- Cisco Community
- Technology and Support
- Security
- Cloud Security
- CDA Support for Windows Server 2016
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
CDA Support for Windows Server 2016
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-21-2016 09:53 AM - edited 03-08-2019 05:40 PM
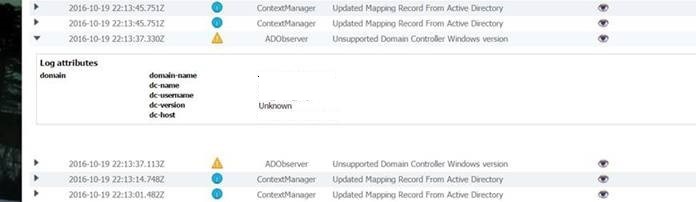
Has anyone seen a roadmap or ETA for a CDA patch to support Windows Server 2016 Domain Controller connections? It appears there is a version check since the WMI namespace it is utilizing hasn't changed from server 2012R2. Its just checking the security event log, I don't understand why there is an OS version constraint to begin with I mean from their doc:
Supported Active Directory Versions
CDA supports the following Active Directory versions:
- Windows 2003
- Windows 2003R2
- Windows 2008
- Windows 2008 R2
- Windows 2012
- Windows 2012 R2
Other than Windows 2000, they support them all. If someone on the Dev team insisted on putting one in, then test and release an update while the OS has been in Beta. I'll take back everything bad I have said this past week if I just missed the release AND I will also admit I suck.
- Labels:
-
Web Security
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-21-2016 07:54 PM
I would be surprised to see any update of CDA's official support listing since that would involve validation testing and support.
Cisco is putting their resources into the more strategic platforms for identity such as ISE. We expect enhancements to ISE's passive identity feature set going forward and even an entry level licensing that's designed to do only that.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-04-2017 08:54 PM
i´m facing with this issue too, how did you work arround it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-05-2017 07:46 AM
I haven't heard anything official, but from back-channel sources I've heard that CDA is dead. Cisco has not done their customer base the courtesy of announcing this nor have they done the courtesy of informing their customer base of the supported way forward, which appears to be ISE. People with inside knowledge and people who spend their time pouring over every Cisco product announcement are probably all over this, but the rest of us are not.
My impression here is that Cisco is pulling a bait-and-switch move: offering a very nice feature and then turning around and requiring you to purchase another product to make it work. Hopefully I'm very, very wrong about this. If I'm not, then this is the sort of business practice that makes us look much more closely at other vendors during our next refresh cycle - we would only stick with Cisco ASA if we had no reasonable alternative.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-18-2017 10:13 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-18-2017 07:33 PM
ISE-PIC (Identity Services Engine - Passive Identity Connector) has been available for several months now.
http://www.cisco.com/c/en/us/products/collateral/security/identity-services-engine/datasheet-c78-738846.html
http://www.cisco.com/c/en/us/td/docs/security/ise/2-2/pic_admin_guide/PIC_admin/PIC_admin_chapter_00.html
It is the recommended and supported platform going forward. It is not free, but the list price is just US$1250 plus US$200 per year for full TAC support.
If you have a full ISE deployment, the features are all included in there as well.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-21-2017 06:55 AM
We were told ICE-PIC wouldn't currently work with the WSAs and still have the WSA apply policies based on AD groups, at least a month ago now.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-22-2017 09:00 AM
My understanding is that ISE-PIC is the "budget" way forward for WSA and ATA identity firewall, but that it's not ready to replace CDA yet. The situation is a mess for the time being, because CDA is in an appallingly deep state of neglect. We're not impressed at all by the way Cisco is handling this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-07-2017 05:12 AM
Like you Erik, I am not impressed with how Cisco is handeling this. We now have to choose between removing Identity Firewall or staying on Windows AD 2012 indefenitly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-14-2017 03:26 PM
Allegedly ISE-PIC will resolve this issue eventually, and the street price of a pair (for redundancy) isn't going to break many budgets. But the amount of time between the release of Server 2016 and "eventually" is completely ridiculous, and the necessity of adding an additional paid component to maintain existing functionality is sketchy.
This is arguable worse than the situation with Symantec adding support for Windows 2012 to BackupExec, and comparisons with Symantec are seldom flattering.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-26-2018 07:11 AM
Is there an update on the status of this? Are 2016 domain controllers still not supported on the CDA? Workarounds?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-28-2018 01:14 PM
No they are still not. It also looks like WSA and CWS are going to go EOL, assumingly with CDA as well.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-16-2018 05:25 PM
We have serious problems with our Identity Firewall feature on ASA.
We set up our new Windows 2016 domain controllers and added them to the domain.
As a result, users' authentications have also passed through these new Domain controllers, and the CDAs have not noticed the logs from the new DCs, which caused not working firewall rules. So we had to power down our new DCs.
I tried to integrate the 2016 DC into the CDA, but it’s not supported and I only got error messages.
We already escalated this to Cisco, but they don‘t have a solution yet.
SGT is a nice additional feature, but it is not an substitute for us, because it doesn‘t have feature parity to identity firewall.
Furthermore ISE-PIC is using pxgrid which is not supported by ASA.
So we have actually a scenario were we even cannot work parallel with the old 2008 domain controllers, which makes migration to Win 2016 impossible.
That‘s insane.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-13-2019 09:58 AM
Very late, but finally they added support for Windows 2016 in CDA Patch 6.
https://www.cisco.com/c/en/us/td/docs/security/ibf/cda_10/release_notes/cda10_rn.html#pgfId-189162
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-24-2019 11:29 PM
Wow, this was unexpected. Tested and surprisingly it works with Windows Server 2016. Just read the documentation.
This solved an issue we had with IPv6 with CDA using ISE's syslogs as the identity provider, as the syslogs with IPv6 addresses were not parsed.
CDA however has its shortcomings
- Looking at Windows Event Logs you will get the IP address used when the user logs in. Not a great idea when your clients are dual stack. You will usually only get the IPv6 address. You don't really have control of how the workstation communicates, so if it communicates with a IPv4 only enabled device you don't have identity
- IP Filter Exclusions don't work with IPv6. Tried adding a IPv6 subnet but it won't validate the input
Other than that the Windows Server 2016 support was welcomed considering there is no alternative from Cisco for a client using ASA and recent Windows Server versions.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide


Cisco is putting their resources into the more strategic platforms for identity such as ISE. We expect enhancements to ISE's passive identity feature set going forward and even an entry level licensing that's designed to do only that.