- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- PEAP Authentication - Configuration example for Windows 7
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
07-15-2011 07:19 AM - edited 11-18-2020 02:54 AM
Introduction
PEAP - Protected Extensible Authentication Protocol is one flavor of EAP It is a authentication protocol used in wireless and used for Point <to> Point connections. PEAP provides more security in authentication for 802.11 wireless local area networks that support 802.1X port access control.
PEAP authentication is managed between the PEAP supplicant and the authentication server (Radius). In first phase the client authenticates the server using a TLS -Transport Layer Security, certificate-based mechanism. This establishes an encrypted tunnel through which the second-phase PEAP credentials may be securely exchanged. The parameters used by the client in negotiating PEAP authentication are configured through the Windows Device Manager properties.
PEAP is based on server side EAP-TLS authentication. With PEAP many organizations can avoid the issues associated with installing digital certificates on every client device as required by EAP-TLS; instead, they can select the methods of client authentication, such as logon passwords or OTPs that best suit their corporate needs. Also PEAP is an enhancement of EAP-TLS authentication, PEAP encapsulates a second-phase authentication transaction within the TLS framework.
Prerequisites
Client running Windows 7 operating system with 802.1X support
Cisco Access Point
Cisco Access control Radius Server (ACS)
Network Diagram

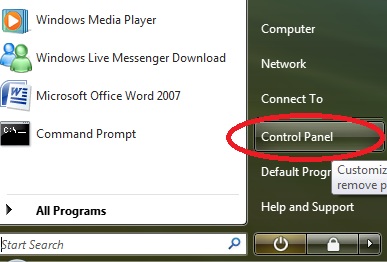
- Click on the START menu and open the Control Panel.
- Click the link under Network and Internet called View network status and tasks. (Note: If the screen looks different, select Control Panel Home on the left.

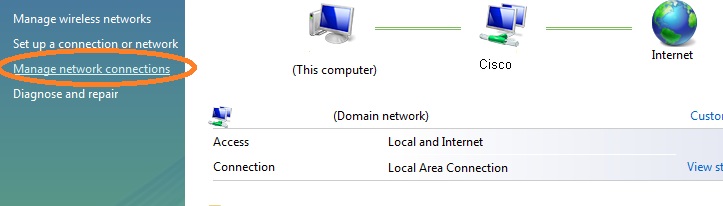
- Click on the Mange Network Connections located on the left side of the window.
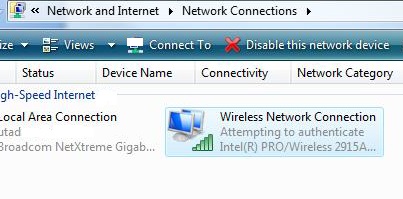
- Right click the Wireless Network Connection and select Connect/Disconnect.
- Click on Setup a connection or network located at the bottom of the window.

