- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- IPv6 support on the Wireless Lan Controller (WLC)
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
03-11-2011 01:16 PM - edited 11-18-2020 02:53 AM
Introduction
Information related to IPv6 support on the Wireless LAN Controller (WLC). Prior to WLC 6.0 release, IPv6 pass-thru is only supported but no L2 security can be enabled on IPv6 WLAN. With WLC 6.0 release and later, IPv6 pass-thru with Layer-2 security supported.
Same Wireless LAN (WLAN) can support both IPv4 and IPv6 clients. IPv6 pass-thru and IPv4 Web auth is also supported on same WLAN. IPv6 is not supported with guest mobility anchor tunneling.
Since controller is a L2 device, no IPv4 or IPv6 routing is supported on WLC controller. that is the reason wireless LAN controller support only bridging mode.
Below is the configuration guide which references IPv6 support.
Configuring IPv6 Bridging
Currently, the 4400 and 4100 series controllers only support IPv6 client pass-through.
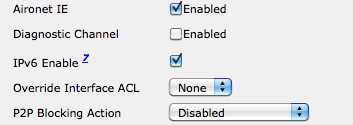
Native IPv6 support is not supported. In order to enable IPv6 on the WLC, check the IPv6 Enable check box on the WLAN SSID configuration under the WLAN> Edit page.
Also, Ethernet Multicast Mode (EMM) is required to support IPv6. If you disable EMM, client devices that use IPv6 lose connectivity. In order to enable EMM, go to the Controller > General page and from the Ethernet Multicast Mode drop down menu, choose Unicast or Multicast.This enables multicast either in Unicast mode or Multicast mode. When multicast is enabled as multicast unicast, packets are replicated for each AP. This can be processor intensive, so use it with caution. Multicast enabled as multicast uses the user assigned multicast address to do a more traditional multicast out to the access points (APs).
IPv6 pass-through Feature is Not Supported on 2100 Series Controllers
Also, there is Cisco bug ID CSCsg78176 (IPv6 pass through is broken with interface assignment and AAA Override), which prevents using IPv6 pass-through when the AAA Override feature is used.
IPv6 Support on WLC and LAP for Release 7.2.103.0
IPv6/Dual Stack Client Support
This section describes new features that have been introduced as part of the IPv6 feature enhancements.
IPv6 Client Mobility
'Intelligent IPv6 Packet Processing enables seamless layer 2 and layer 3 roaming support for both dual stack and IPv6 only client. This feature enables reliable connectivity while roaming.
Note
![]() Cisco 2500 Series Controller requires Multicast-Multicast mode to be enabled with a valid Multicast IP address for IPv6 Client Support.
Cisco 2500 Series Controller requires Multicast-Multicast mode to be enabled with a valid Multicast IP address for IPv6 Client Support.
IPv6 Security
First-hop security features, including RA Guard automatically blocks rogue router announcements from the controller and access point. Source guard, DHCPv6 Server guard, and IPv6 Access Control List are supported in controller. This feature enables increased network availability and lower operational costs by proactively blocking known threats.
IPv6 Client Management
IPv6 addresses visibility on a per client basis, system-wide IP version distribution, and trends from NCS. This feature enables network administrators to perform IPv6 troubleshooting, address planning, client traceability, and so on from a common wired and wireless management system.
IPv6 Packet Optimization
Intelligent packet processing through NDP proxy and rate limiting of chatty IPv6 packets. This feature enables increased radio efficiency and reduces CPU utilization in the router.
New Release 7.6.110.0 support
- From release Notes for Cisco Wireless LAN Controllers and Lightweight Access Points for Release 7.6.110.0, PMIPv6 Feature is Not Supported on Cisco 2500 Series WLCs
- IPv6/Dual Stack client visibility and PMIPv6 feature is Not Supported on Cisco Flex 7500 WLCs but IPv6 client bridging and Router Advertisement Guard are supported.
- IPv6, PMIPv6 Feature is Not Supported on Cisco Virtual WLCs
Open Caveats
CSCuc02149 | Symptom : AP3600 in either autonomous IOS or FlexConnect local switching mode drops IP6to4 TCP SYN ACK packets that are received from its LAN port. A wired sniff at the AP port shows, when the wireless client attempts to establish a TCP connection over IPv6 in IPv4, that the AP transmits the TCP SYN (in IPv6 in IPv4) to the switch, and receives the SYN ACK from the switch, but fails to forward the SYN ACK packet to the wireless client. The first time that the AP, after a reload, drops the SYN ACK packet, the following message will be seen on the AP console, or in its log file: WARNING - Received pak from RXTX port - Check log for detailed information At the same time, the wireless client can successfully ping the IPv6 address of its 6to4 gateway. Conditions : AP3600 or AP2600 in autonomous or FlexConnect local switching mode. Wireless client is attempting to establish TCP connections over IPv6 in IPv4, that is IPv4 protocol type 41. Workaround : 1. 2. 3. |
CSCub89883 | Symptom : Crash in different tasks after enabling guest LAN. Conditions : Guest LAN on a 5500 series controller using 7.2 or later software releases with IPv6 traffic from clients. Workaround : Disable guest LAN or disable IPv6. |
CSCub89883 | Symptom : System is unresponsive in different tasks after guest LAN is enabled. Conditions :
Workaround : Disable guest LAN or disable IPv6. |
Reference
Release Notes for Cisco Wireless LAN Controllers and Lightweight Access Points for Release 7.2.103.0
Release Notes for Cisco Wireless LAN Controllers and Lightweight Access Points for Release 7.4.100.0
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Hi Vinay,
I think from software release 4.X WLC,LAP supports IPv6 along with IPv4 for the WLC given below..
"
_________________________________________________________________________________________
The Cisco Wireless LAN Solution command line interface (CLI) enables operators to connect an ASCII console to the Cisco Wireless LAN Controller and configure the controller and its associated access points.
This document covers the Cisco CLI release 4.1 commands for the following platforms:
•Cisco 2000 series Wireless LAN Controllers
•Cisco 2100 series Wireless LAN Controllers
•Cisco 4400 series Wireless LAN Controllers
•Catalyst 3750G Wireless LAN Controller Switches
•Cisco Wireless Services Module (WiSM) for Cisco Catalyst 6500 Series Switches and Cisco Catalyst 7600 Series Routers
•Cisco Wireless LAN Controller Network Module (WLCM) for Cisco Integrated Services Routers
_________________________________________________________________________________________
config wlan IPv6Support
config wlan IPv6support {enable | disable} wlan_id
__________________________________________________________________________________________
"
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
Would be worth mention that "L2 security" in 6.0 is not complemented by First Hop Security for IPv6 - the latter being supported in 7.2. Any wireless deployment considering to use IPv6 should take a look at 7.2 - deploying IPv6 on wireless without that features is a dangerous exercise.
Also a useful document to read wrt the 7.2 is the deployment guide at http://www.cisco.com/en/US/products/ps10315/products_tech_note09186a0080bae506.shtml
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: