- Cisco Community
- Technology and Support
- Networking
- Networking Knowledge Base
- PEAP Authentication - Configuration example for Windows XP
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
07-13-2011 05:56 AM - edited 11-18-2020 02:54 AM
- Introduction
- Network Diagram
- Network connections
- Connect to a wireless network
- Choose a wireless network
- Add a wireless connection
- More Information on WPA, TKIP and AES
- Wireless Authentication properties
- Authentication Process
- PEAP Authentication process
- Reference Links
Introduction
EAP-MS-CHAP v2 Authentication for Windows XP
PEAP - Protected Extensible Authentication Protocol is one flavor of EAP It is a authentication protocol used in wireless and used for Point <to> Point connections. PEAP provides more security in authentication for 802.11 wireless local area networks that support 802.1X port access control.
PEAP authentication is managed between the PEAP supplicant and the authentication server (Radius). In first phase the client authenticates the server using a TLS -Transport Layer Security, certificate-based mechanism. This establishes an encrypted tunnel through which the second-phase PEAP credentials may be securely exchanged. The parameters used by the client in negotiating PEAP authentication are configured through the Windows Device Manager properties.
PEAP is based on server side EAP-TLS authentication. With PEAP many organizations can avoid the issues associated with installing digital certificates on every client device as required by EAP-TLS; instead, they can select the methods of client authentication, such as logon passwords or OTPs that best suit their corporate needs. Also PEAP is an enhancement of EAP-TLS authentication, PEAP encapsulates a second-phase authentication transaction within the TLS framework.
The Wireless Zero Configuration i.e. WZC is windows built in Client service for Wireless Networking. This client can be configured automatically by AD (Active Directory) Group Policy if you're running a minimum of Windows Server 2003 SP1 or 2003 R2. This section will be mostly demonstrated with Windows XP SP1/2 .
Network Diagram

Network connections
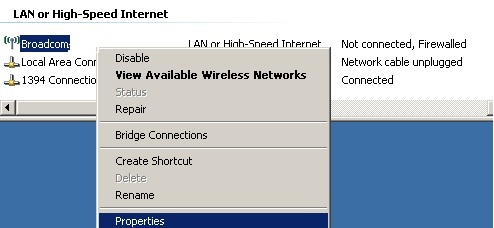
In windows SP1 or SP2, configure the Wireless Client by the right clicking on your Wireless Ethernet card under the "Network Connections" and then select properties.
Connect to a wireless network

SP2 has the updated interface as shown. Right click on the Wireless Icon in system tray, select "View Available Networks" and Click on "Change advanced settings".
Choose a wireless network

In XP SP2, create a profile by clicking on the "Add" button under the "Preferred networks"section. Type the SSID that you are using on your Cisco Access Point.
Add a wireless connection

For "Network Authentication", select "Wi-Fi Protected Access" i.e. WPA. WPA mode requires XP SP2 or Vista. WPA2 is supported if you installed the additional WPA2 patch for Windows XP or running Vista.Your Cisco Access Point also needs to have firmware that supports WPA mode and Wi-Fi H/W adapter drivers supports WPA.
For "Data encryption", select "Temporal Key Integrity Protocol" i.e. TKIP. With WPA or WPA2 choose either TKIP or AES. AES is better but make sure hardware supports it.
More Information on WPA, TKIP and AES
- WPA (Wi-Fi Protected Access)
IEEE 802.11i with different headers. WPA uses TKIP and message integrity is based on RC4 for encryption. It uses Pre- shared (personal) vs. Enterprise (RADIUS) for authentication. WPA and WPA2 may operate in enterprise mode using RADIUS server to hold per user keys for individual access control in a large networks. For a small network i.e. home network (without a RADIUS server) a pre-shared key (PSK) may be used. In the case the same key will be used by all clients, so we may require to do more work in order to keep the key update.
- TKIP vs. AES based CCMP
It is the algorithm used for message integrity and confidentiality. WPA was designed to be used with TKIP and WPA2 designed to use stronger AES based. However, some devices allow WPA (not WPA2) with AES (and WPA2 with TKIP). AES is optional in WPA; in WPA2 both AES is mandatory, BUT TKIP is optional.
Note that TKIP is not directly comparable to AES; TKIP is an integrity check, AES is an encryption algorithm.
In the context of wireless security this actually means TKIP vs. "AES-based CCMP" (not just AES). TKIP is a lower end encryption protocol (WEP2) and AES is a higher end (WPA2/802.11i) encryption protocol. AES is preferred.
- TKIP + AES:-
This is what the encryption standards are for WEP2 (TKIP) and WPA2/802.11i (AES). It will attempt to use AES if available and fall back to TKIP if not. This setting offers the most compatibility but won't guarantee a higher level of encryption if a device falls back to TKIP.
Under the "Authentication" tab, check box "Enable EEE 802.1x authentication for this network" and select "Protected EAP (PEAP)".
Wireless Authentication properties

You will also need to check "Authenticate as computer when computer information is available" to enable "Machine Authentication" i.e. "Computer Authentication". Machine Authentication allows your PC to connect to the network by authenticating as "Computer" before a legitimate user logs in. This allows a machine to obtain group policies just like it was connected to a wired network and this is a unique feature of the Windows Client.
If you don't have "Machine Authentication" enabled then your Group Policy will not function. Also all the non-cached users cannot log on to your machine even if they are given the proper permissions at the Domain level. "Machine Authentication" is needed to recreate the full "Wired" experience. In order for "Machine Authentication" to work, PEAP only requires that a Computer is joined to the domain. The computer will use its "Computer Password"to log on to the network. Note that for EAP-TLS or PEAP-EAP-TLS (stronger alternatives to PEAP) to work the computer must have a "Machine Certificate" installed from the Enterprise Root CA.
Under Protected EAP Properties, Click "Properties" under "EAP".

Note:- In this section, make sure that you check "Validate server certificate" because if you don't PEAP will be as weak as EAP-FAST anonymous DH mode.
Also select the "Trusted Root Certificate Authority" for this wireless connection. In SP2 this has added a new security feature for "Do not prompt user to authorize new servers or trusted certification authorities". This whole window is a very important security feature because Wireless LAN to be locked by your Certificate Authority and not anyone else's.
Choose "EAP-MSCHAP v2" which stands for PEAP-EAP-MSCHAPv2 mode which most people refer to as "PEAP" since this is the most common implementation.
If you had selected "Smart Card or other Certificate" here, it means you've set it to use PEAP-EAP-TLS mode. EAP-TLS mode is configured from the previous section under "Wireless Network Properties" by choosing "Smart Card or other Certificate" instead of "Protected EAP (PEAP)". Both EAP-TLS or PEAP-EAP-TLS require client side Certificates to work, which makes them stronger two factor authentication solutions.
Click "Configure" as shown in screenshot. This mode automatically logs a user on using their current Windows Credentials. If you're trying to connect to a wireless network on a Windows Domain you're not joined to, automatic logon will not work so you must uncheck this and you'll be prompted for domain credentials of the network you're connecting with. Note that it will give you the chance to save those credentials.

Note to users of Microsoft Windows 7
Cisco plug-in software modules such as EAP-FAST and PEAP are compatible with Windows 7. You do not need to upgrade these modules when you upgrade to Windows 7.
Some more Detailed information on WPA, AES, WEP etc
- WPA2 mandates AES-based CCMP for message integrity and confidentiality. TKIP (weaker) is optional.
- WPA2 mixed mode allows device to try WPA2 first, and if that fails fall-back to WPA.
- WEP was supposed to provide Confidentiality, but has found to be vulnerable and should no longer be used, has been found to be vulnerable and is often the default; this should be changed. Most devices that support WEP can be firmware/software upgraded to WPA. Do not use unless some devices can not be upgraded to support WPA. WEP has been outdated for years and has better replacements. The 40-bit encryption is just not strong enough to keep data secure and can be broken rather easily. Newer encryption methods use stronger encryption and have yet to be broken while WEP can be broken in a minute, use WPA where possible.
Preference Summary (Highest to Lowest)
- WPA2 + AES
- WPA + AES (only if all devices support it).
- WPA + TKIP+AES (only if all devices can support it).
- WPA + TKIP
- Disabled (no security)
The most common two options will be WPA2 + AES and WPA + TKIP. Because they match the mandatory requirements in the standards (WPA2 requires AES, WPA requires TKIP).
You can use WPA + AES for higher security than TKIP, but only if your devices support it (it is optional). For this reason it is not very common. You also do not get the improved roaming features of WPA2.
WPA + TKIP+ AES provides a fallback in case AES is not supported by a device in that it switches to the more common TKIP. The disadvantage is that it might switch to TKIP unexpectedly but is more backwards compatible if needed.
Currently TKIP has no known vulnerabilities, so for broadest compatibility we can use WPA + TKIP.
WPA2 + TKIP is possible (as TKIP is optional in WPA2), but AES is more secure and mandatory for all WPA2 devices.
Authentication Process

PEAP Authentication process
1. The client sends an EAP Start message to the access point
2. The access point replies with an EAP Request Identity message
3. The client sends its network access identifier (NAI), which is its username, to the access point in an EAP Response message
4. The access point forwards the NAI to the RADIUS server encapsulated in a RADIUS Access Request message
5. The RADIUS server will respond to the client with its digital certificate
6. The client will validate the RADIUS server's digital certificate
7. The client and server negotiate and create an encrypted tunnel
8. This tunnel provides a secure data path for client authentication
9. Using the TLS Record protocol, a new EAP authentication is initiated by the RADIUS server
10. The exchange will include the transactions specific to the EAP type used for client authentication
11. The RADIUS server sends the access point a RADIUS ACCEPT message, including the client's WEP key, indicating successful authentication
Reference Links
Wireless LAN Security White Paper
PEAP - Configuration example for Windows 7
Find answers to your questions by entering keywords or phrases in the Search bar above. New here? Use these resources to familiarize yourself with the community: