- Cisco Community
- Technology and Support
- Data Center and Cloud
- Application Centric Infrastructure
- Re: Meaning of stateful-flag in aci filter
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-25-2021 01:31 AM
Hello,
I have read several contradictory statements in Cisco Documentation about the stateful flag in aci filters:
- Sometimes it says that it is only used for legacy AVS deployments where the AVS was REALLY doing stateful filtering. If AVS is not used it will do NOTHING.
- Sometimes it says that enabling the stateful flag will more or less just check for the established flag for the return traffic to get something like an established acl without having to do this manually with the tcp flags setting.
What is true?
Solved! Go to Solution.
- Labels:
-
Cisco ACI
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-25-2021 06:36 AM
Hi @ThiloS
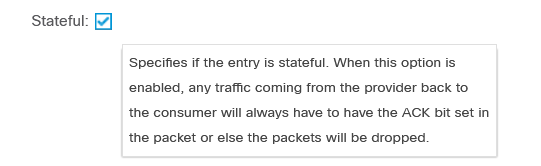
Regarding the stateful flag, this is the hover description:
Basically it says it will look for TCP ACK flag set, otherwise the traffic is dropped. But let's not just believe everything blindly and verify if this is really true.
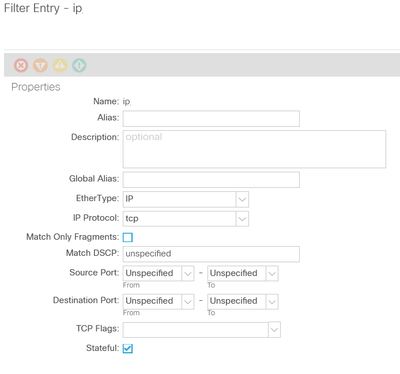
We have a contract with this filter configured between two EPGs (no TCP flags, stateful set
Looking in zoning rule we have this entry:
Leaf301# show zoning-rule +---------+--------+--------+----------+----------------+---------+----------+------+----------+----------------------+ | Rule ID | SrcEPG | DstEPG | FilterID | Dir | operSt | Scope | Name | Action | Priority | +---------+--------+--------+----------+----------------+---------+----------+------+----------+----------------------+ | 4111 | 32772 | 49155 | 45 | uni-dir-ignore | enabled | 3047424 | TEST | permit | fully_qual(7) | | 4102 | 49155 | 32772 | 44 | bi-dir | enabled | 3047424 | TEST | permit | fully_qual(7) | +---------+--------+--------+----------+----------------+---------+----------+------+----------+----------------------+
Important data from it: RuleId = 4111 (this is the provider->consumer direction)
Next, let's checking the zoning rule in hardware:
module-1# show system internal aclqos zoning-rules 4111
ASIC type is NS
=============================================================
Rule ID: 4111 Scope 6 Src EPG: 32772 Dst EPG: 49155 Filter 45
Curr TCAM resource:
=============================
unit_id: 0
=== Region priority: 1921 (rule prio: 7 entry: 129)===
sw_index = 41 | hw_index = 48
Moving further into the hardware, let's see what's the name of the tcam table name where the hw index 48 is configured (our contract entry):
module-1# show system internal aclqos zoning-rules tcam-tbl-name 48 ===== HW-Index 49 ===== KEY: Table MTH_LUX_SLVZ_DHS_SECURITYGROUPKEYTABLE0_MEMIF_DATA, Asic Inst 0, index 49 DATA: Table MTH_LUX_SLVZ_DHS_SECURITYGROUPDATATABLE0_MEMIF_DATA, Asic Inst 0, index 49
Finally let's see how the Contract really looks in TCAM hardware:
module-1# show platform internal ns table MTH_LUX_SLVZ_DHS_SECURITYGROUPKEYTABLE0_MEMIF_DATA 48
Tgt slot is not 24(0 based)
***** ASIC : 0 *****
======================================================================================================================================================
TABLE INSTANCE : 0
======================================================================================================================================================
ENTRY[000048] = sg_label=0x6 sclass=0x8004 dclass=0xc003 prot=0x6
tcpflags=0x10 sup_tx_mask=0x1 src_policy_incomplete_mask=0x1 dst_policy_incomplete_mask=0x1
class_eq_mask=0x1 aclass_mask=0x1ff port_dir_mask=0x1 dport_mask=0xffff
sport_mask=0xffff tcpflags_mask=0xef ip_opt_mask=0x1 ipv6_route_mask=0x1
ip_fragment_mask=0x1 ip_frag_offset0_mask=0x1 ip_frag_offset1_mask=0x1 ip_mf_mask=0x1
l4_partial_mask=0x1 dst_local_mask=0x1 routeable_mask=0x1 spare_mask=0x7ff
v4addr_key_mask=0x1 v6addr_key_mask=0x1 valid=0x1
======================================================================================================================================================
TABLE INSTANCE : 1
======================================================================================================================================================
ENTRY[000048] = sg_label=0x6 sclass=0x8004 dclass=0xc003 prot=0x6
tcpflags=0x10 sup_tx_mask=0x1 src_policy_incomplete_mask=0x1 dst_policy_incomplete_mask=0x1
class_eq_mask=0x1 aclass_mask=0x1ff port_dir_mask=0x1 dport_mask=0xffff
sport_mask=0xffff tcpflags_mask=0xef ip_opt_mask=0x1 ipv6_route_mask=0x1
ip_fragment_mask=0x1 ip_frag_offset0_mask=0x1 ip_frag_offset1_mask=0x1 ip_mf_mask=0x1
l4_partial_mask=0x1 dst_local_mask=0x1 routeable_mask=0x1 spare_mask=0x7ff
v4addr_key_mask=0x1 v6addr_key_mask=0x1 valid=0x1
As you can see, if the contract filter has stateful set will match in hardware on traffic with tcpflags = 0x10, which is the ACK flag set, for the provider->consumer direction.
For the sake of brevity I will show below how TCAM entry looks like without stafetul set.
module-1# show platform internal ns table MTH_LUX_SLVZ_DHS_SECURITYGROUPKEYTABLE0_MEMIF_DATA 48
Tgt slot is not 24(0 based)
***** ASIC : 0 *****
======================================================================================================================================================
TABLE INSTANCE : 0
======================================================================================================================================================
ENTRY[000048] = sg_label=0x6 class_dir=0x1 sclass=0x8004 dclass=0xc003
prot=0x6 sup_tx_mask=0x1 src_policy_incomplete_mask=0x1 dst_policy_incomplete_mask=0x1
class_eq_mask=0x1 aclass_mask=0x1ff port_dir_mask=0x1 dport_mask=0xffff
sport_mask=0xffff tcpflags_mask=0xff ip_opt_mask=0x1 ipv6_route_mask=0x1
ip_fragment_mask=0x1 ip_frag_offset0_mask=0x1 ip_frag_offset1_mask=0x1 ip_mf_mask=0x1
l4_partial_mask=0x1 dst_local_mask=0x1 routeable_mask=0x1 spare_mask=0x7ff
v4addr_key_mask=0x1 v6addr_key_mask=0x1 valid=0x1
======================================================================================================================================================
TABLE INSTANCE : 1
======================================================================================================================================================
ENTRY[000048] = sg_label=0x6 class_dir=0x1 sclass=0x8004 dclass=0xc003
prot=0x6 sup_tx_mask=0x1 src_policy_incomplete_mask=0x1 dst_policy_incomplete_mask=0x1
class_eq_mask=0x1 aclass_mask=0x1ff port_dir_mask=0x1 dport_mask=0xffff
sport_mask=0xffff tcpflags_mask=0xff ip_opt_mask=0x1 ipv6_route_mask=0x1
ip_fragment_mask=0x1 ip_frag_offset0_mask=0x1 ip_frag_offset1_mask=0x1 ip_mf_mask=0x1
l4_partial_mask=0x1 dst_local_mask=0x1 routeable_mask=0x1 spare_mask=0x7ff
v4addr_key_mask=0x1 v6addr_key_mask=0x1 valid=0x1
Stay safe,
Sergiu
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-25-2021 06:06 AM - edited 01-25-2021 06:07 AM
In a short, it’s rudimentary stateful inspection:
You can have contract structure like that:
1. source TCP/1025-65535 >> destination TCP/80 <both direction> <reverse ports>
in this config client can open connection to port 80. and server can reply. Also server open connection with source 80 to any 1025-65535 port .
2. a. source TCP/1025-65535 >> destination TCP/80 NO <both direction>. NO <reverse ports>
b. Source TCP/80 >> destination TCP/1025-65535 STATEFULL
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-25-2021 06:36 AM
Hi @ThiloS
Regarding the stateful flag, this is the hover description:
Basically it says it will look for TCP ACK flag set, otherwise the traffic is dropped. But let's not just believe everything blindly and verify if this is really true.
We have a contract with this filter configured between two EPGs (no TCP flags, stateful set
Looking in zoning rule we have this entry:
Leaf301# show zoning-rule +---------+--------+--------+----------+----------------+---------+----------+------+----------+----------------------+ | Rule ID | SrcEPG | DstEPG | FilterID | Dir | operSt | Scope | Name | Action | Priority | +---------+--------+--------+----------+----------------+---------+----------+------+----------+----------------------+ | 4111 | 32772 | 49155 | 45 | uni-dir-ignore | enabled | 3047424 | TEST | permit | fully_qual(7) | | 4102 | 49155 | 32772 | 44 | bi-dir | enabled | 3047424 | TEST | permit | fully_qual(7) | +---------+--------+--------+----------+----------------+---------+----------+------+----------+----------------------+
Important data from it: RuleId = 4111 (this is the provider->consumer direction)
Next, let's checking the zoning rule in hardware:
module-1# show system internal aclqos zoning-rules 4111
ASIC type is NS
=============================================================
Rule ID: 4111 Scope 6 Src EPG: 32772 Dst EPG: 49155 Filter 45
Curr TCAM resource:
=============================
unit_id: 0
=== Region priority: 1921 (rule prio: 7 entry: 129)===
sw_index = 41 | hw_index = 48
Moving further into the hardware, let's see what's the name of the tcam table name where the hw index 48 is configured (our contract entry):
module-1# show system internal aclqos zoning-rules tcam-tbl-name 48 ===== HW-Index 49 ===== KEY: Table MTH_LUX_SLVZ_DHS_SECURITYGROUPKEYTABLE0_MEMIF_DATA, Asic Inst 0, index 49 DATA: Table MTH_LUX_SLVZ_DHS_SECURITYGROUPDATATABLE0_MEMIF_DATA, Asic Inst 0, index 49
Finally let's see how the Contract really looks in TCAM hardware:
module-1# show platform internal ns table MTH_LUX_SLVZ_DHS_SECURITYGROUPKEYTABLE0_MEMIF_DATA 48
Tgt slot is not 24(0 based)
***** ASIC : 0 *****
======================================================================================================================================================
TABLE INSTANCE : 0
======================================================================================================================================================
ENTRY[000048] = sg_label=0x6 sclass=0x8004 dclass=0xc003 prot=0x6
tcpflags=0x10 sup_tx_mask=0x1 src_policy_incomplete_mask=0x1 dst_policy_incomplete_mask=0x1
class_eq_mask=0x1 aclass_mask=0x1ff port_dir_mask=0x1 dport_mask=0xffff
sport_mask=0xffff tcpflags_mask=0xef ip_opt_mask=0x1 ipv6_route_mask=0x1
ip_fragment_mask=0x1 ip_frag_offset0_mask=0x1 ip_frag_offset1_mask=0x1 ip_mf_mask=0x1
l4_partial_mask=0x1 dst_local_mask=0x1 routeable_mask=0x1 spare_mask=0x7ff
v4addr_key_mask=0x1 v6addr_key_mask=0x1 valid=0x1
======================================================================================================================================================
TABLE INSTANCE : 1
======================================================================================================================================================
ENTRY[000048] = sg_label=0x6 sclass=0x8004 dclass=0xc003 prot=0x6
tcpflags=0x10 sup_tx_mask=0x1 src_policy_incomplete_mask=0x1 dst_policy_incomplete_mask=0x1
class_eq_mask=0x1 aclass_mask=0x1ff port_dir_mask=0x1 dport_mask=0xffff
sport_mask=0xffff tcpflags_mask=0xef ip_opt_mask=0x1 ipv6_route_mask=0x1
ip_fragment_mask=0x1 ip_frag_offset0_mask=0x1 ip_frag_offset1_mask=0x1 ip_mf_mask=0x1
l4_partial_mask=0x1 dst_local_mask=0x1 routeable_mask=0x1 spare_mask=0x7ff
v4addr_key_mask=0x1 v6addr_key_mask=0x1 valid=0x1
As you can see, if the contract filter has stateful set will match in hardware on traffic with tcpflags = 0x10, which is the ACK flag set, for the provider->consumer direction.
For the sake of brevity I will show below how TCAM entry looks like without stafetul set.
module-1# show platform internal ns table MTH_LUX_SLVZ_DHS_SECURITYGROUPKEYTABLE0_MEMIF_DATA 48
Tgt slot is not 24(0 based)
***** ASIC : 0 *****
======================================================================================================================================================
TABLE INSTANCE : 0
======================================================================================================================================================
ENTRY[000048] = sg_label=0x6 class_dir=0x1 sclass=0x8004 dclass=0xc003
prot=0x6 sup_tx_mask=0x1 src_policy_incomplete_mask=0x1 dst_policy_incomplete_mask=0x1
class_eq_mask=0x1 aclass_mask=0x1ff port_dir_mask=0x1 dport_mask=0xffff
sport_mask=0xffff tcpflags_mask=0xff ip_opt_mask=0x1 ipv6_route_mask=0x1
ip_fragment_mask=0x1 ip_frag_offset0_mask=0x1 ip_frag_offset1_mask=0x1 ip_mf_mask=0x1
l4_partial_mask=0x1 dst_local_mask=0x1 routeable_mask=0x1 spare_mask=0x7ff
v4addr_key_mask=0x1 v6addr_key_mask=0x1 valid=0x1
======================================================================================================================================================
TABLE INSTANCE : 1
======================================================================================================================================================
ENTRY[000048] = sg_label=0x6 class_dir=0x1 sclass=0x8004 dclass=0xc003
prot=0x6 sup_tx_mask=0x1 src_policy_incomplete_mask=0x1 dst_policy_incomplete_mask=0x1
class_eq_mask=0x1 aclass_mask=0x1ff port_dir_mask=0x1 dport_mask=0xffff
sport_mask=0xffff tcpflags_mask=0xff ip_opt_mask=0x1 ipv6_route_mask=0x1
ip_fragment_mask=0x1 ip_frag_offset0_mask=0x1 ip_frag_offset1_mask=0x1 ip_mf_mask=0x1
l4_partial_mask=0x1 dst_local_mask=0x1 routeable_mask=0x1 spare_mask=0x7ff
v4addr_key_mask=0x1 v6addr_key_mask=0x1 valid=0x1
Stay safe,
Sergiu
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-25-2021 07:03 AM
Thank you! A perfect detailed response finally! Good job!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-25-2021 12:20 PM
FYI - you may find reading my answer to this post useful.
And I've informed the Cisco documentation team (although they have not yet got back to me) regarding the total confustion created by the incorrect information in https://www.cisco.com/c/en/us/td/docs/switches/datacenter/aci/apic/sw/1-x/Operating_ACI/guide/b_Cisco_Operating_ACI/b_Cisco_Operating_ACI_chapter_01000.html
Forum Tips: 1. Paste images inline - don't attach. 2. Always mark helpful and correct answers, it helps others find what they need.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-25-2021 10:48 PM - edited 01-25-2021 10:49 PM
thank you, yes I already knew this Post and it was useful as well. I just wonder why you obviously can configure the same thing either with a filter using the tcp session rules (flags) manually or by using the stateful checkbox. Also I am 100% sure that in the past this checkbox was referring to AVS only where you could REALLY do stateful filtering with session state in the AVS.
Does this checkbox maybe enable statetul filtering for AVE? And the TCP flags would not?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide