- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Cisco ISE Live logs
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Cisco ISE Live logs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-14-2020 07:52 AM
Hi,
Its a kind of annoying to see many of the following logs throughout the day in cisco ise.
Jan 14, 2020 02:27:05.460 PM | Default >> Default | Default |
why the switch is kept on sending access-request massages from the port, where the device had been already authenticated and working fine.
Moreover, this NAD is sending unnecessary requests to ISE even no device or users connect to the switch.
Is there a way to stop it? Please see the attached screenshot.
Best Regards,
MD
- Labels:
-
Identity Services Engine (ISE)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-16-2020 02:43 PM
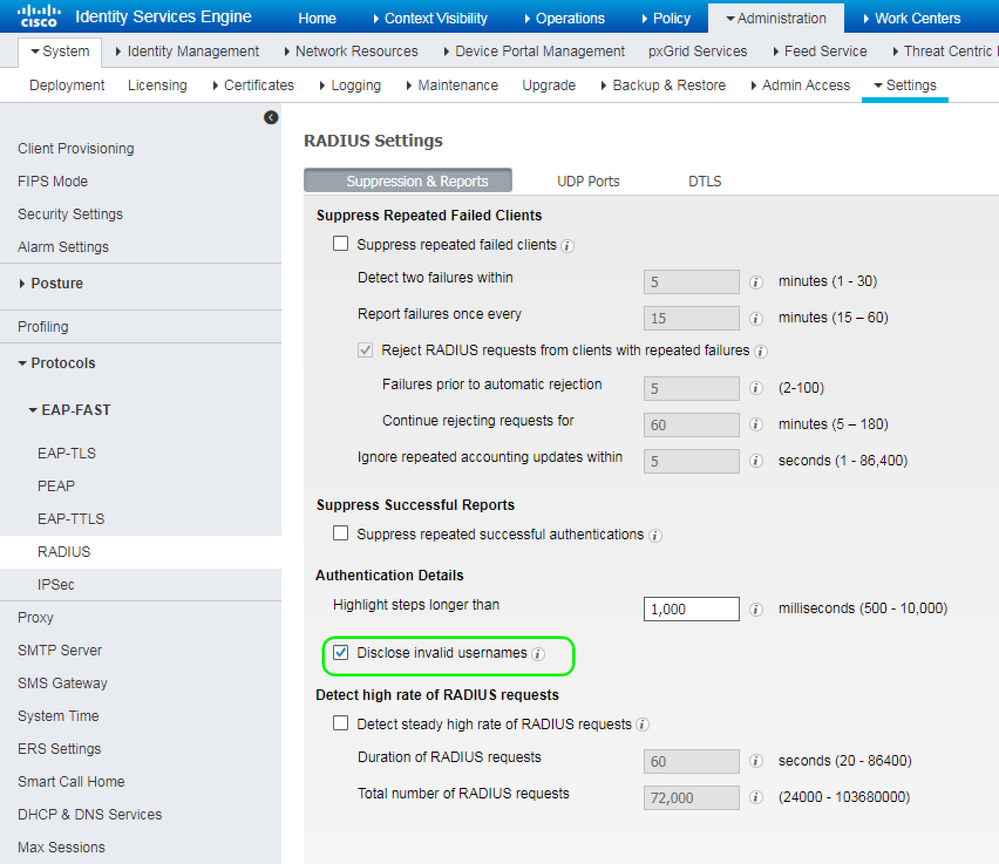
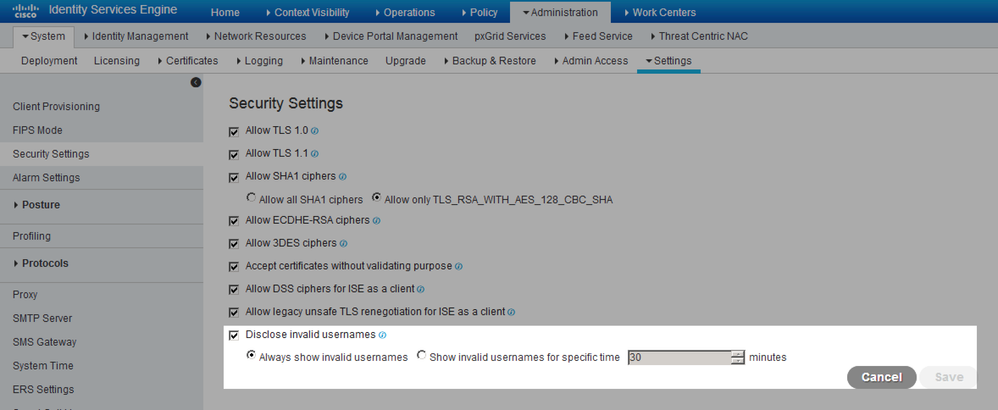
First of all, need to un-mask what INVALID is. ISE 2.4+ is masking the usernames of the failed authentications. ISE 2.4 has an option to disclose it temporally for 30 minutes. Once that identified, then we will try and determine why it repeating the authentications.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-17-2020 05:16 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-18-2020 06:33 PM
ISE 2.6 has it under Security Settings. Note a known issue CSCvo24097 is resolved in ISE 2.6 Patch 3.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 06:40 AM
Hi ,
Yes, Now I can see the name "admin" and getting the following logs. But no one tiring to authenticate, i have configured only a single port for dot1x and MAB. Both IP-phone and laptop is working fine.. If i disconnect one of the device from that post ,it starts sending an unnecessary authentication request to the ISE. Am i doing something wrong?
Switch port Configuration :
interface FastEthernet0/8
description 802.1x Enabled
switchport access vlan 11
switchport mode access
switchport voice vlan 156
srr-queue bandwidth share 1 30 35 5
priority-queue out
authentication control-direction in
authentication event fail action next-method
authentication event server alive action reinitialize
authentication host-mode multi-domain
authentication order mab dot1x
authentication priority mab dot1x
authentication port-control auto
authentication periodic
authentication timer reauthenticate server
authentication timer inactivity server
authentication violation replace
mab
mls qos trust device cisco-phone
mls qos trust cos
dot1x pae authenticator
dot1x timeout tx-period 10
dot1x max-reauth-req 3
spanning-tree portfast
spanning-tree bpduguard enable
spanning-tree guard root
service-policy input AUTOQOS-SRND4-CISCOPHONE-POLICY
BR,
MD
| Event | 5400 Authentication failed |
| Failure Reason | 22056 Subject not found in the applicable identity store(s) |
| Resolution | Check whether the subject is present in any one of the chosen identity stores. Note that some identity stores may have been skipped due to identity resoultion settings or if they do not support the current authentication protocol. |
| Root cause | Subject not found in the applicable identity store(s). |
| Username | admin |
| Authentication Method | PAP_ASCII |
| Authentication Protocol | PAP_ASCII |
| Service Type | Login |
| SelectedAuthenticationIdentityStores | Internal Users |
| SelectedAuthenticationIdentityStores | All_AD_Join_Points |
| SelectedAuthenticationIdentityStores | Guest Users |
| IdentityPolicyMatchedRule | Default |
| ISEPolicySetName | Default |
| IdentitySelectionMatchedRule | Default |
| IsMachineIdentity | false |
| DTLSSupport | Unknown |
| Network Device Profile | Cisco |
| Location | Location#All Locations |
| Device Type | Device Type#All Device Types |
| IPSEC | IPSEC#Is IPSEC Device#No |
| RADIUS Username | admin |
| Event | 5400 Authentication failed |
| Username | admin |
| Endpoint Id | |
| Endpoint Profile | |
| Authentication Policy | Default >> Default |
| Authorization Policy | Default |
| Authorization Result |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
01-20-2020 06:46 AM
Thanks, I guess i have found the root cause. I configured automate-tester on the switch which was causing this behavior.
BR,
MD
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide