- Cisco Community
- Technology and Support
- Security
- VPN
- Multiple peers Crypto Map Issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Multiple peers Crypto Map Issue
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-27-2018 06:26 AM - edited 09-27-2018 06:28 AM
Hi Everyone,
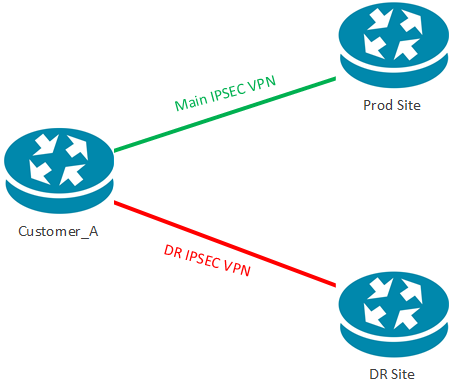
I run to an issue with GRE over IPSec, Same GRE tunnel configuration on (Prod & DR stite) different IPSec peers
we are not using the tunnel source as IPsec peer, the customer configure 2 crypto map entries for our 2 peers, the IPsec to our Prod site worked successfully, when i shutdown the Tunnel at Prod site, and unshut the tunnel at the DR site, IPsec not formed and Tunnel is up down. i tired to clear P1 P2 session, but to worked
Note: P1 is up to our IPSec peers, it should be UP for 1 peer only.
for customer perspective he sees us as one site.
crypto map MAP_A 10 ipsec-isakmp
set peer 10.10.10.253
set transform-set Sky_TS
match address Sky_ACL
!
crypto map MAP_B 15 ipsec-isakmp
set peer 10.10.10.254
set transform-set Sky_TS
match address Sky_ACL
!
But with below configs, (multiple peers in the same crypto map), i switched back and forth the IPSEC worked, any idea?
crypto map MAP_A 10 ipsec-isakmp
set peer 10.10.10.253
set peer 10.10.10.254
set transform-set Sky_TS
match address Sky_ACL
- Labels:
-
VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-28-2018 11:03 AM
Do you have different GRE tunnel interfaces for prod and DR tunnels? If that is the case, the ACL "Sky_ACL" should be different on the crypto map. Since you have the same ACL configured, the router will only try to establish a IPsec tunnel to the first peer (first match rule). You should ideally have 2 different and unique ACL's (plus add some dynamic routing) if you want to achieve failover.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-29-2018 04:08 AM
Hi Rahul
we have identical configs on both sites but different IPsec Peers, from the customer perspective he sees us as one site, i was wondering why this configs works:
2 peers in one crypto map
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-01-2018 03:51 AM - edited 10-01-2018 04:01 AM
2 Peers would work because you have only 1 crypto map entry, hence the traffic can only match that crypto map entry. When you have 2 crypto map entries, it matches crypto entries one by one. So it will always match sequence 1. As mentioned before, if you want to build 2 separate tunnels, keep the crypto ACL's unique so that it not conflict with each other.
Since you are using GRE tunnels, you can have 2 different tunnel interfaces where the tunnel source and destination combination is unique. For example:
int Tunnel1
tunnel source <ISP interface>
tunnel destination 10.10.10.253
int Tunnel 2
tunnel source <ISP interface>
tunnel destination 10.10.10.254
access-list Sky_ACL1 permit gre <isp interface> 10.10.10.253
access-list Sky_ACL2 permit gre <isp interface> 10.10.10.254
crypto map MAP_A 10 ipsec-isakmp
set peer 10.10.10.253
set transform-set Sky_TS
match address Sky_ACL1
!
crypto map MAP_B 15 ipsec-isakmp
set peer 10.10.10.254
set transform-set Sky_TS
match address Sky_ACL2
You can then send routing protocol through Tunnel 1 and 2 with the right metrics to prefer Tunnel1 to Primary site.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide