- Cisco Community
- Technology and Support
- Security
- Network Access Control
- TrustSec deployment without 802.1x
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-02-2020 08:09 AM
We are looking into TrustSec at a high level for network segmentation purposes. Is it possible to deploy Trustsec without doing 802.1x on the layer 2 devices? Could it be used to deploy SGACLS and TAGS to layer 3 routers for segmentation without authenticating clients and doing dot1x on the switch ports?
Solved! Go to Solution.
- Labels:
-
Identity Services Engine (ISE)
Accepted Solutions
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2020 08:06 AM
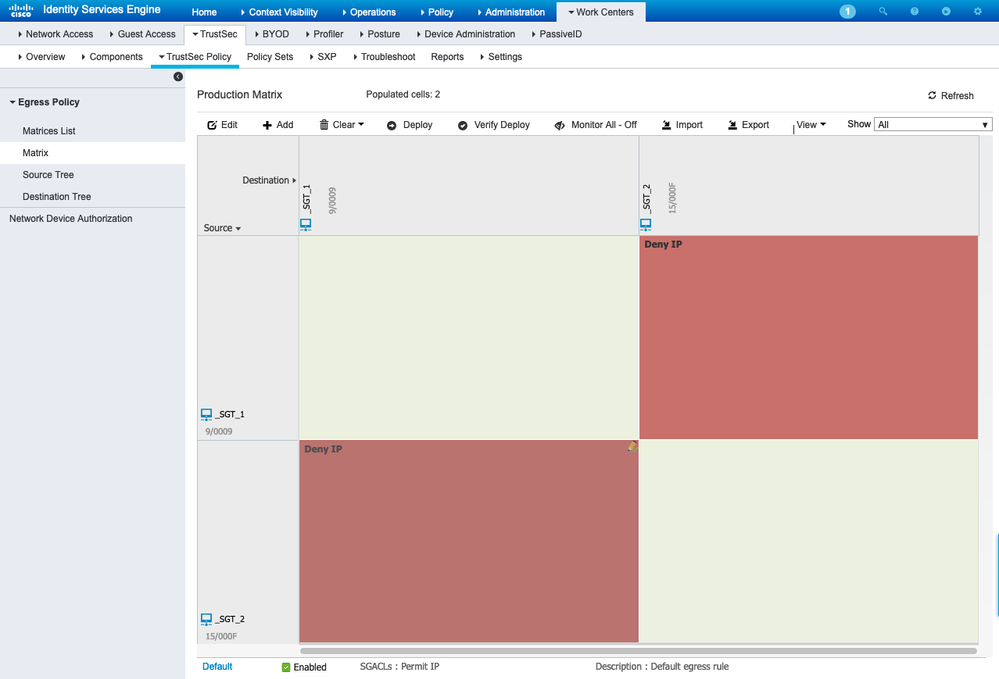
> prevent endpoints in SGT-1 from communicating with endpoints in SGT-2
This is simple and addressed in the TrustSec matrix by assigning Deny IP between the two tags :
> We would want to push the SGACL from ISE to the routers at these branch offices.
You need to ensure your network devices are registered in ISE as TrustSec network devices in order to receive the SGT and SGACL updates you provisioned above.
> you would still have to authenticate the devices using MAB auth in ISE?
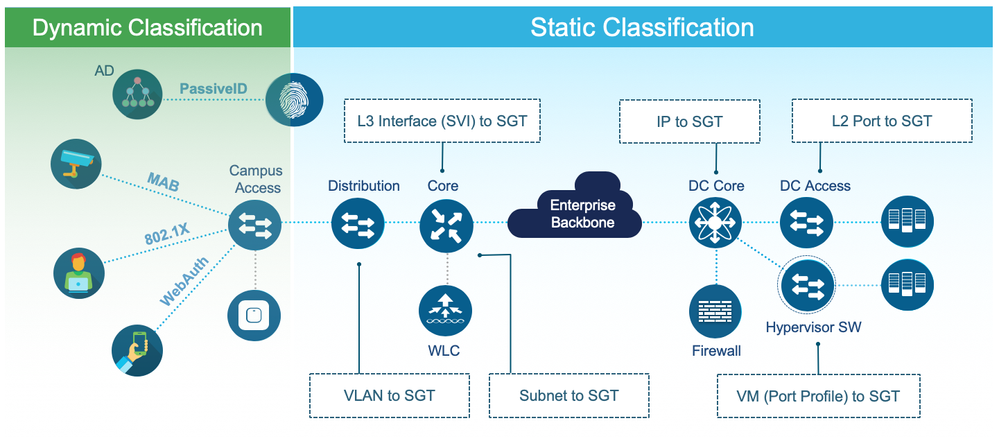
Yes, unless you want to do static classification by VLAN/subnet/IP which would not involve ISE but CLI configuration on each of your network access devices. Here are your options:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-02-2020 04:17 PM
You may assign Scalable Group Tags (SGTs) using any authorization rule in ISE, regardless of mechanics of the authentication. Since you mention Layer-2, your options would be 802.1X or MAC Authentication Bypass (MAB), so MAB it is! This would be most common for non-authenticating devices that you profile or put into a static endpoint group (printers, cameras, etc.) or with every new Guest (until they complete the appropriate guest flow) or otherwise Unknown devices that fall through and hit the Default.
I suggest reading http://cs.co/ise-resources#Segmentation > Campus / Branch Segmentation Design Guide. This should cover the full details of what is needed for Classification (assign SGT) at the edge and Propagating the information to your routers for Enforcement.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-03-2020 05:12 AM
communicating with endpoints in SGT-2. We would want to push the SGACL
from ISE to the routers at these branch offices. If I understand what you
are saying, you would still have to authenticate the devices using MAB auth
in ISE?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2020 08:06 AM
> prevent endpoints in SGT-1 from communicating with endpoints in SGT-2
This is simple and addressed in the TrustSec matrix by assigning Deny IP between the two tags :
> We would want to push the SGACL from ISE to the routers at these branch offices.
You need to ensure your network devices are registered in ISE as TrustSec network devices in order to receive the SGT and SGACL updates you provisioned above.
> you would still have to authenticate the devices using MAB auth in ISE?
Yes, unless you want to do static classification by VLAN/subnet/IP which would not involve ISE but CLI configuration on each of your network access devices. Here are your options:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-05-2020 09:50 AM
In regards to “static classification by vlan/subnet without ISE, are you saying ISE is still involved as far as the SGT/SGACL to the routers, just not from an authentication standpoint, or that ISE would not be used at all in that scenario? Can you still deploy the SGT/SGACL from ISE to the layer 3 network devices, without having to configure 802.1X down the switchport?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-06-2020 04:36 PM
It is possible to use TrustSec without authenticating/authorising the endpoints at the access layer, but this makes for a much less dynamic environment.
There are different types of Static Classification available for TrustSec, including:
- Static IP- or Subnet-SGT mappings configured in ISE and pushed to the network device performing Enforcement via SGACL.
- Static VLAN-SGT, Port-SGT, IP-SGT, Subnet-SGT, L3IF-SGT bindings configured on the network device; these cannot be configured/managed by ISE.
SGACLs can be configured manually on the network device or pushed by ISE, depending on the device platform capabilities. Keep in mind that the Enforcement point must know the IP- or Subnet-SGT mappings for both the Source and Destination to apply the SGACL or SGFW controls.
Also be aware that you may need to use SGFW (via Zone-Based Policy Firewall) if your router platform does not support SGACL. See the current TrustSec Platform Capability Matrix for more info.
There is a vast amount of information and caveats that need to be understood when designing/deploying TrustSec, so I would recommend viewing the following CiscoLive presentations:
Software-Defined Access Controls and Segmentation for Enterprise and Cloud - BRKSEC-2203
Advanced Security Group Tags: The Detailed Walk Through - BRKSEC-3690
Discover and save your favorite ideas. Come back to expert answers, step-by-step guides, recent topics, and more.
New here? Get started with these tips. How to use Community New member guide