- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: ISE Internal user disabled
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ISE Internal user disabled
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-23-2021 02:55 AM
I am running around a strange issue. My ISE internal users gets disabled automatically in 24 hours.
All the users are TACACS users. They change the password from a network device and it works, but after 24 hours the same user gets disabled.
This user does not get disabled if I change the password directly from ISE admin GUI.
- Labels:
-
Identity Services Engine (ISE)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-23-2021 03:13 AM
Hello @manvik,
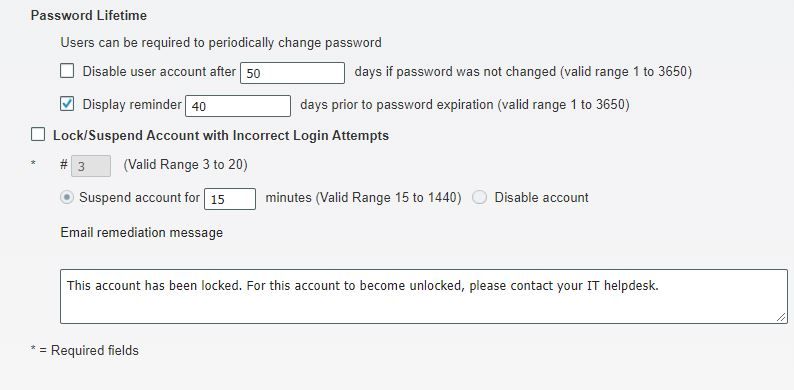
Go to Administration -> Identity Management -> Settings -> User Authentication Settings
in the password policy tab uncheck "Disable user account after":
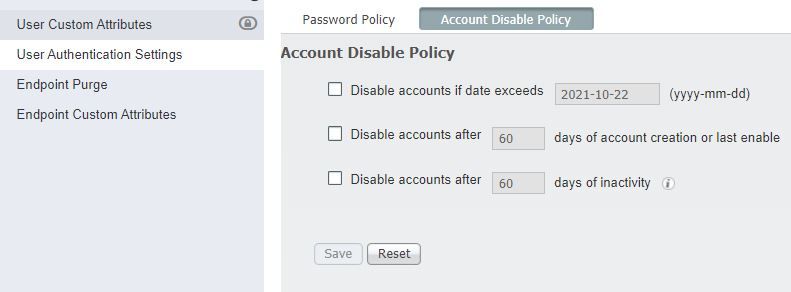
And verify Account disable policy tab :
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-23-2021 05:30 AM
"Disable User account after" is set to 30 days to meet compliance and audit purpose.
my doubt is why does account gets auto disabled after 24 hours of self password change.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-23-2021 06:20 AM
As far as i know because the password did not get changed in that specific delay from 1 to 30.
Uncheck the box, save and check the box again of "Disable User account after" and wait for the 24h.
Or you can check BugSearch
If the same behavior occurs, you can open a TAC case.
Hope that helps.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-24-2021 04:37 PM
Copying from the on-box page-level help,
Check the Disable account after n days of account creation or last enable check box and enter the number of days. This option disables the user account when the account creation date or last access date exceeds the specified number of days. Administrators can manually enable the disabled user accounts, which reset the number of days count.
That means, it's expected to disable the user account after n days.
Please use the options in the Password Lifetime section, instead.
Note that, if the enable password configured for an internal user, then that also needs updated within the configured password lifetime.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide