- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: ISE WLAN Machine Authentication
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
ISE WLAN Machine Authentication
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-05-2020 10:56 AM
Hello,
I've implemented a wired policy to make a machine authentication, It checks if machine exists inside domain and if it belongs to a specific AD group. It works fine but I've not be able to make it working over a WLAN network.
I've copied the wired policy changing only the condition from wired-802.1x to wireless-802.1x but I have some doubts about how I've to configure the SSID and windows connection to SSID:
- Have I to configure it without layer 2 security? or I have to configure WPA, 802.1x...?
- I suppose that I've to configure the ISE as Radius Servers
- I suppose that I've to configure "ISE" inside "NAC State inside advanced options.
- About Windows client, I understand that it is not enough to connect to wireless network, I suppose that I have to create a "manual" connection and specify that it will be through 802.1x and PEAP.
Thank you very much.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-05-2020 11:18 AM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-05-2020 01:04 PM
Thank you very much for the information but this instructions are focused about machine authentication through Certificate and I'm configuring a machine authentication through AD. About the WLC configuration, it does not show the Layer 2 authentication section. I think that this example is not close to my scenario.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-05-2020 01:56 PM
On your SSID, configure Layer-2 security to be WPA/WPA2 and then 802.1x for key management. On your client, you would select WPA2-Enterprise, PEAP, and ensure that it is configured to do computer authentication only. The Windows 10 wireless profile editor is not the best at giving you appropriate options. Using GPO would be best to ensure you push down the correct settings. If you are logged into the computer when trying to connect, it will send your user credentials and that obviously would not match the Domain Computers group. So you need to ensure that the authentication is sending the computer credentials.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-06-2020 08:48 AM
Thank you very much Colby, your information has been very useful. I've imported the wireless profile through a xml file to avoid the windows 10 profile editor. I've got that PC send the host identification inside "Radius-username" field but right now I've a problem, it does not match the policy, it seems there is some problem with the supplicant or its configuration, in the ISE Live Logs I can see that it receives the domain hostname but sometimes I get this error:
| Event | 5440 Endpoint abandoned EAP session and started new |
| Failure Reason | 5440 Endpoint abandoned EAP session and started new |
| Resolution | Verify known NAD or supplicant issues and published bugs. Verify NAD and supplicant configuration. |
| Root cause | Endpoint started new authentication while previous is still in progress. Most probable that supplicant on that endpoint stopped conducting the previous authentication and started the new one. Closing the previous authentication. |
And other times:
| Event | 5411 Supplicant stopped responding to ISE |
| Failure Reason | 12930 Supplicant stopped responding to ISE after sending it the first PEAP message |
| Resolution | Verify that supplicant is configured properly to conduct a full EAP conversation with ISE. Verify that NAS is configured properly to transfer EAP messages to/from supplicant. Verify that supplicant or NAS does not have a short timeout for EAP conversation. Check the network that connects the Network Access Server to ISE. |
| Root cause | Supplicant stopped responding to ISE after sending it the first PEAP message |
What do you think about that?
Thank you very much.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-06-2020 09:02 AM
| Event | 5440 Endpoint abandoned EAP session and started new |
| Failure Reason | 5440 Endpoint abandoned EAP session and started new |
| Resolution | Verify known NAD or supplicant issues and published bugs. Verify NAD and supplicant configuration. |
| Root cause | Endpoint started new authentication while previous is still in progress. Most probable that supplicant on that endpoint stopped conducting the previous authentication and started the new one. Closing the previous authentication. |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-10-2020 10:49 AM
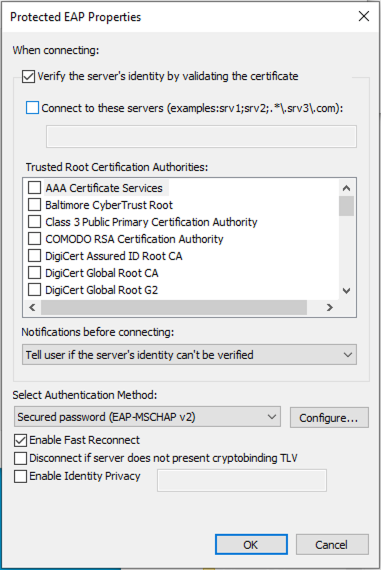
I suspect your Windows endpoint does not trust the ISE certificate and is rejecting the EAP tunnel creation.
Are you using a self-signed certificate on ISE? Never do this for this exact reason.
What are your wireless network properties set to?
Are you requiring validation of the server's certificate (ISE) yet do not have ISE listed as a trusted CA or the ISE certificate is not signed by one of your Trusted Root CAs?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-11-2020 08:36 AM - edited 08-11-2020 08:42 AM
Hi,
I've unchecked this option (Verify the server's identity....), I've tried again and initially the PC does not send the "hostname" inside "username" field, it is blank, then I make a new try and it send it but I can see this error:
| Event | 5440 Endpoint abandoned EAP session and started new |
| Failure Reason | 5440 Endpoint abandoned EAP session and started new |
| Resolution | Verify known NAD or supplicant issues and published bugs. Verify NAD and supplicant configuration. |
| Root cause | Endpoint started new authentication while previous is still in progress. Most probable that supplicant on that endpoint stopped conducting the previous authentication and started the new one. Closing the previous authentication. |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
08-11-2020 02:39 PM - edited 08-11-2020 03:33 PM
You have not provided enough configuration details for us to help you. See How to Ask the Community for Help for future requests.
Please follow our recommended configurations - specifically for dot1x timers - under Configure the Switch for Monitor Mode in the ISE Secure Wired Access Prescriptive Deployment Guide since it could be that you are not allowing enough time for ISE to authenticate a request before sending a new one.
dot1x timeout tx-period 7 dot1x max-reauth-req 3
If doing wireless, see ISE & Catalyst 9800 Integration Guide or AireOS WLC configuration for ISE.
I recommend you call TAC for further troubleshooting.
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide