- Cisco Community
- Technology and Support
- Security
- Network Access Control
- How to use Endpoint Custom Attributes to control network access (DACL or VLAN)?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-17-2021 02:05 PM
I would like to use an endpoint custom attribute to trigger the network access a device has. So as an example if I have a device that has a endpoint custom attribute of Display, I would like to use that as a condition to assign a specific DACL or vlan to that device while it is on the network.
Can anyone point me in the right direction to get this done? I have created a results with authorization profiles for each the vlan and one for the dacl but I do not know how to apply them in a policy set. I would imagine the logic would be if you connected via wired or wireless mab and the device has a custom endpoint attribute assigned where the "custom device type" equals "Display" then either change the vlan or use a downloadable acl to control access for that device. I just can't figure out how to do that, and I haven't found a resource (video, article, configuration guide) that covers limiting access based on custom endpoint attributes.
Your help is appreciated.
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-18-2021 05:17 AM
Thanks for that and what you are showing is what I expect to see. The question is how do I get the attribute to show up in a library for a policy? I find no where in my libraries the ability to use that custom endpoint attribute. In your picture it appears to have endpoints having a CustomAttr field...how did that happen? My point is I cannot connect the dots from creating the attribute to having it actually appear as an option in a policy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-18-2021 10:08 AM
Hi @Odysseu$
please double check if you are not trying to add the Endpoint Custom Attribute in the Authentication Policy ... for this kind of Conditions you should add it in the Authorization Policy.
Hope this helps !!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-19-2021 05:42 AM - edited 04-19-2021 05:43 AM
So one thing for anyone who reads this. To get the authorization policy to show. This is what must be done.
Create a policy set. Add some form of connectivity as the condition (802.1x, MAB, etc) then SAVE THE POLICY (key thing not mentioned anywhere). After you save the policy there is a big > at the end of the policy (notice there is nothing that says this is how you find authorization policy) if you click on the big > it will expand out the policy and behold the authorization policy makes its appearance. If you try to click on > without saving, it doesn't work and you can't see the authorization policy.
Thank you everyone that helped. All of your replies are all true and part of the solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-17-2021 02:56 PM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-17-2021 03:38 PM
authorization policy in the policy set configuration I think I would have
it. When I add a condition in the policy set this is what I get:
[image: image.png]
And there is no way to use the CUSTOMATTRIBUTE dictionary that my custom
endpoint items exist in in a policy set, what am I missing?
[image: image.png]
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-17-2021 09:18 PM
Hi @Odysseu$
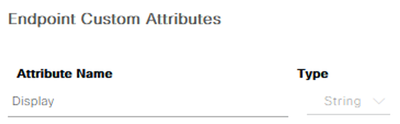
create your Endpoint Custom Attribute at:
Administration > Identity Management > Settings > Endpoint Custom Attribute:
At Policy > Policy Set > select your Policy > Authorization Policy ... at the Attribute condition, type your Custom Attribute:
Hope this helps !!!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-18-2021 05:17 AM
Thanks for that and what you are showing is what I expect to see. The question is how do I get the attribute to show up in a library for a policy? I find no where in my libraries the ability to use that custom endpoint attribute. In your picture it appears to have endpoints having a CustomAttr field...how did that happen? My point is I cannot connect the dots from creating the attribute to having it actually appear as an option in a policy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-18-2021 10:08 AM
Hi @Odysseu$
please double check if you are not trying to add the Endpoint Custom Attribute in the Authentication Policy ... for this kind of Conditions you should add it in the Authorization Policy.
Hope this helps !!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-18-2021 06:56 PM
In addition to the information provided by Marcelo for defining the Endpoint Custom Attribute and creating a Condition and/or Authorisation Policy to use it, the endpoint needs to be associated with that attribute.
If the attribute is not being provided by an External Identity Source like AD, you will need to manually edit the endpoint in Context Visibility and assign the custom attribute you defined.
Example:
Creating the attribute
Defining the AuthZ Policy
Assigning the attribute to the Endpoint
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-19-2021 05:42 AM - edited 04-19-2021 05:43 AM
So one thing for anyone who reads this. To get the authorization policy to show. This is what must be done.
Create a policy set. Add some form of connectivity as the condition (802.1x, MAB, etc) then SAVE THE POLICY (key thing not mentioned anywhere). After you save the policy there is a big > at the end of the policy (notice there is nothing that says this is how you find authorization policy) if you click on the big > it will expand out the policy and behold the authorization policy makes its appearance. If you try to click on > without saving, it doesn't work and you can't see the authorization policy.
Thank you everyone that helped. All of your replies are all true and part of the solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-20-2021 05:09 PM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide