意してください。
電話の設定と作業
TFTP サーバの設定
- 電話機に TFTP サーバを設定するには、次の手順を実行します。
- Settings ボタンを押します。
- [3 - Network Configuration] を選択します。
- * * # を押して電話機のロックを解除します。電話機の右上にあるロック アイコンがロック解除状態に変わります。
- [24 Alternate TFTP](旧型の電話機ではオプション 32 の場合があります)が [YES] に設定されていることを確認します。
- オプション [8 TFTP Server 1] に、正しい TFTP サーバのアドレスを設定します。
電話機の CTL ファイルの削除
- Settings ボタンを押します。
- [Security Configuration](電話機のモデルによってはオプション 4 または 6 の場合があります)を選択します。
- * * # を押して電話機のロックを解除します。
- [CTL file] までスクロールして、Select を押します。
- Erase ボタンを押します(その前に more を押す必要のある場合があります)。
電話機のステータス メッセージの表示
- Settings ボタンを押します。
- [Status] までスクロールして、Select を押します。
- 1 つ目のオプション [Status Messages] で Select を押します。
トラブルシューティング/デバッグ
電話機の登録プロセスの詳細なウォークスルー
次に、電話機を電話プロキシに接続したときにどうなるかの詳細なウォークスルーを示します。
- 電話機の電源が投入され、電話機は DHCP 経由で IP アドレスを取得しようとします。
- 電話機は、CTL ファイルがない場合、tftp サーバからダウンロードしようとします。
- 電 話機が CTL ファイルの tftp 要求を送信すると、ASA はファイアウォールで生成された独自の CTL ファイルを送信します。したがって、パケットは実際には Call Manager 内部に送信または転送されません。すべて ASA によって「スプーフィング」されます。
- 電話機に別の Call Manager からダウンロードされた「古い」CTL ファイルがある場合、新しい CTL ファイルが「古い」CTL ファイルの SAST キーによって署名されていないと、次のステップが失敗する可能性があります。そのため、新しい CTL ファイルは別の SAST キーによって署名された場合、電話機で拒否され、「CTL File Not Authorized」(CTL ファイルが許可されていません)というエラーが表示されます。新しい適切な CTL ファイルをダウンロードできるように、古い CTL ファイルをクリアする必要があります。
- 電話機は、設定内の tftp サーバ エントリを読み取り、ファイル「SEPxxxxxxxxxxx.cfg.xml」の要求を送信します。x は電話機の MAC アドレスを表します。
- ASA は、この tftp 要求を代行受信し、Call Manager から自身のメモリに設定ファイルをダウンロードします。次に、設定ファイルを変更して、その変更したファイルを電話機に送信します。このプロセス中、 ASA から Call Manager に送信された tftp パケットには、ファイアウォールの内部インターフェイスではなく、電話機の送信元 IP アドレスが含まれます。これは、Call Manager から電話機に返信されたリターン トラフィックは ASA を通過しなければならないため重要です。ASA は、ファイルを取得すると、電話機に送信する前に次の変更を行います。
- 「securityDeviceMode」エントリを検索して、暗号化されるように「3」に設定します。
- ASA の設定に応じて、その他の電話機セキュリティ パラメータを変更します。phone-proxy インスタンスの設定の「no disable service-settings」コマンドを参照してください。
- CUCM の IP アドレスおよび CAPF アドレス(存在する場合)で NAT を実行します。
- proxyServerURL を書き換えます(設定されている場合)。
- ACL を作成して、電話機が CUCM との TLS 接続を開始できるようにします。
- 電話機が CUCM で非セキュア電話機として設定されている場合、電話機から CUCM への app-redirect ルールを作成します。
- 電 話機は、変更された設定ファイルを受信し、(ファイアウォール上の変換で設定されているように)Call Manager のグローバル IP アドレスへの新たなセキュア TCP 接続を確立しようとします。SCCP(Skinny)の場合、この接続は TCP ポート 2443 で確立され、SIP の場合は 5061 になります。
- ここでは、電話機からのトラフィックが Call Manager に着信すると、送信元 IP アドレスは電話機の送信元 IP アドレスになることに注意してください。したがって、Call Manager から電話機へのリターン トラフィックは ASA を経由することが重要です。経由しない場合、登録は失敗します。
- TLS ハンドシェイクの間、TLS プロキシは、電話機が示した証明書から電話機の MAC アドレスを抽出し、電話機の IP アドレスのこの MAC アドレスが電話プロキシの secure-phone DB 内にあるかどうかをチェックします。secure-phone DB の内容を確認するには、「show phone-proxy secure-phones」コマンドを使用します。電話機に secure-phone DB のエントリがある場合は、TLS ハンドシェイクは続行されます。ない場合は、TLS プロキシによって拒否され、電話機は登録できません。
- 電 話機が非セキュア電話として設定されている場合、ASA は接続されている各電話機に対して Call Manager との暗号化されない Skinny 接続を確立します。暗号化された電話機としてセキュア プロファイルが設定されている場合、ASA と CUCM との間の接続も暗号化されます。暗号化された接続が、ASA と、接続されている各電話機との間に確立されます。
- リモートの安全な電話 機は、ASA のメディア ターミネーション アドレスに SRTP を送信し始めます。別の電話機への他のレッグが非セキュアの場合、ASA は SRTP パケットを復号化し、RTP パケットとして送信します。同様に、受信側電話機は ASA のメディア ターミネーション アドレスに SRTP または RTP を送信し、ASA はパケットを暗号化/再暗号化し、SRTP としてリモートの安全な電話機に送信します。
一般的な問題
電話機の登録に関する問題
ASA にシスコ製造元証明書がロードされていない
シスコの CA 製造元証明書が ASA にインストールされておらず、電話機が MIC(LSC 証明書ではなく)を使用して接続されている場合、次の syslog が表示されます。
Aug 29 2008 09:03:30: %ASA-6-725001: Starting SSL handshake with client
outside:192.168.254.254/50272 for TLSv1 session.
Aug 29 2008 09:03:30: %ASA-7-725010: Device supports the following 4 cipher(s).
Aug 29 2008 09:03:30: %ASA-7-725011: Cipher[1] : RC4-SHA
Aug 29 2008 09:03:30: %ASA-7-725011: Cipher[2] : AES128-SHA
Aug 29 2008 09:03:30: %ASA-7-725011: Cipher[3] : AES256-SHA
Aug 29 2008 09:03:30: %ASA-7-725011: Cipher[4] : DES-CBC3-SHA
Aug 29 2008 09:03:30: %ASA-7-725008: SSL client outside:192.168.254.254/50272 proposes the
following 2 cipher(s).
Aug 29 2008 09:03:30: %ASA-7-725011: Cipher[1] : AES256-SHA
Aug 29 2008 09:03:30: %ASA-7-725011: Cipher[2] : AES128-SHA
Aug 29 2008 09:03:30: %ASA-7-725012: Device chooses cipher : AES128-SHA for the SSL
session with client outside:192.168.254.254/50272
Aug 29 2008 09:03:32: %ASA-7-725014: SSL lib error. Function: SSL3_READ_BYTES Reason: ssl
handshake failure
Aug 29 2008 09:03:32: %ASA-7-717025: Validating certificate chain containing 1
certificate(s).
Aug 29 2008 09:03:32: %ASA-7-717029: Identified client certificate within certificate
chain. serial number: 19567F78000000281D45, subject name:
cn=CP-7942G-SEP001DA23EA450,ou=EVVBU,o=Cisco Systems Inc..
Aug 29 2008 09:03:32: %ASA-3-717009: Certificate validation failed. No suitable
trustpoints found to validate certificate serial number: 19567F78000000281D45, subject
name: cn=CP-7942G-SEP001DA23EA450,ou=EVVBU,o=Cisco Systems Inc..
Aug 29 2008 09:03:32: %ASA-3-717027: Certificate chain failed validation. No suitable
trustpoint was found to validate chain.
Aug 29 2008 09:03:32: %ASA-7-725014: SSL lib error. Function: SSL3_GET_CLIENT_CERTIFICATE
Reason: no certificate returned
Aug 29 2008 09:03:32: %ASA-6-725006: Device failed SSL handshake with outside
client:192.168.254.254/50272
Aug 29 2008 09:03:32: %ASA-6-302014: Teardown TCP connection 797 for
outside:192.168.254.254/50272 to inside:10.55.151.140/2000 duration 0:00:01 bytes 623 Flow
closed by inspection
電話機に証明書がインストールされていない
症 状:電話機は TFTP 設定をダウンロードしますが、セキュア ポート 2443 でファイアウォールとの接続に失敗します。代わりに、非セキュア ポート 2000(非セキュア ポート)で接続します。電話機に証明書がインストールされていない場合、電話機は暗号化を使用するように示す設定ファイルのエントリを無視し、非セキュア であるかのように接続します。外部 ACL がポート 2000 で着信接続を許可すると、電話機は Call Manager に登録できますが、非セキュア モードになります。受信ポート 2000 がブロックされると、電話機は登録に失敗し、「Opening x.x.x.x」(x.x.x.x を開いています)と表示されます。電話機のステータス メッセージには、設定ファイルがダウンロードされたことだけが表示されます。tftp debug には、CTL および設定ファイルが正常にダウンロードされたことが表示されます。
PP: 172.18.254.73/51783 requesting CTLSEP0007EBF0EE54.tlv
PP: Created entry for secure device outside:172.18.254.73, MAC 0007.ebf0.ee54, current count 1, list count 3
PP: opened 0x32b3cfea
PP: Data Block 1 forwarded from 14.36.107.90/46309 to 172.18.254.73/51783 ingress ifc outside
PP: Received ACK Block 1 from outside:172.18.254.73/51783 to inside:172.18.124.230
PP: Data Block 2 forwarded to 172.18.254.73/51783
PP: Received ACK Block 2 from outside:172.18.254.73/51783 to inside:172.18.124.230
PP: Data Block 3 forwarded to 172.18.254.73/51783
PP: Received ACK Block 3 from outside:172.18.254.73/51783 to inside:172.18.124.230
PP: Data Block 4 forwarded to 172.18.254.73/51783
PP: Received ACK Block 4 from outside:172.18.254.73/51783 to inside:172.18.124.230
PP: Data Block 5 forwarded to 172.18.254.73/51783
PP: Received ACK Block 5 from outside:172.18.254.73/51783 to inside:172.18.124.230
PP: Data Block 6 forwarded to 172.18.254.73/51783
PP: Received ACK Block 6 from outside:172.18.254.73/51783 to inside:172.18.124.230
PP: Data Block 7 forwarded to 172.18.254.73/51783
PP: Received ACK Block 7 from outside:172.18.254.73/51783 to inside:172.18.124.230
PP: Data Block 8 forwarded to 172.18.254.73/51783
PP: Received ACK Block 8 from outside:172.18.254.73/51783 to inside:172.18.124.230
PP: Data Block 9 forwarded to 172.18.254.73/51783
PP: Received ACK Block 9 from outside:172.18.254.73/51783 to inside:172.18.124.230
PP: TFTP session complete, all data sent
PP: 172.18.254.73/51784 requesting SEP0007EBF0EE54.cnf.xml.sgn
PP: opened 0x32b48326
PP: Received Data Block 1 from inside:172.18.124.230/32815 to outside:172.18.254.73/51784
Received Block 1
PP: Acked Block #1 from 172.18.124.241/33423 to 172.18.124.230/32815
PP: Received Data Block 2 from inside:172.18.124.230/32815 to outside:172.18.254.73/51784
Received Block 2
PP: Acked Block #2 from 172.18.124.241/33423 to 172.18.124.230/32815
PP: Received Data Block 3 from inside:172.18.124.230/32815 to outside:172.18.254.73/51784
Received Block 3
PP: Acked Block #3 from 172.18.124.241/33423 to 172.18.124.230/32815
PP: Received Data Block 4 from inside:172.18.124.230/32815 to outside:172.18.254.73/51784
Received Block 4
PP: Acked Block #4 from 172.18.124.241/33423 to 172.18.124.230/32815
PP: Received Data Block 5 from inside:172.18.124.230/32815 to outside:172.18.254.73/51784
Received Block 5
PP: Acked Block #5 from 172.18.124.241/33423 to 172.18.124.230/32815
PP: Received Data Block 6 from inside:172.18.124.230/32815 to outside:172.18.254.73/51784
Received Block 6
PP: Acked Block #6 from 172.18.124.241/33423 to 172.18.124.230/32815
PP: Received Data Block 7 from inside:172.18.124.230/32815 to outside:172.18.254.73/51784
Received Block 7
PP: Acked Block #7 from 172.18.124.241/33423 to 172.18.124.230/32815
PP: Received Data Block 8 from inside:172.18.124.230/32815 to outside:172.18.254.73/51784
Received Block 8
PP: Acked Block #8 from 172.18.124.241/33423 to 172.18.124.230/32815
PP: Added ACL for 172.18.254.73 to outside:14.36.107.90/2443
PP: Applied Application Redirect rule for 172.18.254.73/2000 to 14.36.107.90, secure port 2443
PP: Added ACL for 172.18.254.73 to outside:14.36.107.90/59699
PP: Applied Application Redirect rule for 172.18.254.73/3804 to 14.36.107.90, secure port 59699
PP: Modifying to encrypted mode.
PP: Modifying to TLS as the transport layer protocol.
PP: Data Block 1 forwarded from 14.36.107.90/9694 to 172.18.254.73/51784
PP: Received ACK Block 1 from outside:172.18.254.73/51784 to inside:172.18.124.230
PP: Data Block 2 forwarded to 172.18.254.73/51784
PP: Received ACK Block 2 from outside:172.18.254.73/51784 to inside:172.18.124.230
PP: Data Block 3 forwarded to 172.18.254.73/51784
PP: Received ACK Block 3 from outside:172.18.254.73/51784 to inside:172.18.124.230
PP: Data Block 4 forwarded to 172.18.254.73/51784
PP: Received ACK Block 4 from outside:172.18.254.73/51784 to inside:172.18.124.230
PP: Data Block 5 forwarded to 172.18.254.73/51784
PP: Received ACK Block 5 from outside:172.18.254.73/51784 to inside:172.18.124.230
PP: Data Block 6 forwarded to 172.18.254.73/51784
PP: Received ACK Block 6 from outside:172.18.254.73/51784 to inside:172.18.124.230
PP: Data Block 7 forwarded to 172.18.254.73/51784
PP: Received ACK Block 7 from outside:172.18.254.73/51784 to inside:172.18.124.230
PP: Data Block 8 forwarded to 172.18.254.73/51784
PP: Received ACK Block 8 from outside:172.18.254.73/51784 to inside:172.18.124.230
PP: TFTP session complete, all data sent
syslog には、tftp 接続、およびポート 2000 でのその後の Skinny 接続だけが表示されます。
Sep 19 2008 15:19:03: %ASA-7-609001: Built local-host outside:172.18.254.73
Sep 19 2008 15:19:03: %ASA-6-305011: Built dynamic UDP translation from
outside:172.18.254.73/51783 to inside:172.18.124.241/41910
Sep 19 2008 15:19:03: %ASA-6-302015: Built inbound UDP connection 25958 for
outside:172.18.254.73/51783 (172.18.124.241/41910) to inside:172.18.124.230/69 (14.36.107.90/69)
Sep 19 2008 15:19:03: %ASA-6-305011: Built dynamic UDP translation from
inside:172.18.124.230/39638 to outside:14.36.107.90/46309
Sep 19 2008 15:19:03: %ASA-6-302015: Built inbound UDP connection 25959 for
outside:172.18.254.73/51783 (172.18.124.241/41910) to inside:172.18.124.230/39638 (14.36.107.90/46309)
Sep 19 2008 15:19:04: %ASA-6-305012: Teardown dynamic UDP translation from
inside:172.18.124.230/32813 to outside:14.36.107.90/62674 duration 0:02:30
Sep 19 2008 15:19:05: %ASA-6-305011: Built dynamic UDP translation from
outside:172.18.254.73/51784 to inside:172.18.124.241/33423
Sep 19 2008 15:19:05: %ASA-6-302015: Built inbound UDP connection 25960 for
outside:172.18.254.73/51784 (172.18.124.241/33423) to inside:172.18.124.230/69 (14.36.107.90/69)
Sep 19 2008 15:19:05: %ASA-6-302015: Built inbound UDP connection 25961 for
outside:172.18.254.73/51784 (172.18.124.241/33423) to inside:172.18.124.230/32815 (14.36.107.90/9694)
Sep 19 2008 15:19:05: %ASA-6-305011: Built dynamic TCP translation from
inside:172.18.124.230/3804 to outside:14.36.107.90/59699
Sep 19 2008 15:19:06: %ASA-2-106001: Inbound TCP connection denied from
172.18.254.73/51989 to 14.36.107.90/2000 flags SYN on interface outside
Sep 19 2008 15:19:07: %ASA-2-106001: Inbound TCP connection denied from
172.18.254.73/51989 to 14.36.107.90/2000 flags SYN on interface outside
Call Manager から電話機へのトラフィックが ASA を通過しないため、TFTP に障害が発生する
Call Manager から電話機に戻るトラフィックは、ASA を通過する必要があります。通過しない場合、非対称ルーティングにより登録プロセスは失敗します。
こ の場合、電話機は直接 ASA から CTL ファイルを受信するので(Call Manager はまだ関与しません)、CTL ファイルは電話機によってダウンロードされます。電話機は、CTL ファイルがロードされると、Call Manager に TFTP 要求を送信します。この tftp 要求パケットは、電話機の実際の外部 IP から送信されます。Call Manager は、要求された tftp データを電話機の実際の IP アドレス宛に送信して応答します。ネットワークは、Call Manager からファイアウォールを経由して電話機にリターン パケットをルーティングする必要があります。パケットが ASA を通過しなかった場合、電話機で受信されたときにドロップされます。ネットワーク内で ASA が配置されている場所によっては、このルーティング問題を解決するには、いくつかの(場合によっては大きな)ルーティング変更が必要になることがありま す。回避策の 1 つとして、すべての電話機のトラフィックがネットワークに入るときにインバウンド NAT/PAT を実行する方法があります。しかし、これは他の問題を引き起こす原因になることがあります(特に nat-control が有効な場合。nat-control が有効で、外部 NAT/PAT が設定されている場合は、すべての着信トラフィックに対して外部 NAT を設定する必要があります)。
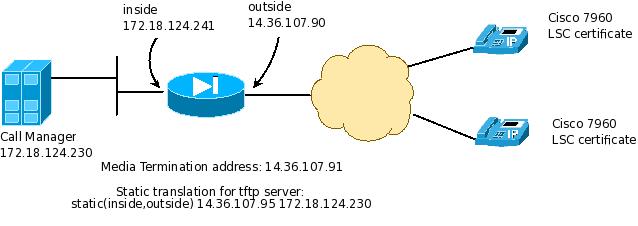
次の図にこの問題を示します。
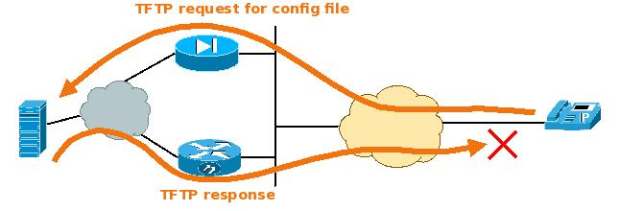
次に、ASA でリモートの電話機が電話プロキシに接続されている場合の「debug phone-proxy tftp」の出力例を示します。ネットワークは、Call Manager から電話機に ASA を経由してトラフィックをルーティングしません。そのため、設定ファイルの TFTP 転送は失敗します。電話機は何度も繰り返しダウンロードしようとします。
PP: 172.18.254.73/52361 requesting CTLSEP0007EBF0EE54.tlv
PP: opened 0x116804ea
PP: Data Block 1 forwarded from 14.36.107.90/8554 to 172.18.254.73/52361 ingress ifc outside
PP: Received ACK Block 1 from outside:172.18.254.73/52361 to inside:172.18.124.230
PP: Data Block 2 forwarded to 172.18.254.73/52361
PP: Received ACK Block 2 from outside:172.18.254.73/52361 to inside:172.18.124.230
PP: Data Block 3 forwarded to 172.18.254.73/52361
PP: Received ACK Block 3 from outside:172.18.254.73/52361 to inside:172.18.124.230
PP: Data Block 4 forwarded to 172.18.254.73/52361
PP: Received ACK Block 4 from outside:172.18.254.73/52361 to inside:172.18.124.230
PP: Data Block 5 forwarded to 172.18.254.73/52361
PP: Received ACK Block 5 from outside:172.18.254.73/52361 to inside:172.18.124.230
PP: Data Block 6 forwarded to 172.18.254.73/52361
PP: Received ACK Block 6 from outside:172.18.254.73/52361 to inside:172.18.124.230
PP: Data Block 7 forwarded to 172.18.254.73/52361
PP: Received ACK Block 7 from outside:172.18.254.73/52361 to inside:172.18.124.230
PP: Data Block 8 forwarded to 172.18.254.73/52361
PP: Received ACK Block 8 from outside:172.18.254.73/52361 to inside:172.18.124.230
PP: Data Block 9 forwarded to 172.18.254.73/52361
PP: Received ACK Block 9 from outside:172.18.254.73/52361 to inside:172.18.124.230
PP: TFTP session complete, all data sent
PP: 172.18.254.73/52362 requesting SEP0007EBF0EE54.cnf.xml.sgn
PP: opened 0x116974f6
PP: 172.18.254.73/52363 requesting SEP0007EBF0EE54.cnf.xml.sgn
PP: opened 0x116a21e2
PP: 172.18.254.73/52364 requesting SEP0007EBF0EE54.cnf.xml.sgn
PP: opened 0x116b06ae
電話機は設定ファイルを要求し続けますが、成功しません。このリモートの電話機に外部 PAT を追加すると、問題が緩和されます(ここでは、ファイアウォールを経由して着信するすべての外部トラフィックに対して PAT を実行しました)。
PhoneProxyASA(config)# nat (outside) 55 0 0 outside
PhoneProxyASA(config)# global (inside) 55 interface
または
次に、内部にある Call Manager 宛のトラフィックだけに対して外部で PAT を実行する例を示します。
PhoneProxyASA(config)#object-group service CUCM-PROXY-PORTS
PhoneProxyASA(config-service)#service-object udp eq tftp
service-object udp range 1024 65535
service-object tcp eq 2443
service-object tcp eq 5061
service-object tcp eq 3804
PhoneProxyASA(config)#access-list cucm-traffic extended permit object-group
CUCM-PROXY-PORTS any host 172.18.124.230
PhoneProxyASA(config)#nat (outside) 55 access-list cucm-traffic outside
PhoneProxyASA(config)#global (inside) 55 interface
172.18.124.230 は内部にある Call Manager の変換アドレスです。
または
PhoneProxyASA(config)# nat (outside) 55 172.18.254.73 255.255.255.255 outside
PhoneProxyASA(config)# global (inside) 55 interface
172.18.254.73 は外部にある電話機の IP アドレスです。
または
8.3 では、NAT 設定形式が変更され、Twice NAT がポリシー ベース NAT に導入されました。次に、稼動している Twice NAT を示します。CUCM パブリック IP アドレス宛のトラフィックに動的に PAT を実行し、送信元を ASA の内部 IP アドレスに、CUCM パブリック IP アドレスの宛先を対応するプライベート IP アドレスに変換します。
PhoneProxyASA(config)# object network obj-cucm-public
PhoneProxyASA(config-network-object)# host <cucm-public-ip-address>
PhoneProxyASA(config)# object network obj-cucm-private
PhoneProxyASA(config-network-object)# host <cucm-private-ip-address>
PhoneProxyASA(config)# nat (outside,inside) source dynamic any interface destination static obj-cucm-public obj-cucm-private
Call Manager クラスタに複数のデバイスがあり、ASA が 1 台にだけ設定されている
Call Manager クラスタに複数のデバイス(TFTP サーバ、パブリッシャ、サブスクライバなど)がある場合、デバイスごとにスタティック変換、ctl-file エントリ、およびトラストポイントが必要です。
ASA での DNS 解決に関する問題
Call Manager がホスト名(IP アドレスではなく)で定義されている場合は、電話機が初めて tftp 設定をダウンロードすると、ASA は Call Manager のホスト名でルックアップを実行しようとしますが、失敗します。「debug phone-proxy tftp」の出力には次が表示されます。
....
PP: Received Data Block 15 from vlan100:172.16.100.1/34248 to vlan96:172.16.96.16/49165
Received Block 15
PP: Acked Block #15 from 172.16.96.16/49165 to 172.16.100.1/34248
PP: Received Data Block 16 from vlan100:172.16.100.1/34248 to vlan96:172.16.96.16/49165
Received Block 16
PP: Acked Block #16 from 172.16.96.16/49165 to 172.16.100.1/34248
PP: Received Data Block 17 from vlan100:172.16.100.1/34248 to vlan96:172.16.96.16/49165
Received Block 17
PP: Acked Block #17 from 172.16.96.16/49165 to 172.16.100.1/34248
PP: Received Data Block 18 from vlan100:172.16.100.1/34248 to vlan96:172.16.96.16/49165
Received Block 18
PP: Acked Block #18 from 172.16.96.16/49165 to 172.16.100.1/34248
PP: Unable to get dns response for id 7
PP: Callback, error modifying config file
PP: Unable to CM name addr
PP: Callback required for parsing config file
対処方法は、Call Manager の名前に対して IP を解決できるように ASA で名前解決を設定することです。
ASA の時刻が間違っているため、証明書検証に失敗する
ファイアウォールの日付が間違っている場合、電話機から提供される証明書が拒否されることがあります。電話機に TLS の問題を示すエラーが点滅する場合があります。
ファイアウォールの syslog には次が表示されます。
Jan 02 2005 22:22:38: %ASA-6-305011: Built dynamic TCP translation from
outside:172.18.254.95/1072 to inside:172.18.124.241/3165
Jan 02 2005 22:22:38: %ASA-6-302013: Built inbound TCP connection 569 for
outside:172.18.254.95/1072 (172.18.124.241/3165) to inside:172.18.124.230/2000 (14.36.107.90/2443)
Jan 02 2005 22:22:38: %ASA-6-725001: Starting SSL handshake with client
outside:172.18.254.95/1072 for TLSv1 session.
Jan 02 2005 22:22:38: %ASA-7-725010: Device supports the following 4 cipher(s).
Jan 02 2005 22:22:38: %ASA-7-725011: Cipher[1] : RC4-SHA
Jan 02 2005 22:22:38: %ASA-7-725011: Cipher[2] : AES128-SHA
Jan 02 2005 22:22:38: %ASA-7-725011: Cipher[3] : AES256-SHA
Jan 02 2005 22:22:38: %ASA-7-725011: Cipher[4] : DES-CBC3-SHA
Jan 02 2005 22:22:38: %ASA-7-725008: SSL client outside:172.18.254.95/1072 proposes
the following 2 cipher(s).
Jan 02 2005 22:22:38: %ASA-7-725011: Cipher[1] : AES256-SHA
Jan 02 2005 22:22:38: %ASA-7-725011: Cipher[2] : AES128-SHA
Jan 02 2005 22:22:38: %ASA-7-725012: Device chooses cipher : AES128-SHA for the SSL
session with client outside:172.18.254.95/1072
Jan 02 2005 22:22:38: %ASA-7-111009: User 'enable_15' executed cmd: show logging
Jan 02 2005 22:22:40: %ASA-7-717025: Validating certificate chain containing 1
certificate(s).
Jan 02 2005 22:22:40: %ASA-7-717029: Identified client certificate within certificate
chain. serial number: 01, subject name: cn=SEP0007EBF0EE54.
Jan 02 2005 22:22:40: %ASA-7-717030: Found a suitable trustpoint capf_trustpoint to
validate certificate.
Jan 02 2005 22:22:40: %ASA-3-717009: Certificate validation failed. Certificate date
is out-of-range, serial number: 01, subject name: cn=SEP0007EBF0EE54.
Jan 02 2005 22:22:40: %ASA-3-717027: Certificate chain failed validation. Certificate
chain date is out-of-range.
Jan 02 2005 22:22:40: %ASA-7-725014: SSL lib error. Function: SSL3_GET_CLIENT_CERTIFICATE
Reason: no certificate returned
Jan 02 2005 22:22:40: %ASA-6-725006: Device failed SSL handshake with outside
client:172.18.254.95/1072
Jan 02 2005 22:22:40: %ASA-6-302014: Teardown TCP connection 569 for
outside:172.18.254.95/1072 to inside:172.18.124.230/2000 duration 0:00:02 bytes 901 Flow closed by inspection
電話機のコール音声に関する問題
コール中にポンという音が聞こえる
Bug ID CSCsv86408 を参照してください。
コールの確立時に音声が一方向だけ、またはまったく聞こえない
この問題の最も考えられる原因は、次のいずれかの状況が原因となる誤ったパケット ルーティングです。
- 電 話機から MTA アドレス宛に送信されたパケットがファイアウォールに到達しない。これは、ファイアウォール(ファイアウォールの各インターフェイス)によって取得され た、MTA で送受信されたすべてのトラフィックのキャプチャに示されます。パケットがファイアウォールに到達していない場合、パケットがドロップされたかどうかを確 認するためにさらにトラブルシューティングが必要です。
- 電話機から MTA アドレス宛に送信されたパケットはファイアウォールに到達し、インターフェイス X に着信するが、ASA から電話機に送信されたトラフィックはインターフェイス Y から送信される。これは、ファイアウォール(ファイアウォールの各インターフェイス)によって取得された、MTA で送受信されたすべてのトラフィックのキャプチャに示されます。電話機から受信された音声トラフィックが、ファイアウォールがその電話機に音声トラフィッ クを送信するインターフェイスとは別のインターフェイス上のファイアウォールに入ると、パケットは ASA によってドロップされます。その理由は、電話機から受信された UDP パケットがファイアウォールによって確立された接続に適合しないためです。「no matching conn」による ASP ドロップが表示されます。
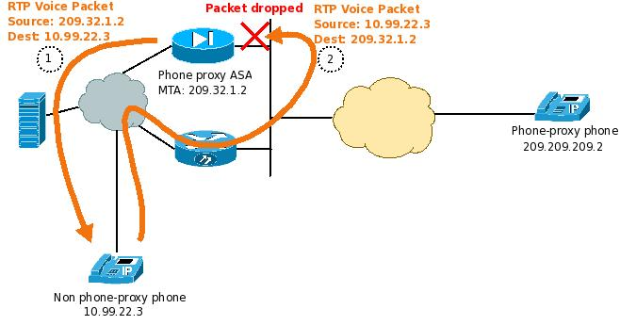
次にこの例を示します。
バージョン 8.2 から、インターフェイス単位のメディア ターミネーション アドレスをサポートする新機能が追加されます。これにより、この例で示す問題が緩和されます。
次のいずれかを実行すると、この問題を緩和できる可能性があります。
- MTA 宛のトラフィックがファイアウォールの内部インターフェイスにルーティングされるように、ネットワークの内部でスタティック ルートを追加します。
- 隣接するデバイスにスタティック ルートを追加し、内部で実行されているこのルーティング プロトコル全体でこのルートを再配布します。
- 音 声トラフィックがそのトラフィックを受信するインターフェイスから送信されるように、ファイアウォールのルーティング テーブルを変更します。上記の例では、10.99.22.3 宛のトラフィックが外部インターフェイスから送信されるように、ファイアウォールにルートを追加します。
電話サービスに関する問題
ディレクトリ サービスおよび認証サービスが Call Manager 8.0 で動作しない
ディ レクトリや認証など、Call Manager 8.0(CUCM 8.0)の電話 HTTP サービスの一部として、HTTPS 接続をデフォルトで使用します。現時点では、これらの機能は ASA 電話プロキシのプロキシ サーバ機能ではサポートされていません。
ASA 不具合(Bug ID CSCti62447)を参照してください。
動作しない理由
電話機が安全な(HTTPS)接続を確立するためには、電話機は Call Manager の TVS ストアと通信する必要があります。現時点では、電話プロキシは TVS ストアとの通信がサポートしていません。そのため、Secure Services は失敗します。
電話プロキシを使用しない TVS のメッセージ フローは次のとおりです。
- 電話機は起動すると、CUCM サーバから Identity Trust List(ITL)をダウンロードします。ITL は、Trust Verification Server(TVS)とその証明書のリストです。
- 電話機は、必要なサービス(ディレクトリなど)のための、HTTPS サーバとの SSL ハンドシェイクを開始します。
- HTTPS サーバは電話機に Server Hello とサーバ証明書を返信します。
- 電話機は、TCP ポート 2445 で TVS サーバのいずれかとの SSL 接続を作成します。TVS サーバは CUCM サーバです。
- 電 話機は TVS サーバに「Is this server certificate in the CUCM trust store, or signed by a certificate in the CUCM trust store?」(これは CUCM 信頼ストア内のサーバ証明書ですか? または CUCM 信頼ストア内の証明書によって署名されていますか?)と質問します。
- 「はい」の場合は、元の HTTPS サーバとの SSL ハンドシェイクは続行されます。そうでない場合は、SSL ハンドシェイクは失敗します。
こ の機能を使用すると、TVS をサポートするすべての IP 電話エンドポイントに対して CUCM サーバ上に信頼ストアを 1 つ維持できます。これは、8.X CUCM で 9.X 電話機ファームウェアを実行する第 3 世代以降のすべての電話機においてデフォルトで有効化できます。
回避策
現在の電話プロキシ実装で動作させるには、電話機に HTTPS ではなく HTTP を使用させるようにする必要があります。このための直接的な解決方法はありません。電話機に HTTPS ではなく HTTP を使用させるには、リモートの電話プロキシ電話機で次の Call Manager の設定を行ってください。
Call Manager の電話設定で([CCMAdmin] > [Device] > [Phone])、非 HTTPS バージョンの別の電話サービス URL を手動で指定します。HTTP URL 行で通常のフィールドと「安全な」フィールドの両方に入力します。
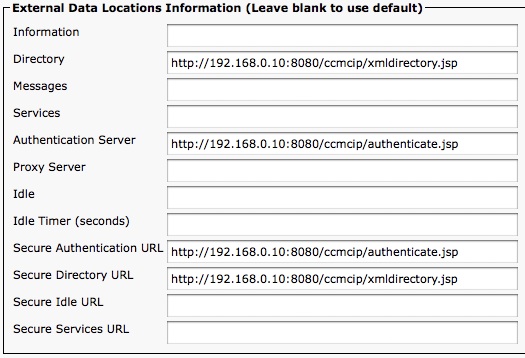
- Call Manager の [Services Provisioning] で([CCMAdmin] > [Device] > [Phone])、電話機が [External] または [Both] に設定されていることを確認します。これにより、入力する URL を使用できます。
Call Manager で電話設定が正しく設定されたら、ASA 電話プロキシ設定で通常どおり「プロキシ サーバ」機能を設定します。次に例を示します。
phone-proxy ASA-phone-proxy
media-termination phone-proxy-mta
tftp-server address 192.168.0.11 interface Inside
tls-proxy ASA-tls-proxy
ctl-file ctl_phoneproxy_file
proxy-server address 192.168.0.11 interface Inside
show コマンドと出力例
ここに示す show コマンドは、次のネットワーク図に基づいています。
| show phone-proxy secure-phones |
電話プロキシの secure-phone DB 内に現存するすべての電話機を表示します。電話機のポートが 0 の場合は、電話機が CUCM に登録されなかったことを意味します。
PhoneProxyASA# show phone-proxy secure-phones
ASA-phone-proxy: 2 in use, 2 most used
Interface IP Address Port MAC Timeout Idle
outside 172.18.254.25 19931 0009.b7d0.eea7 0:05:00 0:00:11
outside 172.18.254.73 50124 0007.ebf0.ee54 0:05:00 0:00:08
PhoneProxyASA#
| show phone-proxy media-sessions |
ファイアウォールを経由する現在アクティブなメディア セッション(コール)をすべて表示します。現在アクティブなコールがない場合は、この出力は空白になります。
PhoneProxyASA# show phone-proxy secure-phones
ASA-phone-proxy: 2 in use, 2 most used
Interface IP Address Port MAC Timeout Idle
outside 172.18.254.25 19931 0009.b7d0.eea7 0:05:00 0:00:11
outside 172.18.254.73 50124 0007.ebf0.ee54 0:05:00 0:00:08
PhoneProxyASA#
| show phone-proxy media-sessions |
ファイアウォールを経由する現在アクティブなメディア セッション(コール)をすべて表示します。現在アクティブなコールがない場合は、この出力は空白になります。
PhoneProxyASA# show phone-proxy media-sessions
2 in use, 2 most used
Media-session: 14.36.107.91/26830 :: client ip 172.18.254.73/29836
Lcl SRTP conn 14.36.107.91/26830 to 172.18.254.25/41282 tx_pkts 60 rx_pkts 61
Media-session: 14.36.107.91/29724 :: client ip 172.18.254.25/41282
Lcl SRTP conn 14.36.107.91/29724 to 172.18.254.73/29836 tx_pkts 61 rx_pkts 61
PhoneProxyASA#
| show tls-proxy sessions |
ASA で現在 TLS 接続を終端しているすべての電話機を表示します。
PhoneProxyASA# show tls-proxy sessions
3 in use (3 established), 7 most used
outside 172.18.254.95:1035 inside 172.18.124.230:2000 P:0xd5a407f0(ASA-tls-proxy) S:0xd5bd4738 byte 8392
outside 172.18.254.46:1143 inside 172.18.124.230:2000 P:0xd5a407f0(ASA-tls-proxy) S:0xd5bd7c90 byte 8572
outside 172.18.254.49:6136 inside 172.18.124.230:2000 P:0xd5a407f0(ASA-tls-proxy) S:0xd5bbac40 byte 6460
同一の接続が show conn の出力で表示されます。
PhoneProxyASA# show conn
4 in use, 48 most used
TCP outside 172.18.124.241(172.18.254.95):1035 inside 172.18.124.230:2000, idle 0:00:27, bytes 16951, flags UIOB
TCP outside 172.18.124.241(172.18.254.49):6136 inside 172.18.124.230:2000, idle 0:00:13, bytes 13949, flags UIOB
TCP outside 172.18.124.241(172.18.254.46):1143 inside 172.18.124.230:2000, idle 0:00:04, bytes 17213, flags UIOB
| show tls-proxy sessions detail |
TLS 接続に関する詳細情報を表示します。CUCM への接続が平文の場合、次のように State に「TCPOK」と表示されます。
PhoneProxyASA# show tls-proxy sessions detail
outside 172.18.22.223:2658 DMZ 192.168.2.3:2000 P:0xd5f4fc20(mytls)
S:0xd6193430 byte 37124
Client: State SSLOK Cipher AES128-SHA Ch 0xd49090d8 TxQSize 0
LastTxLeft 0 Flags 0x31
Server: State TCPOK Cipher N/A Ch 0xd4909118 TxQSize 0
LastTxLeft 0 Flags 0x8
| show phone-proxy signaling-sessions |
PhoneProxyASA# show phone-proxy signaling-sessions
outside 172.18.254.25:19931 inside 172.18.124.230:2000
Local Media (audio) conn: 172.18.254.25/22988 to 14.36.107.91/26830
Local SRTP key set : Remote SRTP key set
Remote Media (audio) conn: 14.36.107.91/26830 to 14.36.107.91/29724
outside 172.18.254.73:50124 inside 172.18.124.230:2000
Local Media (audio) conn: 172.18.254.73/29836 to 14.36.107.91/29724
Local SRTP key set : Remote SRTP key set
Remote Media (audio) conn: 14.36.107.91/29724 to 14.36.107.91/26830
PhoneProxyASA#
| show asp table classify domain app-redirect |
電話プロキシによって作成されたすべての app-redirect ルールを表示します。電話機が非セキュア電話機として設定された場合は、CUCM に対して各電話機にエントリが 1 つ必要です。
PhoneProxyASA# show asp table classify domain app-redirect
Interface _phone_proxy_ifc:
Interface inside:
Interface outside:
in id=0xd5b85918, priority=12, domain=app-redirect, deny=false
hits=1, user_data=0xd007, cs_id=0x0, flags=0x0, protocol=6
src ip=172.18.254.73, mask=255.255.255.255, port=0
dst ip=14.36.107.95, mask=255.255.255.255, port=2443, dscp=0x0
in id=0xd59f0d10, priority=12, domain=app-redirect, deny=false
hits=0, user_data=0xdc0e, cs_id=0x0, flags=0x0, protocol=6
src ip=172.18.254.73, mask=255.255.255.255, port=0
dst ip=14.36.107.95, mask=255.255.255.255, port=3804, dscp=0x0
in id=0xd5ba9a28, priority=12, domain=app-redirect, deny=false
hits=1, user_data=0xd007, cs_id=0x0, flags=0x0, protocol=6
src ip=172.18.254.25, mask=255.255.255.255, port=0
dst ip=14.36.107.95, mask=255.255.255.255, port=2443, dscp=0x0
in id=0xd59d8f58, priority=12, domain=app-redirect, deny=false
hits=0, user_data=0xdc0e, cs_id=0x0, flags=0x0, protocol=6
src ip=172.18.254.25, mask=255.255.255.255, port=0
dst ip=14.36.107.95, mask=255.255.255.255, port=3804, dscp=0x0
Interface identity:
Last clearing of hits counters: Never
PhoneProxyASA#
| show asp table classify domain inspect-phone-proxy |
設定済みの電話プロキシ TFTP サーバ宛のすべての TFTP トラフィックを、inspect-phone-proxy エンジンに配信する分類ルールを表示します。分類ルールには、特定のインターフェイスの TFTP サーバのグローバル アドレスが表示されます。電話プロキシがグローバルに適用された場合、電話プロキシが常駐するインターフェイスを除く各インターフェイスに分類ルールが必 要です。このルールは電話プロキシ設定が MPF でサービス ポリシーに適用されたときに作成され、ファイアウォール上の既存の変換設定に基づいてルールが作成されます。したがって、電話プロキシを設定して適用して から NAT 設定を配置すると、asp テーブル ルールは不正確になります(Call Manager のローカル IP(グローバル IP ではなく)が表示されます)。そのため、必ず nat を設定してから電話プロキシ mpf をサービス ポリシーに適用します。
PhoneProxyASA#show asp table classify domain inspect-phone-proxy
Interface _phone_proxy_ifc:
Interface inside:
Interface outside:
in id=0xd5ba1640, priority=73, domain=inspect-phone-proxy, deny=false
hits=4200, user_data=0xd59beff8, cs_id=0x0, reverse, flags=0x0, protocol=17
src ip=0.0.0.0, mask=0.0.0.0, port=0
dst ip=14.36.107.95, mask=255.255.255.255, port=69, dscp=0x0
in id=0xd59ca8b8, priority=73, domain=inspect-phone-proxy, deny=false
hits=0, user_data=0xd48b62b0, cs_id=0x0, reverse, flags=0x0, protocol=17
src ip=0.0.0.0, mask=0.0.0.0, port=0
dst ip=14.36.107.95, mask=255.255.255.255, port=69, dscp=0x0
Interface identity:
Last clearing of hits counters: Never
PhoneProxyASA#
| show conn | inc p |
TFTP トラフィックを検査する inspect-phone-proxy を通過する、すべての接続を表示します。
PhoneProxyASA# show conn | inc p
9 in use, 67 most used
UDP outside 172.18.254.25:8872 inside 172.18.124.230:32847, idle 0:00:02, bytes 4076, flags p-
UDP outside 172.18.254.25:62644 inside 172.18.124.230:39392, idle 0:00:03, bytes 4486, flags p-
TCP outside 172.18.124.241(172.18.254.25):29544 inside 172.18.124.230:2000, idle 0:00:01, bytes 894, flags UOB
UDP outside 172.18.254.25:8872 inside 172.18.124.230:69, idle 0:00:02, bytes 32, flags p-
UDP outside 172.18.254.25:62644 inside 172.18.124.230:69, idle 0:00:03, bytes 0, flags p-
TCP outside 172.18.124.241(172.18.254.73):50124 inside 172.18.124.230:2000, idle 0:00:14, bytes 22969, flags UIOB
PhoneProxyASA#
Syslog
電話プロキシ機能に関する新規 Syslog
%ASA-4-446001 - Maximum number of configured TLS proxy sessions reached
%ASA-4-446001: Maximum TLS Proxy session limit of max_sess reached.
%ASA-4-446002 - License exceeded
%ASA-4-446002: Denied TLS Proxy session from outside:10.10.10.2/49572 to inside:192.168.1.2/2000, licensed UC Proxy session limit of 20 exceeded
電話プロキシに接続された電話機の再起動および再接続時の Syslog 例
%ASA-5-305011: Built dynamic UDP translation from outside:172.18.254.73/53011 to
inside:172.18.124.241/60692
%ASA-6-302015: Built inbound UDP connection 4338 for outside:172.18.254.73/53011
(172.18.124.241/60692) to inside:172.18.124.230/69 (14.36.107.95/69)
%ASA-6-302015: Built inbound UDP connection 4339 for outside:172.18.254.73/53011
(172.18.124.241/60692) to inside:172.18.124.230/4677 (14.36.107.95/4677)
%ASA-7-111009: User 'enable_15' executed cmd: show logging
%ASA-6-305011: Built dynamic UDP translation from outside:172.18.254.73/53012 to
inside:172.18.124.241/63537
%ASA-6-302015: Built inbound UDP connection 4340 for outside:172.18.254.73/53012
(172.18.124.241/63537) to inside:172.18.124.230/69 (14.36.107.95/69)
%ASA-6-302015: Built inbound UDP connection 4341 for outside:172.18.254.73/53012
(172.18.124.241/63537) to inside:172.18.124.230/32851 (14.36.107.95/32851)
%ASA-6-305011: Built dynamic TCP translation from outside:172.18.254.73/50125 to
inside:172.18.124.241/37554
%ASA-6-302013: Built inbound TCP connection 4342 for outside:172.18.254.73/50125
(172.18.124.241/37554) to inside:172.18.124.230/2000 (14.36.107.95/2443)
%ASA-6-725001: Starting SSL handshake with client outside:172.18.254.73/50125 for TLSv1 session.
%ASA-7-725010: Device supports the following 4 cipher(s).
%ASA-7-725011: Cipher[1] : RC4-SHA
%ASA-7-725011: Cipher[2] : AES128-SHA
%ASA-7-725011: Cipher[3] : AES256-SHA
%ASA-7-725011: Cipher[4] : DES-CBC3-SHA
%ASA-7-725008: SSL client outside:172.18.254.73/50125 proposes the following 2 cipher(s).
%ASA-7-725011: Cipher[1] : AES256-SHA
%ASA-7-725011: Cipher[2] : AES128-SHA
%ASA-7-725012: Device chooses cipher : AES128-SHA for the SSL session with client
outside:172.18.254.73/50125
%ASA-7-717025: Validating certificate chain containing 1 certificate(s).
%ASA-7-717029: Identified client certificate within certificate chain.
serial number: 01, subject name: cn=SEP0007EBF0EE54.
%ASA-7-717030: Found a suitable trustpoint capf_trustpoint to validate certificate.
%ASA-6-717022: Certificate was successfully validated. serial number: 01,
subject name: cn=SEP0007EBF0EE54.
%ASA-6-717028: Certificate chain was successfully validated with warning,
revocation status was not checked.
%ASA-6-725002: Device completed SSL handshake with client outside:172.18.254.73/50125
%ASA-6-305011: Built dynamic TCP translation from outside:172.18.254.73/52675
to inside:172.18.124.241/45909
%ASA-7-711002: Task ran for 8 msec, Process = Dispatch Unit, PC = 8172a27, Traceback =
%ASA-7-711002: Task ran for 8 msec, Process = Dispatch Unit, PC = 8172a27,
Traceback = 0x08172A27 0x0805E983
%ASA-6-305012: Teardown dynamic TCP translation from outside:172.18.254.73/50124 to
inside:172.18.124.241/51711 duration 1:41:06
%ASA-6-305011: Built dynamic UDP translation from outside:172.18.254.73/53013 to
inside:172.18.124.241/58122
%ASA-6-302015: Built inbound UDP connection 4343 for outside:172.18.254.73/53013
(172.18.124.241/58122) to inside:172.18.124.230/69 (14.36.107.95/69)
%ASA-6-302015: Built inbound UDP connection 4344 for outside:172.18.254.73/53013
(172.18.124.241/58122) to inside:172.18.124.230/32852 (14.36.107.95/32852)
%ASA-7-111009: User 'enable_15' executed cmd: show logging
%ASA-6-305011: Built dynamic UDP translation from outside:172.18.254.73/53014 to
inside:172.18.124.241/54570
%ASA-6-302015: Built inbound UDP connection 4345 for outside:172.18.254.73/53014
(172.18.124.241/54570) to inside:172.18.124.230/69 (14.36.107.95/69)
%ASA-6-302015: Built inbound UDP connection 4346 for outside:172.18.254.73/53014
(172.18.124.241/54570) to inside:172.18.124.230/32853 (14.36.107.95/32853)
%ASA-6-305011: Built dynamic UDP translation from outside:172.18.254.73/53015 to
inside:172.18.124.241/63316
%ASA-6-302015: Built inbound UDP connection 4347 for outside:172.18.254.73/53015
(172.18.124.241/63316) to inside:172.18.124.230/69 (14.36.107.95/69)
%ASA-6-302015: Built inbound UDP connection 4348 for outside:172.18.254.73/53015
(172.18.124.241/63316) to inside:172.18.124.230/32854 (14.36.107.95/32854)
%ASA-7-111009: User 'enable_15' executed cmd: show logging
%ASA-7-111009: User 'enable_15' executed cmd: show logging
debug と出力例
debug phone-proxy tftp |
この debug は、ファイアウォールによってプロキシされる tftp セッションに関する情報を出力します。
PhoneProxyASA# debug phone-proxy tftp
PhoneProxyASA#
PhoneProxyASA# !- The phone is now rebooted
PhoneProxyASA#
PhoneProxyASA# PP: 172.18.254.25/37212 requesting CTLSEP0009B7D0EEA7.tlv
PP: opened 0x8685366
PP: Data Block 1 forwarded from 14.36.107.95/29840 to 172.18.254.25/37212 ingress ifc outside
PP: Received ACK Block 1 from outside:172.18.254.25/37212 to inside:172.18.124.230
PP: Data Block 2 forwarded to 172.18.254.25/37212
PP: Received ACK Block 2 from outside:172.18.254.25/37212 to inside:172.18.124.230
PP: Data Block 3 forwarded to 172.18.254.25/37212
PP: Received ACK Block 3 from outside:172.18.254.25/37212 to inside:172.18.124.230
PP: Data Block 4 forwarded to 172.18.254.25/37212
PP: Received ACK Block 4 from outside:172.18.254.25/37212 to inside:172.18.124.230
PP: Data Block 5 forwarded to 172.18.254.25/37212
PP: Received ACK Block 5 from outside:172.18.254.25/37212 to inside:172.18.124.230
PP: Data Block 6 forwarded to 172.18.254.25/37212
PP: Received ACK Block 6 from outside:172.18.254.25/37212 to inside:172.18.124.230
PP: Data Block 7 forwarded to 172.18.254.25/37212
PP: Received ACK Block 7 from outside:172.18.254.25/37212 to inside:172.18.124.230
PP: Data Block 8 forwarded to 172.18.254.25/37212
PP: Received ACK Block 8 from outside:172.18.254.25/37212 to inside:172.18.124.230
PP: Data Block 9 forwarded to 172.18.254.25/37212
PP: Received ACK Block 9 from outside:172.18.254.25/37212 to inside:172.18.124.230
PP: TFTP session complete, all data sent
PP: 172.18.254.25/53261 requesting SEP0009B7D0EEA7.cnf.xml.sgn
PP: opened 0x8693dd2
PP: Received Data Block 1 from inside:172.18.124.230/32851 to outside:172.18.254.25/53261
Received Block 1
PP: Acked Block #1 from 172.18.124.241/49633 to 172.18.124.230/32851
PP: Received Data Block 2 from inside:172.18.124.230/32851 to outside:172.18.254.25/53261
Received Block 2
PP: Acked Block #2 from 172.18.124.241/49633 to 172.18.124.230/32851
PP: Received Data Block 3 from inside:172.18.124.230/32851 to outside:172.18.254.25/53261
Received Block 3
PP: Acked Block #3 from 172.18.124.241/49633 to 172.18.124.230/32851
PP: Received Data Block 4 from inside:172.18.124.230/32851 to outside:172.18.254.25/53261
Received Block 4
PP: Acked Block #4 from 172.18.124.241/49633 to 172.18.124.230/32851
PP: Received Data Block 5 from inside:172.18.124.230/32851 to outside:172.18.254.25/53261
Received Block 5
PP: Acked Block #5 from 172.18.124.241/49633 to 172.18.124.230/32851
PP: Received Data Block 6 from inside:172.18.124.230/32851 to outside:172.18.254.25/53261
Received Block 6
PP: Acked Block #6 from 172.18.124.241/49633 to 172.18.124.230/32851
PP: Received Data Block 7 from inside:172.18.124.230/32851 to outside:172.18.254.25/53261
Received Block 7
PP: Acked Block #7 from 172.18.124.241/49633 to 172.18.124.230/32851
PP: Received Data Block 8 from inside:172.18.124.230/32851 to outside:172.18.254.25/53261
Received Block 8
PP: Acked Block #8 from 172.18.124.241/49633 to 172.18.124.230/32851
PP: Modifying to encrypted mode.
PP: Modifying to TLS as the transport layer protocol.
PP: Data Block 1 forwarded from 14.36.107.95/32851 to 172.18.254.25/53261
PP: Received ACK Block 1 from outside:172.18.254.25/53261 to inside:172.18.124.230
PP: Data Block 2 forwarded to 172.18.254.25/53261
PP: Received ACK Block 2 from outside:172.18.254.25/53261 to inside:172.18.124.230
PP: Data Block 3 forwarded to 172.18.254.25/53261
PP: Received ACK Block 3 from outside:172.18.254.25/53261 to inside:172.18.124.230
PP: Data Block 4 forwarded to 172.18.254.25/53261
PP: Received ACK Block 4 from outside:172.18.254.25/53261 to inside:172.18.124.230
PP: Data Block 5 forwarded to 172.18.254.25/53261
PP: Received ACK Block 5 from outside:172.18.254.25/53261 to inside:172.18.124.230
PP: Data Block 6 forwarded to 172.18.254.25/53261
PP: Received ACK Block 6 from outside:172.18.254.25/53261 to inside:172.18.124.230
PP: Data Block 7 forwarded to 172.18.254.25/53261
PP: Received ACK Block 7 from outside:172.18.254.25/53261 to inside:172.18.124.230
PP: Data Block 8 forwarded to 172.18.254.25/53261
PP: Received ACK Block 8 from outside:172.18.254.25/53261 to inside:172.18.124.230
PP: TFTP session complete, all data sent
PP: Retrieved MAC 0009.b7d0.eea7 from subject-name cn=SEP0009B7D0EEA7, mac string 0009B7D0EEA7
PP: Found phone device d5b94218
PP: 172.18.254.25/14201 requesting SEP0009B7D0EEA7.cnf.xml.sgn
PP: opened 0x86abd3a
PP: Received Data Block 1 from inside:172.18.124.230/32851 to outside:172.18.254.25/14201
Received Block 1
PP: Acked Block #1 from 172.18.124.241/6550 to 172.18.124.230/32851
PP: Received Data Block 2 from inside:172.18.124.230/32851 to outside:172.18.254.25/14201
Received Block 2
PP: Acked Block #2 from 172.18.124.241/6550 to 172.18.124.230/32851
PP: Received Data Block 3 from inside:172.18.124.230/32851 to outside:172.18.254.25/14201
Received Block 3
PP: Acked Block #3 from 172.18.124.241/6550 to 172.18.124.230/32851
PP: Received Data Block 4 from inside:172.18.124.230/32851 to outside:172.18.254.25/14201
Received Block 4
PP: Acked Block #4 from 172.18.124.241/6550 to 172.18.124.230/32851
PP: Received Data Block 5 from inside:172.18.124.230/32851 to outside:172.18.254.25/14201
Received Block 5
PP: Acked Block #5 from 172.18.124.241/6550 to 172.18.124.230/32851
PP: Received Data Block 6 from inside:172.18.124.230/32851 to outside:172.18.254.25/14201
Received Block 6
PP: Acked Block #6 from 172.18.124.241/6550 to 172.18.124.230/32851
PP: Received Data Block 7 from inside:172.18.124.230/32851 to outside:172.18.254.25/14201
Received Block 7
PP: Acked Block #7 from 172.18.124.241/6550 to 172.18.124.230/32851
PP: Received Data Block 8 from inside:172.18.124.230/32851 to outside:172.18.254.25/14201
Received Block 8
PP: Acked Block #8 from 172.18.124.241/6550 to 172.18.124.230/32851
PP: Modifying to encrypted mode.
PP: Modifying to TLS as the transport layer protocol.
PP: 172.18.254.25/47823 requesting RINGLIST.XML.sgn
PP: opened 0x86bf8f6
PP: Data Block 1 forwarded from 14.36.107.95/32851 to 172.18.254.25/14201
PP: Received Data Block 1 from inside:172.18.124.230/32851 to outside:172.18.254.25/47823
Received Block 1
PP: Acked Block #1 from 172.18.124.241/13065 to 172.18.124.230/32851
PP: Received Data Block 2 from inside:172.18.124.230/32851 to outside:172.18.254.25/47823
Received Block 2
PP: Acked Block #2 from 172.18.124.241/13065 to 172.18.124.230/32851
PP: Received ACK Block 1 from outside:172.18.254.25/14201 to inside:172.18.124.230
PP: Data Block 2 forwarded to 172.18.254.25/14201
PP: Received Data Block 3 from inside:172.18.124.230/32851 to outside:172.18.254.25/47823
Received Block 3
PP: Acked Block #3 from 172.18.124.241/13065 to 172.18.124.230/32851
PP: Received Data Block 4 from inside:172.18.124.230/32851 to outside:172.18.254.25/47823
Received Block 4
PP: Acked Block #4 from 172.18.124.241/13065 to 172.18.124.230/32851
PP: Received Data Block 5 from inside:172.18.124.230/32851 to outside:172.18.254.25/47823
Received Block 5
PP: Acked Block #5 from 172.18.124.241/13065 to 172.18.124.230/32851
PP: Data Block 1 forwarded from 14.36.107.95/32851 to 172.18.254.25/47823
PP: Received ACK Block 2 from outside:172.18.254.25/14201 to inside:172.18.124.230
PP: Data Block 3 forwarded to 172.18.254.25/14201
PP: Received ACK Block 1 from outside:172.18.254.25/47823 to inside:172.18.124.230
PP: Data Block 2 forwarded to 172.18.254.25/47823
PP: Received ACK Block 3 from outside:172.18.254.25/14201 to inside:172.18.124.230
PP: Data Block 4 forwarded to 172.18.254.25/14201
PP: Received ACK Block 2 from outside:172.18.254.25/47823 to inside:172.18.124.230
PP: Data Block 3 forwarded to 172.18.254.25/47823
PP: Received ACK Block 4 from outside:172.18.254.25/14201 to inside:172.18.124.230
PP: Data Block 5 forwarded to 172.18.254.25/14201
PP: Received ACK Block 3 from outside:172.18.254.25/47823 to inside:172.18.124.230
PP: Data Block 4 forwarded to 172.18.254.25/47823
PP: Received ACK Block 5 from outside:172.18.254.25/14201 to inside:172.18.124.230
PP: Data Block 6 forwarded to 172.18.254.25/14201
PP: Received ACK Block 4 from outside:172.18.254.25/47823 to inside:172.18.124.230
PP: Data Block 5 forwarded to 172.18.254.25/47823
PP: Received ACK Block 6 from outside:172.18.254.25/14201 to inside:172.18.124.230
PP: Data Block 7 forwarded to 172.18.254.25/14201
PP: Received ACK Block 5 from outside:172.18.254.25/47823 to inside:172.18.124.230
PP: TFTP session complete, all data sent
PP: Received ACK Block 7 from outside:172.18.254.25/14201 to inside:172.18.124.230
PP: Data Block 8 forwarded to 172.18.254.25/14201
PP: 172.18.254.25/56992 requesting DISTINCTIVERINGLIST.XML.sgn
PP: opened 0x86c9112
PP: Received ACK Block 8 from outside:172.18.254.25/14201 to inside:172.18.124.230
PP: TFTP session complete, all data sent
PP: Received Data Block 1 from inside:172.18.124.230/32851 to outside:172.18.254.25/56992
Received Block 1
PP: Acked Block #1 from 172.18.124.241/62582 to 172.18.124.230/32851
PP: Received Data Block 2 from inside:172.18.124.230/32851 to outside:172.18.254.25/56992
Received Block 2
PP: Acked Block #2 from 172.18.124.241/62582 to 172.18.124.230/32851
PP: Data Block 1 forwarded from 14.36.107.95/32851 to 172.18.254.25/56992
PP: Received ACK Block 1 from outside:172.18.254.25/56992 to inside:172.18.124.230
PP: Data Block 2 forwarded to 172.18.254.25/56992
PP: Received ACK Block 2 from outside:172.18.254.25/56992 to inside:172.18.124.230
PP: TFTP session complete, all data sent
PhoneProxyASA#
| debug phone-proxy media |
PhoneProxyASA# debug phone-proxy media
PhoneProxyASA#
PhoneProxyASA# !- A call is made from one phone to another
PhoneProxyASA#
PhoneProxyASA#
snp_client_sess_create: Creating client_sess 14.36.107.91/25752 172.18.254.73/24316
snp_media_sess_lock: locking media_sess 14.36.107.91/25752 1
Creating new media session in SNP 14.36.107.91/25752
Setting remote_side SRTP params in SNP 14.36.107.91/25752
SNP_SRTP::master_key and salt 1c9050bb8e388149b89b092e4dca2275 1c9050bb8e388149b89b092e4dca2275
snp_media_sess_lock: locking media_sess 14.36.107.91/25752 2
Rmt media is NULL 14.36.107.91/39012
Getting remote SRTP params in SNP 14.36.107.91/25752
snp_media_sess_lock: locking media_sess 14.36.107.91/25752 3
Remote SRTP params for 14.36.107.91/25752 already set
Setting local SRTP params in SNP 14.36.107.91/25752
SNP_SRTP::master_key and salt e8f9f25522578aff38d32d95895e40b4 e8f9f25522578aff38d32d95895e40b4
snp_client_sess_create: Creating client_sess 14.36.107.91/29668 172.18.254.25/17472
snp_media_sess_lock: locking media_sess 14.36.107.91/29668 1
Creating new media session in SNP 14.36.107.91/29668
Remote SRTP params for 14.36.107.91/25752 already set
Local SRTP params for 14.36.107.91/25752 already set
Setting remote_side SRTP params in SNP 14.36.107.91/29668
SNP_SRTP::master_key and salt e8f9f25522578aff38d32d95895e40b4 e8f9f25522578aff38d32d95895e40b4
snp_media_sess_lock: locking media_sess 14.36.107.91/25752 4
snp_media_sess_lock: locking media_sess 14.36.107.91/25752 5
snp_media_sess_lock: locking media_sess 14.36.107.91/29668 2
Getting remote SRTP params in SNP 14.36.107.91/29668
snp_media_sess_lock: locking media_sess 14.36.107.91/29668 3
Remote SRTP params for 14.36.107.91/29668 already set
Setting local SRTP params in SNP 14.36.107.91/29668
SNP_SRTP::master_key and salt 1c9050bb8e388149b89b092e4dca2275 1c9050bb8e388149b89b092e4dca2275
snp_media_sess_lock: locking media_sess 14.36.107.91/29668 4
snp_media_sess_lock: locking media_sess 14.36.107.91/29668 5
SNP_SRTP::Remote media_session found for 14.36.107.91/25752 lcl_ip/lcl_port 14.36.107.91/29668
SNP_SRTP::Setting rmt_pp_ip 14.36.107.91 for 14.36.107.91/25752
SNP_SRTP::Setting passthrough
SNP_SRTP::Setting client_port to sport 24316
SNP_SRTP::Remote media_session found for 14.36.107.91/29668 lcl_ip/lcl_port 14.36.107.91/25752
SNP_SRTP::Setting passthrough
SNP_SRTP::Setting client_port to sport 49114
PhoneProxyASA#
PhoneProxyASA# !- Call is now connected
PhoneProxyASA#
PhoneProxyASA# !- Call is hung up
PhoneProxyASA#
snp_media_sess_unlock: unlocking media_sess 14.36.107.91/25752 4
snp_media_sess_unlock: unlocking media_sess 14.36.107.91/25752 3
snp_media_sess_unlock: unlocking media_sess 14.36.107.91/29668 4
snp_media_sess_unlock: unlocking media_sess 14.36.107.91/29668 3
snp_media_sess_unlock: unlocking media_sess 14.36.107.91/25752 2
snp_media_sess_unlock: unlocking media_sess 14.36.107.91/25752 1
snp_media_sess_unlock: unlocking media_sess 14.36.107.91/29668 2
snp_media_sess_unlock: unlocking media_sess 14.36.107.91/29668 1
snp_media_sess_unlock: unlocking media_sess 14.36.107.91/25752 0
snp_media_sess_release: releasing media_sess 14.36.107.91/25752
snp_media_sess_unlock: unlocking media_sess 14.36.107.91/29668 0
snp_media_sess_release: releasing media_sess 14.36.107.91/29668
PhoneProxyASA#
| debug phone-proxy signaling |
PhoneProxyASA# debug phone-proxy signaling
PhoneProxyASA#
PhoneProxyASA#
PhoneProxyASA# ! One phone now calls another...
PhoneProxyASA#
PhoneProxyASA#
Inspect Skinny: generating SRTP key
PP_SIG:: Setting rmt SRTP params in pp_cl d5b943f8
PP_SIG::master_key and salt 013351f6a163735e469307253dfa4c11 013351f6a163735e469307253dfa4c11
Inspect Skinny: generating SRTP key
PP_SIG:: Setting rmt SRTP params in pp_cl d59db4d8
PP_SIG::master_key and salt 8704186bbb636c51079eb312e4d8d77d 8704186bbb636c51079eb312e4d8d77d
PP_SIG::pp_update_media_info: using conn's laddr 172.18.254.73/27754
PP_SIG::Updating lcl media info 172.18.254.73/27754
PP_SIG::Setting lcl_media_sess 14.36.107.91/29596
PP_SIG::Updating lcl PP media info 14.36.107.91/29596
PP_SIG:: calling np_media_sess_set_media_conns
PP_SIG::pp_update_media_info: Found media_sess 14.36.107.91/29596
Called np_nat_api_determine_location: 14.36.107.91/29596
PP_SIG::Updating rmt media info 14.36.107.91/29596
PP_SIG::Setting rmt_media_sess 14.36.107.91/29596
PP_SIG::Updating rmt PP media info 14.36.107.91/29596
PP_SIG:: Getting lcl SRTP params in pp_cl d59db4d8
PP_SIG::pp_update_media_info: using conn's laddr 172.18.254.25/20912
PP_SIG::Updating lcl media info 172.18.254.25/20912
PP_SIG::Setting lcl_media_sess 14.36.107.91/25654
PP_SIG::Updating lcl PP media info 14.36.107.91/25654
PP_SIG:: calling np_media_sess_set_media_conns
PP_SIG:: calling np_media_sess_set_media_conns
PP_SIG:: calling np_media_sess_set_media_conns
PP_SIG::pp_update_media_info: Found media_sess 14.36.107.91/25654
Called np_nat_api_determine_location: 14.36.107.91/25654
PP_SIG::Updating rmt media info 14.36.107.91/25654
PP_SIG::Setting rmt_media_sess 14.36.107.91/25654
PP_SIG::Updating rmt PP media info 14.36.107.91/25654
PP_SIG:: Getting lcl SRTP params in pp_cl d5b943f8
PP_SIG:: calling np_media_sess_set_media_conns
PP_SIG:: calling np_media_sess_set_media_conns
PhoneProxyASA#
PhoneProxyASA#
PhoneProxyASA#
PhoneProxyASA# !- Call is ended by called party
PhoneProxyASA#
PhoneProxyASA#
PP_SIG::pp_clear_lcl_media_ptr_values: calling media_sess_unlock on d59c35f8
PP_SIG::pp_clear_rmt_media_ptr_values: calling media_sess_unlock on d5b90218
PP_SIG::pp_clear_lcl_media_ptr_values: calling media_sess_unlock on d5b90218
PP_SIG::pp_clear_rmt_media_ptr_values: calling media_sess_unlock on d59c35f8
PhoneProxyASA#
-------------------------------------------------------------------------------------------------------------------
DOC-1226
検索バーにキーワード、フレーズ、または質問を入力し、お探しのものを見つけましょう
シスコ コミュニティをいち早く使いこなしていただけるよう役立つリンクをまとめました。みなさんのジャーニーがより良いものとなるようお手伝いします
下記より関連するコンテンツにアクセスできます