- Cisco Community
- Technology and Support
- Security
- VPN
- Re: Anyconnect 3.1 and user certificate-based authentication
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Anyconnect 3.1 and user certificate-based authentication
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2014 06:40 AM - edited 02-21-2020 07:30 PM
Hi experts,
I'm trying to test a basic full tunnel VPN connection from Anyconnect 3.1 installed on a Windows 7 machine to a Cisco ASA, using only certificate authentication.
Steps i took:
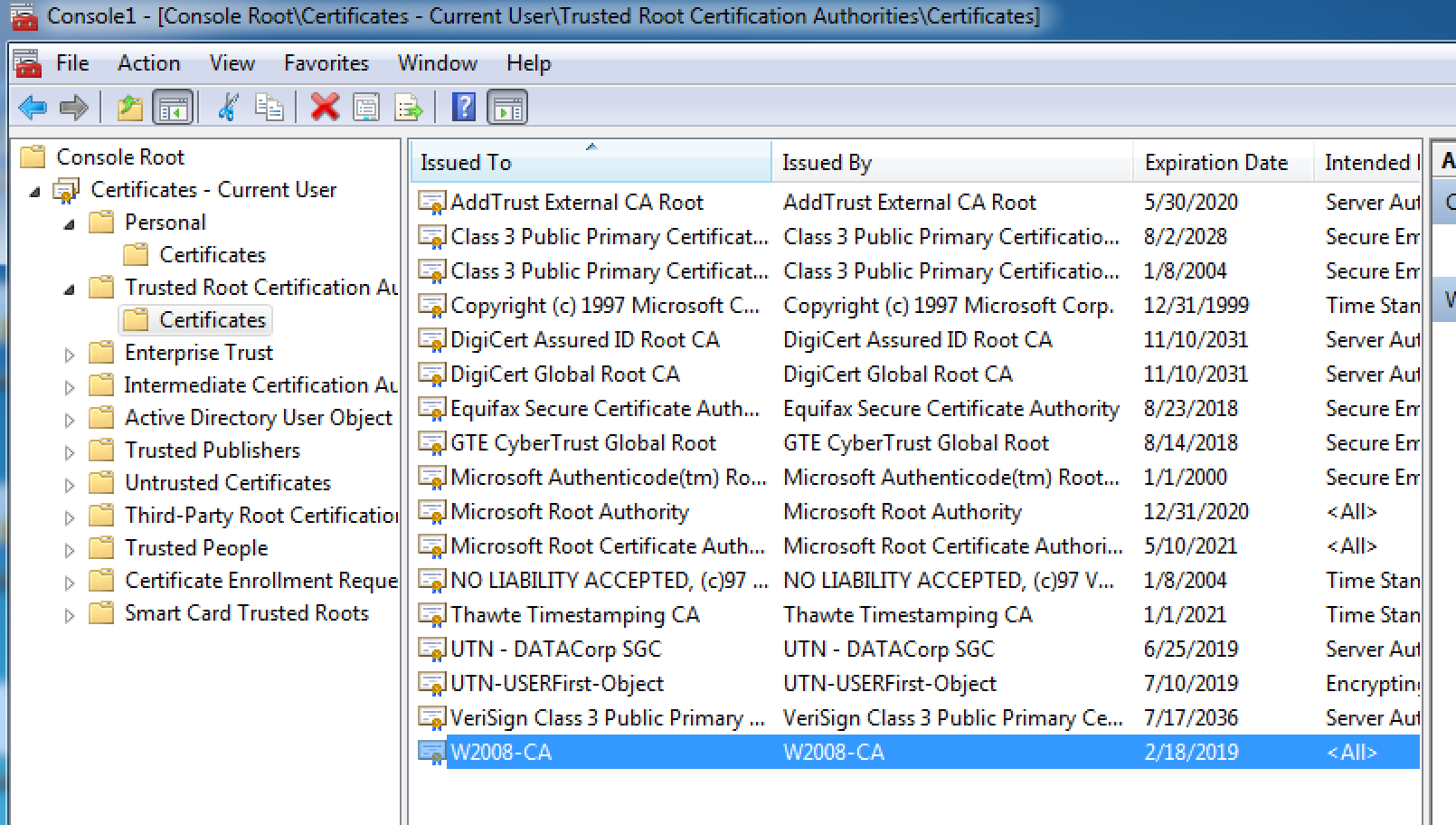
1) I've created a Windows 2008 certificate authority for testing, and imported the root CA certificate into both the Windows 7 client and into Cisco ASA
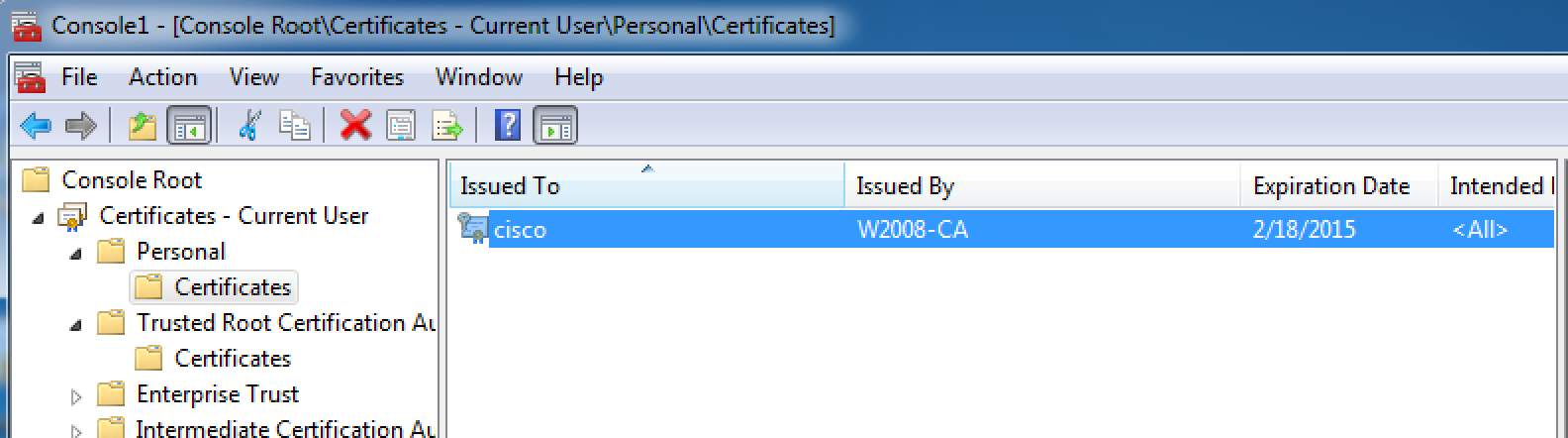
2) I generated a certificate signing request on the W7 client, got that signed by W2008 CA and imported the signed certificate into W7. Both user certificate and root CA are in the personal certificate store
3) On ASA, I've also generated a certificate signing request, got that signed by W2008 CA and imported the signed certificate back in ASA
I then used ASDM to configure ASA to support Anyconnect on its untrust interface.
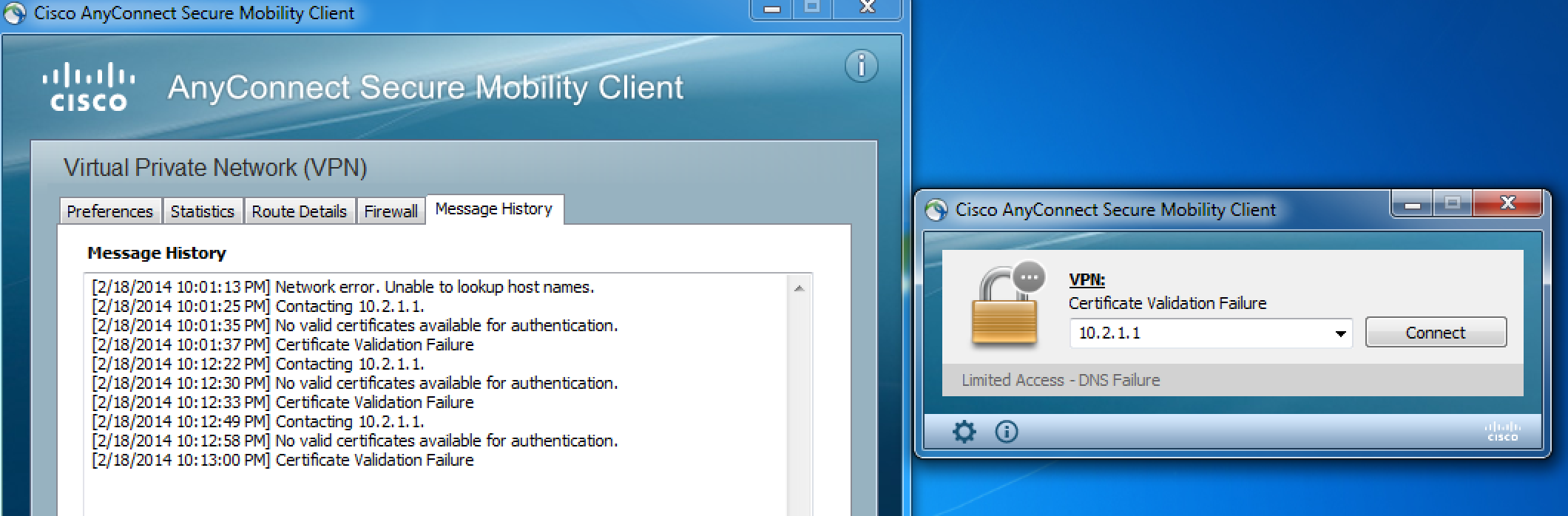
When I use Anyconnect on the W7 client to connect to ASA, I got "No valid certificates available for authentication" and "certificate validation failure" messages as seen in the below screenshot
I can confirm that both user and root CA certificate exist in the personal certificate store
The corresponding ASA configuration and debug output are shown in the attached txt file. On the ASA, I've made sure its ID certificate has CN=<public IP of ASA> since I don't have a DNS setup in place.
Can anyone suggest what could be wrong with my setup?
- Labels:
-
AnyConnect
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2014 08:30 AM
I believe the root CA certificate should go in your client's trusted root CA store. Your text doesn't say that but the screenshots indicate you have.
On the ASA, have you setup the SSL Settings (Configuration > Remote Access VPN > Advanced > SSL Settings) to bind the Trustpoint to the interface?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2014 08:14 PM
Hi Marvin,
Yes the root CA certificate is in the trusted root CA store of the W7 client's personal certificate store. I have also bound the trustpoint to the untrust interface.
crypto ca trustpoint ASA-ID-TP
enrollment terminal
fqdn 10.2.1.1
subject-name CN=10.2.1.1
crl configure
ssl trust-point ASA-ID-TP untrust
I'll try to see if I can get anything from DART..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-18-2014 10:49 PM
Problem has been fixed by using IP address instead of hostname in the Anyconnect Client profile, since I don't have a DNS setup in my environment.

Once that is done I was able to connect and authenticate using user certificates.
ASA1# sh vpn-sessiondb detail anycon
Session Type: AnyConnect Detailed
Username : cisco Index : 2
Assigned IP : 10.5.1.100 Public IP : 10.3.1.10
Protocol : IKEv2 IPsecOverNatT AnyConnect-Parent
License : AnyConnect Premium
Encryption : AES256 Hashing : none SHA1
Bytes Tx : 0 Bytes Rx : 30758
Pkts Tx : 0 Pkts Rx : 195
Pkts Tx Drop : 0 Pkts Rx Drop : 0
Group Policy : GroupPolicy_VPN-CP1 Tunnel Group : VPN-CP1
Login Time : 06:40:49 UTC Wed Feb 19 2014
Duration : 0h:07m:38s
Inactivity : 0h:00m:00s
NAC Result : Unknown
VLAN Mapping : N/A VLAN : none
IKEv2 Tunnels: 1
IPsecOverNatT Tunnels: 1
AnyConnect-Parent Tunnels: 1
AnyConnect-Parent:
Tunnel ID : 2.1
Public IP : 10.3.1.10
Encryption : none Auth Mode : Certificate
Idle Time Out: 30 Minutes Idle TO Left : 22 Minutes
Client Type : AnyConnect
Client Ver : 3.1.05152
IKEv2:
Tunnel ID : 2.2
UDP Src Port : 50530 UDP Dst Port : 4500
Rem Auth Mode: Certificate
Loc Auth Mode: rsaCertificate
Encryption : AES256 Hashing : SHA1
Rekey Int (T): 86400 Seconds Rekey Left(T): 85941 Seconds
PRF : SHA1 D/H Group : 5
Filter Name :
Client OS : Windows
IPsecOverNatT:
Tunnel ID : 2.3
Local Addr : 0.0.0.0/0.0.0.0/0/0
Remote Addr : 10.5.1.100/255.255.255.255/0/0
Encryption : AES256 Hashing : SHA1
Encapsulation: Tunnel
Rekey Int (T): 28800 Seconds Rekey Left(T): 28341 Seconds
Rekey Int (D): 4608000 K-Bytes Rekey Left(D): 4607970 K-Bytes
Idle Time Out: 30 Minutes Idle TO Left : 29 Minutes
Bytes Tx : 0 Bytes Rx : 31218
Pkts Tx : 0 Pkts Rx : 196
NAC:
Reval Int (T): 0 Seconds Reval Left(T): 0 Seconds
SQ Int (T) : 0 Seconds EoU Age(T) : 459 Seconds
Hold Left (T): 0 Seconds Posture Token:
Redirect URL :
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-21-2018 12:29 AM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide

