- Cisco Community
- Technology and Support
- Security
- Network Access Control
- ISE 2.6 and Microsoft AD integration using LDAP-S
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-03-2020 01:17 PM
Hi Experts,
Under the configuration on ISE for Active Directory integration, Administration > Identity Management > External Identity Sources > Active Directory, I don't see the options to use "LDAP Secure" ( such as port 636). I assumed, with 2.6, ISE does support LDAPS for Microsoft AD, but can't find any configuration guide. Can anyone share some docs that cover how to setup ISE with LDAPS for Microsoft AD?, what's the certificate requirement? Any limitation on Authentication and Authorization? etc.
Thanks in advance.
Solved! Go to Solution.
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-05-2020 07:41 AM
Please 'RATE' and 'MARK ACCEPTED', if applicable.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-04-2020 12:57 AM
AFAIK, the communication ports are fixed. We cannot change AD connector communication from LDAP 389 port to LDAPS 636 Port. Though it is LDAP, but all the attributes are encrypted.
If you need LDAPS, configure a new external LDAP identity store on ISE and there you can use LDAPS port.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-04-2020 07:51 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-05-2020 07:01 AM
Hi @Ping Zhou ,
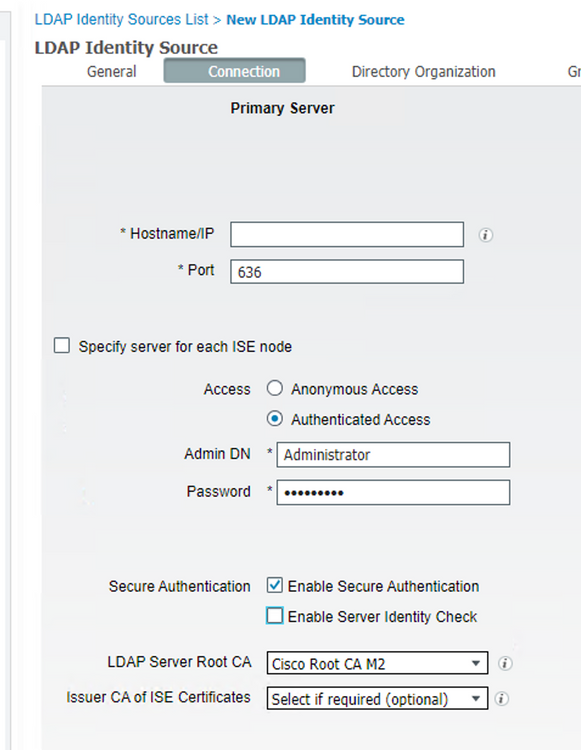
You need to choose Schema as 'Active Directory'. Then configure it like in the picture below.
Make sure LDAP and ISE trust each other's certificate's CA certificates.
Please 'RATE' and 'MARK ACCEPTED', if applicable.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-05-2020 07:34 AM
Thanks again for sharing your config screenshot.
,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-05-2020 07:41 AM
Please 'RATE' and 'MARK ACCEPTED', if applicable.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
10-26-2020 06:24 AM
Hi,
do you have any updates regarding the public docs you mentioned?
Many thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-25-2021 10:37 AM
Just wondering if there is an update on this yet?
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
02-25-2021 11:11 AM
Hi @Kacey Wilson ,
it looks like that the answer is no ... please take a look at: ISE Installation Guide 3.0 - Node Ports., search for External Identity Sources and Resources (Outbound).
Hope this helps !!!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
09-23-2022 01:12 AM
Is there any update on this?
If you use the standard way of joining the AD via Administration > Identity Management > External Identity Sources > Active Directory, are you still only able to use port 389?
I am reading the Implementing and Configuring Cisco Identity Services Engine (SISE), and it says the way which is suggested above by configuring it via an LDAP external Identity Source has limitations:
Active Directory and LDAP Comparison
Active Directory
Rich attribute set
Direct tie between ISE and AD
Fast performance
ISE can join multiple directories
Search up or down the tree
Active Directory accessed as LDAP server
ISE can join multiple directories
Slower performance
Fewer attributes
Search down the tree only
You can access the Active Directory database either as Active Directory or as an LDAP server. Both methods have their pros and cons:
When you connect to Active Directory via the Active Directory method, you gain advantages due to the direct tie between the Cisco ISE and Active Directory—an extensive attribute range, good performance, and the ability to search up or down the tree. Starting from version 1.3, Cisco ISE can join multiple directories.
When you connect to Active Directory as an LDAP server, you can join multiple directories. However, this method slows performance, offers fewer attributes, and supports only searching down the tree.
Why is it not possible to join the domain via LDAPs via Administration > Identity Management > External Identity Sources > Active Directory?
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide