- Cisco Community
- Technology and Support
- Security
- Network Access Control
- Re: Prevent ISE from sending authentication to AD if BadPwdCount = <value>
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-20-2019 09:10 AM - edited 05-20-2019 09:13 AM
I'd like to configure ISE so that if the AD attribute badPwdCount is equal or less than a particular value, ISE won't send any additional authentication attempts in order to prevent ISE from locking out the AD account. This is for CWA that is hooked into AD. Yes, it's a bad idea to use a CP with an AD back-end but alas, that is the task I have at hand!
As far as I know and can see, ISE only supports AD attribute use with the AuthZ policy, not AuthN and therefore this capability is NOT support by ISE but perhaps I am missing something. Can anyone confirm definitively?
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-20-2019 09:48 AM
AD attributes are only available for use in authorization policy. ISE will still query AD if the authentication request comes in regardless of the attribute.
Regards,
-Tim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-20-2019 09:48 AM
AD attributes are only available for use in authorization policy. ISE will still query AD if the authentication request comes in regardless of the attribute.
Regards,
-Tim
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-21-2019 01:26 AM
Cheers - that's inline with documentation and my testing.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-11-2019 09:23 AM
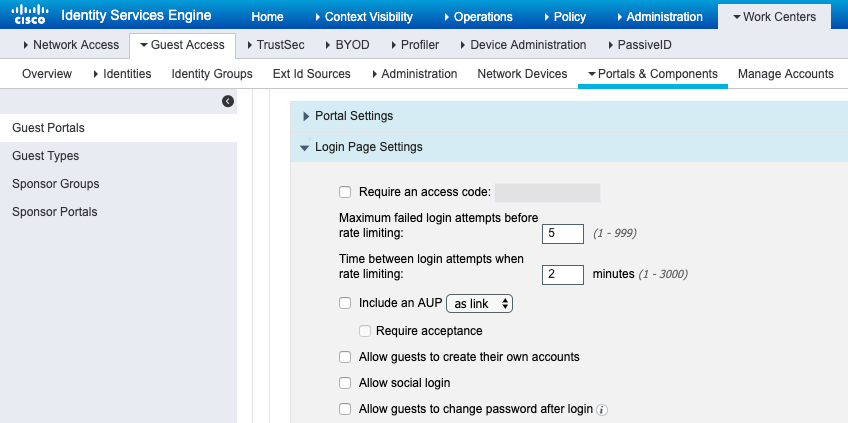
If using CWA there is better option. We have authentication rate limiting directly on the portal page that you can use. This isn't utilizing AuthZ policy:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-18-2019 01:51 AM
Cheers. Unfortunately this is a much worse option. I've already tested this option but as ISE doesn't know the BadPwdCount in AD, in many case the AD account will be locked out. For example, if BadPwdCount is already at 2 because it was tripped by some other application that hooks into AD or standard Windows login where the the user makes a typo twice (and AD policy is 3 failed logins), ISE will still send request not knowing AD is at 2, and lock it out.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-18-2019 02:05 PM
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide