- Cisco Community
- シスコ コミュニティ
- ネットワークインフラストラクチャ
- [TKB] ネットワークインフラ ドキュメント
- Catalyst9000 : EVPN VXLAN L2 Overlay (バックツーバック入力レプリケーション)設定
- RSS フィードを購読する
- 新着としてマーク
- 既読としてマーク
- ブックマーク
- 購読
- 印刷用ページ
- 不適切なコンテンツを報告
- RSS フィードを購読する
- 新着としてマーク
- 既読としてマーク
- ブックマーク
- 購読
- 印刷用ページ
- 不適切なコンテンツを報告
2024-04-22 06:57 PM
はじめに
本ドキュメントでは、Catalyst においての、EVPN VXLAN L2 Overlay (バックツーバック入力レプリケーション)の設定について解説します。
本ドキュメントの検証にあたり、Cisco Modeling Labs ( CML )および cat9000v-17.11 を使用しています。
※ CML、cat9000v-17.11 の取得および使用方法については、本ドキュメントでは扱いません
Back-to-Back L2 VNI Configurations
Topology
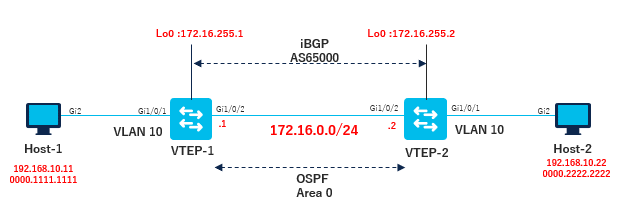
EVPN VXLAN L2 Overlay 設定
- VTEPでのL2 VPN EVPNの設定
- VTEPのVLANでのEVPNインスタンス設定
- VTEP の VLAN でのアクセス側インターフェイスの設定
- VTEP でのループバック インターフェイスの設定
- VTEP での NVE インターフェイスの設定
- EVPN アドレスファミリを使用した VTEP での BGP の設定
1. VTEPでのL2 VPN EVPNの設定
hostname VTEP-1
(snip)
!
l2vpn evpn
replication-type static
router-id Loopback1
!
l2vpn evpn instance 10 vlan-based
encapsulation vxlan
replication-type ingress
!
2. VTEPのVLANでのEVPNインスタンス設定
hostname VTEP-1
(snip)
!
vlan configuration 10 <<< 10 = vlan id
member evpn-instance 1 vni 10010
!
3. VTEP の VLAN でのアクセス側インターフェイスの設定
hostname VTEP-1
(snip)
!
interface GigabitEthernet1/0/1
switchport access vlan 10
switchport mode access
spanning-tree portfast
!
4.VTEP でのループバック インターフェイスの設定
hostname VTEP-1
(snip)
!
interface Loopback0
ip address 172.16.255.1 255.255.255.255
ip ospf 1 area 0
!
interface Loopback1
ip address 172.16.254.1 255.255.255.255
ip ospf 1 area 0
!
5. VTEP での NVE インターフェイスの設定
hostname VTEP-1
(snip)
!
interface nve1
no ip address
source-interface Loopback1
host-reachability protocol bgp
member vni 10010 ingress-replication
!
6. EVPN アドレスファミリを使用した VTEP での BGP の設定
hostname VTEP-1
(snip)
!
router ospf 1
router-id 172.16.255.1
!
router bgp 65000
no bgp log-neighbor-changes
neighbor 172.16.255.2 remote-as 65000
neighbor 172.16.255.2 update-source Loopback0
!
address-family ipv4
neighbor 172.16.255.2 activate
exit-address-family
!
address-family l2vpn evpn
neighbor 172.16.255.2 activate
neighbor 172.16.255.2 send-community both
exit-address-family
!
VXLANのカプセル化に50byteオーバーヘッドが発生するため、MTUを拡張
system mtu 8978
VTEP-1 Full Config
hostname VTEP-1
(snip)
!
l2vpn evpn
replication-type static
router-id Loopback1
!
l2vpn evpn instance 10 vlan-based
encapsulation vxlan
replication-type ingress
!
system mtu 8978
!
vlan configuration 10
member evpn-instance 10 vni 10010
!
interface Loopback0
ip address 172.16.255.1 255.255.255.255
ip ospf 1 area 0
!
interface Loopback1
ip address 172.16.254.1 255.255.255.255
ip ospf 1 area 0
!
interface GigabitEthernet1/0/1
switchport access vlan 10
switchport mode access
spanning-tree portfast
!
interface GigabitEthernet1/0/2
no switchport
ip address 172.16.0.1 255.255.255.0
ip ospf network point-to-point
ip ospf 1 area 0
!
interface nve1
no ip address
source-interface Loopback1
host-reachability protocol bgp
member vni 10010 ingress-replication
!
router ospf 1
router-id 172.16.255.1
!
router bgp 65001
no bgp log-neighbor-changes
neighbor 172.16.255.2 remote-as 65001
neighbor 172.16.255.2 update-source Loopback0
!
address-family ipv4
neighbor 172.16.255.2 activate
exit-address-family
!
address-family l2vpn evpn
neighbor 172.16.255.2 activate
neighbor 172.16.255.2 send-community both
exit-address-family
!
end
VTEP-2 Full Config
hostname VTEP-2
!
l2vpn evpn
replication-type static
router-id Loopback1
!
l2vpn evpn instance 10 vlan-based
encapsulation vxlan
replication-type ingress
!
system mtu 8978
!
vlan configuration 10
member evpn-instance 10 vni 10010
!
interface Loopback0
ip address 172.16.255.2 255.255.255.255
ip ospf 1 area 0
!
interface Loopback1
ip address 172.16.254.2 255.255.255.255
ip ospf 1 area 0
!
interface GigabitEthernet1/0/1
switchport access vlan 10
switchport mode access
spanning-tree portfast
!
interface GigabitEthernet1/0/2
no switchport
ip address 172.16.0.2 255.255.255.0
ip ospf network point-to-point
ip ospf 1 area 0
!
interface nve1
no ip address
source-interface Loopback1
host-reachability protocol bgp
member vni 10010 ingress-replication
!
router ospf 1
router-id 172.16.255.2
!
router bgp 65001
no bgp log-neighbor-changes
neighbor 172.16.255.1 remote-as 65001
neighbor 172.16.255.1 update-source Loopback0
!
address-family ipv4
neighbor 172.16.255.1 activate
exit-address-family
!
address-family l2vpn evpn
neighbor 172.16.255.1 activate
neighbor 172.16.255.1 send-community both
exit-address-family
!
end
確認コマンド
- show nve peers
- show bgp l2vpn evpn summary
- show bgp l2vpn evpn
- show l2vpn evpn mac evi 10
- show arp
Host-1 -> Host-2へのトラフィック送信時
show nve peers
ピアリーフスイッチの NVE インターフェイスの状態の情報を表示
- state UPを確認
VTEP-1#sh nve peers
'M' - MAC entry download flag 'A' - Adjacency download flag
'4' - IPv4 flag '6' - IPv6 flag
Interface VNI Type Peer-IP RMAC/Num_RTs eVNI state flags UP time
nve1 10010 L2CP 172.16.254.2 2 10010 UP N/A 00:01:03
show bgp l2vpn evpn summary
レイヤ 2 VPN EVPN アドレスファミリの BGP 情報を表示
- BGP Neighbor がUPしていることを確認
VTEP-1#sh bgp l2vpn evpn summary
(snip)
Neighbor V AS MsgRcvd MsgSent TblVer InQ OutQ Up/Down State/PfxRcd
172.16.255.2 4 65001 9 9 8 0 0 00:02:00 2
show bgp l2vpn evpn
BGP table にRoute Distinguisher: 172.16.255.2:10が登録されていることを確認
VTEP-1#sh bgp l2vpn evpn
(snip)
Network Next Hop Metric LocPrf Weight Path
Route Distinguisher: 172.16.254.1:10
*>i [2][172.16.254.1:10][0][48][000022222222][0][*]/20
172.16.254.2 0 100 0 ?
*> [2][172.16.254.1:10][0][48][525400073FF3][0][*]/20
0.0.0.0 32768 ?
*> [2][172.16.254.1:10][0][48][525400073FF3][128][FE80::5054:FF:FE07:3FF3]/36
0.0.0.0 32768 ?
Route Distinguisher: 172.16.254.2:10
*>i [2][172.16.254.2:10][0][48][000022222222][0][*]/20
172.16.254.2 0 100 0 ?
Route Distinguisher: 172.16.254.1:10
*> [3][172.16.254.1:10][0][32][172.16.254.1]/17
0.0.0.0 32768 ?
Network Next Hop Metric LocPrf Weight Path
*>i [3][172.16.254.1:10][0][32][172.16.254.2]/17
172.16.254.2 0 100 0 ?
Route Distinguisher: 172.16.254.2:10
*>i [3][172.16.254.2:10][0][32][172.16.254.2]/17
172.16.254.2 0 100 0 ?
show l2vpn evpn mac
VTEP-1#sh l2vpn evpn mac
MAC Address EVI VLAN ESI Ether Tag Next Hop(s)
-------------- ----- ----- ------------------------ ---------- ---------------
0000.1111.1111 10 10 0000.0000.0000.0000.0000 0 Gi1/0/1:10
0000.2222.2222 10 10 0000.0000.0000.0000.0000 0 172.16.254.2
5254.0007.3ff3 10 10 0000.0000.0000.0000.0000 0 Gi1/0/1:10
5254.000a.9468 10 10 0000.0000.0000.0000.0000 0 172.16.254.2
show arp
Host-1#ping 192.168.10.22
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.10.22, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 306/319/345 ms
Host-1#sh arp
Protocol Address Age (min) Hardware Addr Type Interface
Internet 192.168.10.11 - 0000.1111.1111 ARPA GigabitEthernet1
Internet 192.168.10.22 72 0000.2222.2222 ARPA GigabitEthernet1
関連記事
- 既読としてマーク
- 新着としてマーク
- ブックマーク
- ハイライト
- 印刷
- 不適切なコンテンツを報告
- 既読としてマーク
- 新着としてマーク
- ブックマーク
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Appreciate it if you'd possibly post your question in Japanese.
- 既読としてマーク
- 新着としてマーク
- ブックマーク
- ハイライト
- 印刷
- 不適切なコンテンツを報告
- 既読としてマーク
- 新着としてマーク
- ブックマーク
- ハイライト
- 印刷
- 不適切なコンテンツを報告
こんにちは。翻訳による日本語での問い合わせということで十分にご質問内容を把握できていないかも
しれませんが、SD-Access に近い内容のアプローチをご検討いただいているのかと推測しております。
SD-Access に関しては、以下にドキュメントがございます。以下をご参照の上、詳細をご確認いただけ
ればと存じます。
Cisco SD-Access Solution Design Guide (CVD)
https://www.cisco.com/c/en/us/td/docs/solutions/CVD/Campus/cisco-sda-design-guide.html
検索バーにキーワード、フレーズ、または質問を入力し、お探しのものを見つけましょう
シスコ コミュニティをいち早く使いこなしていただけるよう役立つリンクをまとめました。みなさんのジャーニーがより良いものとなるようお手伝いします
下記より関連するコンテンツにアクセスできます