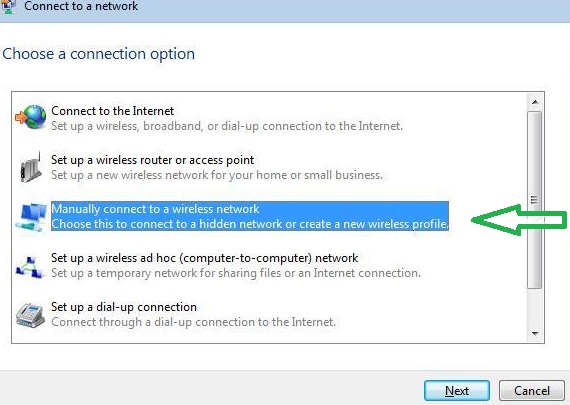
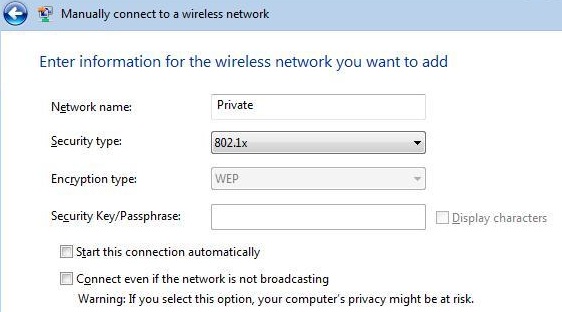
- Manually connect to a wireless network. Select Next.
- Choose the desired SSID of the network to be used for PEAP authentication from the Available networks list, and click Configure. Click Add in the Preferred networks section to configure a new network SSID.
- Choose the appropriate Network Authentication and Data Encryption parameters using the drop-down arrows.
- In this configuration example we used the Network Name is Private, Security Type is 802.1X, and Encryption type is WEP.Uncheck “Start this connection automatically”. Select Next.
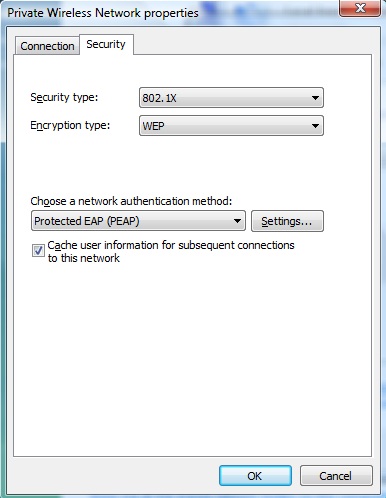
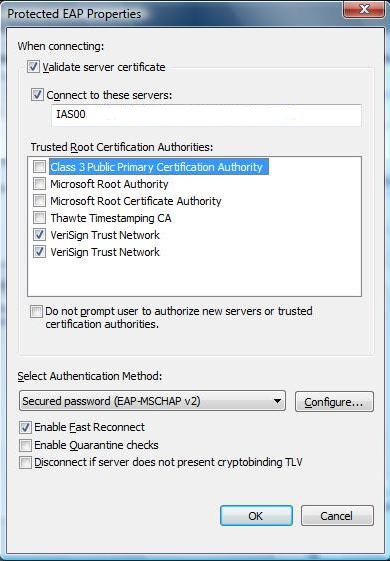
- Click on the Settings button next to PEAP
- Check “Connect to these servers:” box . Add “IAS00 (dummy name)” to the box. Check any VeriSign Certificate Authorities. If you do not see any VeriSign Trust Network Options, continue on with the instructions.
- Check Validate server certificate.
Note:- If you do not check Validate server certificate, user credentials are not protected by the EAP server certificate. The configuration of the Microsoft PEAP (EAP-MSCHAP v2) supplicant (available in Windows XP SP1 and later and in Windows 2000 SP4)
Note:- For a computer to be successfully authenticated to a domain, the computer must be registered to the domain using a non-802.1X secured network (a wired connection) prior to attempting machine authentication with PEAP.
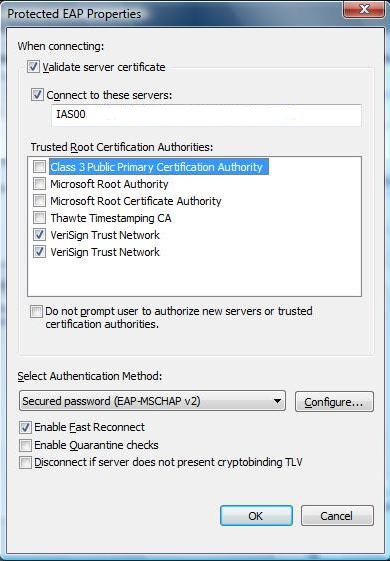
- In this example (above snapshot) we assumed that the server name is IAS00, certificate authority is VeriSign. It may be different depend upon network.
- Check the correct CA in the Trusted Root Certification Authorities list.
- Choose Secured password (EAP-MSCHAP v2) using the drop-down arrow in the Select Authentication Method field.
- Check Enable Fast Reconnect to enable client devices to perform a PEAP session resume with properly equipped and configured EAP servers. PEAP session resume enables client devices to re-authenticate with an EAP server after roaming to a new access point without submitting the second-phase PEAP credentials. The session is resumed using the cached TLS credentials.
- Click Configure, and the EAP MSCHAP V2 Properties screen appears

- Uncheck the box (Automatically use my Windows logon name and password).
![]()
If desired, check Automatically use my Windows logon name and password (and domain if any) to enable the Microsoft PEAP supplicant to use the Windows logon name for PEAP authentication. This enables the user to log in to the wireless network using their Windows credentials.
When this options is checked, the user credentials cannot be changed because they are stored in the user's profile, whether using manually entered credentials or using Windows credentials.
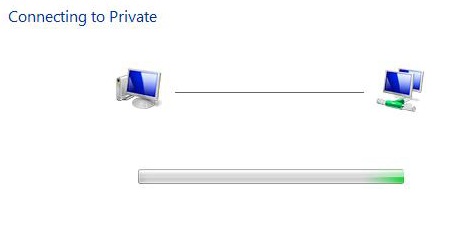
- Choose Private and click the Connect button
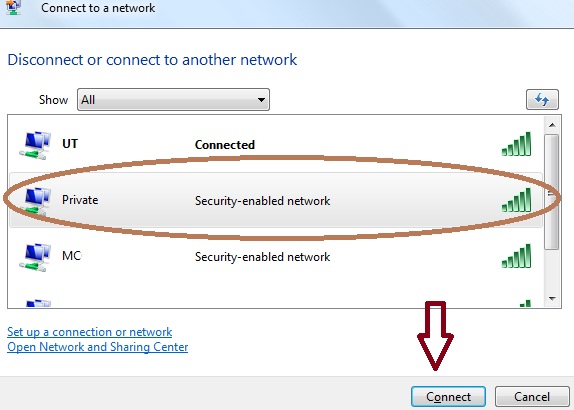
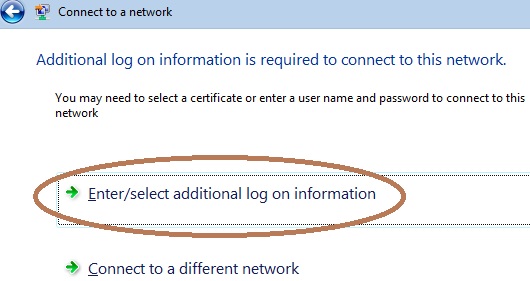
- Click Enter/select additional log on information.
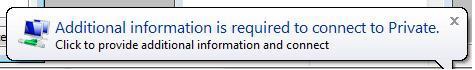
- A box will appear in the bottom right of the screen as indicated below. Once you select it, a Server certificate box will appear. Select OK.

- Click on the box that appears in the bottom right of the screen.
- Return to the Protected EAP Properties box and check the boxes in front of VeriSign Trust Network.
- Another box will show up asking for a User name, password, and Domain. Type in your Username, your password, and Logon Domain. Click OK

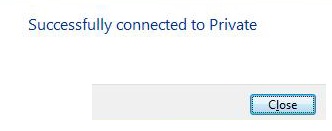
- It will connect you to the wireless Network using PEAP. If this doesn't happen then a box will pop up at the bottom right hand corner (See below)
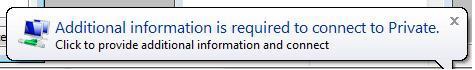
- Click on the box and another box will show up asking for a User name, password, and Domain. Type in your Username, your password, and Logon Domain. Click OK. It will connect you to the wireless Network using PEAP.
PEAP Authentication process

1. The client sends an EAP Start message to the access point
2. The access point replies with an EAP Request Identity message
3. The client sends its network access identifier (NAI), which is its username, to the access point in an EAP Response message
4. The access point forwards the NAI to the RADIUS server encapsulated in a RADIUS Access Request message
5. The RADIUS server will respond to the client with its digital certificate
6. The client will validate the RADIUS server's digital certificate
7. The client and server negotiate and create an encrypted tunnel
8. This tunnel provides a secure data path for client authentication
9. Using the TLS Record protocol, a new EAP authentication is initiated by the RADIUS server
10. The exchange will include the transactions specific to the EAP type used for client authentication
11. The RADIUS server sends the access point a RADIUS ACCEPT message, including the client's WEP key, indicating successful authentication
Reference Links
Wireless LAN Security White Paper
PEAP - Configuration example for Windows XP
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: