- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: Cisco ISE IP Interfaces configuration
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-23-2020 11:42 PM - edited 02-26-2020 12:04 AM
Hello Team,
Need suggesion...
(We have 2 ISE hardware box SNS-3495) we are planning to connect 2x ISE (Active/Standby) with 3x interfaces.
Please share if any supportive IP designing document is available.
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-24-2020 02:10 AM
Hello Mohammed,
Thanks for your response.
Is there any suppoting document which states that "Its not necessary for PAN and PSN to be in same subnet." ??
Also please suggest if IP assignement is correct or not.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-25-2020 02:23 PM
ISE will listen for TACACS+ on Gig2 if you prefer to use a separate interface. This is all dependent on your overall architecture and design (routing, security zones, etc).
Both RADIUS and TACACS+ are lightweight protocols, so unless you expect to overload the interface bandwidth there may be no value in using separate interfaces if the same node will be processing both.
I would suggest also reviewing the following:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-24-2020 01:06 AM
One IP per NIC is good unless you expect high throughput or you want NIC
bonding for redundancy.
Its not necessary for PAN and PSN to be in same subnet. Just ensure that
required ports are allowed to communication and latency is less than 200
msec.
***** Please remember to rate useful posts.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-24-2020 02:10 AM
Hello Mohammed,
Thanks for your response.
Is there any suppoting document which states that "Its not necessary for PAN and PSN to be in same subnet." ??
Also please suggest if IP assignement is correct or not.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-24-2020 01:08 PM
The wording of the question is a bit vague, but it sounds like you have 2 total SNS-3495 appliances (you should be aware that End of Software Support on that platform was October 2019 - 34xx EoL Notice ) you are using to deploy ISE.
If this is the case, you would have all 4 Personas (PAN, MnT, PSN, Device Admin) running on both nodes. In this scenario, you would typically only use 2x IP addresses for ISE (Gig0 for management, RADIUS, TACACS, etc; Gig1 for Guest Portal) and 1x IP address for CIMC for each node.
I would suggest reviewing the following collateral:
Install Guide - Network Deployments in ISE
Install Guide - ISE Ports Reference
When using multiple interfaces for ISE services, you will also need to configure an interface alias for portal redirection. I would suggest reviewing the section on Load Balancing ISE Web Services in this Cisco Live presentation:
BRKSEC-3432 - Advanced ISEArchitect, Design and Scale ISE for your production networks
Cheers,
Greg
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-25-2020 01:41 AM
Helo Greg,
Thank for the information.
Deployment scenario that you have mentioned is correct. We have 2 total SNS-3495 appliances and we are aware that it is EOS & EOL.
As you mentioned "you would typically only use 2x IP addresses for ISE (Gig0 for management, RADIUS, TACACS, etc; Gig1 for Guest Portal)" so cant we configure Gig 2 for TACACS ??
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-25-2020 02:23 PM
ISE will listen for TACACS+ on Gig2 if you prefer to use a separate interface. This is all dependent on your overall architecture and design (routing, security zones, etc).
Both RADIUS and TACACS+ are lightweight protocols, so unless you expect to overload the interface bandwidth there may be no value in using separate interfaces if the same node will be processing both.
I would suggest also reviewing the following:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 01:18 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 12:56 PM
I would not see the value in using separate interfaces in the same subnet for the separate services. Using separate interfaces would typically involve those interfaces sitting on different subnets.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-02-2020 11:51 PM
Yes you are correct.
So if we use Gig 0 for Mgmt & TACACS and Gig 1 for Guest then that will be a best approch.
however Gig 0 & Gig 1 in different subnet and connected to different switch then what will be my gateway ??
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
03-03-2020 02:15 PM
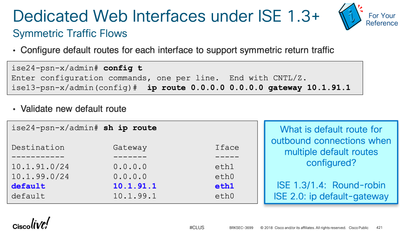
As of ISE 2.0, you can configure multiple default gateways via 'ip route' when you have multiple interfaces and it will use the correct gateway for outbound traffic.
I would suggest reviewing the Load Balancing ISE Web Services section of the following CiscoLive deck:
BRKSEC-3699: Designing ISE for Scale & High Availability - 2018 Orlando (Session Reference deck)
Excerpt:
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide