- Cisco Community
- Technology and Support
- Online Tools and Resources
- Cisco CLI Analyzer
- Cisco CLI Analyzer
- Cisco CLI Analyzer RSA key verification failing everytime
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Cisco CLI Analyzer RSA key verification failing everytime
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-18-2021 05:50 PM
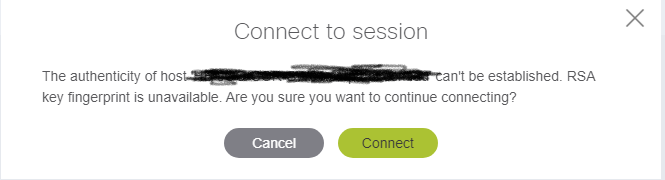
Since version 3.6.7 I get this each time I open an SSH connection to any of the devices in my fleet. I have been using the CLI analyzer tool for more than a year and none of the devices have changed RSA keys.
Deleteing the known_hosts file made no difference.
- Labels:
-
Cisco CLI Analyzer
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-20-2021 03:52 PM
Hi Luke. Thanks for using Cisco CLI Analyzer.
If you are on a Windows machine and these devices were working prior to version 3.6.7, it's likely due to the fact that we updated the version of ssh-keyscan included with Cisco CLI Analyzer in order to address some security vulnerabilities. With the upgrade of ssh-keyscan, several dated KEX Algorithms were deprecated and are no longer recognized as valid when doing the handshake for host key verification. This can pose a problem for older Cisco hardware.
We are planning to include a feature to bypass this warning automatically in release 3.6.8 of Cisco CLI Analyzer.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-21-2021 07:19 AM
Thanks Scott,
Would regenerating the ssh key on the switch(es) be a workaround? If so which algorithms can be used?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-06-2021 01:00 PM
Here was my workaround.
1. Close Cisco CLI Analyzer
2. Install Cisco CLI Analyzer v3.6.6 on another PC.
3. Rename the folder C:\Program Files\Cisco Systems, Inc\Cisco CLI Analyzer\keyscan\64 to "old" on your PC
4. Copy same folder from v3.6.6 PC to your PC in the same location.
5. Start Cisco CLI Analyzer.
This replaces their "updated" version if KeyScan with the previous version. You will get a prompt the first time you connect to the switch but then it adds it to the list of trusted hosts and you're golden.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-31-2021 01:42 AM
hi any ETA for version 3.6.8 ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-01-2021 06:45 AM
Hello @fpacholski
Tentatively the release for 3.6.8 will be available in the next week or two. If you wish to be notified when it's available please edit your notifications in the Software Downloads page. https://software.cisco.com/download/home/286311499/type/286312309/os?catid=null
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-01-2021 05:38 PM - edited 06-01-2021 05:41 PM
Is there a way to get a startup log / trace file from Cisco CLI Analyzer?
I got the upgrade to 3.6.8 today and now have less than nothing as the application fails to display any window of any sort; I can see it running in task manager / process explorer but it looks to be choking on something.
Process Explorer shows that the nw.exe process is starting the below command, which dies off within a few moments:
"C:\Program Files\Cisco Systems, Inc\Cisco CLI Analyzer\nw.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1852,4388010660445875460,871930487639031769,131072 --disable-features=nw2 --lang=en-US --service-sandbox-type=none --no-sandbox --user-data-dir="C:\Users\[redacted]\AppData\Local\Cisco-CLI-Analyzer\User Data" --nwapp-path="C:\Program Files\Cisco Systems, Inc\Cisco CLI Analyzer" --mojo-platform-channel-handle=3328 /prefetch:8
*edit* there appears to be a crashdump file being produced at a rate of 8 per minute, there is several hundred of these mdmp files by now.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-07-2021 02:29 PM
Hi Luke. Probably a silly question, but have you tried uninstalling and reinstalling? I've heard a couple cases of folks having issues with auto upgrades. You should be able to uninstall and reinstall without discarding any of your user data.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-04-2022 03:24 PM
I found this fix on another site.
Type the below text into the console - hostname is the ip address or hostname of router.
'ssh-keygen -R hostname'
Exit then log in again.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide