- Cisco Community
- Technology and Support
- Security
- VPN
- ipsec site to site vpn - tunnel up but unable to ping peer
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ipsec site to site vpn - tunnel up but unable to ping peer
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-24-2020 05:37 AM - edited 11-24-2020 02:57 PM
Hi All,
Im new to Cisco and hope that someone more knowledgeable can find out what I'm missing.
I have a site to site VPN configured from Head office to branch office(just concentration on branch office Site C - 30.30.30.30).
The VPN configured on the head office is on a CISCO router.
The branch office is a Sophos XG firewall. Im able to ping CISCO router from branch office so that confirms that the VPN is up and running.
In the head office, im not able to ping branch office resources.
| Current configuration : 6987 bytes |
| ! |
| version 15.6 |
| service timestamps debug datetime msec |
| service timestamps log datetime msec |
| no service password-encryption |
| ! |
| hostname headofficerouter |
| ! |
| boot-start-marker |
| boot-end-marker |
| ! |
| ! |
| enable secret 5 abcd |
| enable password pqrs |
| ! |
| aaa new-model |
| ! |
| ! |
| aaa authentication login userauthen local |
| aaa authorization network groupauthor local |
| ! |
| aaa session-id common |
| clock timezone WST 8 0 |
| no ip domain lookup |
| ip domain name mydomain.com |
| ip cef |
| no ipv6 cef |
| ! |
| ! |
| ! |
| ! |
| ! |
| multilink bundle-name authenticated |
| ! |
| ! |
| chat-script lte "" "AT!SCACT=1,1" TIMEOUT 60 "OK" |
| ! |
| ! |
| ! |
| ! |
| ! |
| license udi pid C899G-LTE-LA-K9 sn FGL223910M4 |
| ! |
| ! |
| username user1 privilege 15 secret 5 secret |
| username user2 password 0 secret |
| username user3 privilege 15 secret 5 secret |
| ! |
| redundancy |
| ! |
| ! |
| ! |
| ! |
| ! |
| controller Cellular 0 |
| lte modem link-recovery rssi onset-threshold -110 |
| lte modem link-recovery monitor-timer 20 |
| lte modem link-recovery wait-timer 10 |
| lte modem link-recovery debounce-count 6 |
| ! |
| track 1 interface Dialer0 ip routing |
| crypto isakmp policy 10 |
| encr 3des |
| hash md5 |
| authentication pre-share |
| group 2 |
| ! |
| crypto isakmp policy 11 |
| encr 3des |
| hash md5 |
| authentication pre-share |
| group 2 |
| ! |
| crypto isakmp policy 12 |
| encr 3des |
| hash md5 |
| authentication pre-share |
| group 2 |
| ! |
| crypto isakmp policy 13 |
| encr 3des |
| hash md5 |
| authentication pre-share |
| group 2 |
| crypto isakmp key siteAsecret address 10.10.10.10 no-xauth |
| crypto isakmp key siteBsecret address 20.20.20.20 no-xauth |
| crypto isakmp key siteCsecret address 30.30.30.30 no-xauth |
| ! |
| crypto isakmp client configuration group ispname |
| key ispkey |
| dns 192.168.10.220 |
| domain admin.domain.com |
| pool ippool |
| acl 108 |
| ! |
| ! |
| crypto ipsec transform-set tripledes esp-3des esp-md5-hmac |
| mode tunnel |
| ! |
| ! |
| ! |
| crypto dynamic-map dynmap 10 |
| set transform-set tripledes |
| crypto map combined client authentication list userauthen |
| crypto map combined isakmp authorization list groupauthor |
| crypto map combined client configuration address respond |
| crypto map combined 10 ipsec-isakmp |
| set peer 10.10.10.10 |
| set transform-set tripledes |
| match address 101 |
| crypto map combined 11 ipsec-isakmp |
| set peer 20.20.20.20 |
| set transform-set tripledes |
| match address 102 |
| crypto map combined 12 ipsec-isakmp |
| set peer 30.30.30.30 |
| set transform-set tripledes |
| match address 103 |
| crypto map combined 13 ipsec-isakmp dynamic dynmap |
| ! |
| ! |
| ! |
| ! |
| ! |
| ! |
| interface Loopback0 |
| ip address 1.1.1.1 255.255.255.0 |
| ! |
| interface Cellular0 |
| ip address negotiated |
| encapsulation slip |
| dialer in-band |
| dialer idle-timeout 0 |
| dialer string lte |
| dialer-group 1 |
| ipv6 enable |
| pulse-time 1 |
| ! |
| interface Cellular1 |
| no ip address |
| encapsulation slip |
| ! |
| interface GigabitEthernet0 |
| no ip address |
| ! |
| interface GigabitEthernet1 |
| no ip address |
| interface GigabitEthernet2 |
| no ip address |
| ! |
| interface GigabitEthernet3 |
| no ip address |
| ! |
| interface GigabitEthernet4 |
| no ip address |
| ! |
| interface GigabitEthernet5 |
| no ip address |
| ! |
| interface GigabitEthernet6 |
| no ip address |
| ! |
| interface GigabitEthernet7 |
| no ip address |
| ! |
| interface GigabitEthernet8 |
| no ip address |
| shutdown |
| duplex auto |
| speed auto |
| ! |
| interface GigabitEthernet9 |
| no ip address |
| duplex auto |
| speed auto |
| pppoe enable group global |
| pppoe-client dial-pool-number 1 |
| ! |
| interface Vlan1 |
| ip address 192.168.10.254 255.255.255.0 |
| ip nat inside |
| ip virtual-reassembly in |
| no ip route-cache |
| ip policy route-map lanvpn |
| interface Dialer0 |
| description WAN Interface |
| mtu 1492 |
| ip address negotiated |
| ip access-group 100 out |
| no ip redirects |
| no ip unreachables |
| no ip proxy-arp |
| ip mtu 1480 |
| ip flow ingress |
| ip nat outside |
| ip virtual-reassembly in |
| encapsulation ppp |
| dialer pool 1 |
| dialer-group 1 |
| ppp authentication chap callin |
| ppp chap hostname xxxx.com |
| ppp chap password 0 xxsecret |
| ppp pap sent-username xxxx.com password 0 xxsecret |
| no cdp enable |
| crypto map combined |
| ! |
| ip local pool ippool 192.168.14.10 192.168.14.15 |
| ip forward-protocol nd |
| no ip http server |
| no ip http secure-server |
| ! |
| ! |
| no ip nat service sip udp port 5060 |
| ip nat inside source route-map nonat interface Dialer0 overload |
| ip nat inside source static tcp 192.168.10.145 25 100.100.100.100 25 extendable |
| ip nat inside source static tcp 192.168.5.100 80 100.100.100.100 80 extendable |
| ip nat inside source static tcp 192.168.5.100 443 100.100.100.100 443 extendable |
| ip nat inside source static tcp 192.168.10.145 110 100.100.100.100 7110 extendable |
| ip nat inside source static tcp 192.168.10.243 8080 100.100.100.100 8080 extendable |
| ip route 0.0.0.0 0.0.0.0 Dialer0 track 1 |
| ip route 0.0.0.0 0.0.0.0 Cellular0 5 |
| ip route 192.168.5.0 255.255.255.0 192.168.10.253 |
| ip route 192.192.187.0 255.255.255.0 Cellular0 |
| ! |
| ip sla 1 |
| icmp-echo 8.8.8.8 |
| ip sla schedule 1 life forever start-time now |
| dialer-list 1 protocol ip permit |
| ipv6 ioam timestamp |
| ! |
| route-map nonat permit 10 |
| match ip address 105 |
| access-list 1 remark Rick Vincent Home machine |
| access-list 1 permit 203.161.100.98 |
| access-list 1 remark Telnet access list |
| access-list 1 permit 192.168.10.0 0.0.0.255 |
| access-list 100 remark Outside interface allows |
| access-list 100 permit ip any any |
| access-list 101 remark SiteA VPN Access list |
| access-list 101 permit ip 192.168.10.0 0.0.0.255 192.168.11.0 0.0.0.255 |
| access-list 102 remark SiteB VPN access list |
| access-list 102 permit ip 192.168.10.0 0.0.0.255 192.168.12.0 0.0.0.255 |
| access-list 103 remark SiteC VPN access list |
| access-list 103 permit ip 192.168.10.0 0.0.0.255 192.168.13.0 0.0.0.255 |
| access-list 104 permit ip 192.168.10.0 0.0.0.255 10.0.0.0 0.255.255.255 |
| access-list 105 deny ip 192.168.10.0 0.0.0.255 192.168.11.0 0.0.0.255 |
| access-list 105 deny ip 192.168.10.0 0.0.0.255 192.168.12.0 0.0.0.255 |
| access-list 105 deny ip 192.168.10.0 0.0.0.255 192.168.13.0 0.0.0.255 |
| access-list 105 deny ip 192.168.10.0 0.0.0.255 192.168.14.0 0.0.0.255 |
| access-list 105 permit ip 192.168.10.0 0.0.0.255 any |
| access-list 105 permit ip 192.168.5.0 0.0.0.255 any |
| access-list 108 permit ip 192.168.10.0 0.0.0.255 192.168.14.0 0.0.0.255 |
| access-list 120 permit ip 192.168.10.0 0.0.0.255 192.168.11.0 0.0.0.255 |
| access-list 120 permit ip 192.168.10.0 0.0.0.255 192.168.12.0 0.0.0.255 |
| access-list 120 permit ip 192.168.10.0 0.0.0.255 192.168.13.0 0.0.0.255 |
| access-list 120 permit ip 192.168.10.0 0.0.0.255 192.168.14.0 0.0.0.255 |
| ! |
| ! |
| ! |
| control-plane |
| ! |
| ! |
| ! |
| mgcp behavior rsip-range tgcp-only |
| mgcp behavior comedia-role none |
| mgcp behavior comedia-check-media-src disable |
| mgcp behavior comedia-sdp-force disable |
| ! |
| mgcp profile default |
| ! |
| ! |
| ! |
| ! |
| ! |
| ! |
| vstack |
| ! |
| line con 0 |
| no modem enable |
| line aux 0 |
| line 2 |
| no activation-character |
| no exec |
| transport preferred none |
| stopbits 1 |
| line 3 |
| exec-timeout 0 0 |
| script dialer lte |
| modem InOut |
| no exec |
| transport input all |
| transport output all |
| rxspeed 150000000 |
| txspeed 50000000 |
| line 8 |
| no exec |
| line vty 0 4 |
| privilege level 15 |
| transport input ssh |
| ! |
| scheduler allocate 20000 1000 |
With this config, when i run a ping to 192.168.13.254 (Router at Site C), i get the follwoing:
#ping 192.168.13.254
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.13.254, timeout is 2 seconds:
.....
Success rate is 0 percent (0/5)
- Labels:
-
IPSEC
-
Other VPN Topics
-
Remote Access
-
VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-24-2020 07:55 PM - edited 11-25-2020 04:49 AM
....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-25-2020 11:51 AM - edited 11-25-2020 12:14 PM
Hi friend
Can I see route table of HQ router ?
second do these step
1-clear access-list counter in HQ
2-do ping from HQ to SiteC (note use source)
3- show access-list, here please share the output.
normal the access-lit will show hit in route-map (deny for SiteC) and IPSec ACL (permit for SiteC).
please share output here.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-25-2020 01:59 PM - edited 11-25-2020 01:59 PM
Given you can reach the endpoints behind the HQ router from the remote site, this suggests the VPN tunnel is healthy and working. However, the issue seems to be that the Sophos XG firewall is denying the traffic initiated from the HQ. I would check with the XG admins to ensure there are no ACLs/security policies denying the traffic coming from the HQ.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-26-2020 06:34 AM
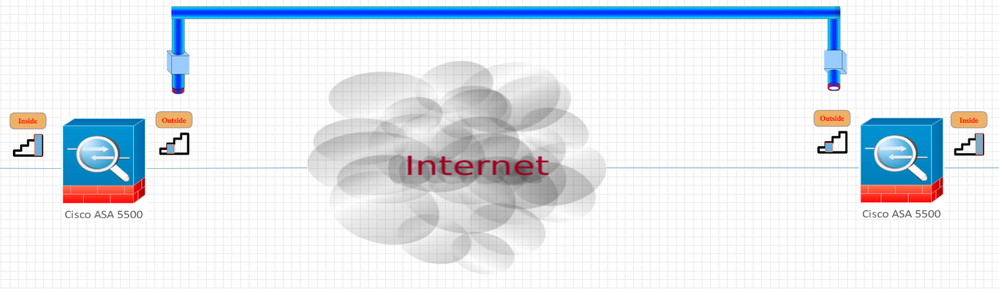
this photo to just to make understand the issue here.
I have some thing to share here please check this is other side of Router.
Sophos FW send the traffic to HQ no issue. (I make lan in GNS3 use router and there is no any issue with config).
HQ send traffic to Sophos FW the traffic drop!!
if the traffic not encrypt by router then by show crypto ipsec sa we can see error counter increase for each ping.
the traffic is encrypt by router and send to FW.
FW here decrypt the traffic and send it to LAN behind it...here the trick
the FW to protect LAN behind and hence the traffic is drop there.
so make the FW allow ICMP from LAN of HQ to LAN behind the FW.
hope this solve your issue and please mention that this issue solved.
- « Previous
-
- 1
- 2
- Next »
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide